Privacy protection express delivery and pickup system and method based on intelligent contract
A smart contract, privacy protection technology, applied in computer parts, collaborative devices, record carriers used by machines, etc., can solve the problems of information leakage, inability to keep the privacy information of senders and recipients confidential, and achieve protection The effect of personal privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0056] Today's blockchain smart contract technology is developing rapidly and is gradually being applied to the Internet of Things and logistics. Since the smart contract technology does not require the intervention of a third-party organization (express company), but automatically executes the business process of privacy protection in the delivery and pickup process, making full use of the characteristics of decentralization and high efficiency can make the privacy protection process easier. The present invention takes the delivery and pick-up smart contract as the core, completes the privacy protection of personal information during the delivery and pick-up process of express delivery, and ensures the security of express delivery data.
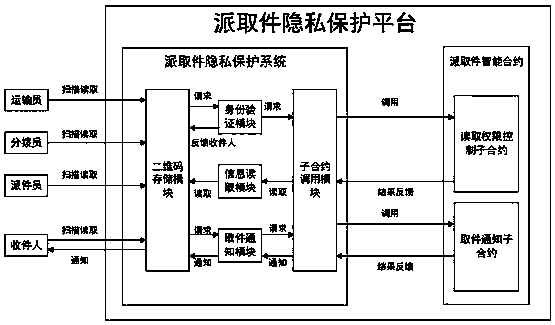
[0057] Therefore, if figure 1 As shown, in this embodiment, a smart contract-based privacy protection express delivery system is disclosed, including a privacy protection device and a smart contract device running on the area chain;
[0058...
Embodiment 2
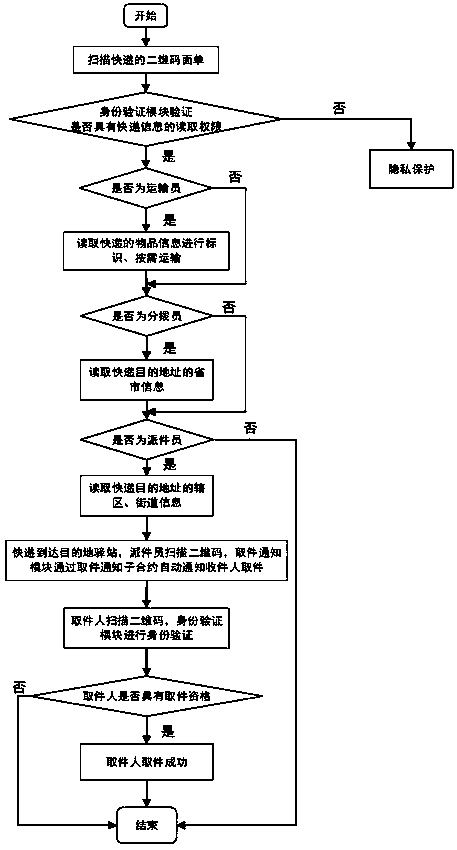
[0110] This embodiment discloses a privacy-protected courier delivery and pick-up method based on smart contracts, which is executed according to the following steps:
[0111] Step 1. Generate a QR code after encrypting according to the mailing information, and obtain the QR code image;
[0112] Optionally, the step 1 generates a two-dimensional code after encrypting according to the mailing information, and obtains a two-dimensional code image, which specifically includes:
[0113] Use the SHA256 function in the hash algorithm to encrypt the mailing information and then use the QRCode encoding technology to convert it and store it to obtain a two-dimensional code image.
[0114] Step 2, wait for the user to scan the two-dimensional code image, identify the identity of the user who scanned the two-dimensional code image, and obtain the user identity. The user identity includes sender, transporter, dispatcher, dispatcher, receiver, etc. recipients and others;
[0115] Optiona...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap