Method of discovering intermediate functions and selecting path between two communication devices
A function and path technology, applied in the field of data transmission
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] The general principle of the invention is based on discovering basic transport functions hosted in different intermediate nodes of a communication network through which a path is established between a first party communication device and a second party communication device.
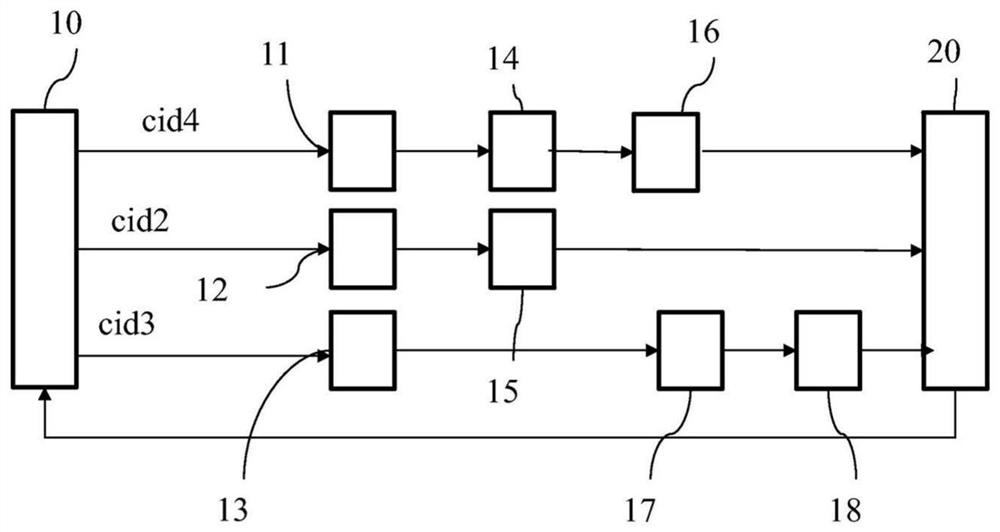
[0061] Figure 1A A first system 1 is shown in which the method according to the invention is implemented.
[0062] The system 1 comprises a first party communication device 10, such as a communication device 10 such as residential gateways, "smartphone" type mobile phones, digital decoders or "set-top boxes", etc.
[0063] System 1 includes a plurality of intermediate nodes 11-18 located in one or more communication networks. Such intermediate nodes 11 - 18 are, for example, elements of mobile networks (MEC (Mobile Edge Computing), C-RAN (Cloud Radio Access Network)), routers, gateways providing transport functions or application functions, or proxies. Intermediate nodes 11-18 host one or more ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More