A cryptographic system and method
A technology of a cryptographic system and an encryption scheme, applied in the field of cryptographic systems, can solve problems such as large key size and multiple storage resources, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
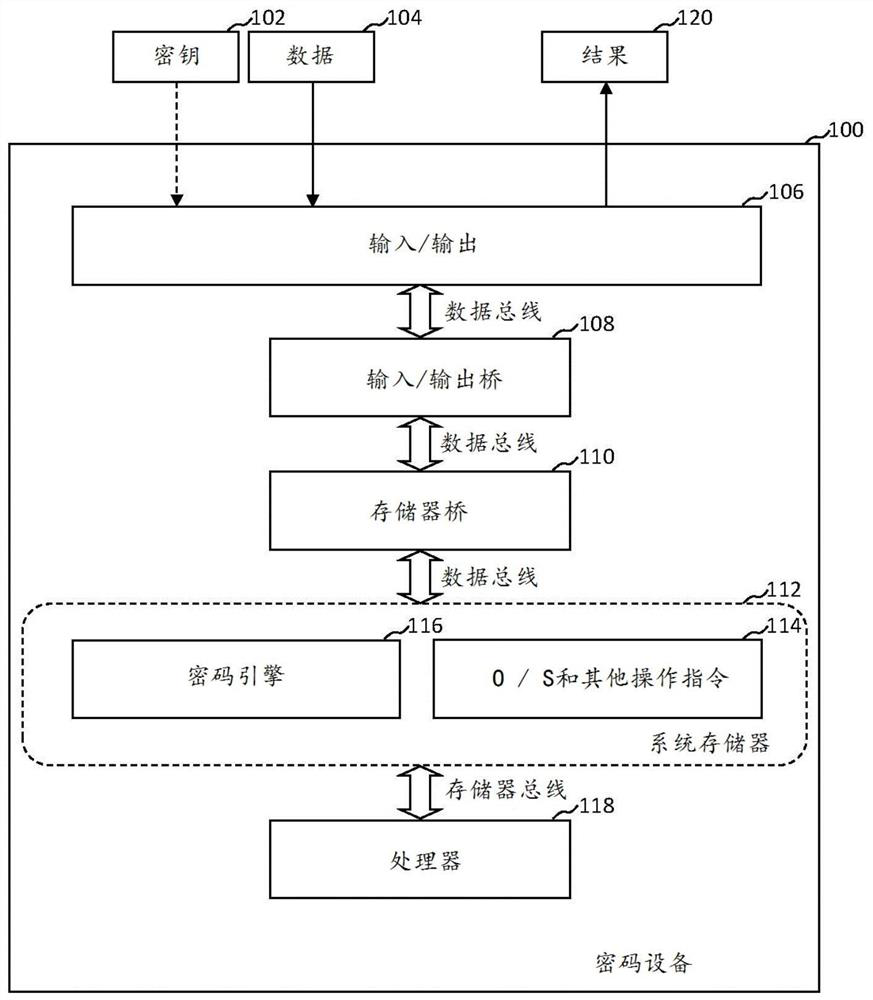
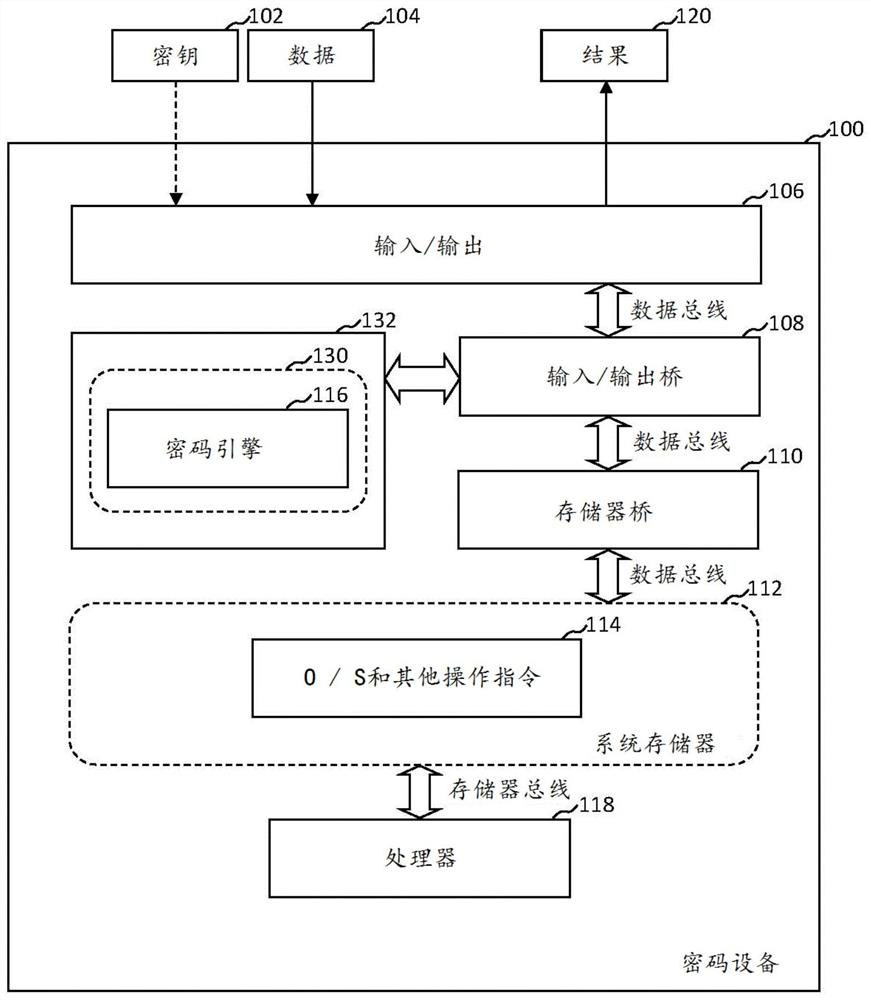
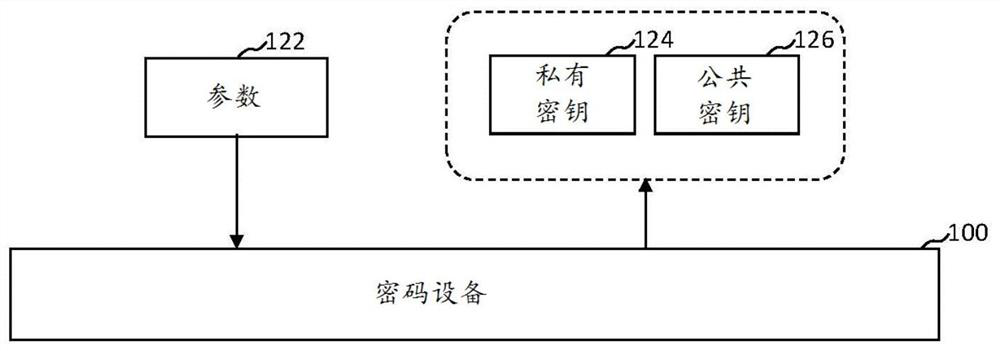
Image
Examples
example 1
[0084] Example 1: In this example, m=6, r=2. because We get n=2048+32=2080. Let d=61, t=30, then k≥2080-60·6=1720.
example 2
[0085] Example 2: For l=2, G(x) is a polynomial ring irreducible formula. The parity check matrix for this example is:
[0086]
[0087] and
[0088]
[0089] in and
[0090]
[0091] sum
[0092] middle x t-1 、x t-2 , ..., x, coefficients at 1
[0093]
[0094]
[0095]
[0096]
[0097] The parity check matrix H is defined as:
[0098]
[0099] As mentioned above, through the support set L as a set of rational functions to construct specific generalizations of Goppa codes. A specific generalization of Goppa codes is neither Reed Solomon (RS) codes nor alternation codes.
[0100] In order to decode these generalized Goppa codes, the Goppa polynomial G(x) and the support set L must be known. Classical decoding algorithms can then be used (Euclidean, Berlekamp-Massey, Patterson, etc.).
[0101] Using a set of position numerators whose order is greater than 1 reduces the order m of the Galois field extension used to obtain the support...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap