Threat attack protection decision-making method adopting AI and big data analysis and AI system
A decision-making method and big data technology, applied in the field of information security, can solve problems such as the difficulty of pertinence and accuracy to meet expectations, and achieve the effect of pertinence and accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
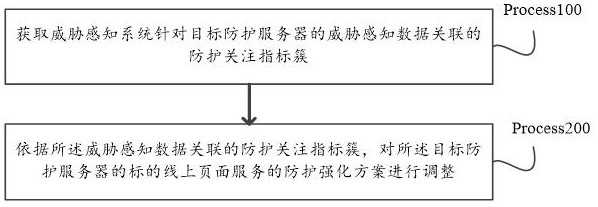
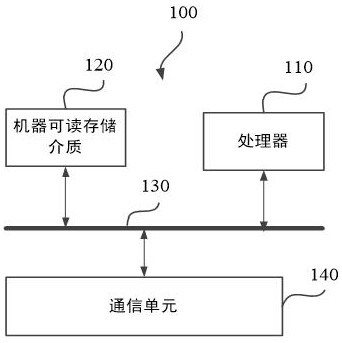
Method used
Image
Examples
Embodiment Construction
[0018] The terms "first", "second", "third", "fourth", etc. (if present) in the description and claims of the present invention and the above-mentioned drawings are used to distinguish similar objects and are not necessarily used to describe a specific order or sequence. It is to be understood that the data so used may be interchanged under appropriate circumstances such that the embodiments of the invention described herein can, for example, be practiced in sequences other than those illustrated or described herein. Furthermore, the terms "comprising" and "corresponding to", and any variations thereof, are intended to cover non-exclusive inclusion, for example, a process, method, system, product or device comprising a series of steps or units is not necessarily limited to the explicit lists Those steps or units listed may instead include other steps or units not expressly listed or inherent to these processes, methods, products or devices.
[0019] The following describes th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More