System as well as method for protecting an item to be secured
An article, security technology, applied in the field of systems and methods for protecting article security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
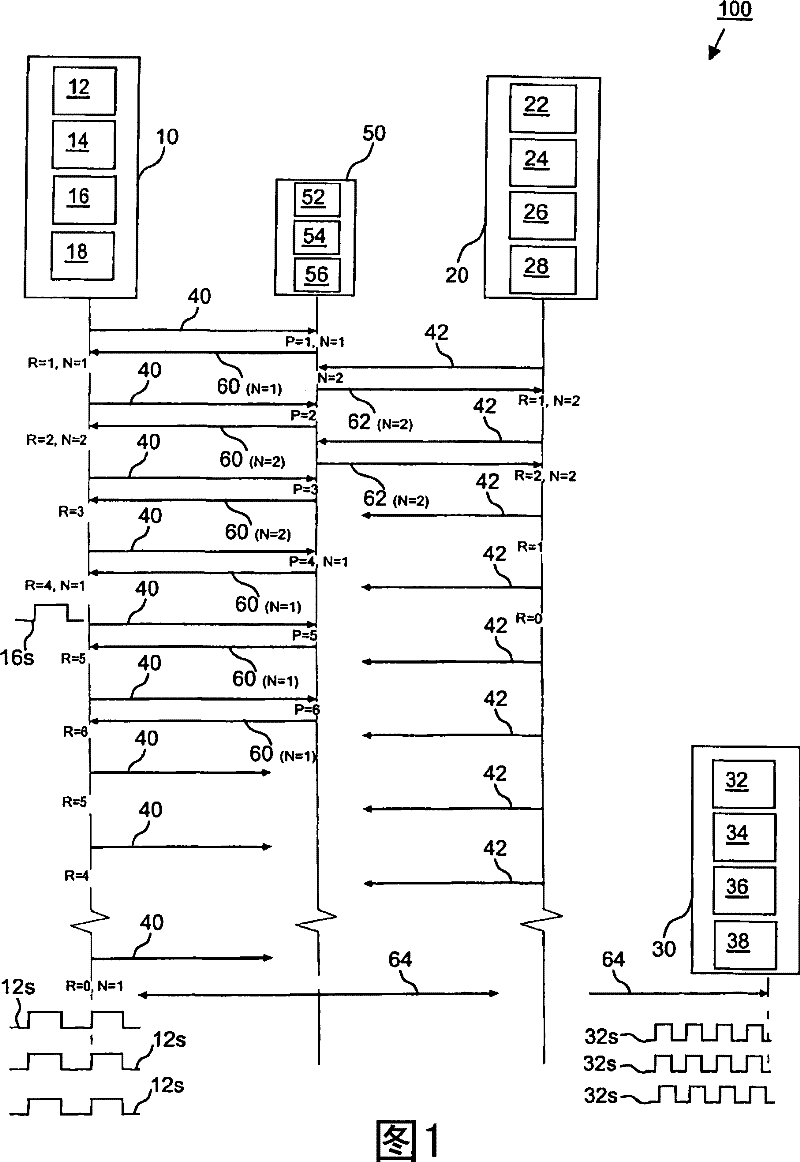
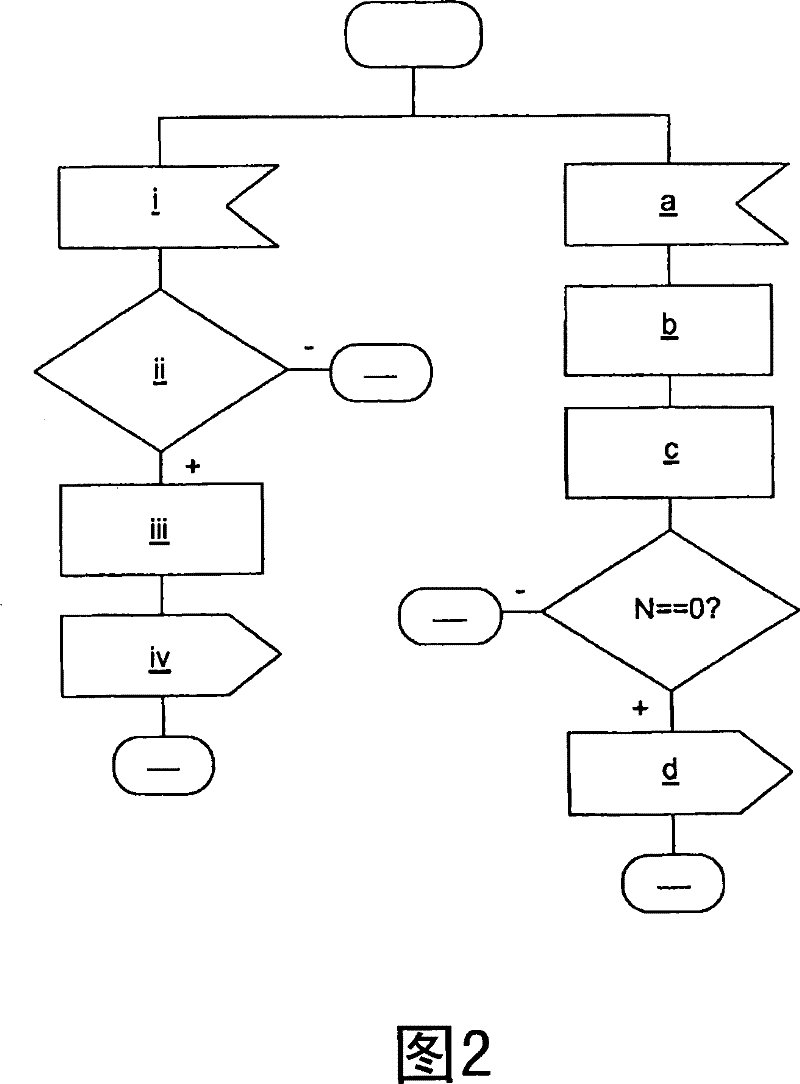
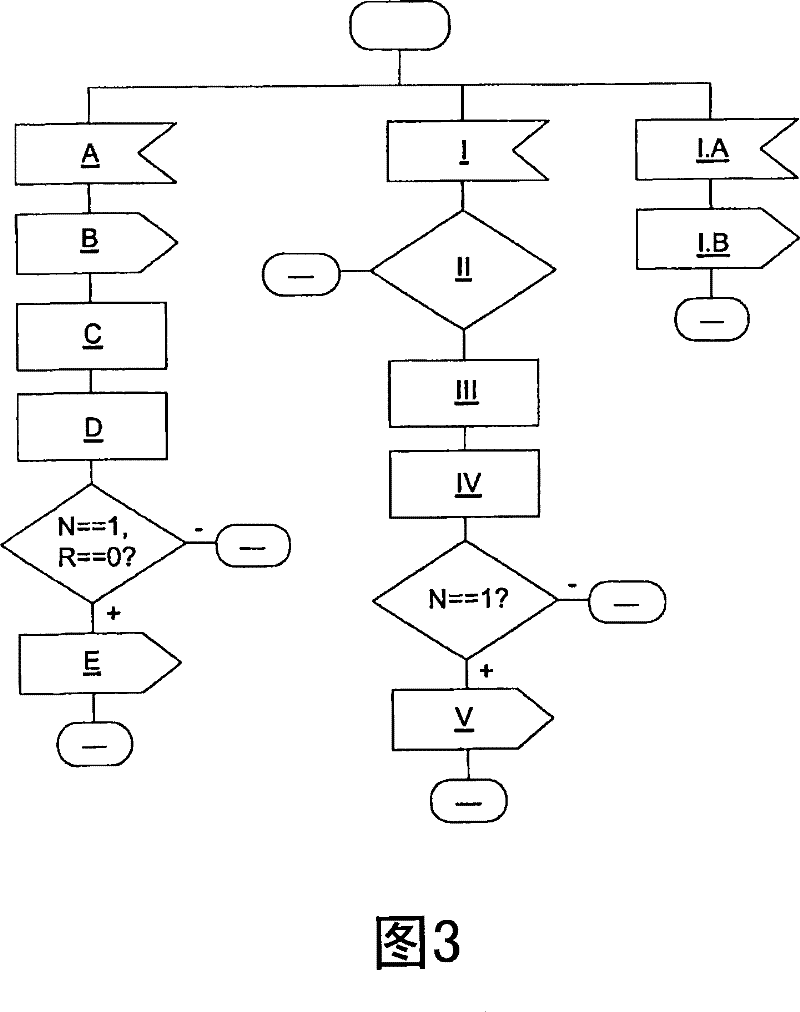
[0067] for Figure 1 to Figure 3 Corresponding parts in , use the same reference numerals.
[0068] figure 1 The system 100 shown comprises a transponder device 50 , ie an electronic tag assigned to a valuable item, and two monitor devices 10 , 20 assigned to this electronic tag 50 .
[0069] Each monitor device 10 , 20 is based on short-range radio frequency communication and includes a transmitting unit 18 , 28 for periodically transmitting at least one request 40 , 42 (ie a ping message) to the electronic tag 50 .
[0070] Instead the tag is designed to transmit at least one response 60 , 62 , ie a return message, to the monitor device 10 , 20 that has pinged ( 40 , 42 ) the electronic tag 50 .
[0071] As an exemplary embodiment, figure 1 A series of messages 40, 60 and 42, 62 between tags belonging to two co-custodians of valuables are shown. Each supervisor has one of the monitor devices 10, 20 which periodically sends a "ping" message 40, 42 to the tag 50 attached t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More