H.264 video integrality authentication method
An authentication method and integrity technology applied in the field of H.264 video integrity authentication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0149] A H.264 video integrity authentication method, comprising the following content:
[0150] (1) Authentication code generation
[0151](a) Smooth and fast hierarchical quantitative authentication code generation
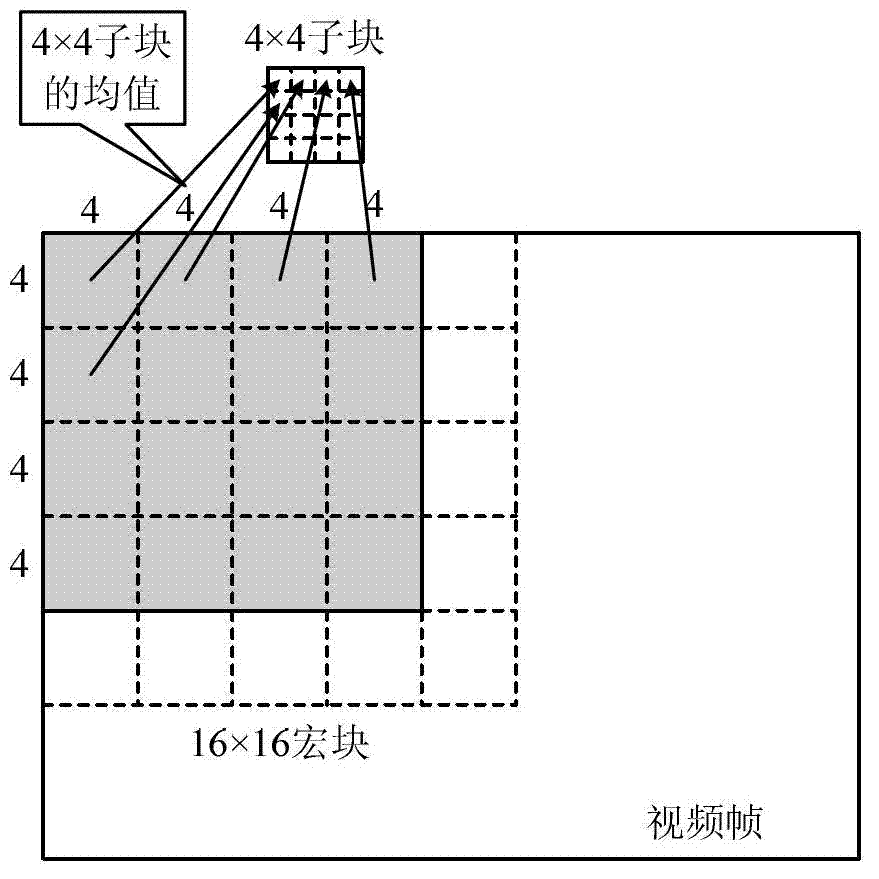
[0152] Since the length of the authentication code cannot be too large, the dimensionality reduction of the original data is very necessary. For a given video frame F we first extract its luminance component F L As processing, we then downsample by computing the mean of the 4×4 sub-blocks.
[0153] Let us look at a numerical example, for a CIF image with a resolution of 352×288, F d The dimensions are 88×72, which is still too large for an authentication code. We further add F d It is divided into several sub-blocks for feature extraction. The sub-block size is again chosen to be 4×4, or even 8×8 if a smaller authentication code is required.
[0154] figure 1 Shown as a structure of blocks and sub-blocks. The characteristic value will be extracted from ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More