Access control system and access control method for electronic product code
An electronic product code and access control technology, which is applied to the usage of multiple keys/algorithms, instruments, and sensing record carriers, can solve the problems that EPCIS item information is vulnerable to theft, tampering, and deletion, so as to prevent illegal access and guarantee Privacy Effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
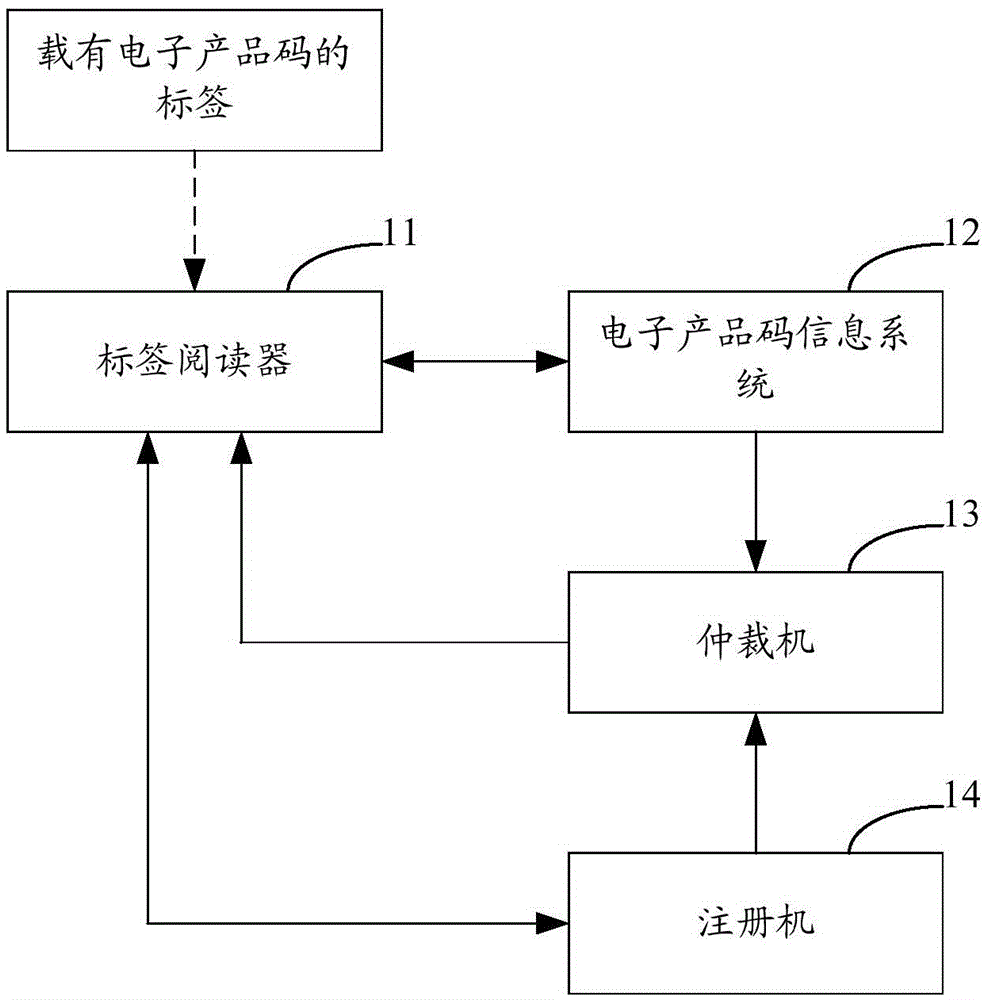
[0027] figure 2 The structure of the electronic product code access control system provided by the first embodiment of the present invention is shown, and for the convenience of description, only the parts related to the first embodiment of the present invention are shown.
[0028] In Embodiment 1 of the present invention, the access control system of the electronic product code includes: a registration machine 14, which is used to establish public parameters and a master private key, and when a registration request is received and the registration request meets the conditions, output the first private key and the second private key. 2. Private key; the electronic product code information system 12 is used to store the ciphertext of the electronic product code information and the ciphertext of the corresponding key, and after receiving the label information access request, store the ciphertext of the electronic product code information and the ciphertext of the corresponding k...
Embodiment 2
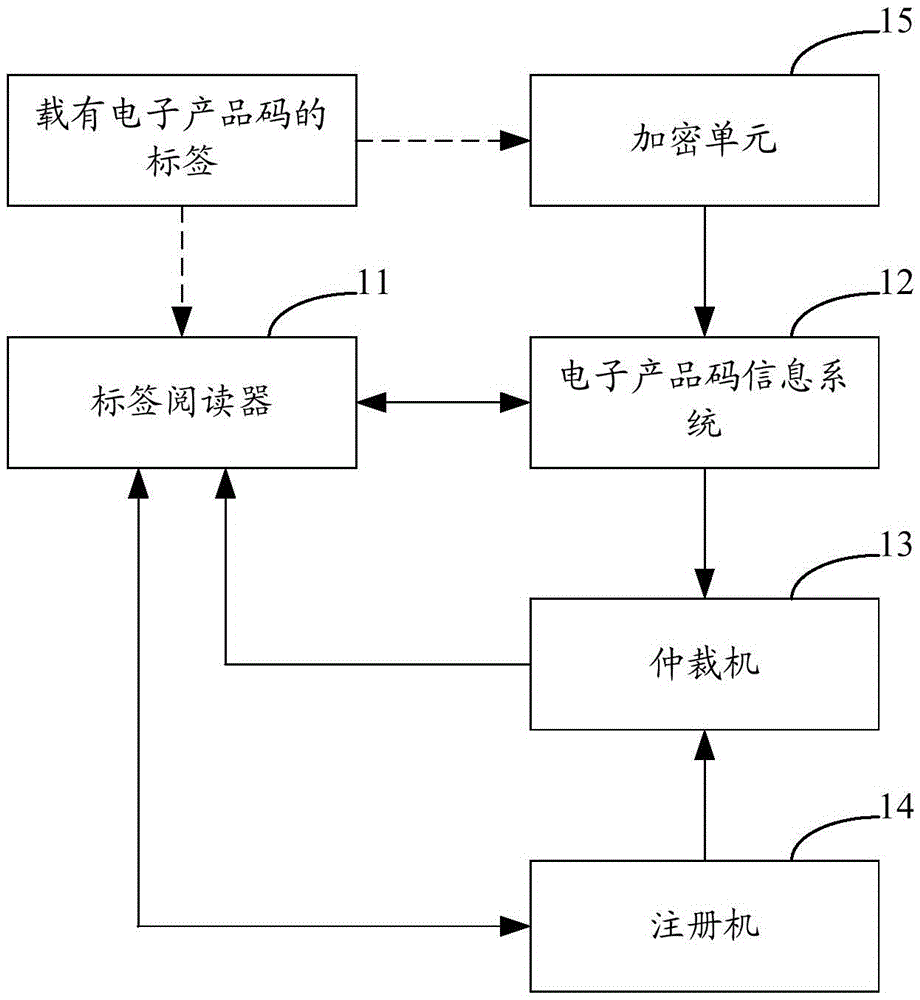
[0031] image 3 The structure of the electronic product code access control system provided by the second embodiment of the present invention is shown, and for the convenience of description, only the parts related to the second embodiment of the present invention are shown.
[0032] Different from Embodiment 1, in Embodiment 2 of the present invention, the access control system of the electronic product code further includes: an encryption unit 15, which is used to randomly generate a key by using an encryption algorithm, and encrypt the information of the electronic product code to obtain the electronic product code The ciphertext of the information, and then according to the preset access structure of the electronic product code information, the ciphertext of the corresponding key of the electronic product code information is generated, and the ciphertext of the electronic product code information and the ciphertext of the corresponding key are stored in the electronic produ...
Embodiment 3
[0034] Figure 4 It shows a flow chart of the access control method of the electronic product code access control system provided in the third embodiment of the present invention and described in the first or second embodiment.
[0035] In Embodiment 3 of the present invention, the access control method of the access control system of the electronic product code includes:
[0036] Step S1: The registration machine establishes the public parameters and the master private key. Step S1 may further include the following steps:
[0037] S11: Set the security parameter λ.
[0038] S12: Define the first multiplicative group whose order is a prime number p and the second multiplicative group get the first multiplicative group The generator g of and defines the bilinear map e:
[0039] S13: Set attribute space For each attribute in the attribute space choose randomly and calculate
[0040] S14: Random selection and calculate u=g β , w=e(g,g) α .
[0041] S15: Est...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap