Method and system for determining bearer control policy
A technology of control strategy and bearer control, applied in the field of communication, can solve the problems of complicated service access process, reduced user experience, waste of network resources, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The present invention will be described more fully hereinafter with reference to the accompanying drawings, in which exemplary embodiments of the invention are illustrated.
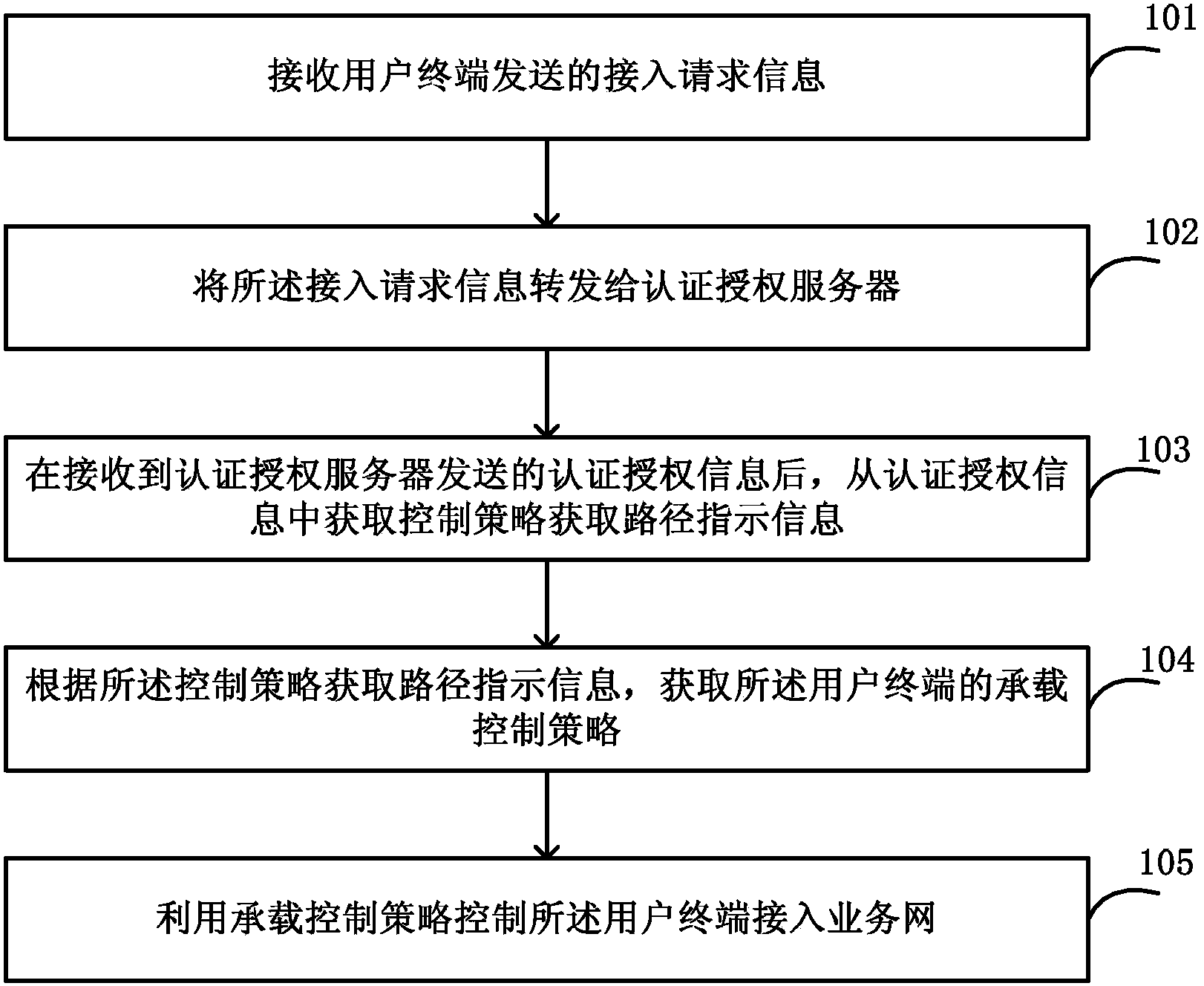
[0041] figure 1 A schematic diagram of an embodiment of a method for determining a bearer control policy in the present invention. Such as figure 1 As shown, the steps of the method for determining the bearer control strategy in this embodiment are as follows:
[0042] Step 101, receiving access request information sent by a user terminal, where the access request information includes user terminal identification information.
[0043] Step 102: Forward the access request information to an authentication and authorization server, so that the authentication and authorization server authenticates the user terminal according to the user terminal identification information.
[0044] Step 103, after receiving the authentication and authorization information sent by the authentication and authorization...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More