Data protection method and safety bastion host
A technology of data protection and bastion machine, which is applied in the field of communication and can solve problems such as the inability to guarantee the security of server data.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
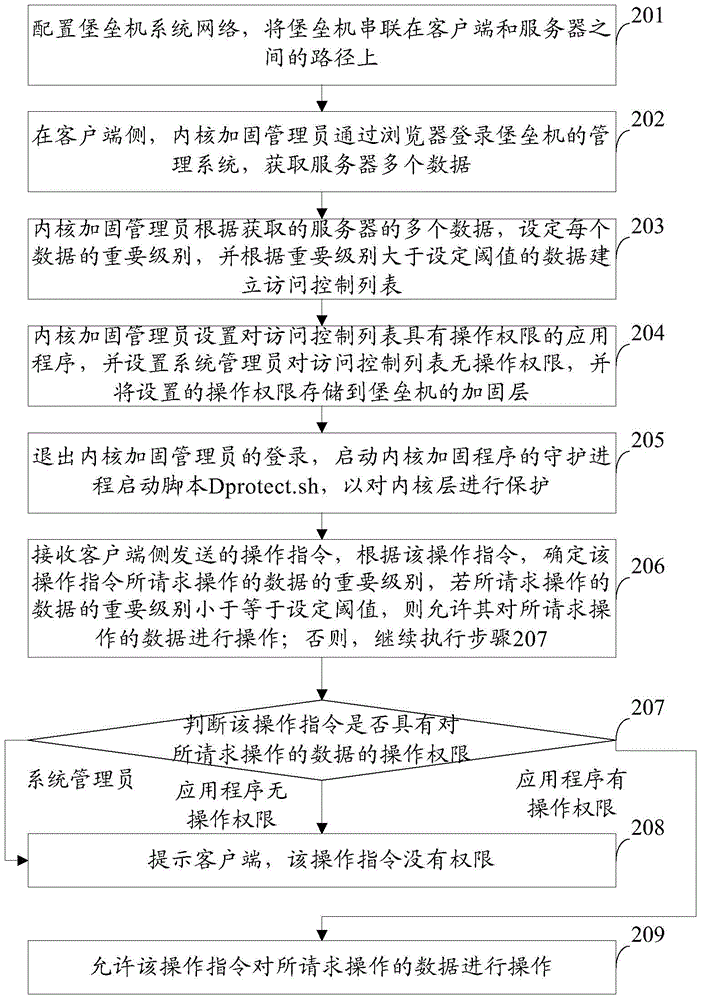
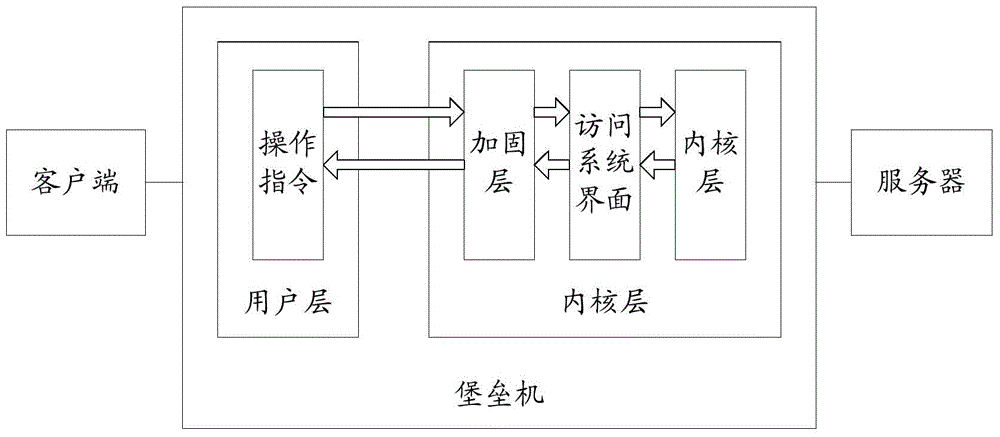
[0039] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention. Apparently, the described embodiments are only some of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
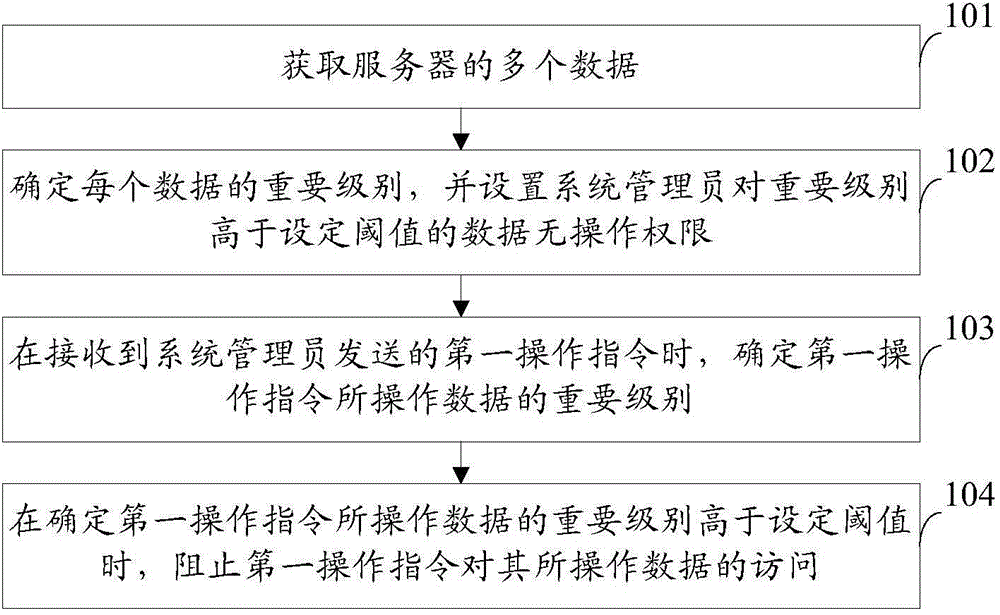
[0040] Such as figure 1 As shown, the embodiment of the present invention provides a data protection method, in which the bastion machine is connected in series on the path between the client and the server, and the method may include the following steps:
[0041] Step 101: Obtain multiple pieces of data from the server.
[0042] Step 102: Determine the importance level of each data, and set the system administrator to have no operation authority on th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More