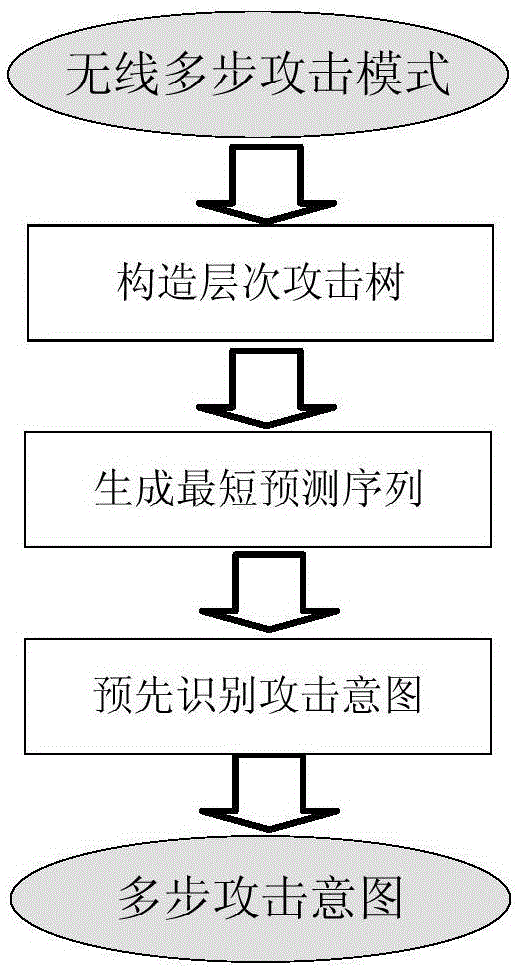
WLAN multi-step attack intention pre-recognition method
An identification method and intent technology, applied in digital transmission systems, electrical components, transmission systems, etc., can solve problems such as the inability to apply multi-step attack identification methods, and achieve the effect of pre-identification and efficiency improvement
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0050] The present invention will be further described below in conjunction with the accompanying drawings and embodiments. While the invention will be described in conjunction with the preferred embodiments, it will be understood that it is not intended to limit the invention to the described embodiments. On the contrary, the invention is to cover alternatives, modifications and equivalents, which may be included within the scope of the invention as defined by the appended claims.
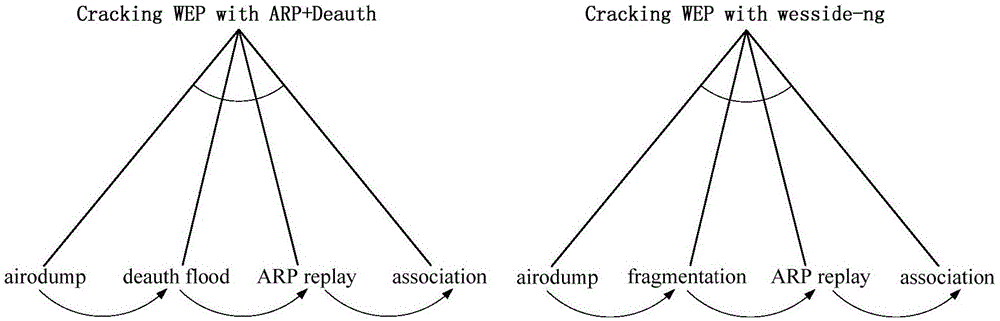
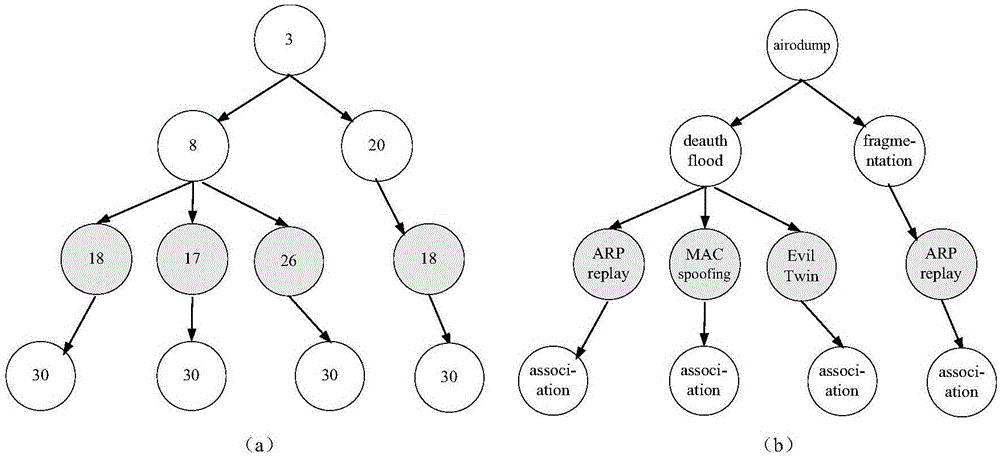
[0051] Step 1. Construct a hierarchical attack tree
[0052] For example, using the idea of hierarchical planning library proposed by Geib and Goldman to describe the two multi-step attack modes of ARP+Dauthentication Flood attack to crack WEP key and wesside-ng to crack WEP key in wireless attack, the following can be obtained: figure 2 The hierarchical planning library shown.
[0053] Among them, the arcs without arrows represent the relationship of "and", which means that the realization o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More