Storage device access control method and system
A storage device and access control technology, applied in internal/peripheral computer component protection, digital data authentication, etc., can solve the problems of no storage device legality detection, insufficient terminal data security, data security impact, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] The scope of applicability of the present invention will become apparent from the detailed description given below. It should be understood, however, that the detailed description and specific examples, while indicating the preferred embodiment of the invention, are given for purposes of illustration only.
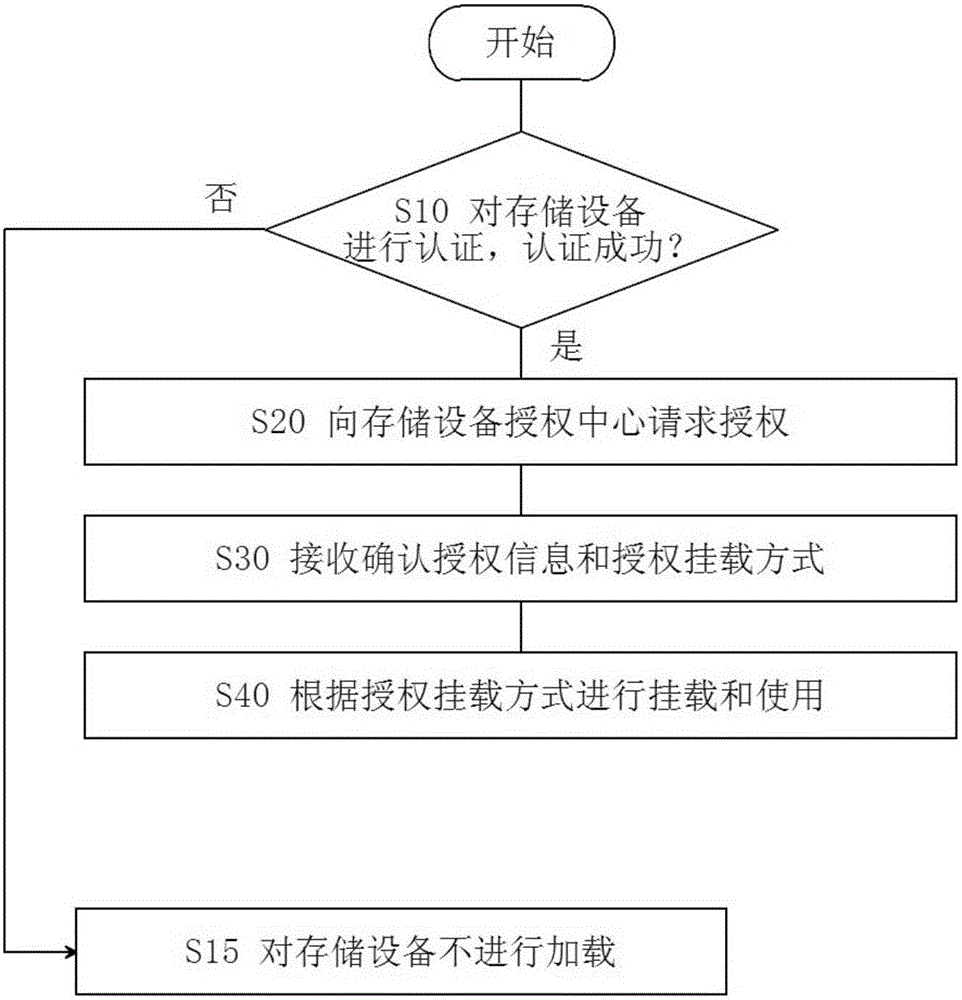
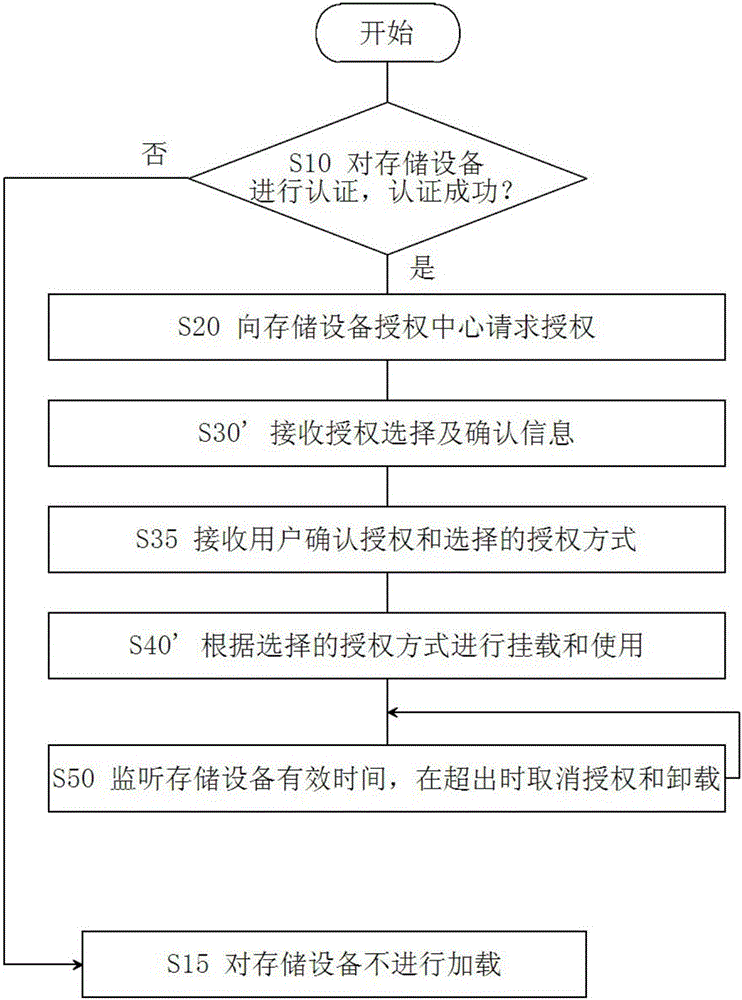
[0022] figure 1 A flow chart of a method for controlling storage device access according to an embodiment of the present invention is shown. The method starts at step S10. For example, a storage device access event is detected through a service (resident process) of a terminal such as a computer that manages storage device access. When a storage device access is detected, the legality and availability of the storage device Credibility certification. The authentication method can adopt one or more of the following: 1) Determine whether the terminal and the storage device match according to the customized communication protocol and instruction, for example, use a sp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com