A safe and efficient outsourcing calculation implementation method and system
An implementation method and efficient technology, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
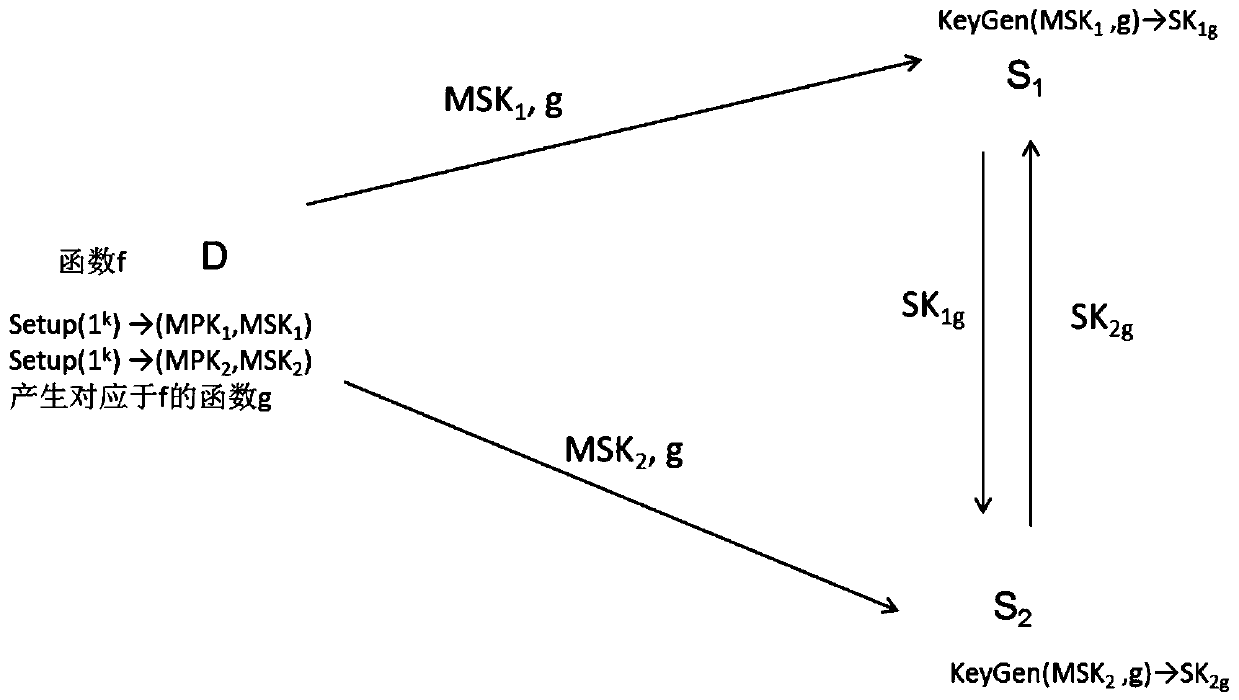
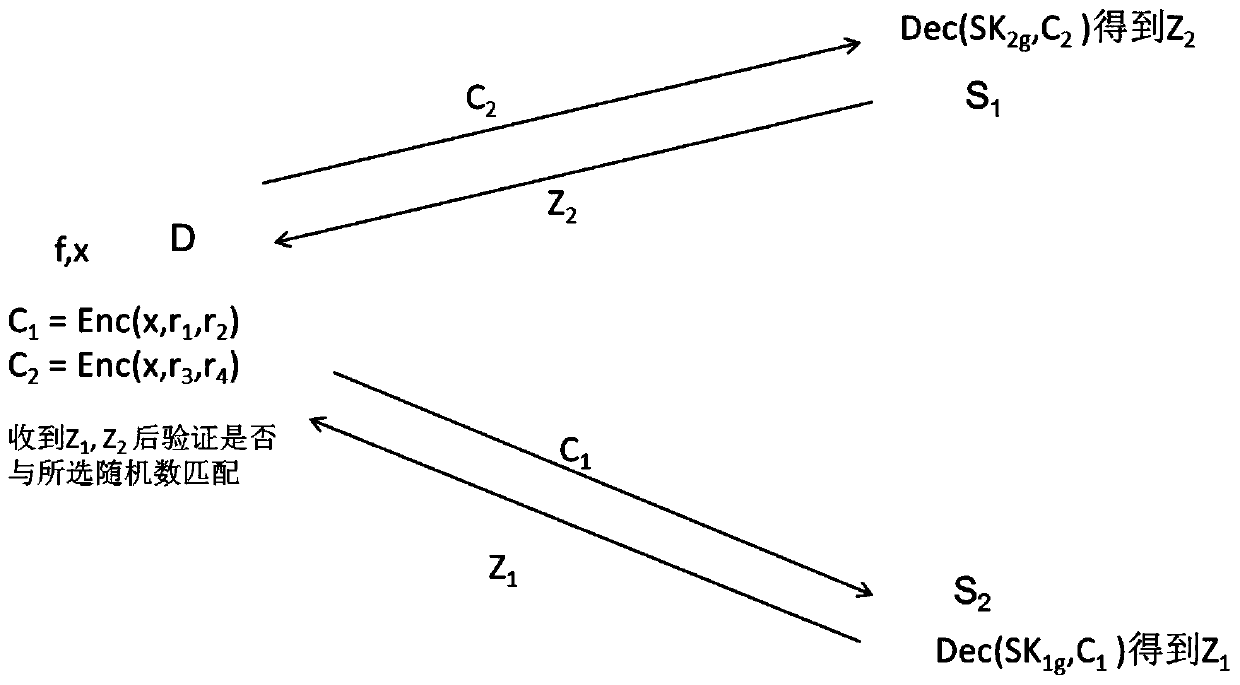
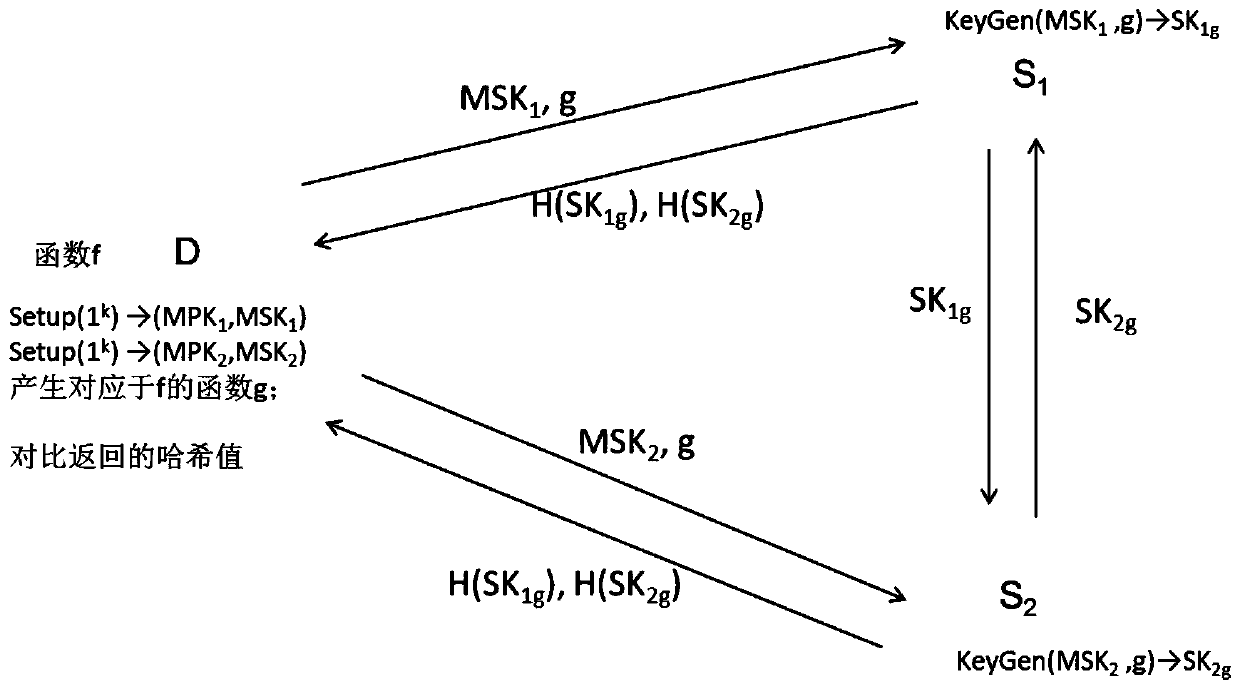
[0035] In order to make the above objects, features and advantages of the present invention more obvious and understandable, the present invention will be further described below through specific embodiments and accompanying drawings.
[0036] The functional encryption scheme is a fine-grained encryption scheme. The decryptor can use the decryption key to obtain the function value corresponding to the plaintext, but does not know other information about the plaintext. This feature can be well applied in outsourced computing, because the client wants the server to complete the calculation, but does not want to leak the value of the outsourced data x.
[0037] Functional encryption means that the decryption party has the ciphertext C of the message x and the decryption key SK corresponding to the function f f , can only decrypt the function value f(x) of the message, but cannot know other information about x. The functional encryption algorithm is defined as follows:
[0038] ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More