Network attack surface tracking method, server and system
A network attack and server technology, which is applied in the field of network security and can solve the problems of network node security vulnerabilities and untraceable attack surfaces.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings, so that the advantages and features of the present invention can be more easily understood by those skilled in the art, so as to define the protection scope of the present invention more clearly.
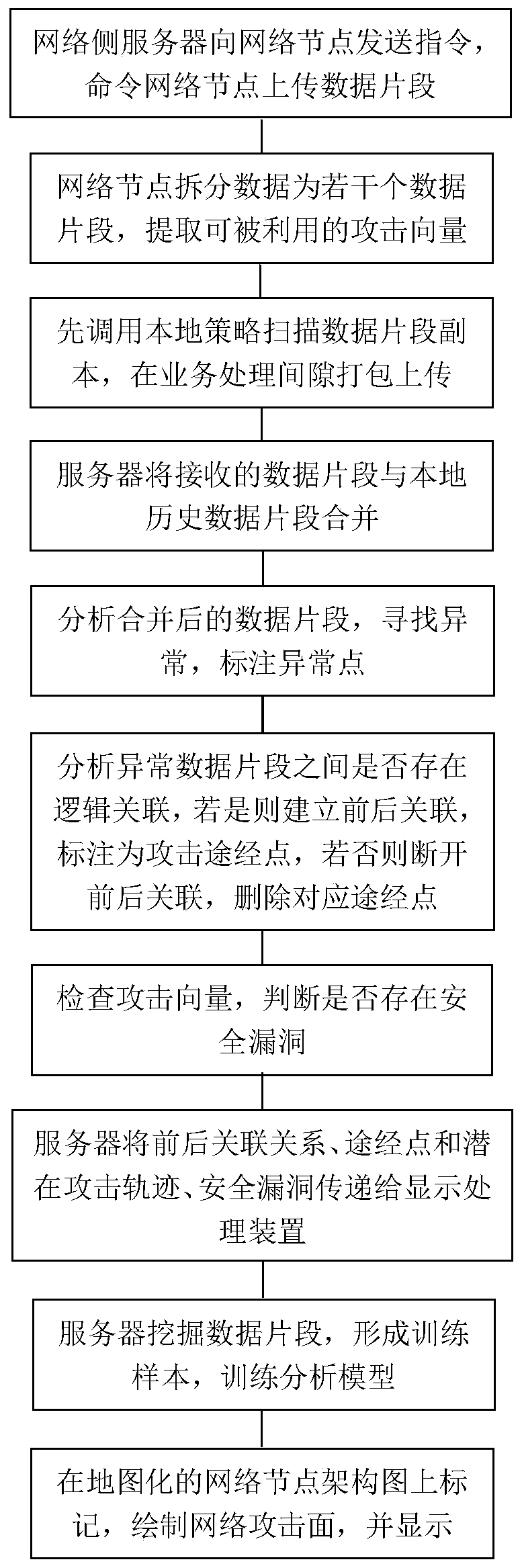
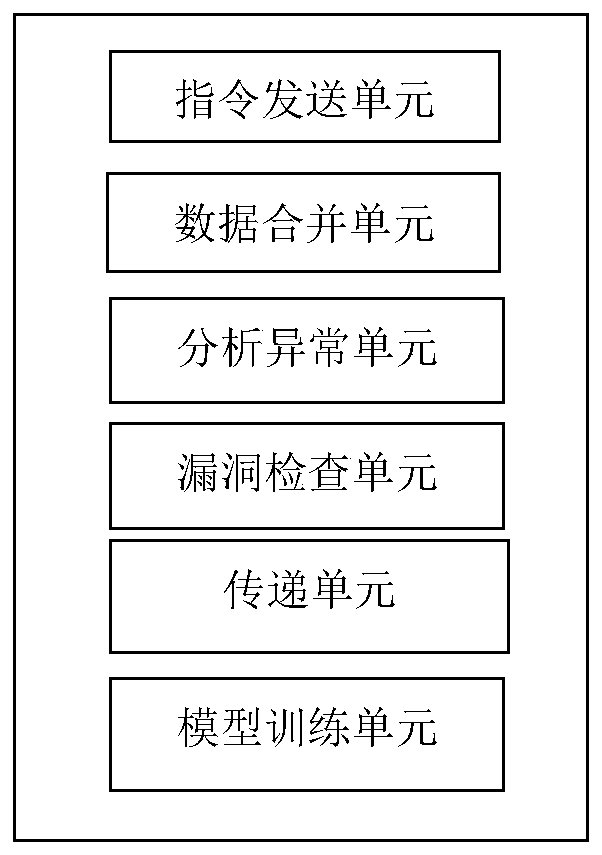
[0038] figure 1 The flow chart of the method for network attack surface tracking provided by this application, the method includes:
[0039] The server on the network side sends an instruction to each network node, and the instruction is used to instruct each network node to upload the local data segment to the server;
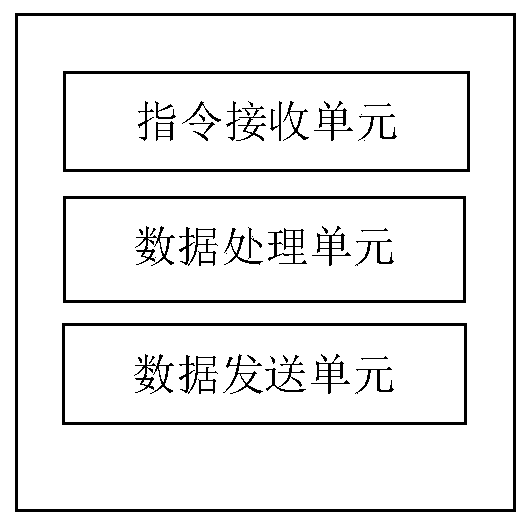
[0040] After each network node receives the instruction, it splits the local data flow through the network node into several data fragment copies, and extracts exploitable attack vectors therefrom;
[0041] Each network node first invokes a local strategy to scan the copy of the data segment to check whether it contains an explo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More