Breach host detection method, device and equipment and readable storage medium
A detection method and host technology, applied in the field of network security, can solve the problems of low accuracy of detection results, difficult perception of lost hosts, and strong concealment, so as to improve network security and reliability, solve problems, and improve comprehensiveness. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
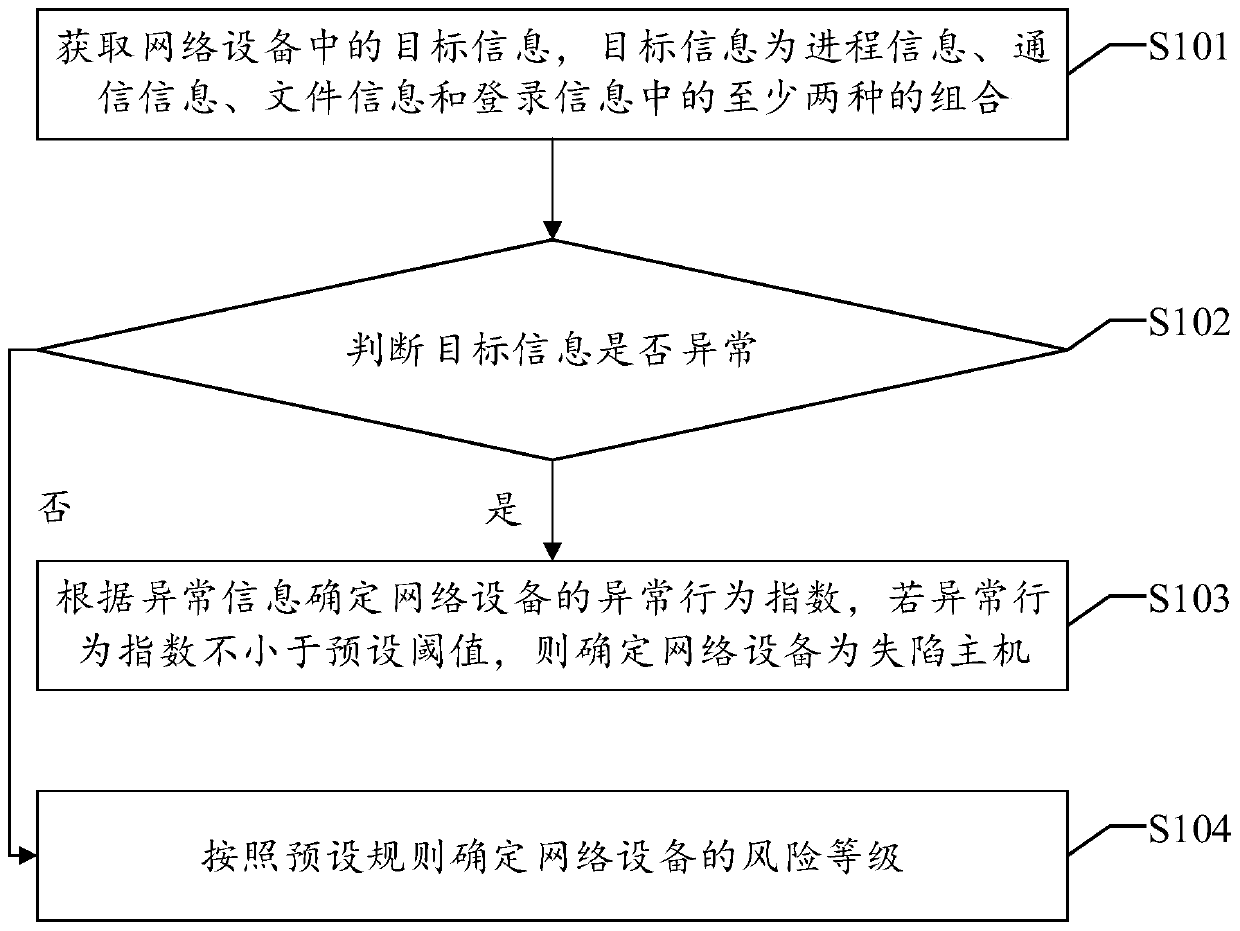
[0045] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0046] Existing technologies usually determine the compromised host based on known viruses or known malicious traffic, and the entire process only analyzes the single-dimensional data of the compromised host, which is somewhat one-sided, and there are omissions and misreporting events, so the accuracy of the detection results If it is low, it may also lose the opportunity to detect and solve problems in advance, leading to larger-scale network security incidents. For this reason, th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More