Authentication terminal for compiling password based on identity authentication digital signature
A digital signature and password technology, applied in the field of network information security, can solve the problems of inability to prove the identity of network users, the inability of network users to prove digital signatures, and the inability to verify the authenticity of identity of network users, so as to prevent forged identities The effect of unauthorized access to network resources, defense against fake identity authentication, and defense against attacks on network user identity certification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
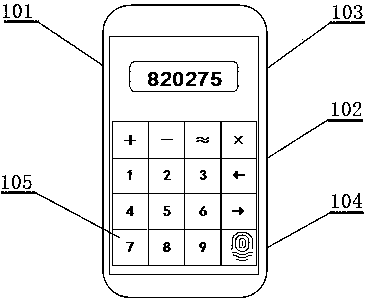
[0007] In order to describe the structural characteristics and operation steps of the present invention in detail, the following preferred embodiments are given below and further described with reference to the accompanying drawings. like figure 1 Shown: the present invention comprises main body 101, and described main body 101 is provided with microprocessor 102, and described microprocessor 102 is the command and control center of whole authentication terminal, has the dynamic password of receiving authentication server, based on the rule key of operation and fingerprint key Correct with memory 4 rule key and fingerprint identification, instruction key signature module 103 and dynamic password digital signature work out password, and send authentication server; Described microprocessor 102 top is provided with key signature module 103, and described key Signature module 103 is used for dynamic password operation digital signature and makes up password; Described key signatur...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More