Virtual object control method, device, computer equipment and storage medium
A virtual object and control method technology, applied in the computer field, can solve problems such as single attack method, lack of authenticity, and inconformity with battle scenarios, so as to avoid malicious attacks and improve authenticity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
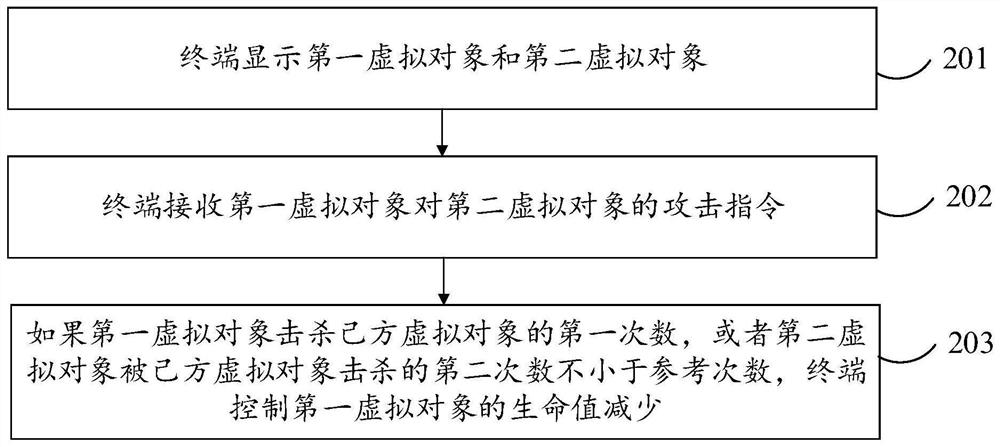
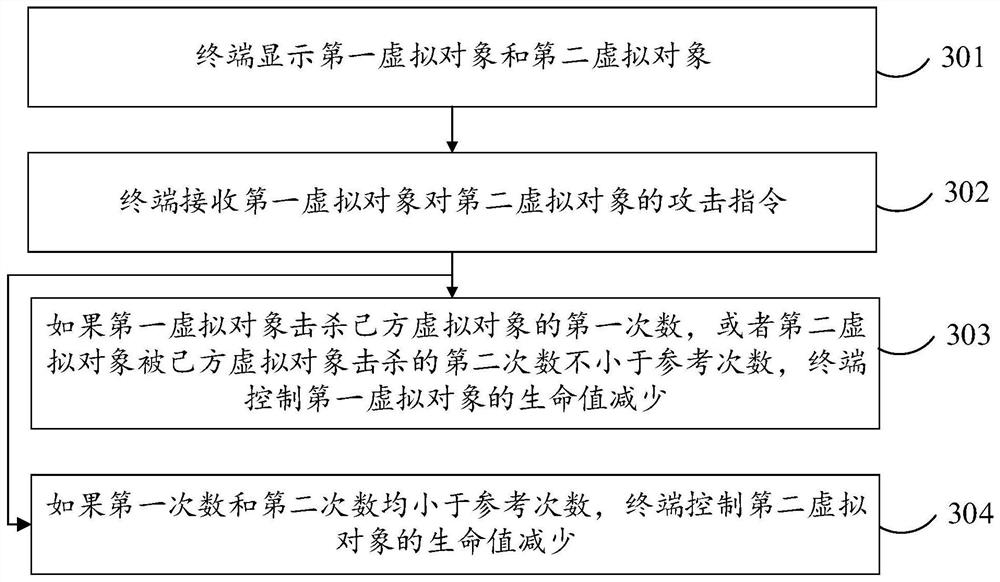
[0069] In order to make the objectives, technical solutions and advantages of the embodiments of the present application more clear, the embodiments of the present application will be further described in detail below with reference to the accompanying drawings.
[0070] The terms "first", "second", etc. used in this application may be used herein to describe various concepts, but these concepts are not limited by these terms unless otherwise specified. These terms are only used to distinguish one concept from another. For example, a first virtual object may be referred to as a second virtual object, and similarly, a second virtual object may be referred to as a first virtual object, without departing from the scope of this application.
[0071] As used in this application, the terms "at least one", "plurality", "each" and "any", at least one includes one, two or more, multiple includes two or more, and each Each refers to each of the corresponding plurality, and any refers t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More