Internet of vehicles intrusion detection method and system based on deep reinforcement learning
A technology of intrusion detection and reinforcement learning, applied in the field of network security, can solve problems such as difficult normal behavior modeling
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
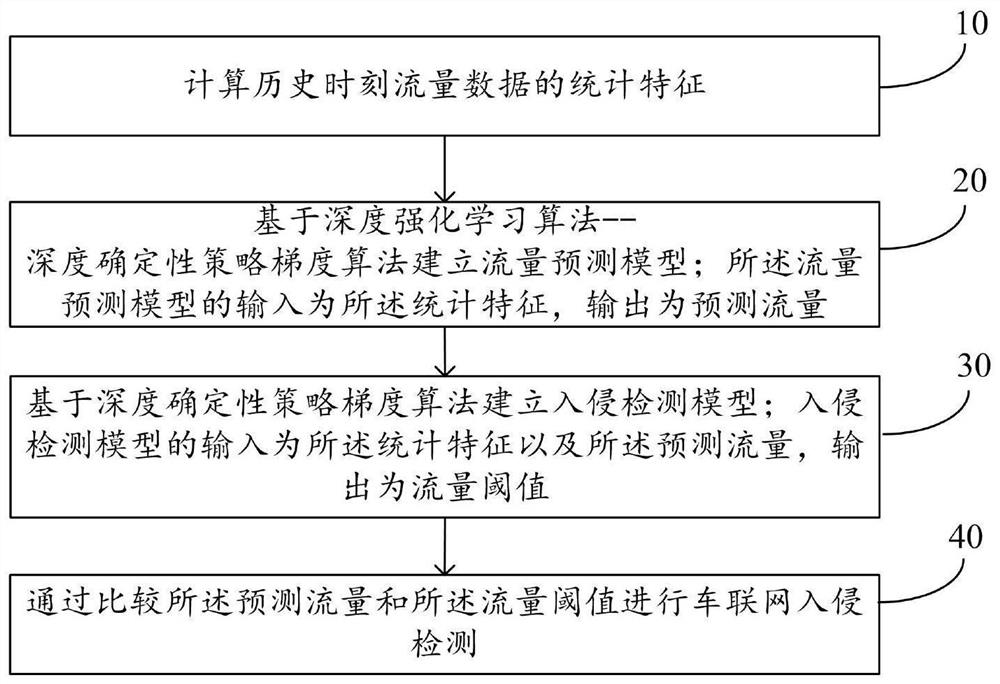
Method used
Image
Examples
specific Embodiment
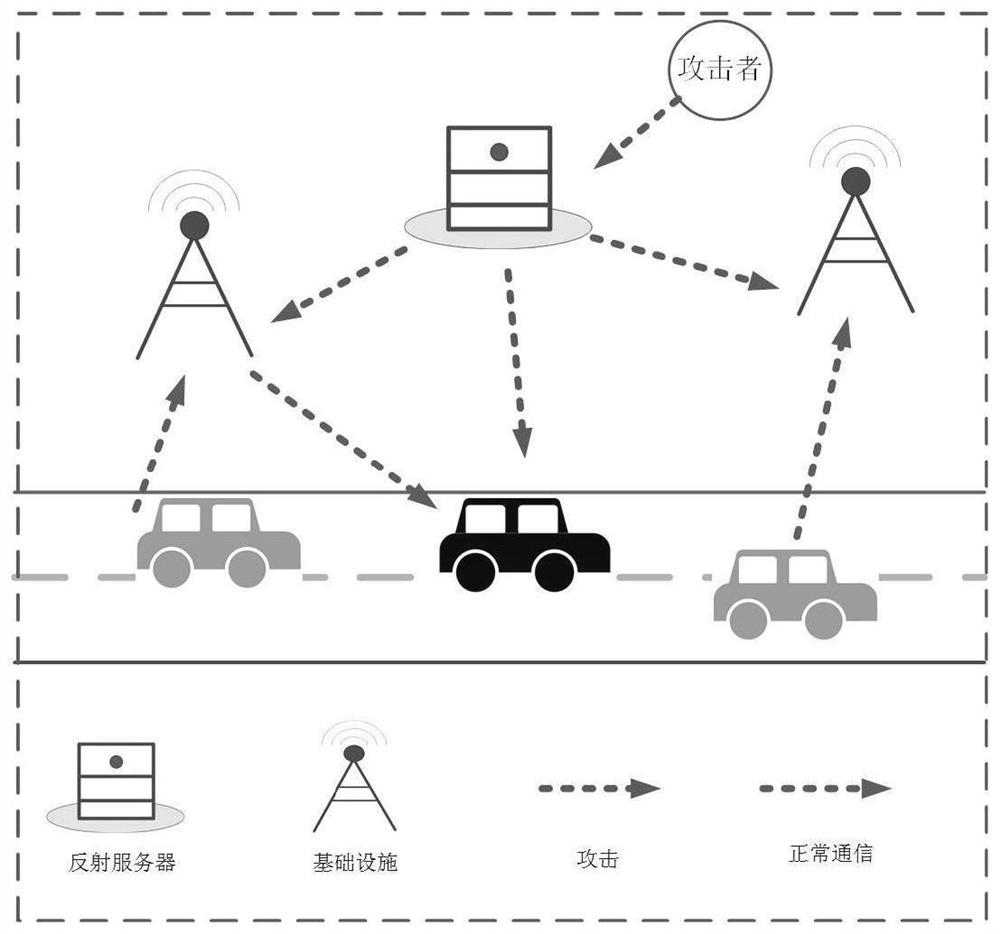
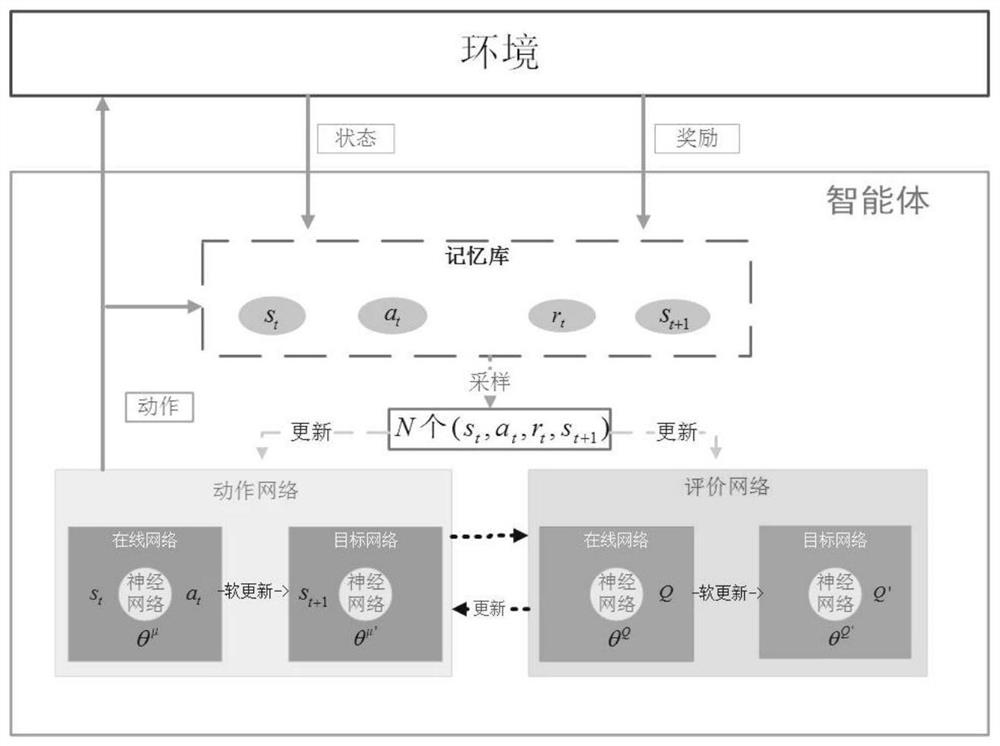
[0066] Such as figure 2 As shown, the attacker imposes DDoS attack on the infrastructure server side, we obtain the traffic data and calculate the statistical characteristics on the infrastructure server side, and then feed it back to the server manager, and the server manager uses the deep deterministic policy gradient method (such as image 3 shown) to calculate the predicted value of the traffic at the current moment, and then complete the intrusion detection of itself, so as to achieve the purpose of improving its own security.
[0067] Step 1: Collect traffic data on the infrastructure server side. The traffic data (X(t-100),...,X(t-1)) of the past 100 moments are divided into traffic data based on the TCP protocol (T(t-100),...,T( t-1)) and UDP-based traffic data (U(t-100),...,U(t-1)). Statistical features such as the mean, variance, and sparsity of traffic based on different protocols are calculated for the past 100 moments. The sparsity is the number of non-zero fl...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More