Patents
Literature
1294 results about "Intrusion detection system" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
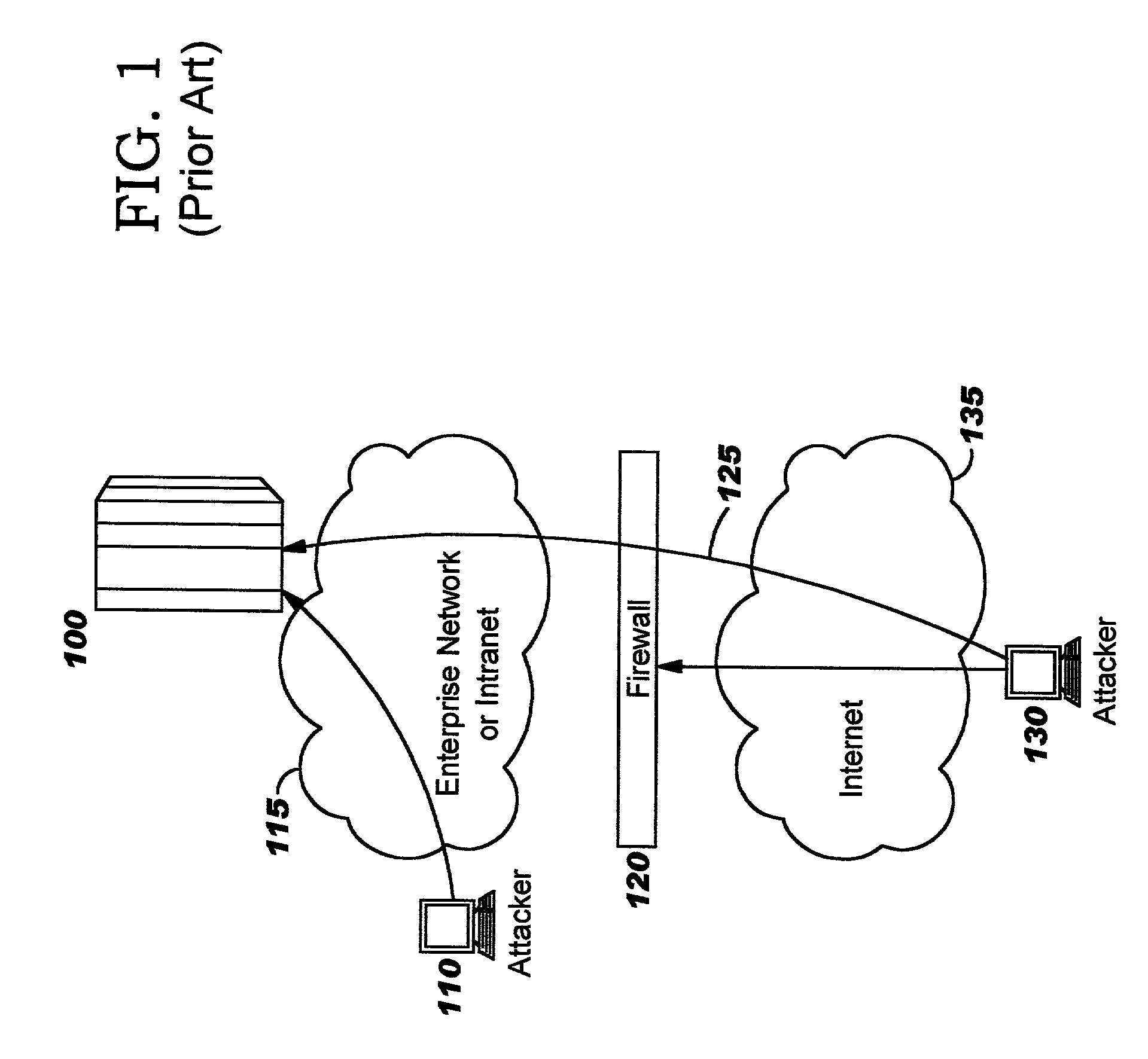
An intrusion detection system (IDS) is a device or software application that monitors a network or systems for malicious activity or policy violations. Any malicious activity or violation is typically reported either to an administrator or collected centrally using a security information and event management (SIEM) system. A SIEM system combines outputs from multiple sources and uses alarm filtering techniques to distinguish malicious activity from false alarms.
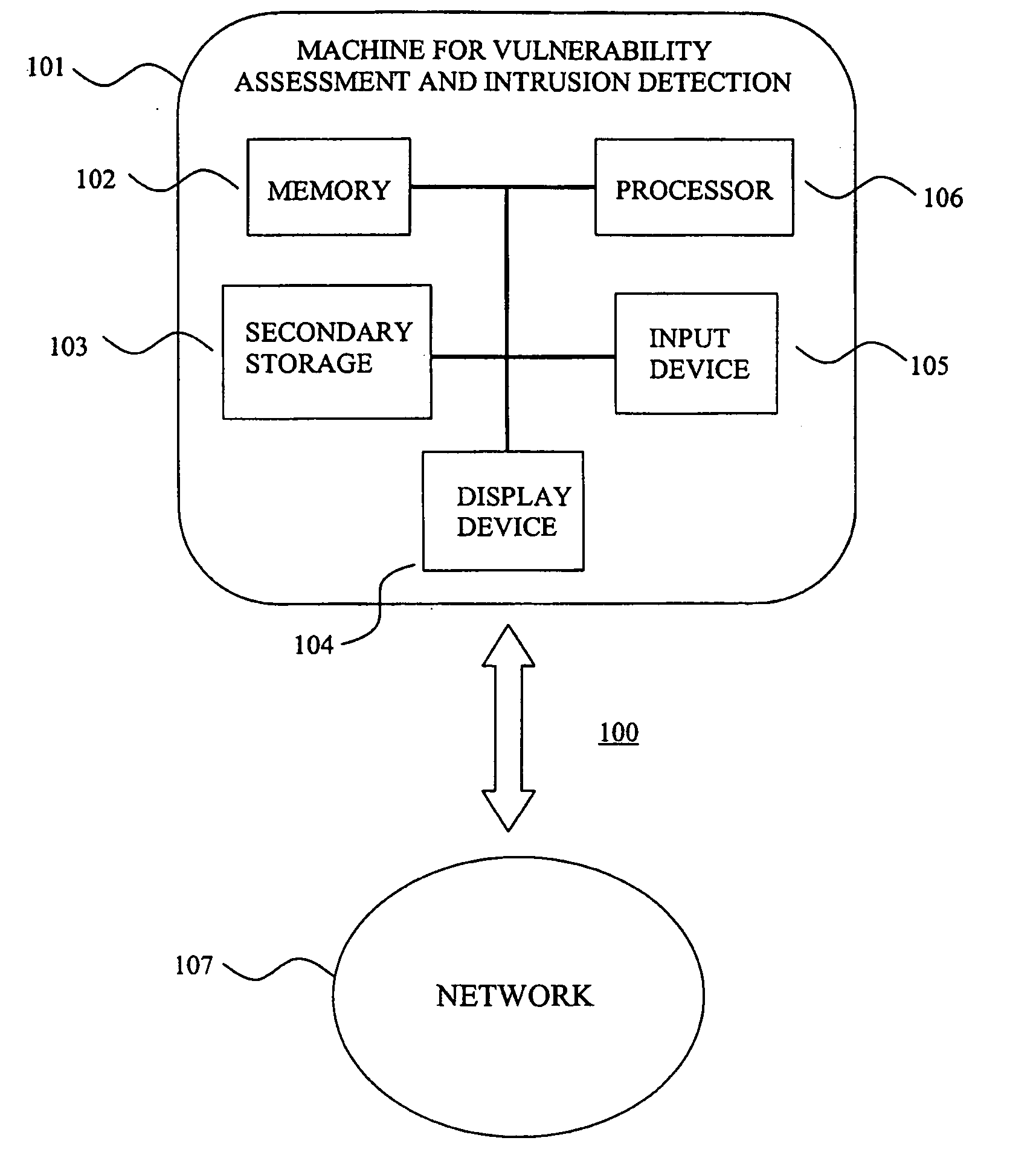
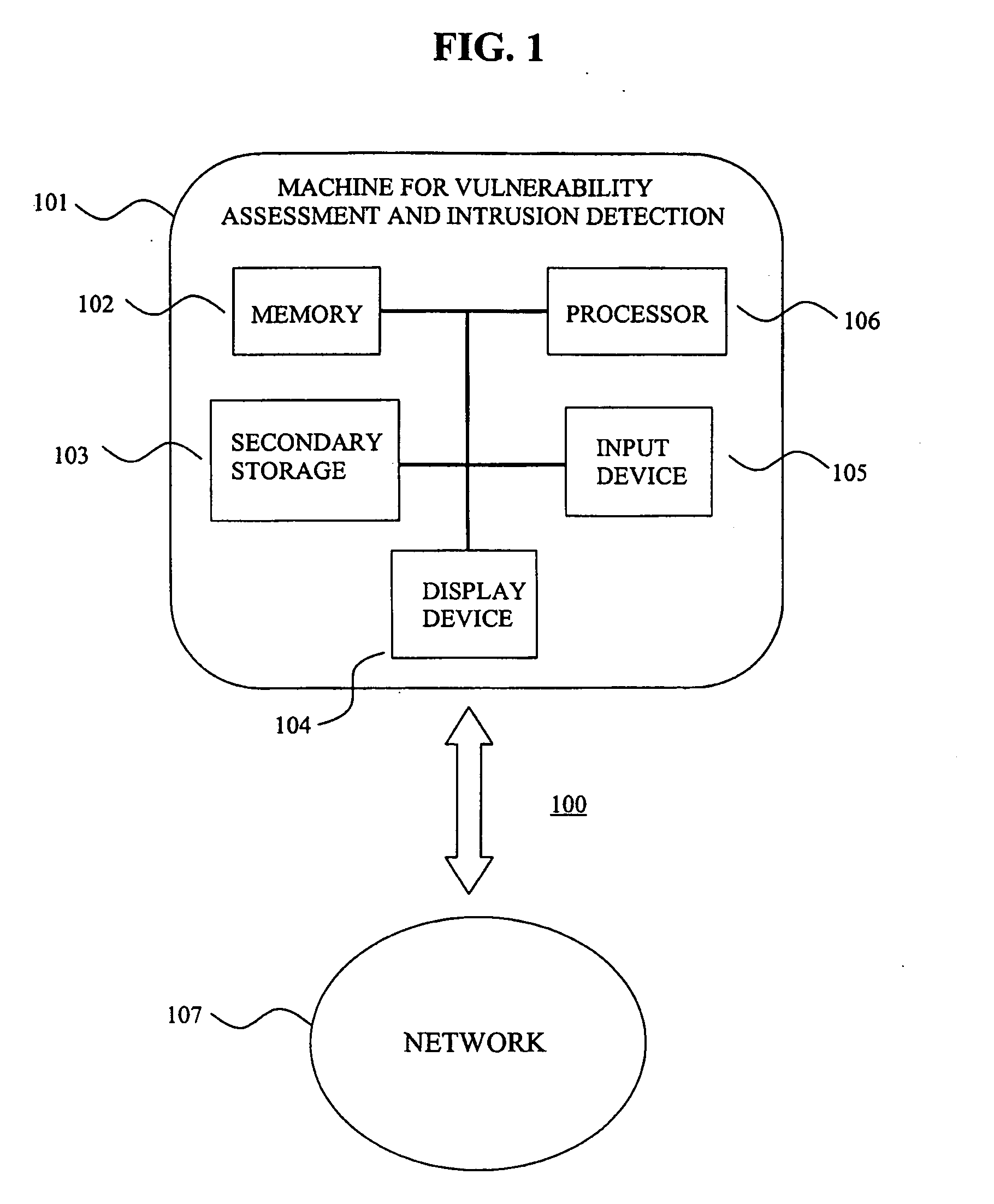
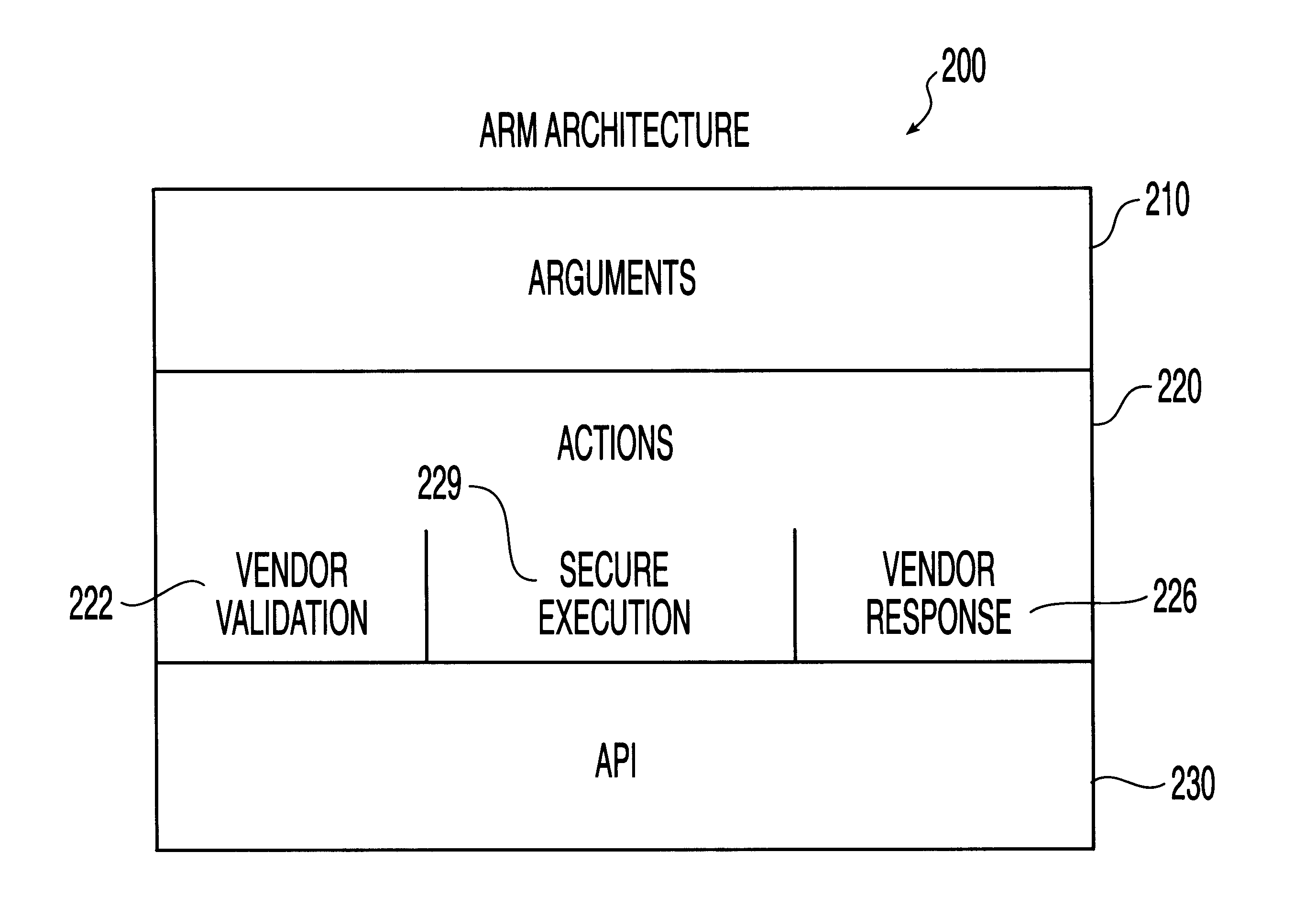
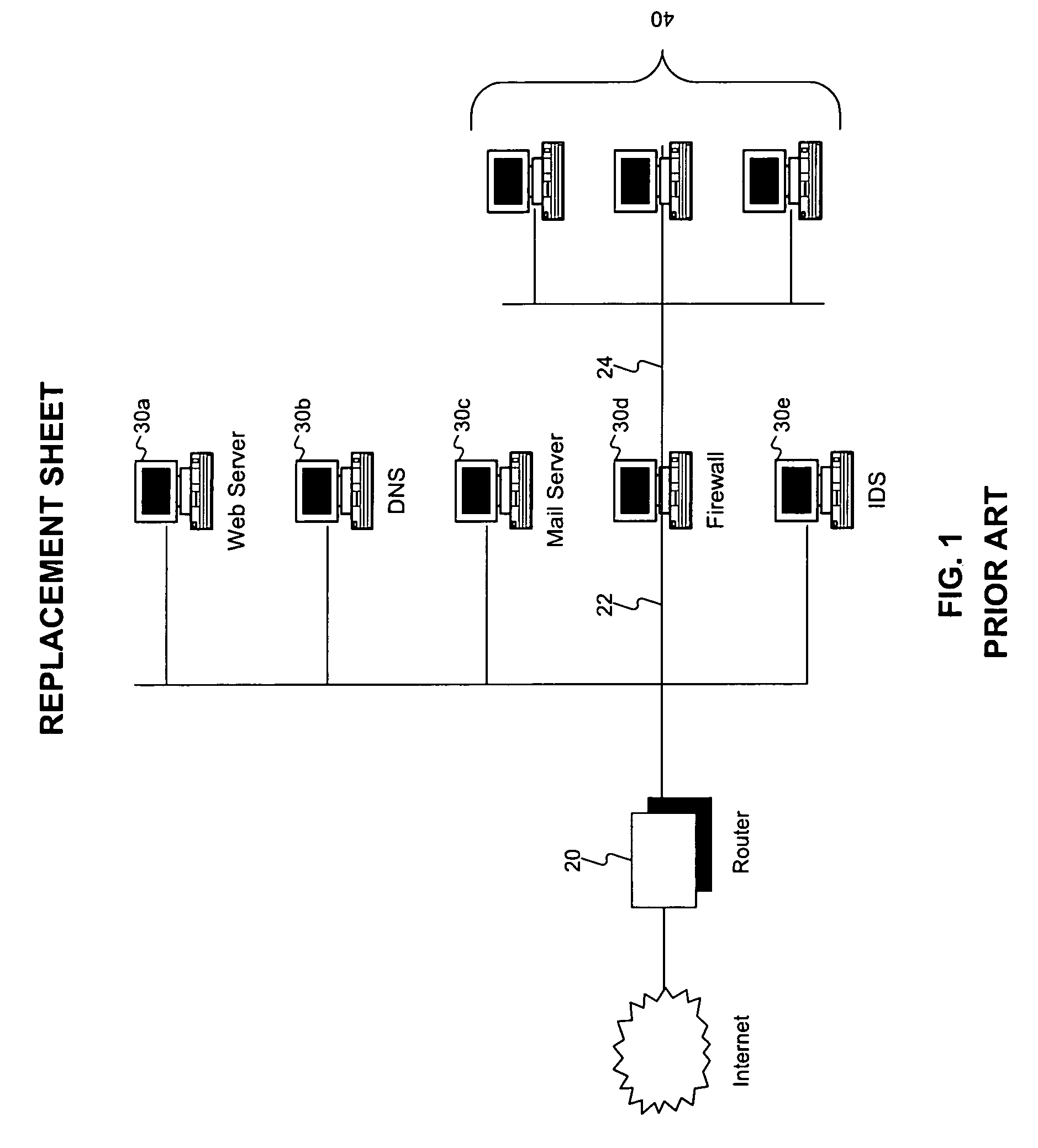
System for intrusion detection and vulnerability assessment in a computer network using simulation and machine learning
InactiveUS20060191010A1Memory loss protectionError detection/correctionComputer configurationData transmission
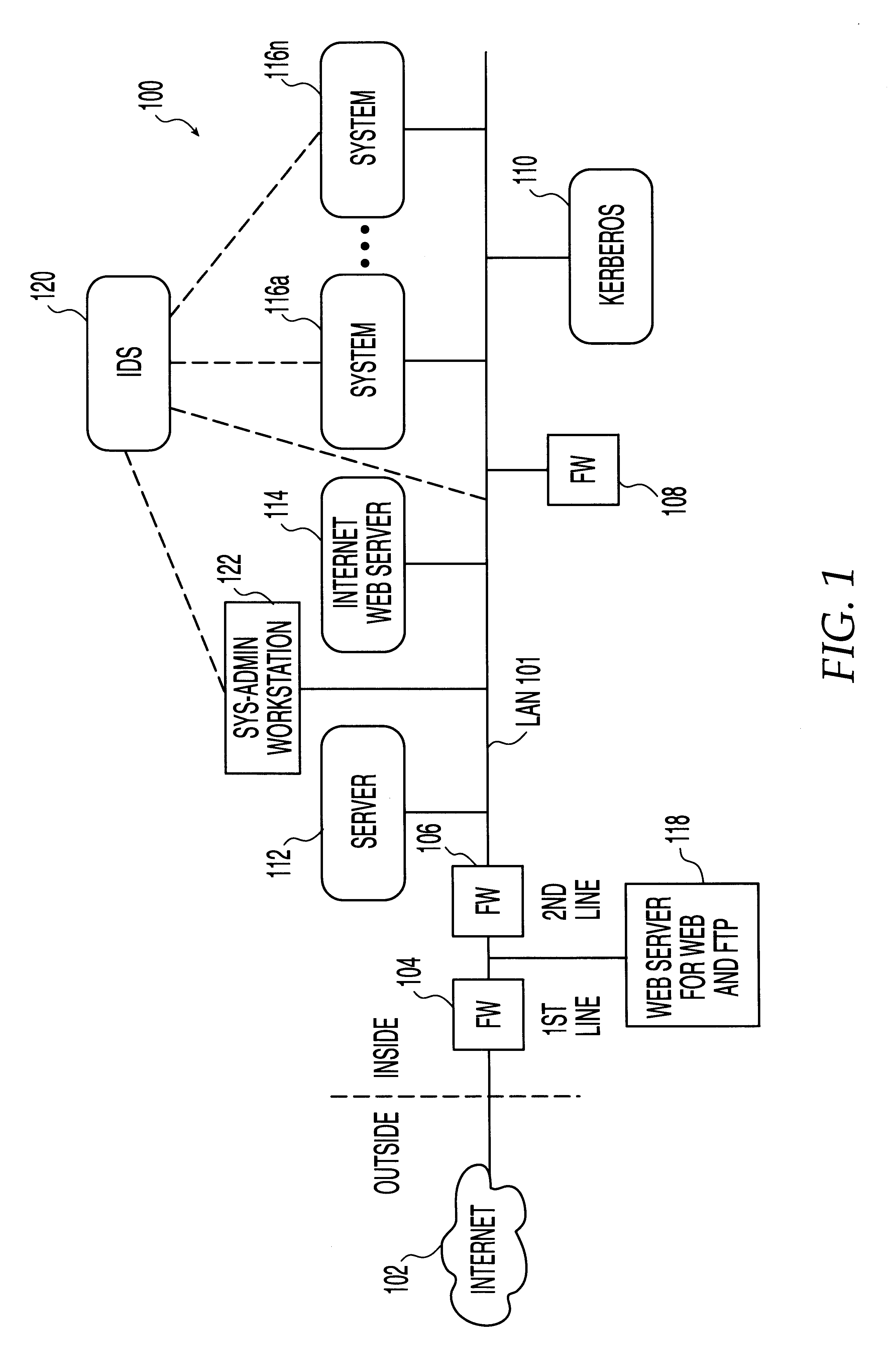
The present invention provides a system and method for predicting and preventing unauthorized intrusion in a computer configuration. Preferably, the invention comprises a communication network to which at least two computing devices connect, wherein at least one of the computing devices is operable to receive data transmitted by the other computing device. The invention further comprises a database that is accessible over the network and operable to store information related to the network. A vulnerability assessment component is provided that is operable to execute a command over the communication network, and a data monitoring utility operates to monitor data transmitted over the communication network as the vulnerability assessment component executes commands. Also, an intrusion detection component is included that is operable to provide a simulated copy of the network, to generate a first data transmission on the simulated copy of the network that represents a second data transmission on the communication network, and to compare the first data transmission with a second data transmission. The vulnerability assessment component preferably interfaces with the intrusion detection component to define rules associated with the first and second data transmissions, to store the rules in the database, and to retrieve the rules from the database in order to predict and prevent unauthorized intrusion in the computer configuration.
Owner:PACE UNIVERSITY
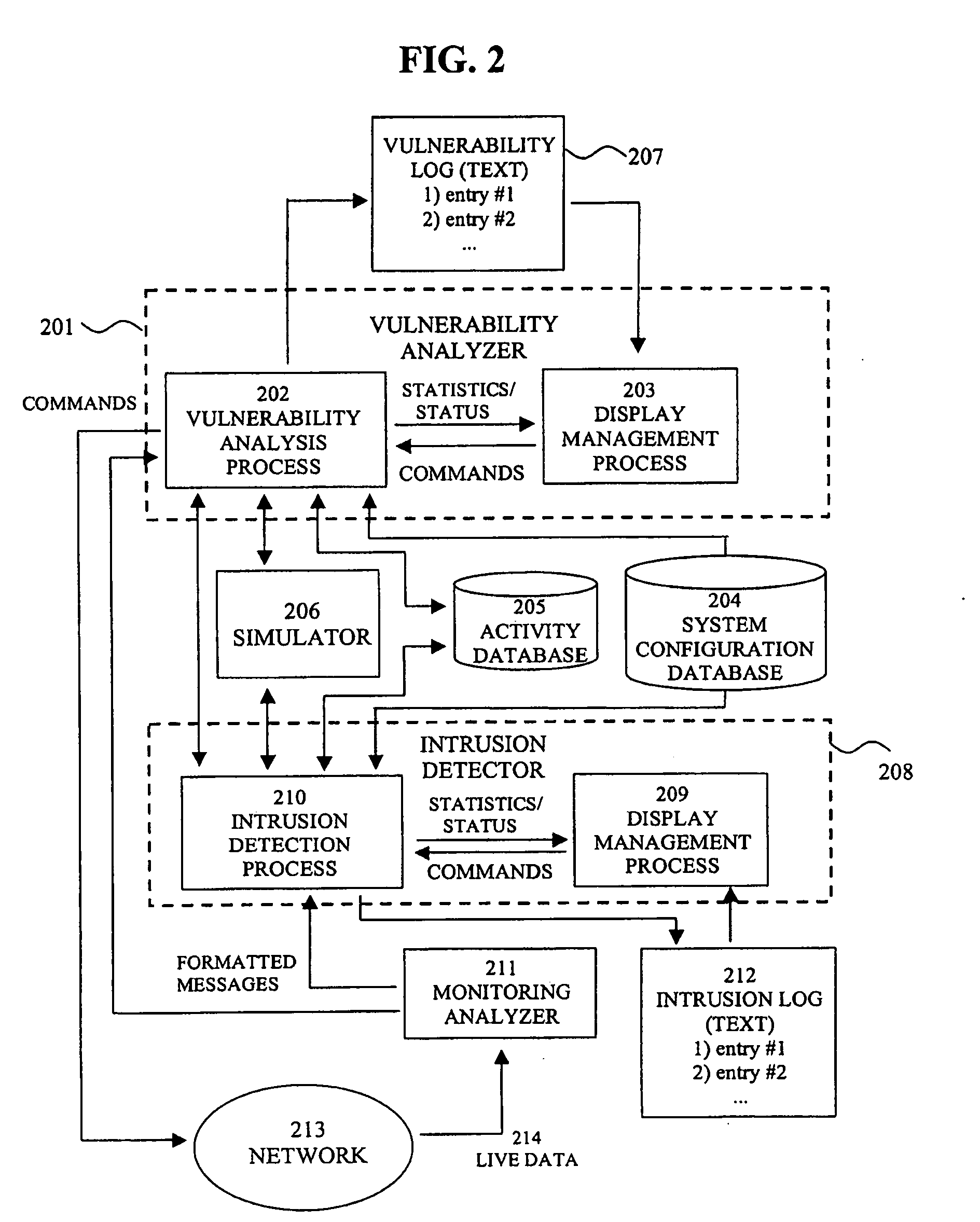
System, method and computer program product for automatic response to computer system misuse using active response modules
InactiveUS6275942B1Rapid responseMemory loss protectionDigital data processing detailsSoftware engineeringSecurity level
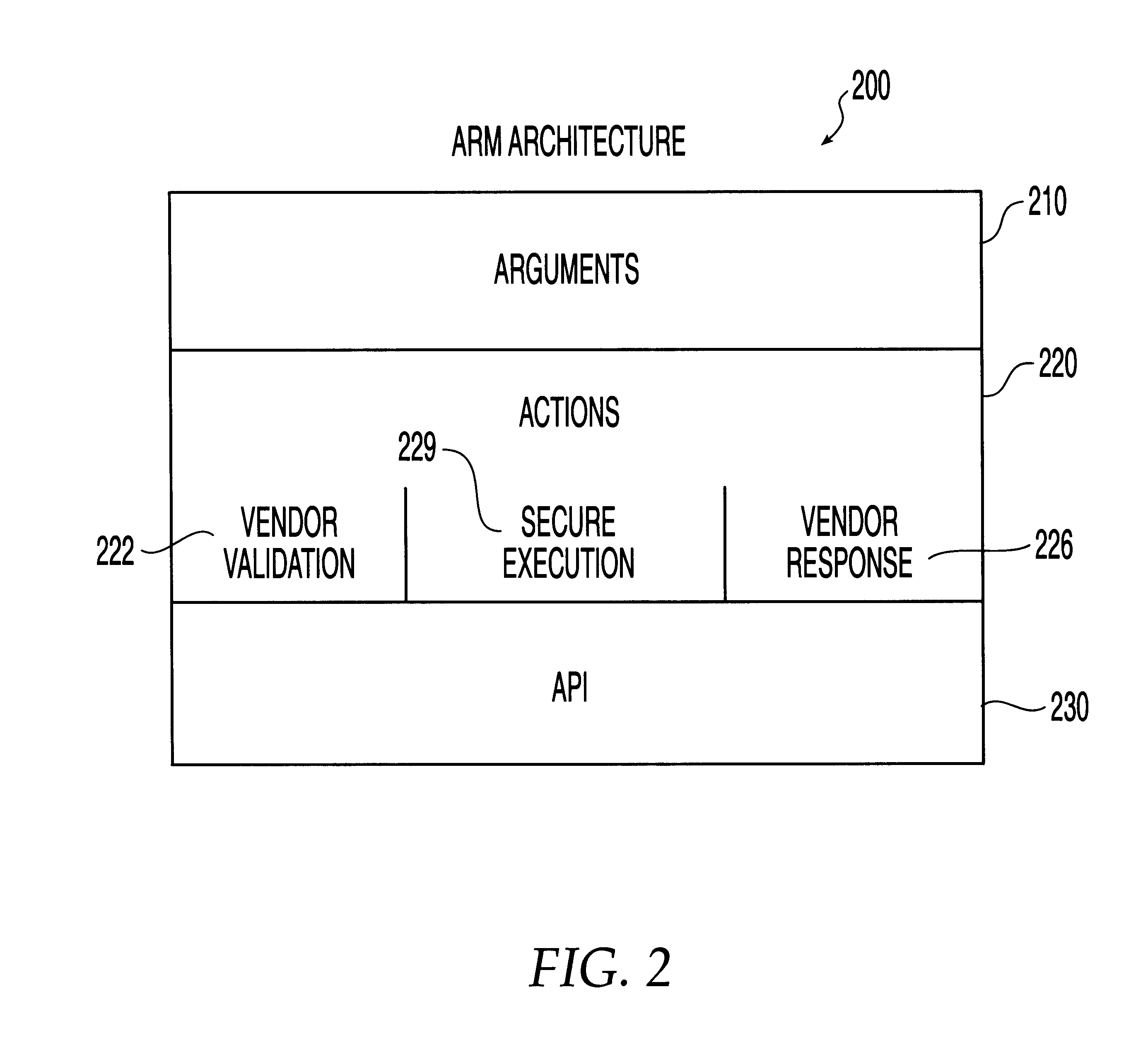
A system, method and computer program product for automatic response to computer system misuse using active response modules (ARMs). ARMs are tools that allow static intrusion detection system applications the ability to dynamically increase security levels by allowing real-time responses to detected instances of computer misuse. Several classes of ARMs exist which allow them to interface with several types of network elements found within a computing environment (e.g., firewalls, web servers, Kerberos severs, certificate authorities, etc.). The ARMs, once defined, are deployed in a "plug and play" manner into an existing intrusion detection system within a computing environment. A user (e.g., system administrator) may then configure the ARMs by linking them to specific computer misuses. Upon receipt of an instance of the computer misuse from the intrusion detection system, each ARM linked to the misuse collects pertinent data from the intrusion detection system and invokes a response specified by the ARM class and the collected pertinent data.
Owner:MCAFEE LLC +1
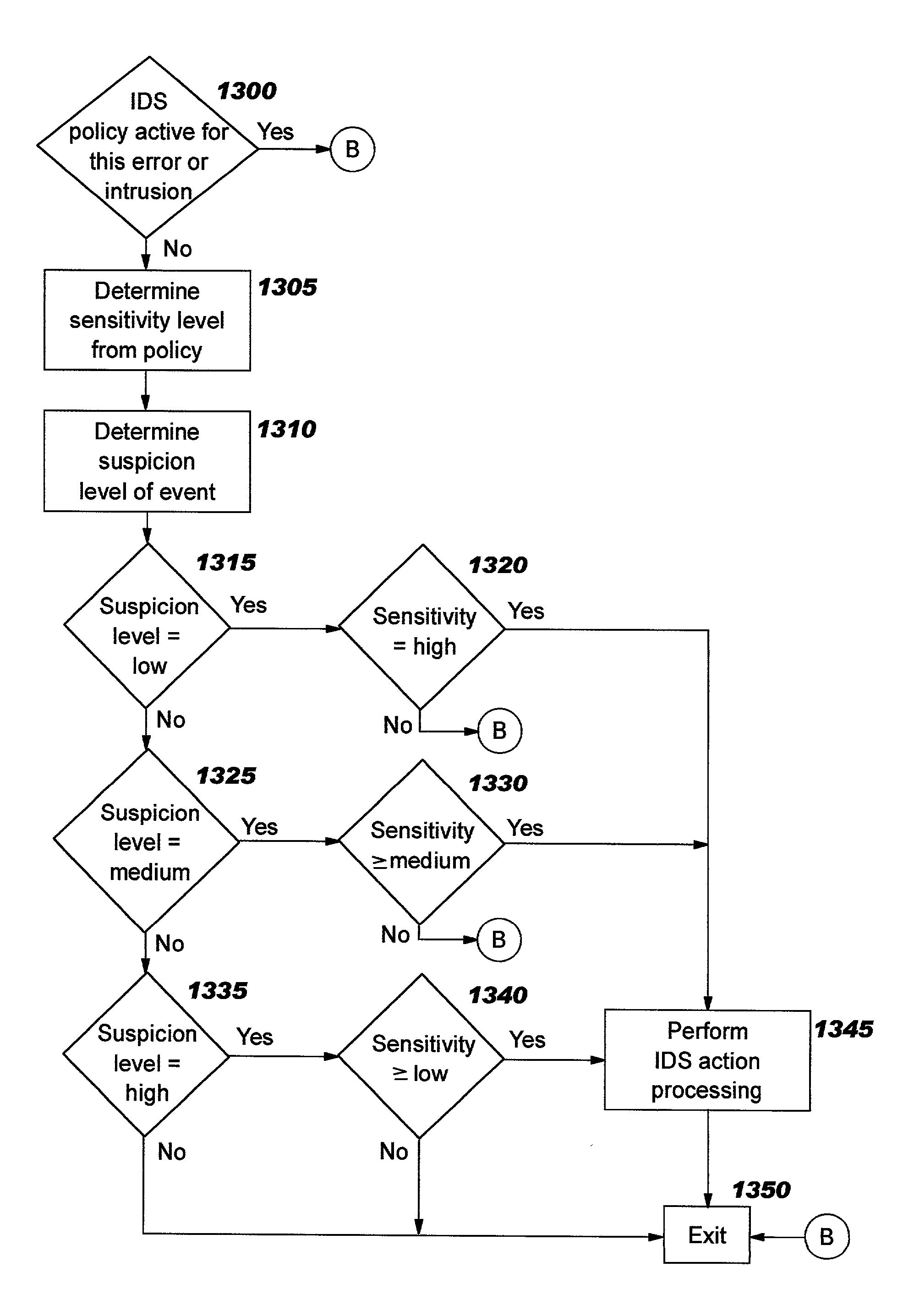
Intrusion event filtering and generic attack signatures
ActiveUS20030145225A1Memory loss protectionError detection/correctionGeneric attackIntrusion detection system
Improvements in intrusion detection are disclosed by providing intrusion event filtering and / or generic attack signature processing. These services may be integrated into a system or server that is the potential target of attack, or alternatively may be implemented in a network device. Filtering may be provided using sensitivity levels and suspicion levels. Generic attack signatures describe relatively broad classes of intrusions. Intrusion detection policy information may be used to direct the actions to be taken upon detecting an attack.
Owner:TREND MICRO INC
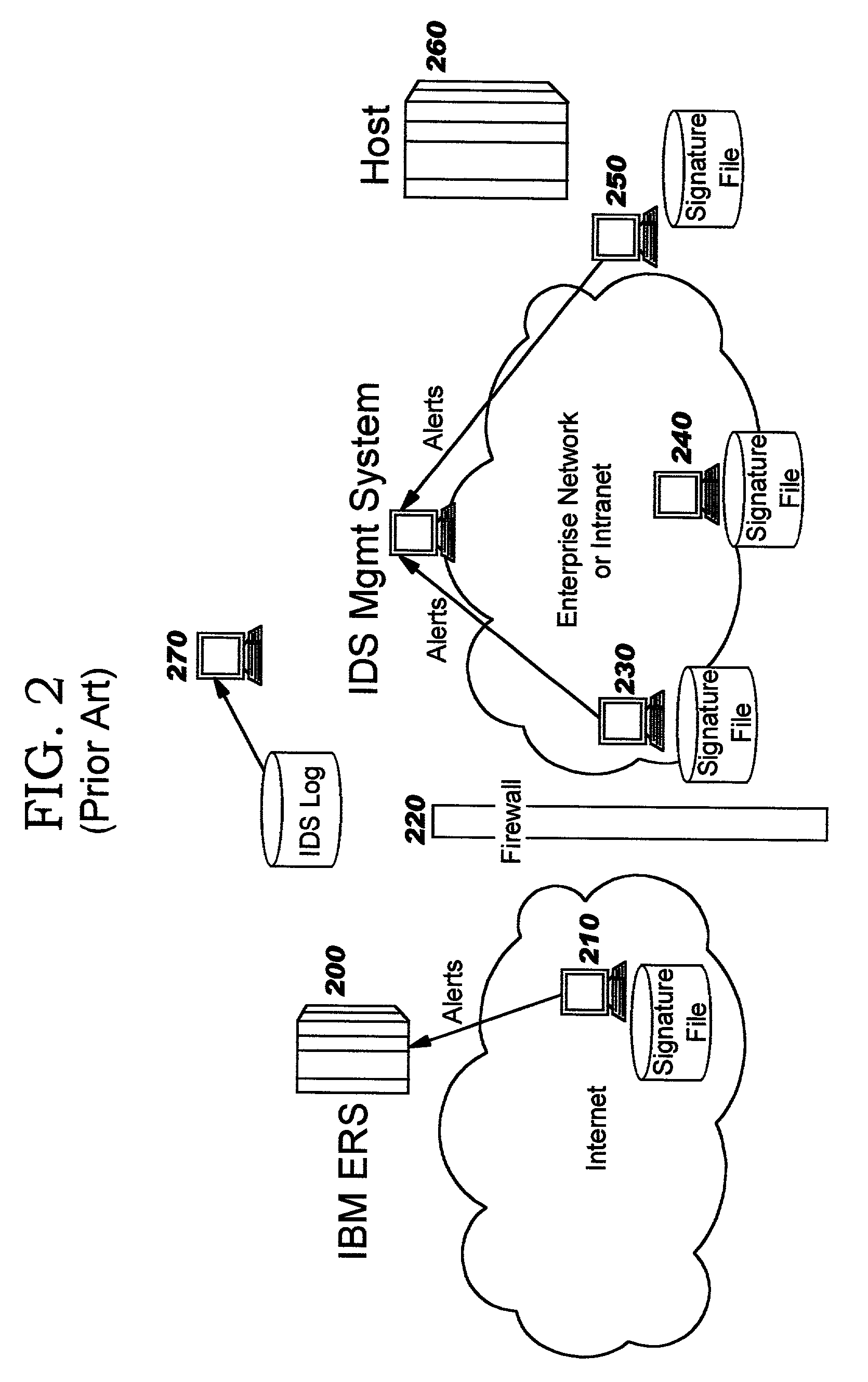
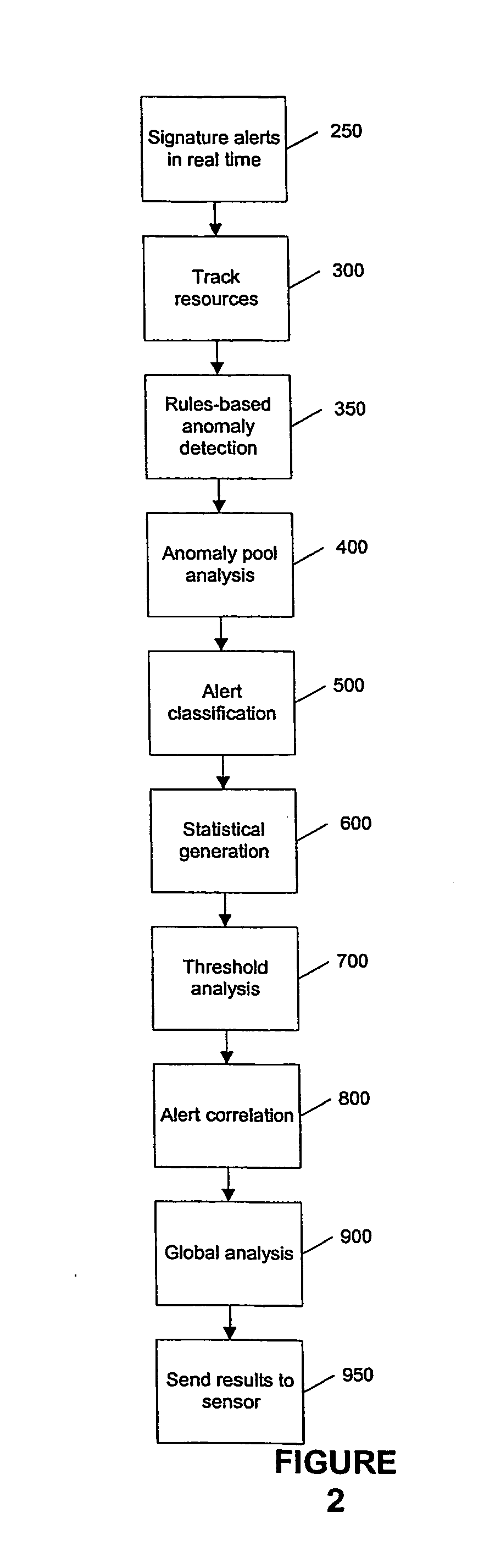
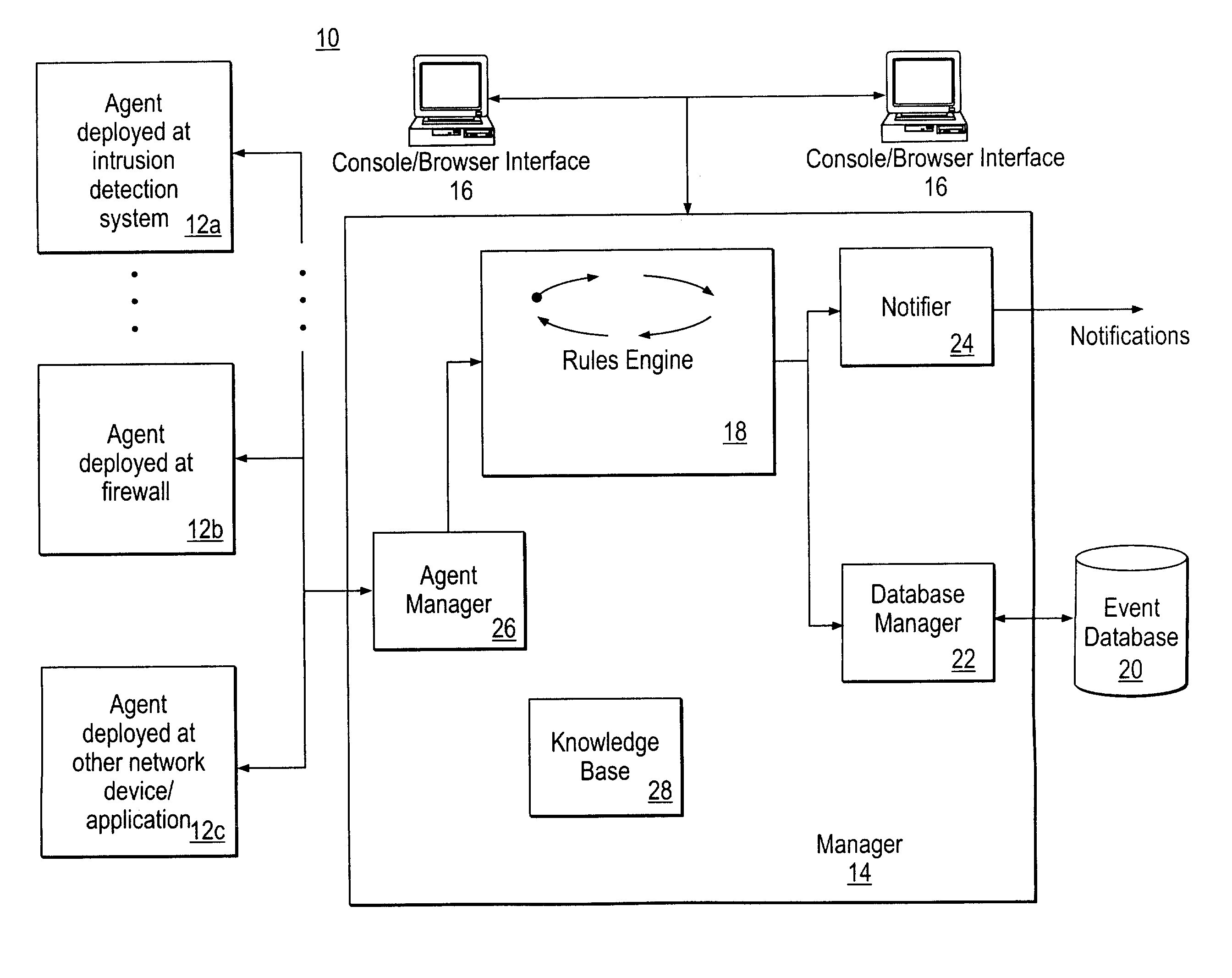
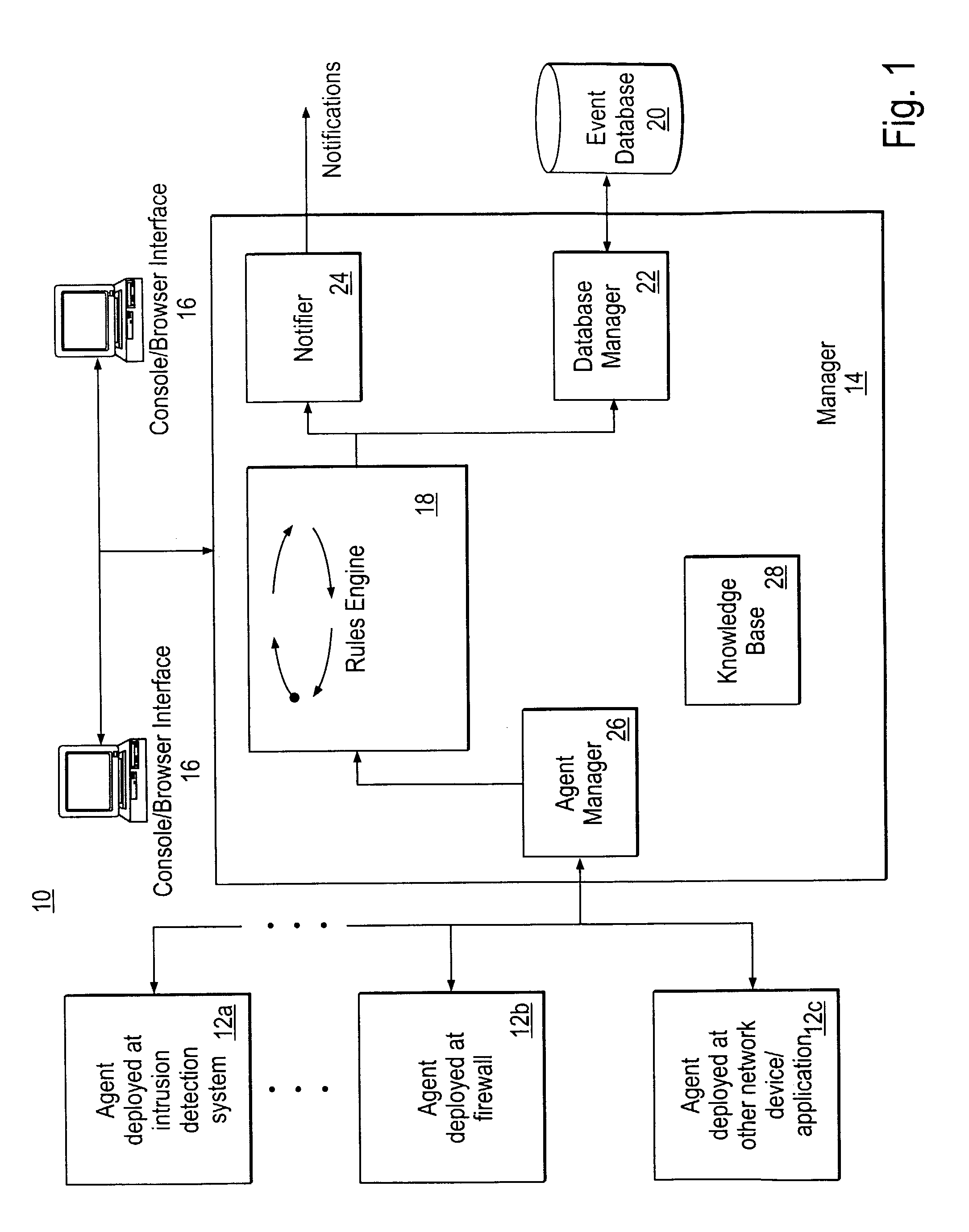
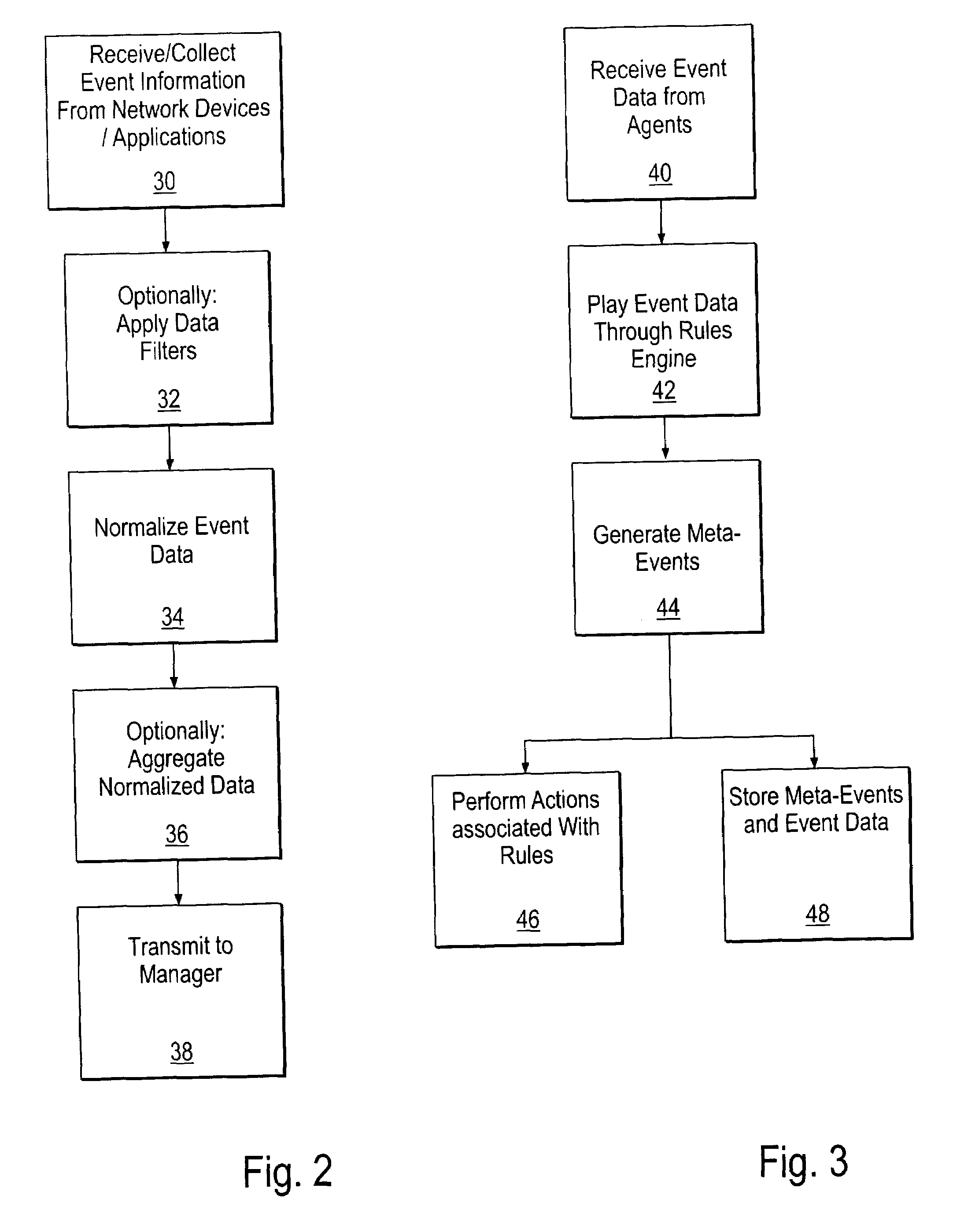
Method and System for Managing Computer Security Information
InactiveUS20020078381A1Efficient managementReduce processing speedMemory loss protectionDigital data processing detailsTraffic capacitySafety management systems
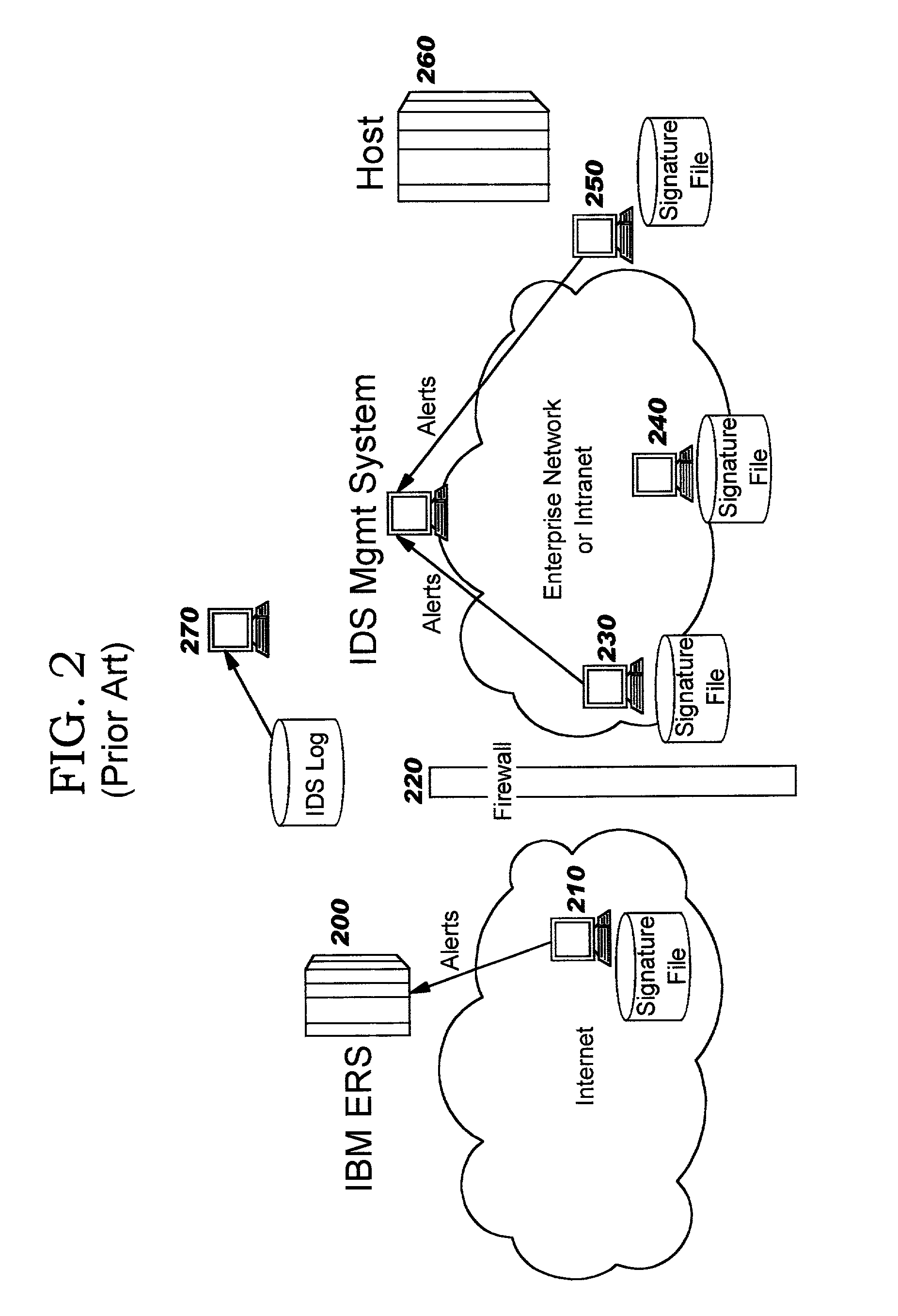
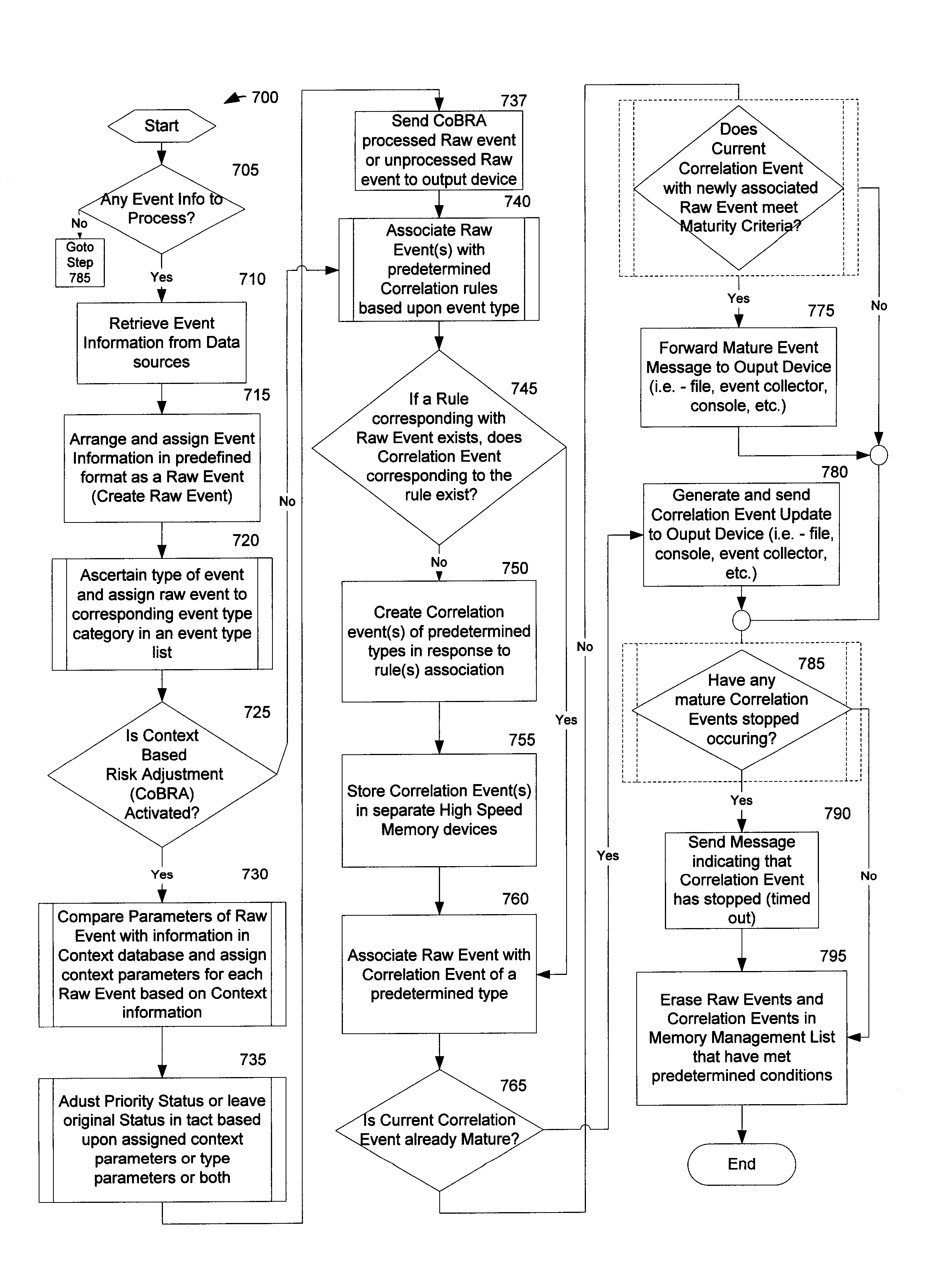
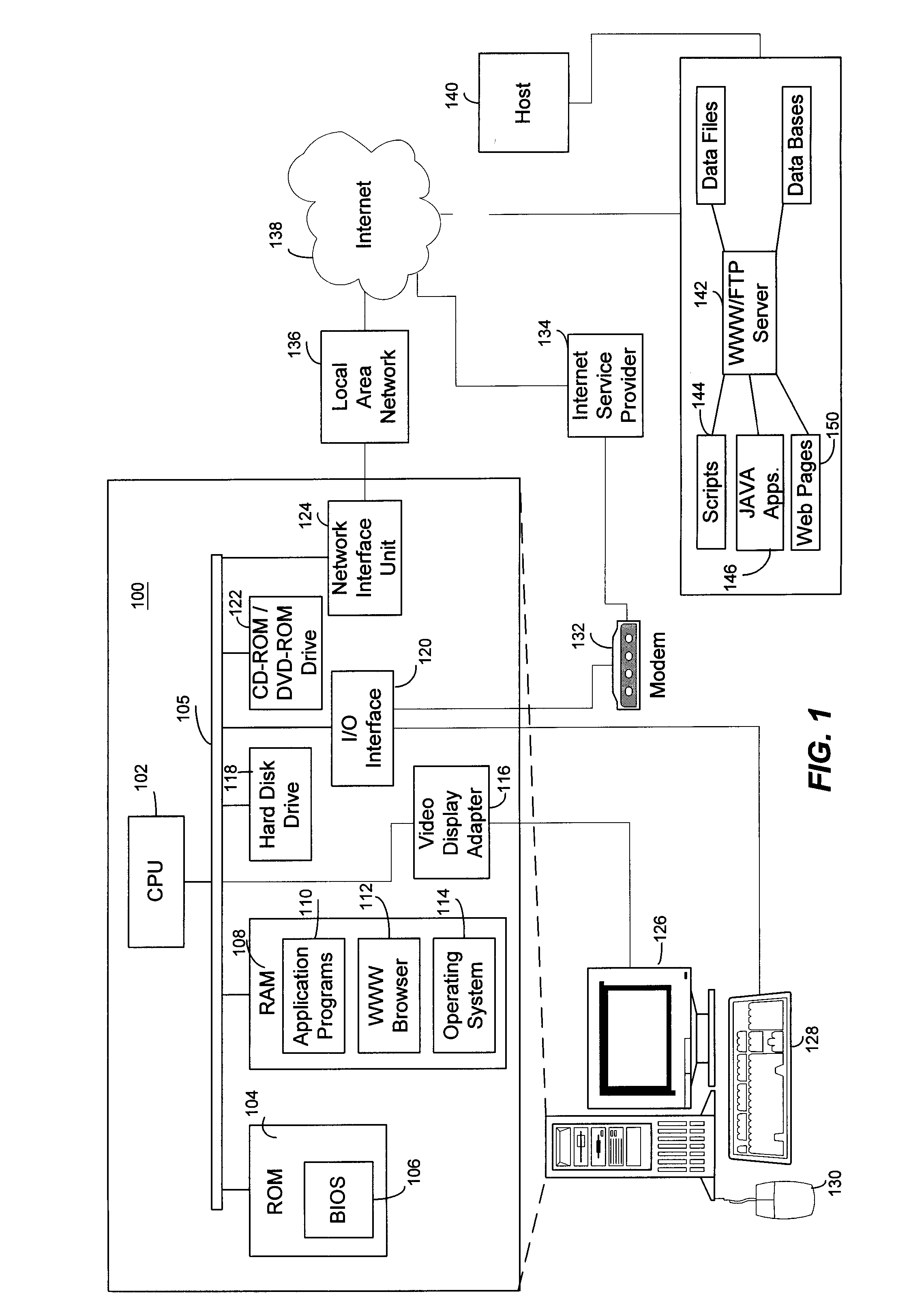
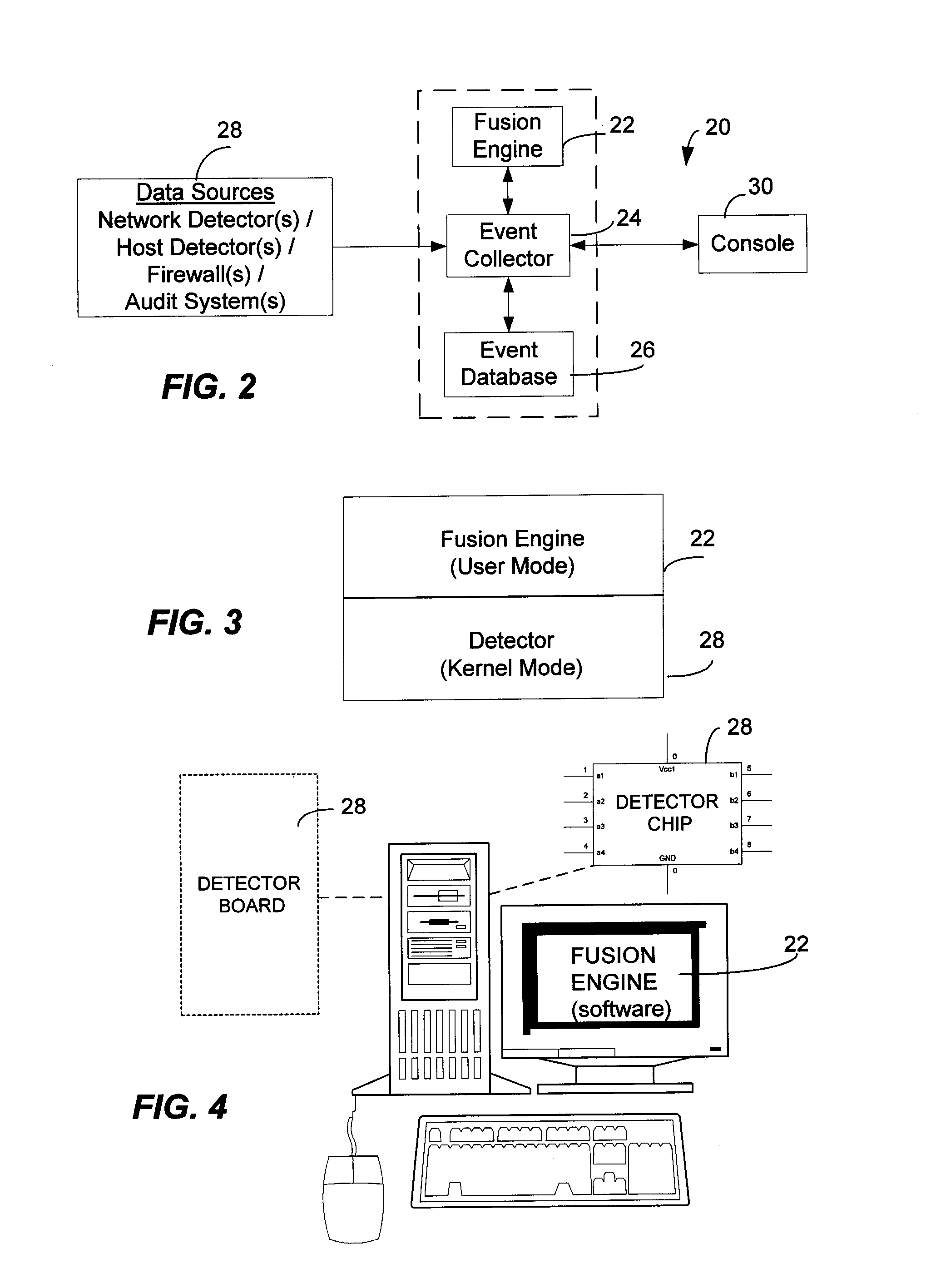
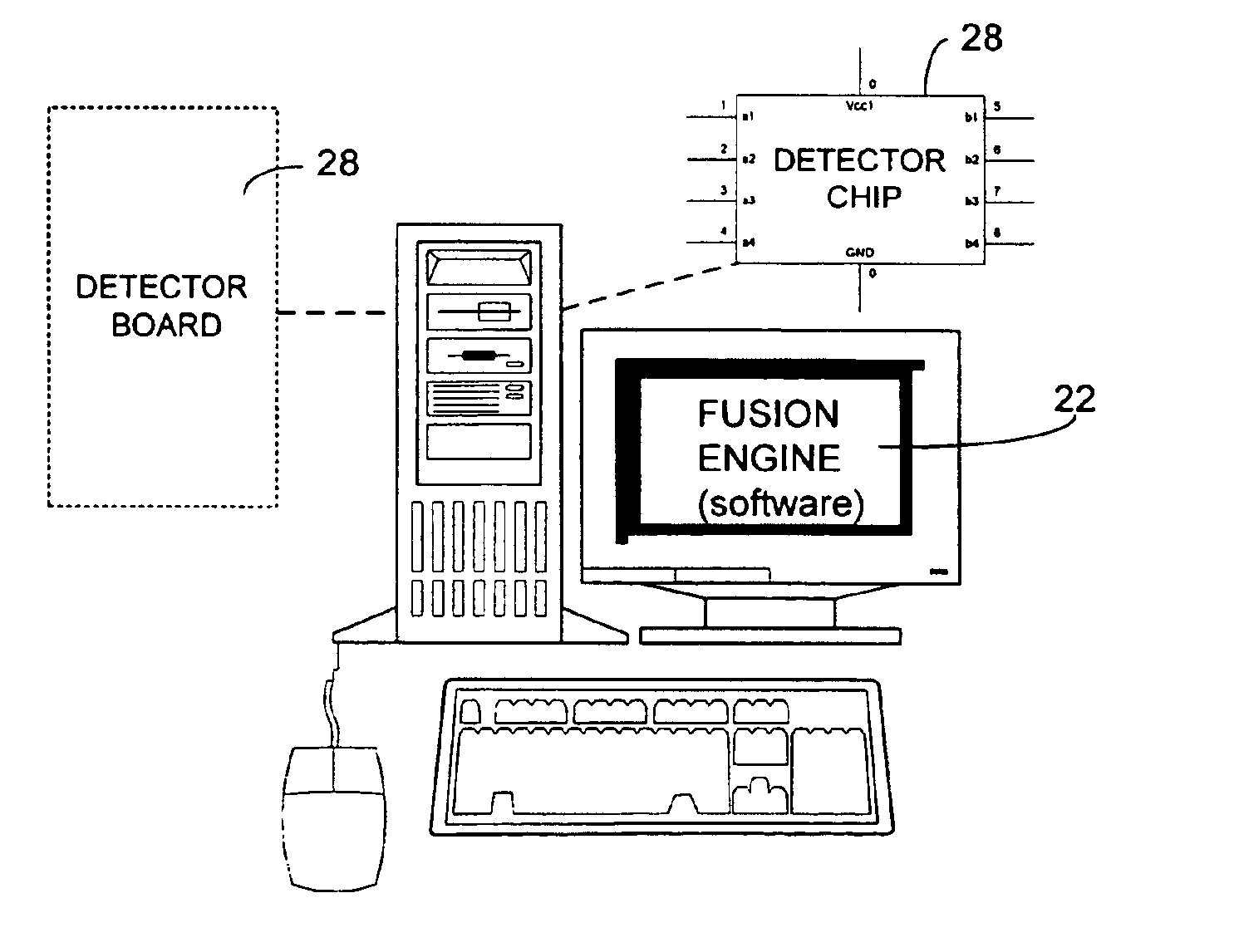
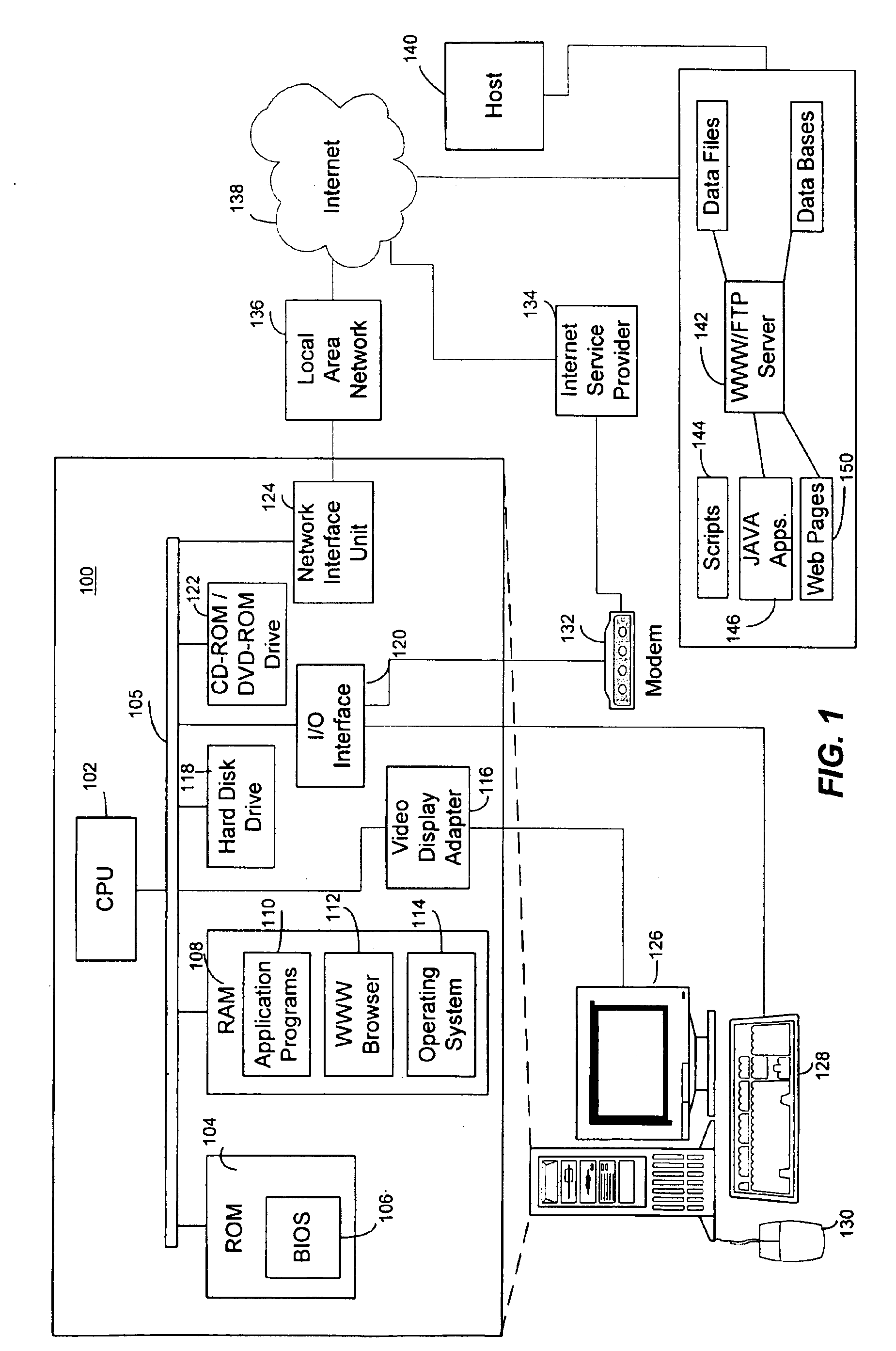
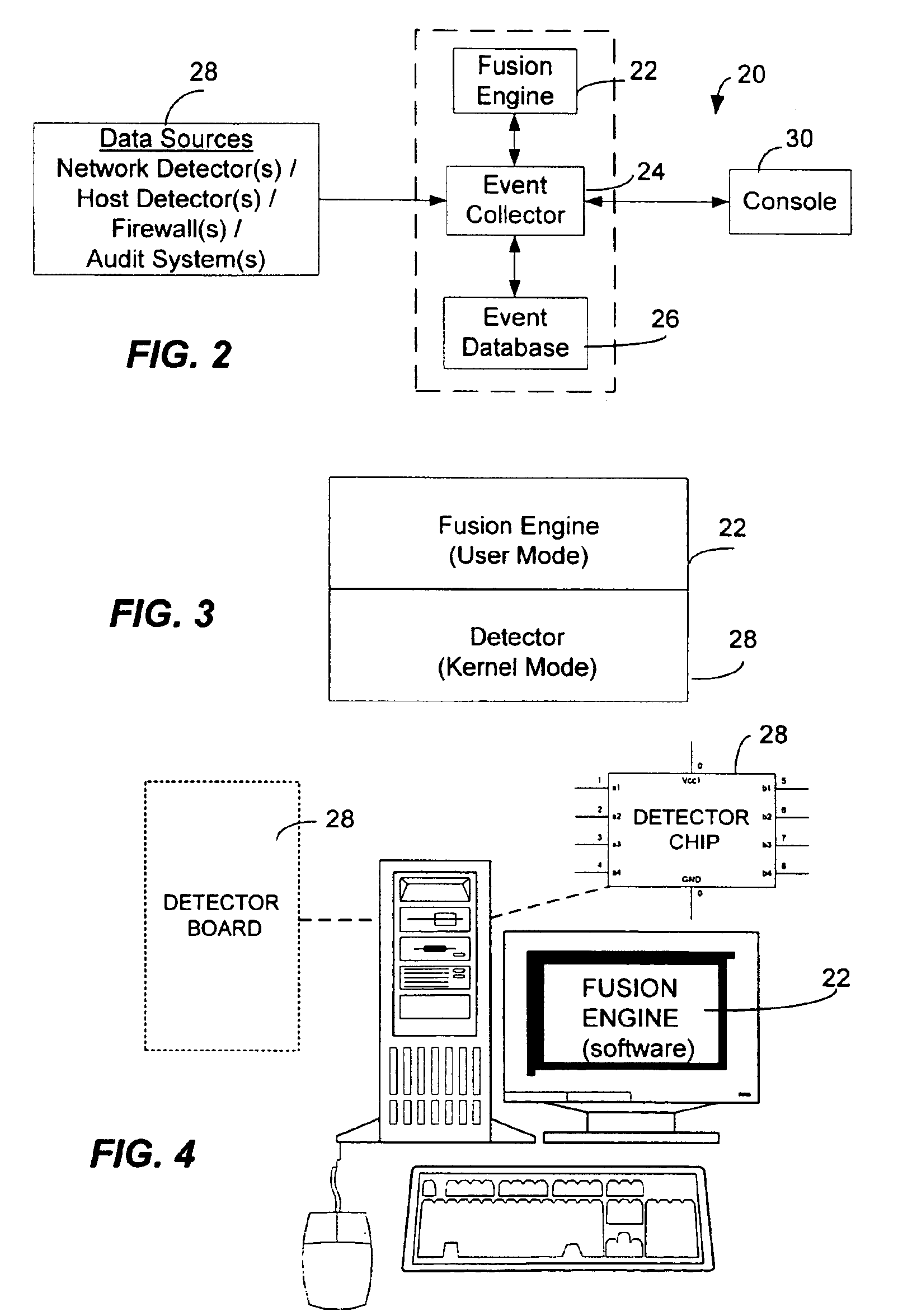
<heading lvl="0">Abstract of Disclosure< / heading> A security management system includes a fusion engine which "fuses" or assembles information from multiple data sources and analyzes this information in order to detect relationships between raw events that may indicate malicious behavior and to provide an organized presentation of information to consoles without slowing down the processing performed by the data sources. The multiple data sources can comprise sensors or detectors that monitor network traffic or individual computers or both. The sensors can comprise devices that may be used in intrusion detection systems (IDS). The data sources can also comprise firewalls, audit systems, and other like security or IDS devices that monitor data traffic in real-time. The present invention can identify relationships between one or more real-time, raw computer events as they are received in real-time. The fusion engine can also assess and rank the risk of real-time raw events as well as mature correlation events.
Owner:IBM CORP
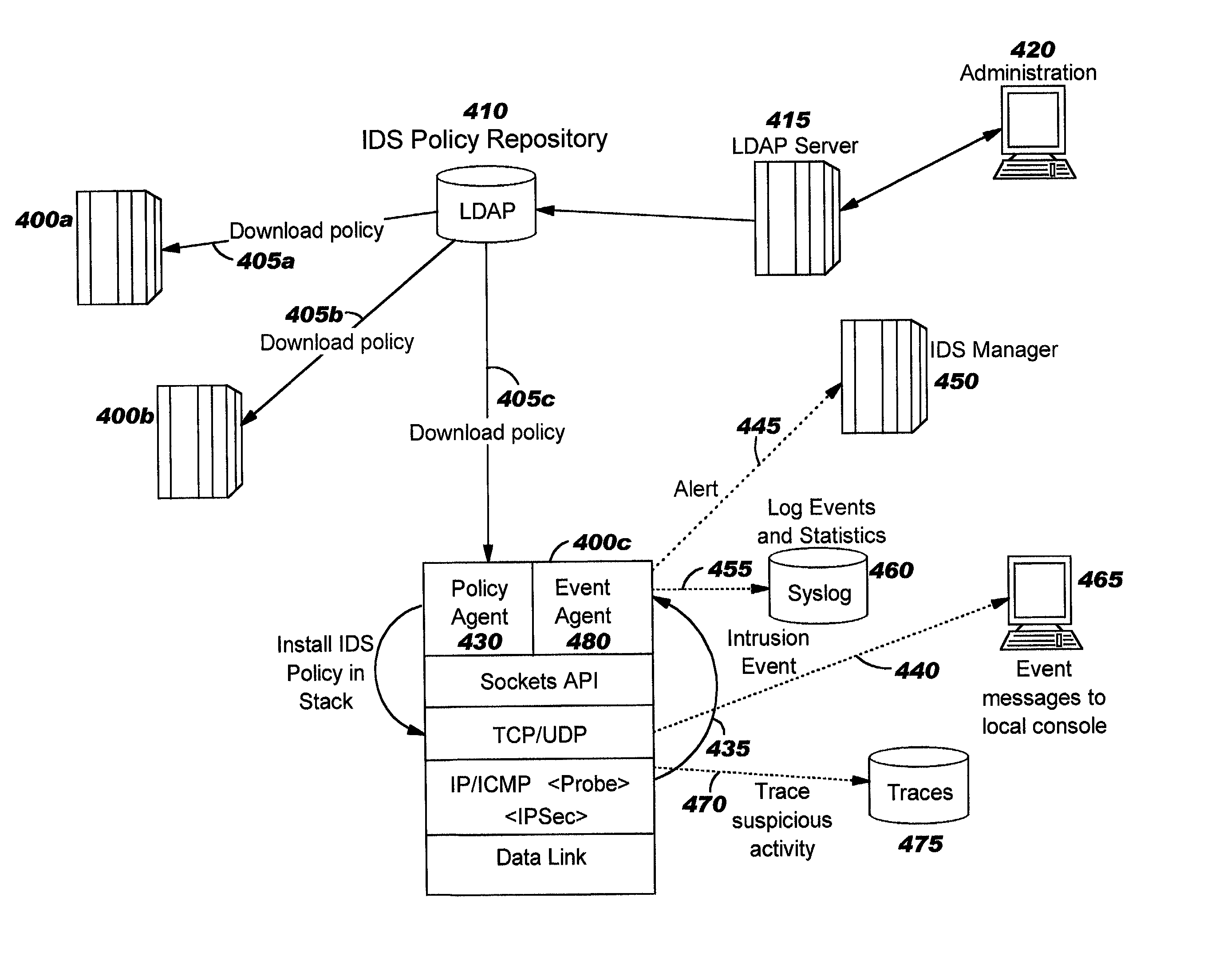
Integrated intrusion detection services
ActiveUS20030145226A1Memory loss protectionDigital computer detailsService improvementContext specific
Improvements in intrusion detection are disclosed by providing integrated intrusion detection services. Preferably, these services are integrated into a system or server that is the potential target of attack. Stack-based security processing is leveraged for access to cleartext data within the layers of the protocol stack. Layer-specific attacks may therefore be processed efficiently. Evaluation of incoming traffic for an intrusion is preferably performed only after an error condition of some type has been detected. This approach reduces the overhead of intrusion detection by reducing the number of packets to be inspected, and at the same time allows more efficient packet inspection through use of context-specific information that may be used to direct the inspection to particular candidate attacks. Generic attack class capability is also disclosed. Intrusion detection policy information may be used to direct the actions to be taken upon detecting an attack.
Owner:TREND MICRO INC
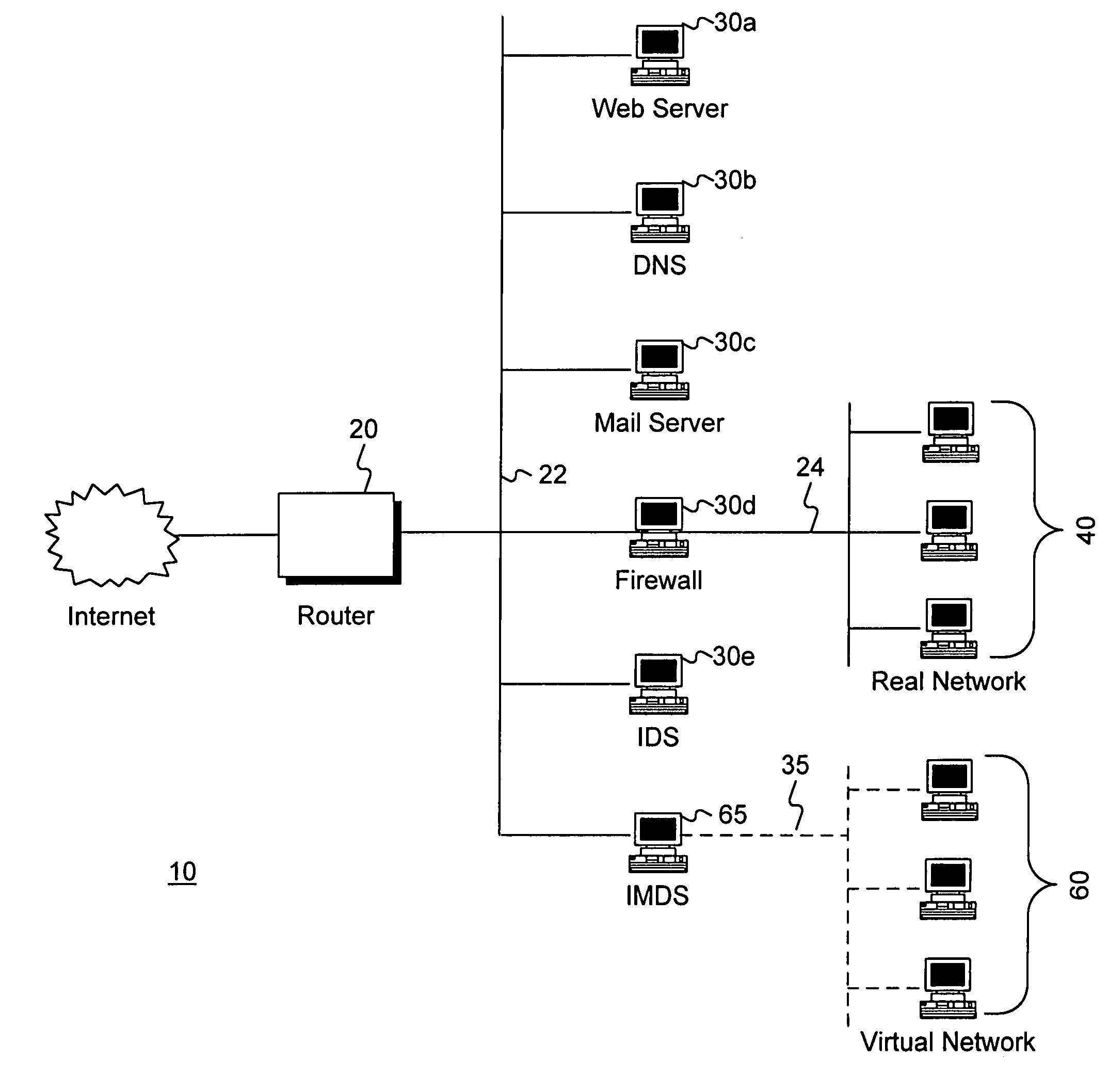
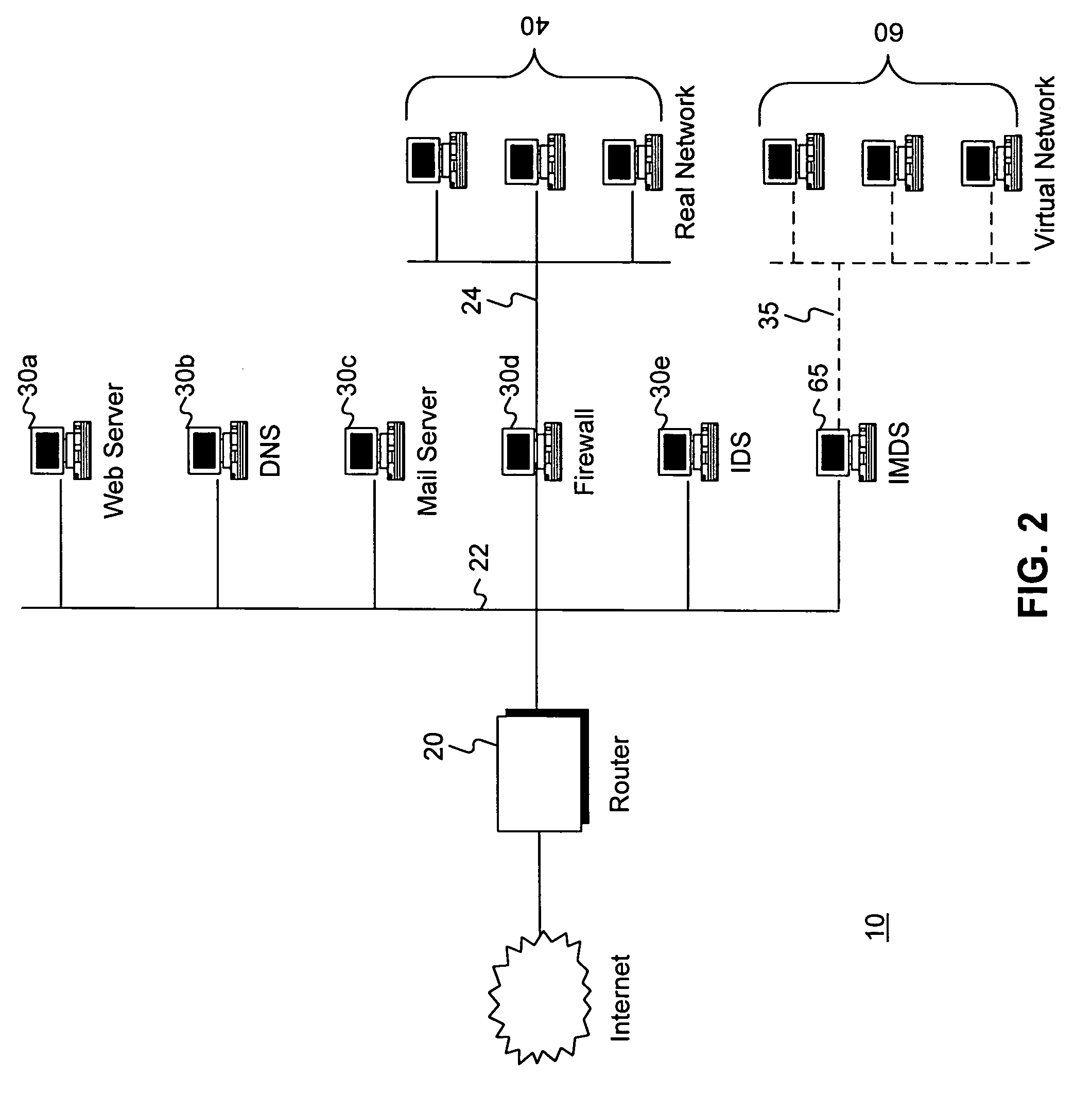
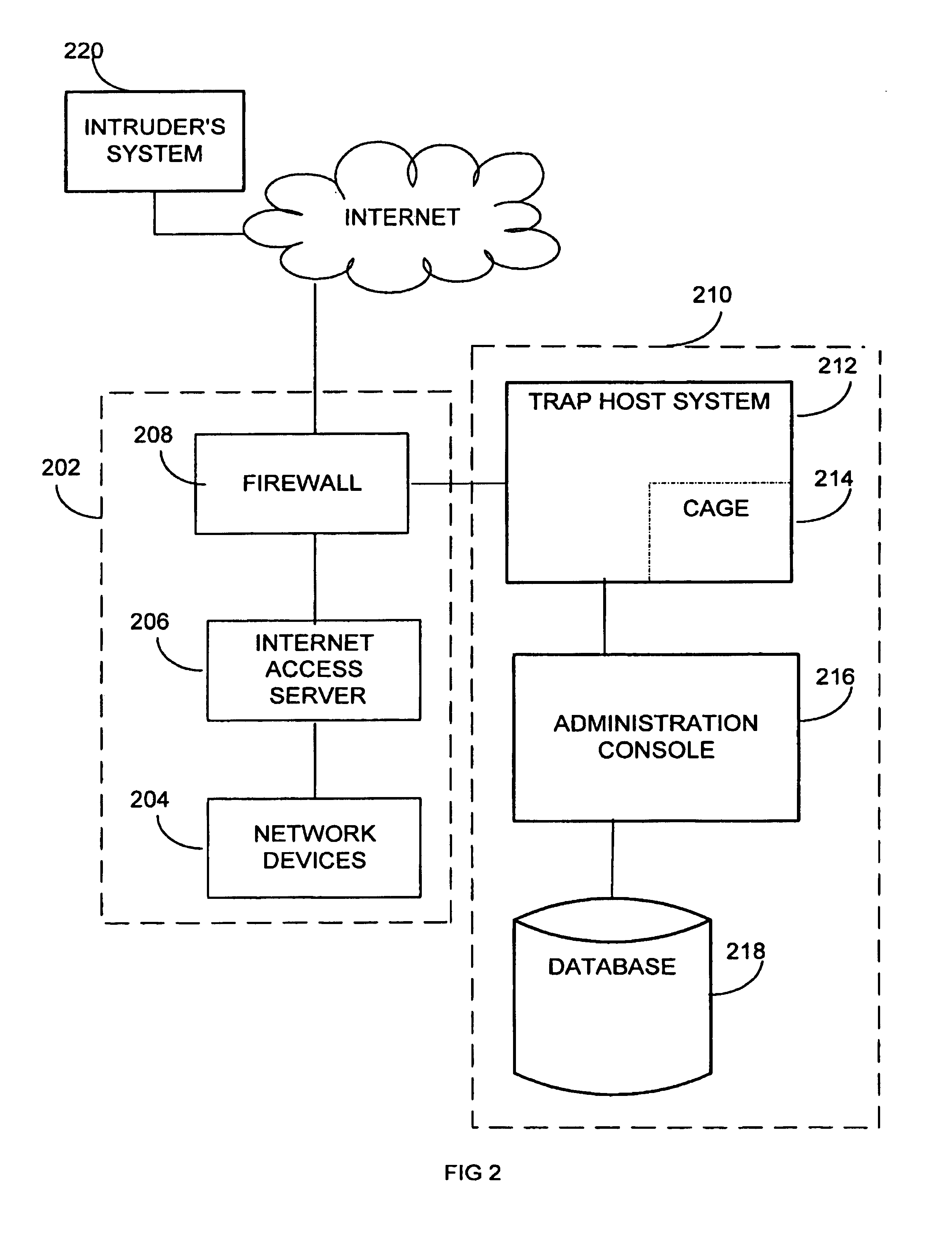
Intrusion and misuse deterrence system employing a virtual network
InactiveUS7240368B1Improve securityEasy to implementMemory loss protectionError detection/correctionIp addressBandwidth limitation
A method and apparatus is disclosed for increasing the security of computer networks through the use of an Intrusion and Misuse Deterrence System (IMDS) operating on the network. The IMDS is a system that creates a synthetic network complete with synthetic hosts and routers. It is comprised of a network server with associated application software that appears to be a legitimate portion of a real network to a network intruder. The IMDS consequently invites inquiry and entices the intruder away from the real network. Simulated services are configured to appear to be running on virtual clients with globally unique, class “C” IP addresses. Since there are no legitimate users of the virtual network simulated by the IMDS, all such activity must be inappropriate and can be treated as such. Consequently, the entire set of transactions by an intruder can be collected and identified rather than just those transactions that meet a predefined attack profile. Also, new exploits and attacks are handled just as effectively as known attacks, resulting in better identification of attack methodologies as well as the identification and analysis of new attack types. Since the IMDS only has to be concerned with the traffic going to its simulated hosts it additionally eliminates the bandwidth limitation that plagues a traditional intrusion detection system (IDS).
Owner:VERIZON SERVICES GROUP +2
Adaptive behavioral intrusion detection systems and methods
ActiveUS20050044406A1Increase opportunitiesMicrobiological testing/measurementDigital data processing detailsApplication serverInternet traffic
Systems and methods for analyzing historical network traffic and determining which traffic does not belong in a network are disclosed. Intrusion detection is performed over a period of time, looking for behavioral patterns within networks or information systems and generating alerts when these patterns change. The intrusion detection system intelligently forms correlations between disparate sources to find traffic anomalies. Over time, behaviors are predictive, and the intrusion detection system attempts to predict outcomes, becoming proactive instead of just reactive. Intrusions occur throughout whole information systems, including both network infrastructure and application servers. By treating the information system as a whole and performing intrusion detection across it, the chances of detection are increased significantly.
Owner:MASERGY COMMUNICATIONS
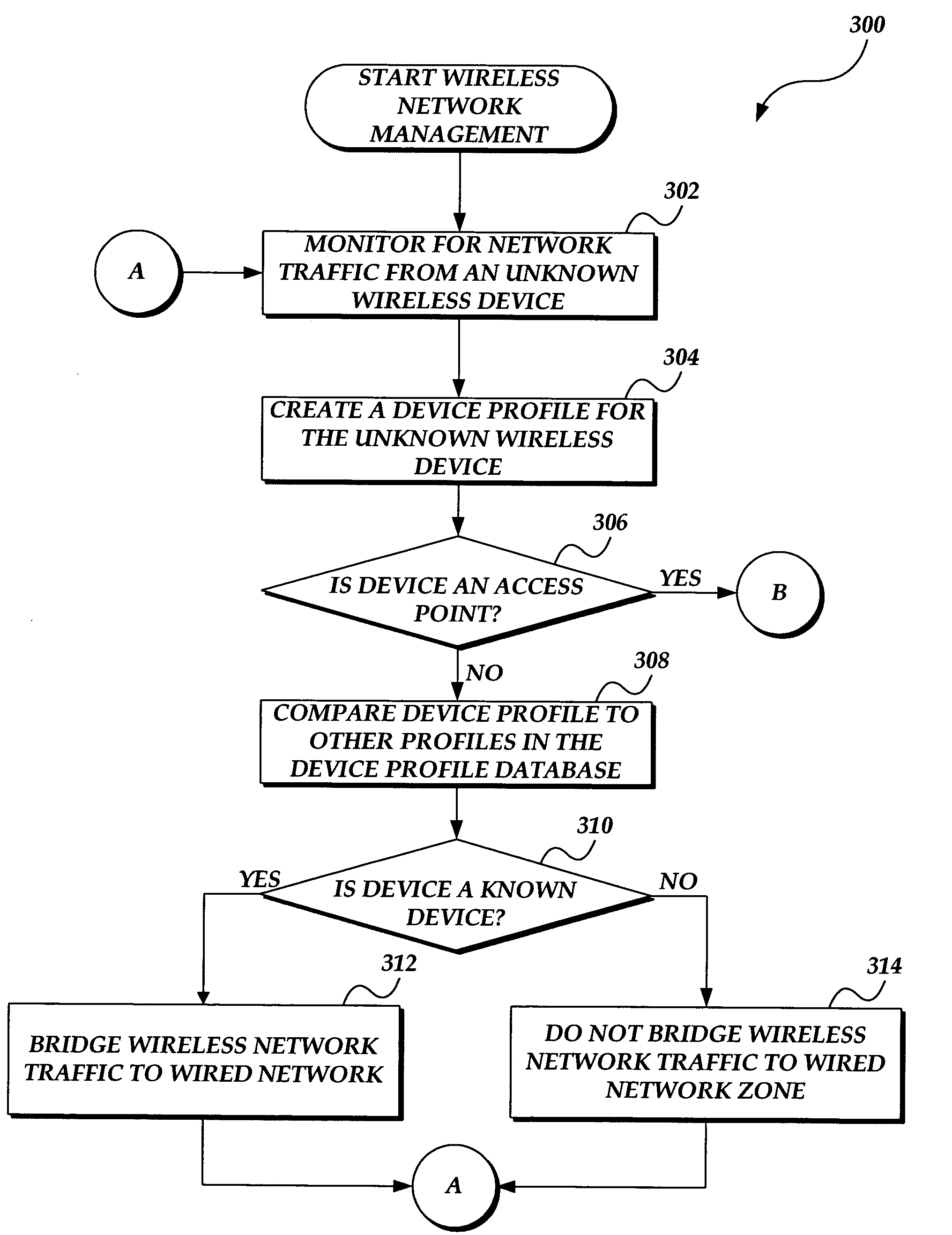
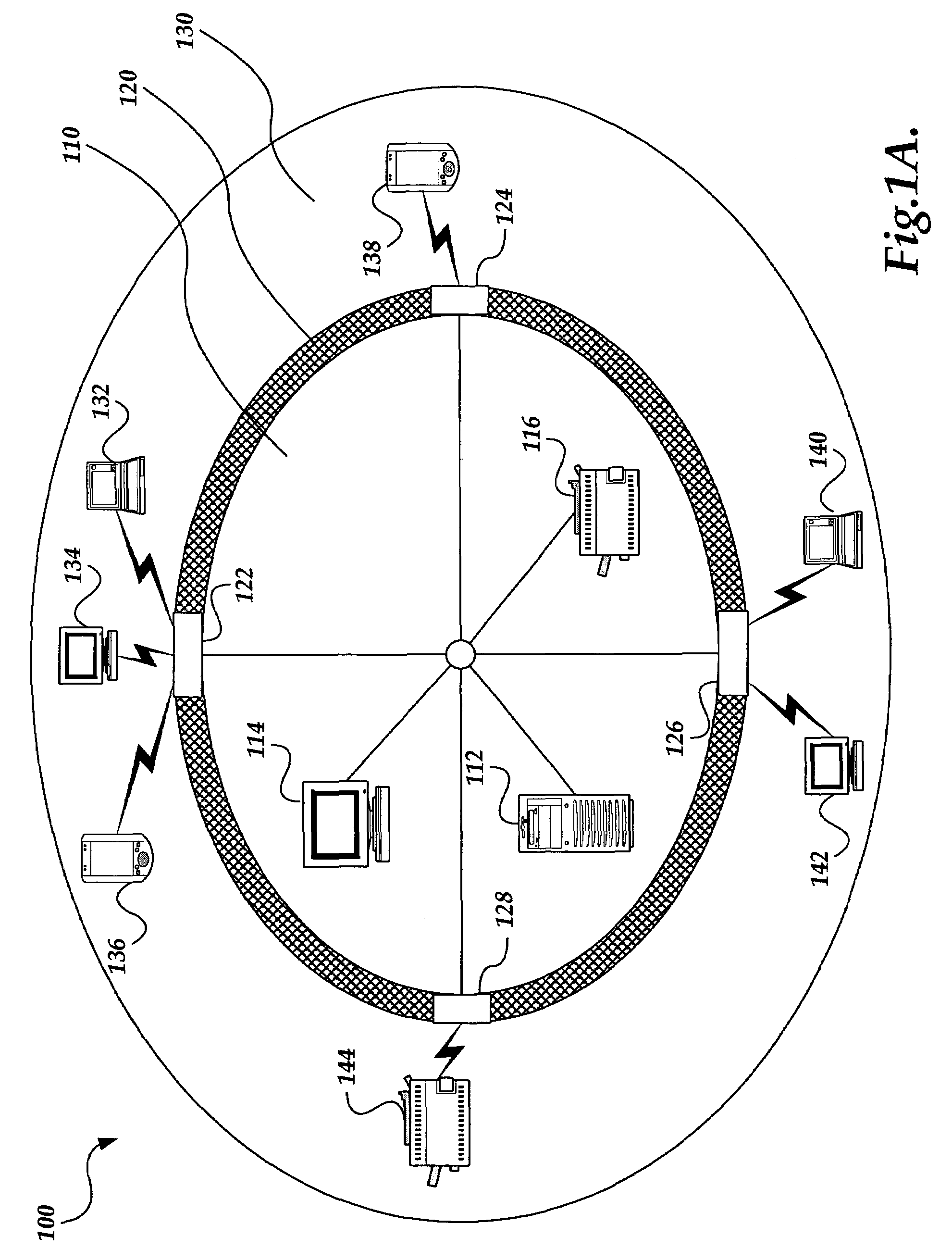
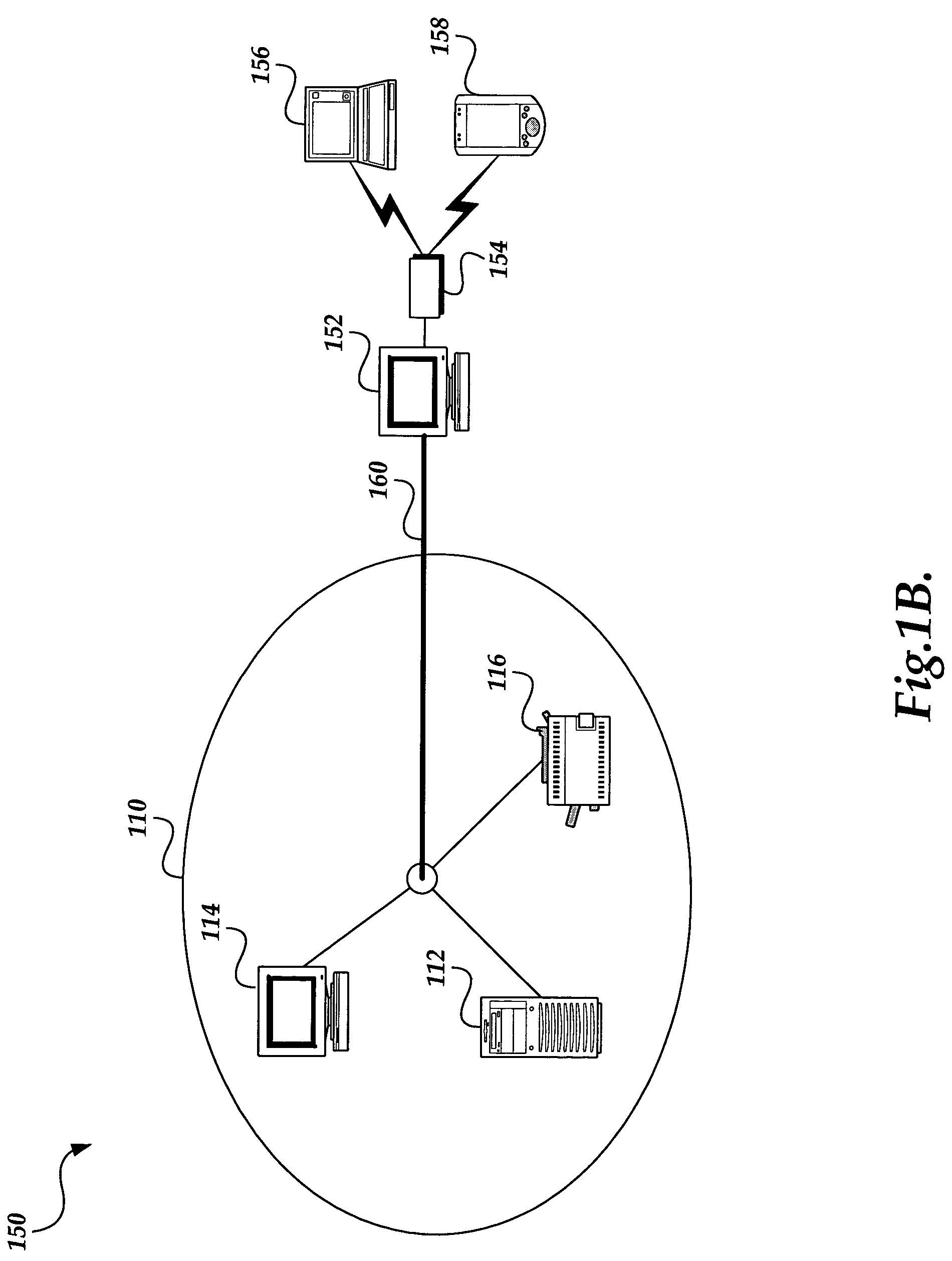
System and method for wireless local area network monitoring and intrusion detection
InactiveUS7340768B2Memory loss protectionDigital data processing detailsThreat levelNotification system
The present invention provides a system and method for providing real-time wireless network monitoring and intrusion detection. The present invention profiles wireless devices and maintains a database of known / authorized wireless device profiles. Wireless devices are analyzed to determine the threat level they pose to the network, and if the threat level exceeds a predetermined threshold, the invention refuses to bridge the network traffic from the wireless devices to the wired network. The present invention provides reporting of the wireless network activity, the known and unknown wireless devices, and the threat levels posed by the wireless devices. If an unknown wireless device is determined to be, or may be, a wireless access point, an alert is generated, such as notifying a system administrator to take appropriate action.
Owner:WIMETRICS CORP
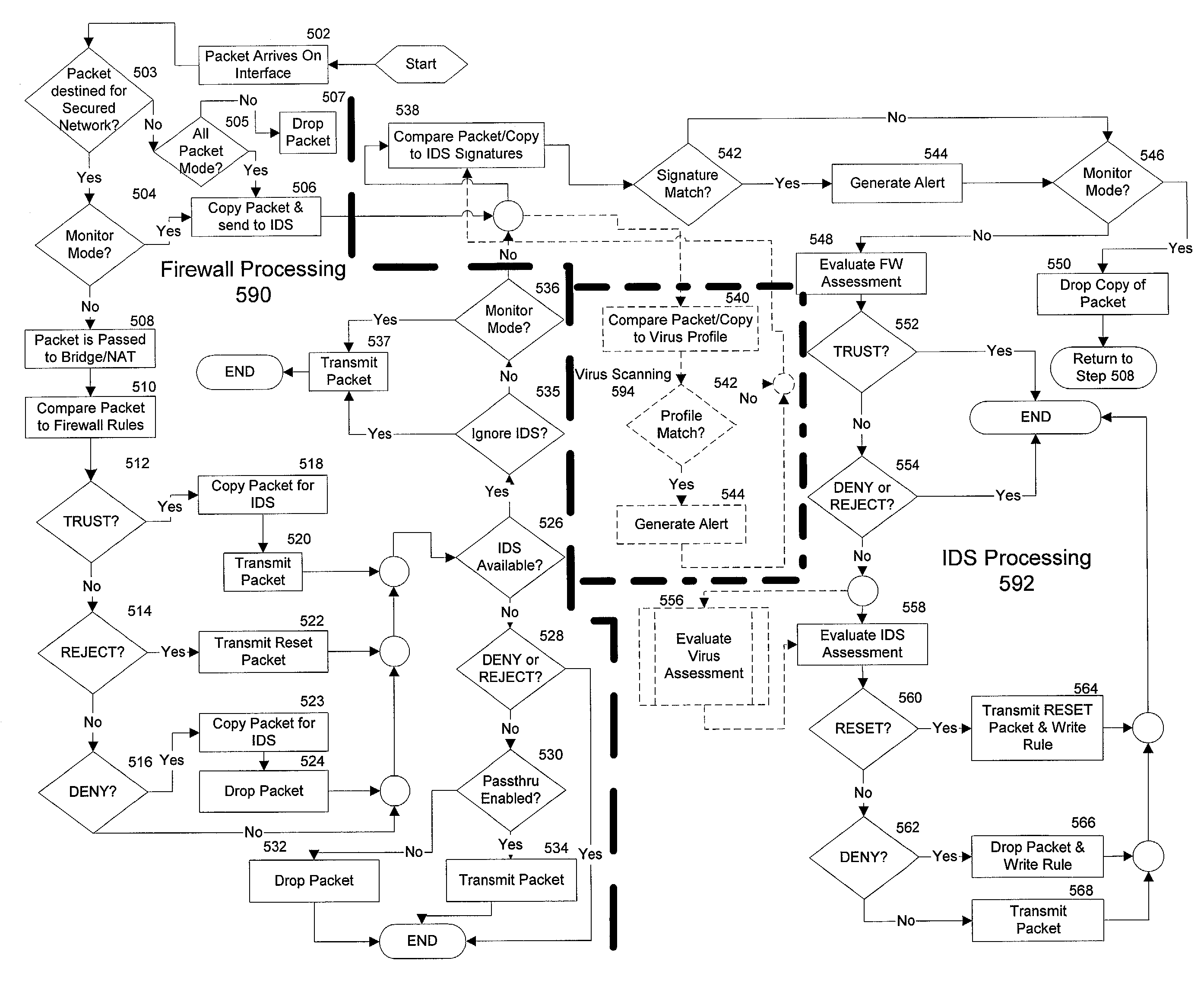
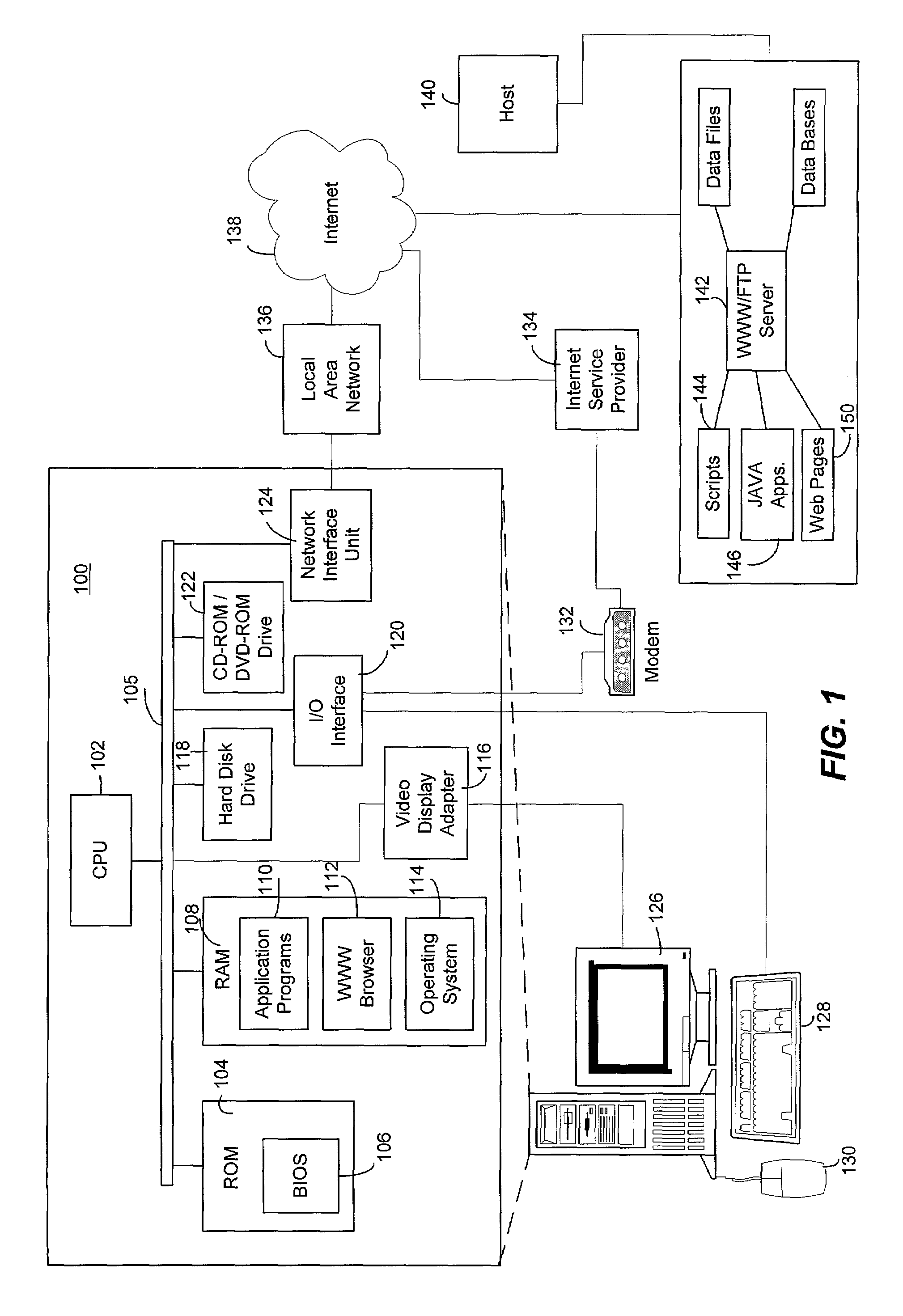
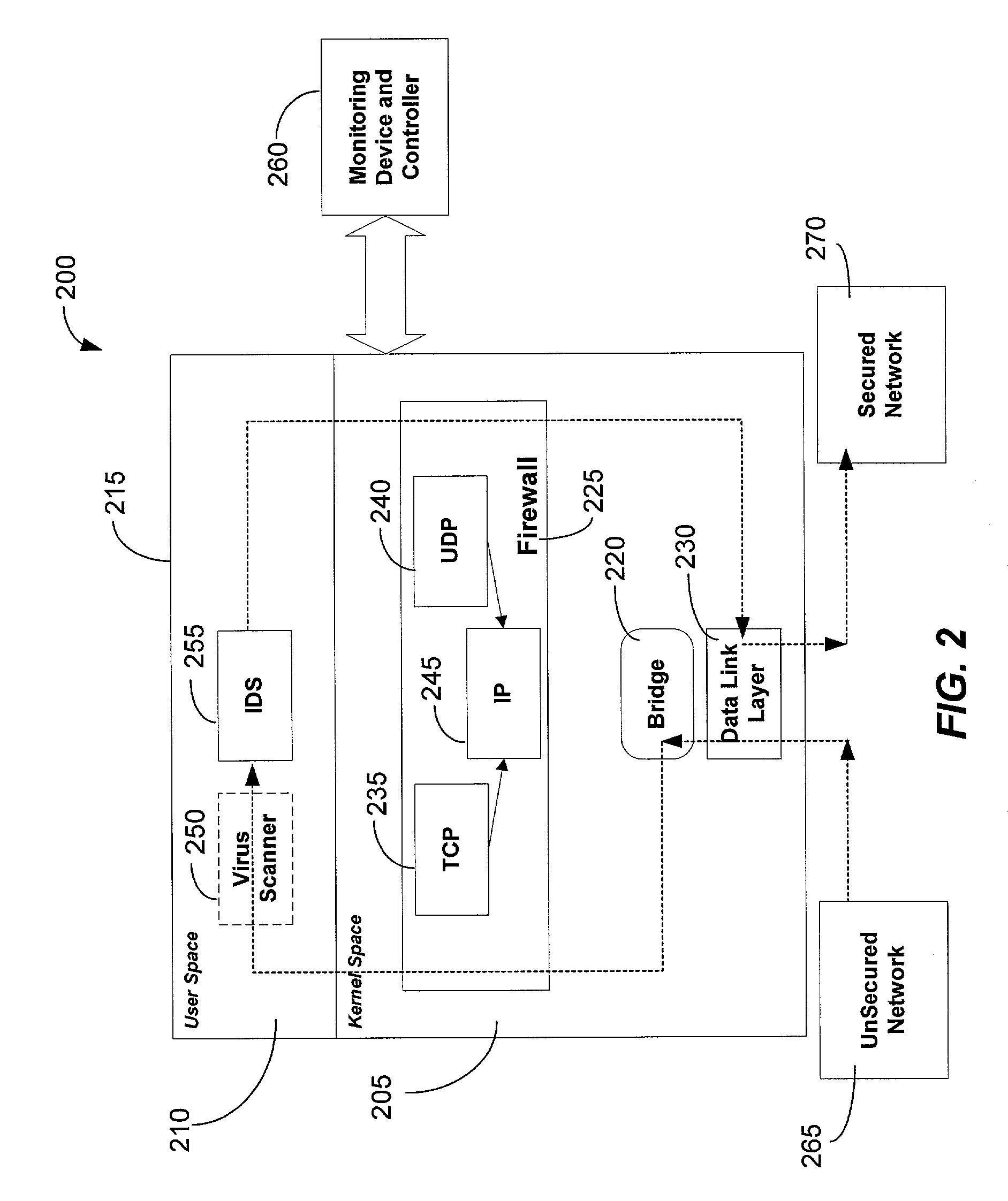
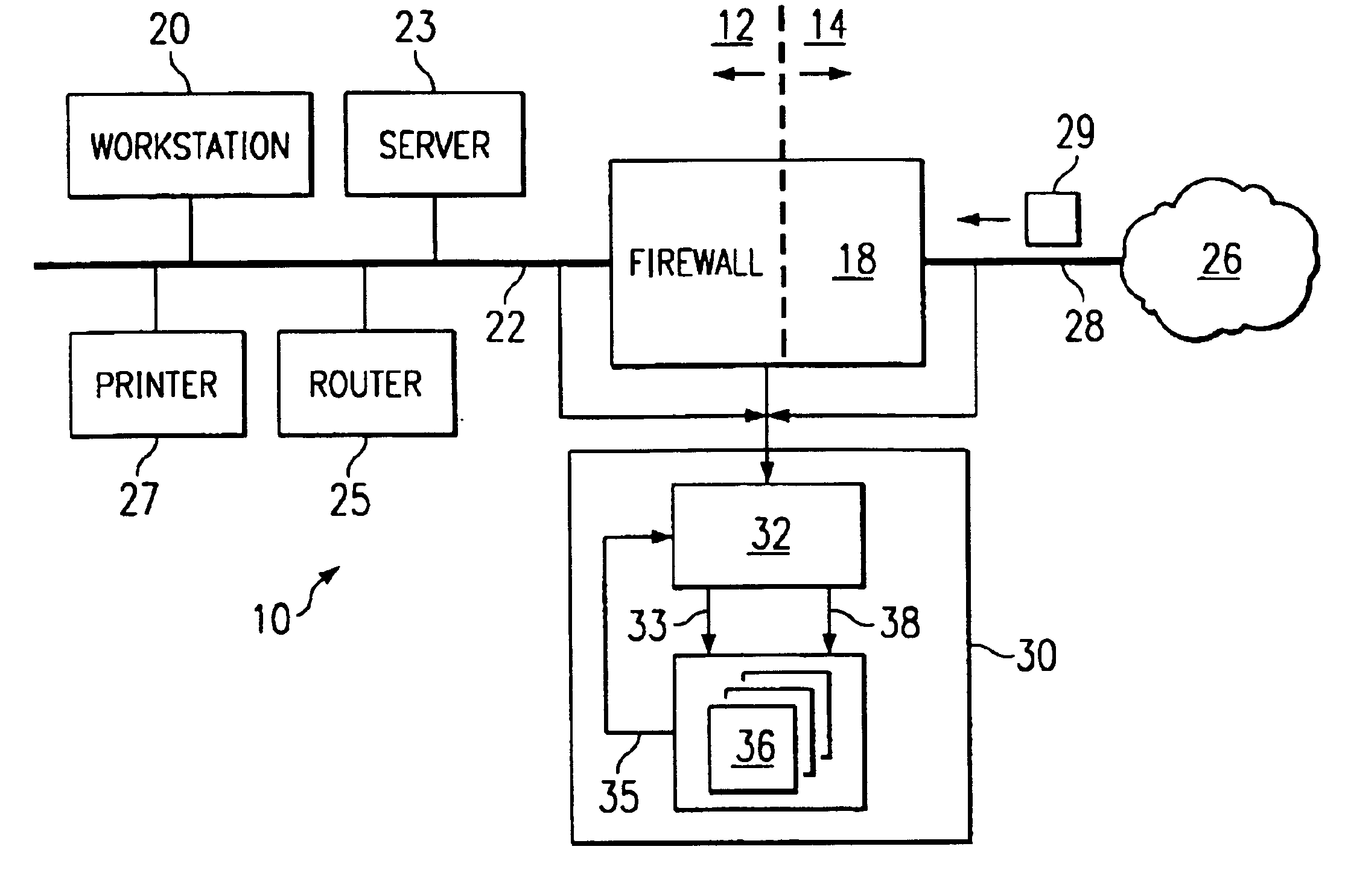
Integrated computer security management system and method
InactiveUS7331061B1Centralized controlIncrease speedMemory loss protectionError detection/correctionSafety management systemsSecurity management
The present invention is generally directed to a computer security management system that integrates a firewall with an intrusion detection system (IDS). In other words, the firewall and IDS of the present invention can be designed to communicate process or status information and packets with one another. The present invention can facilitate centralized control of the firewall and the IDS and can increase the speed at which packets are passed between a secured computer network and an external network. Increased packet processing speed can be achieved in several ways. For example, the firewall and IDS can process packets in series, in parallel, and sometimes singularly when one of the components is not permitted to process a packet. Alternatively, singular processing can also be performed when one component is permitted to pass a packet to the secured computer network without checking with the other component.
Owner:SECUREWORKS
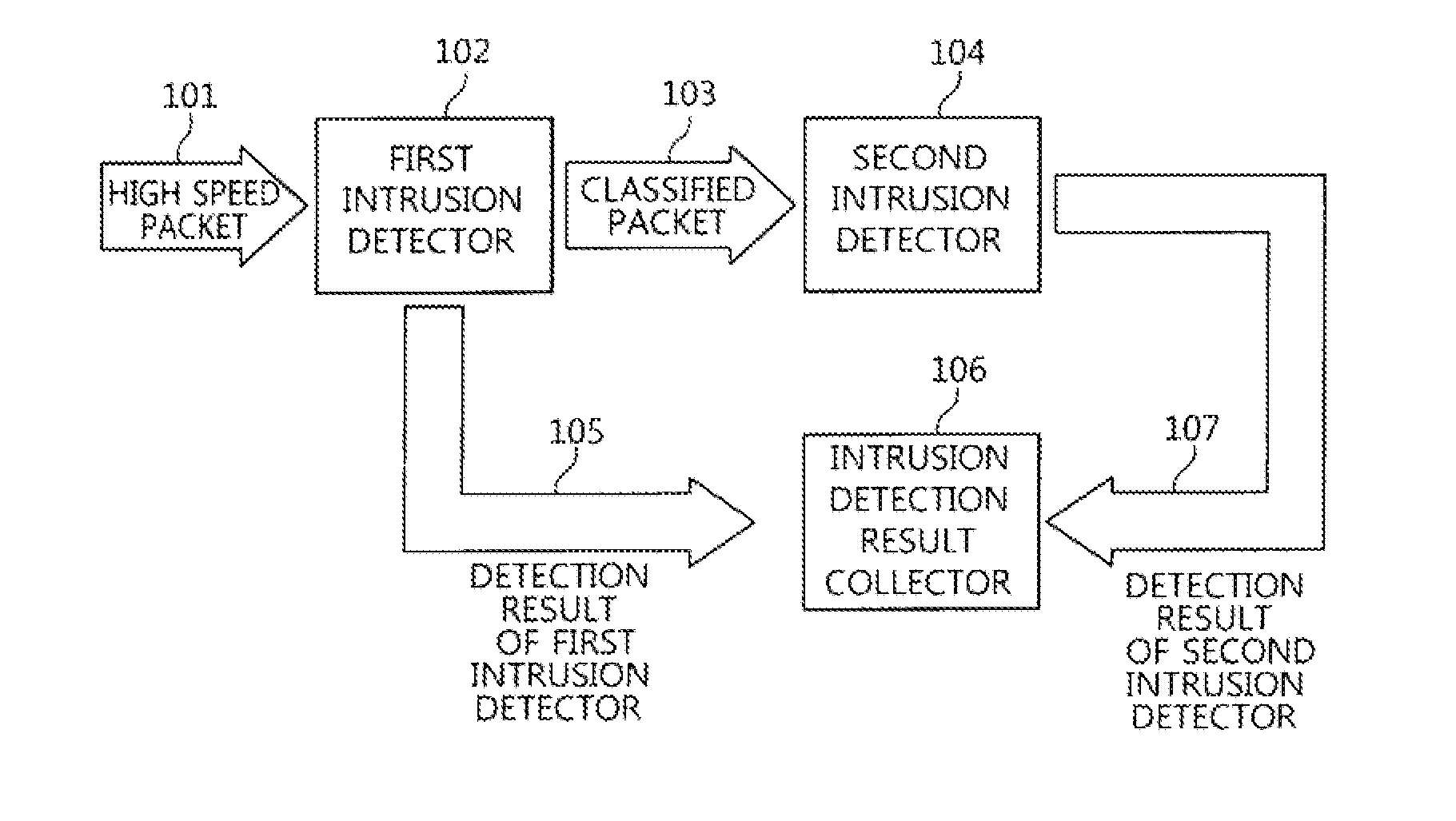
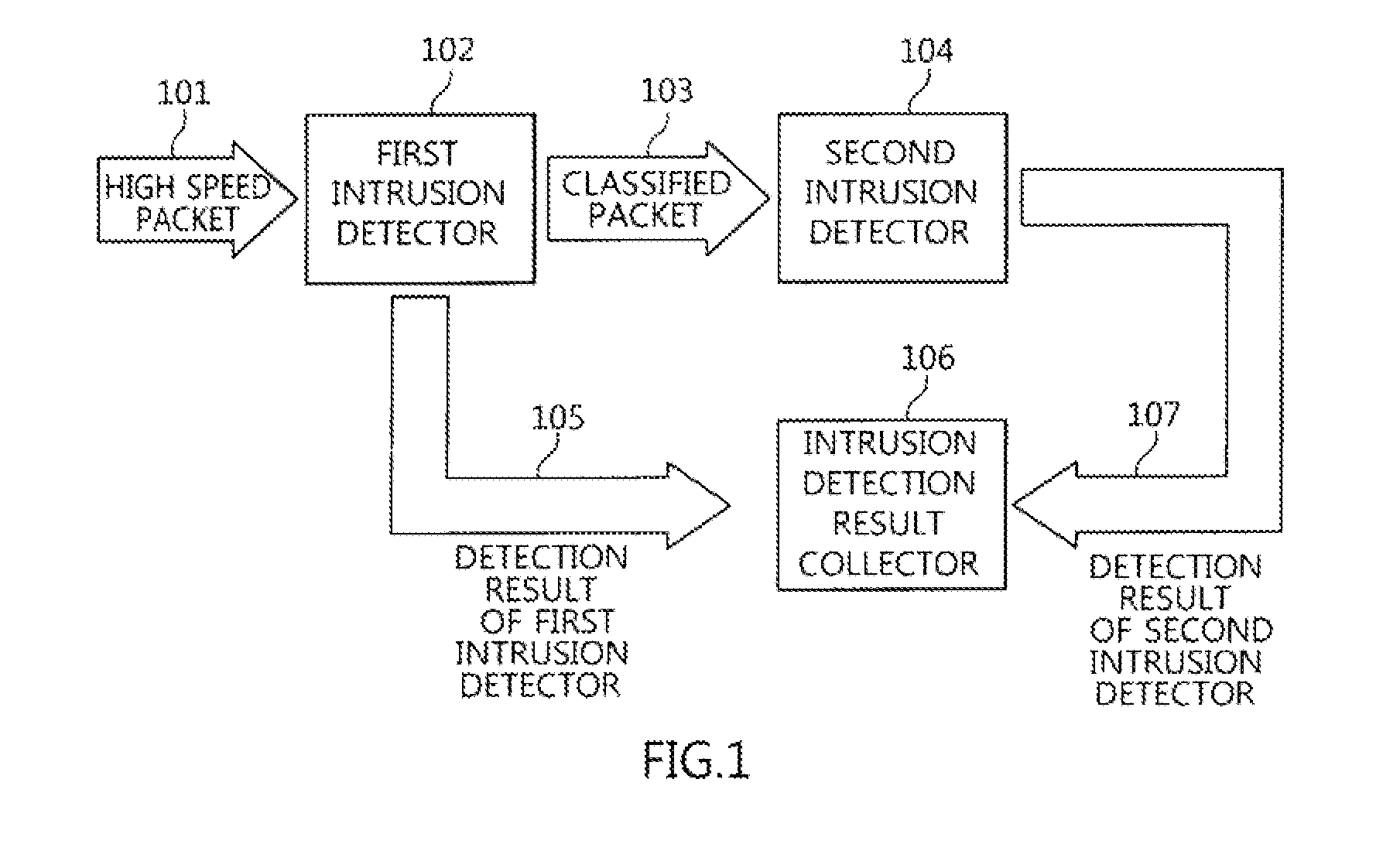
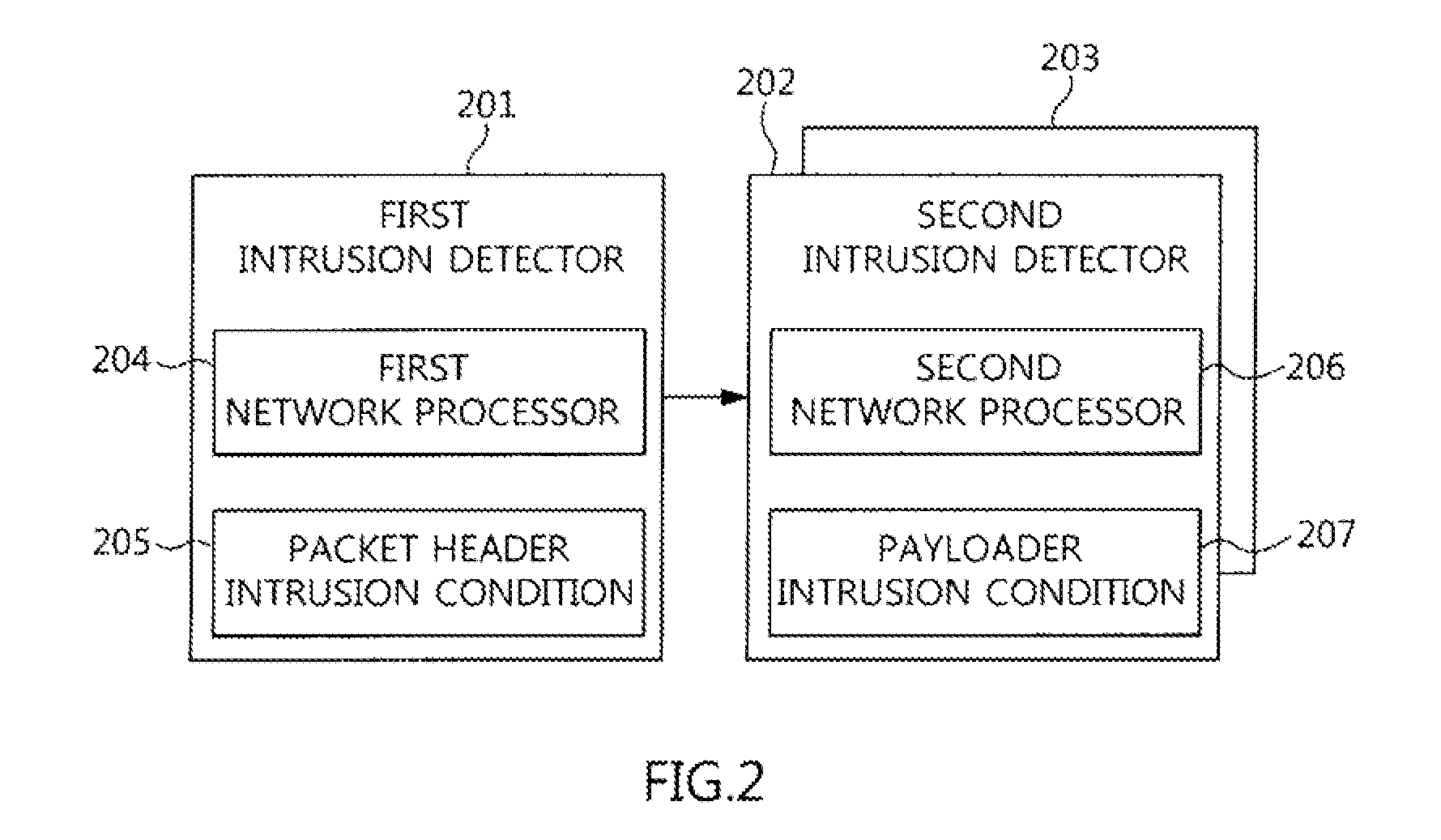
Two-stage intrusion detection system for high-speed packet processing using network processor and method thereof
ActiveUS20130160122A1Memory loss protectionData taking preventionNetwork processorDistributed computing
A system and method for detecting network intrusion by using a network processor are provided. The intrusion detection system includes: a first intrusion detector, configured to use a first network processor to perform intrusion detection on layer 3 and layer 4 of a protocol field among information included in a packet header of a packet transmitted to the intrusion detection system, and when no intrusion is detected, classify the packets according to stream and transmit the classified packets to a second intrusion detector; and a second intrusion detector, configured to use a second network processor to perform intrusion detection through deep packet inspection (DPI) for the packet payload of the packets transmitted from the first intrusion detector. Thereby, intrusion detection for high-speed packets can be performed in a network environment.
Owner:ELECTRONICS & TELECOMM RES INST
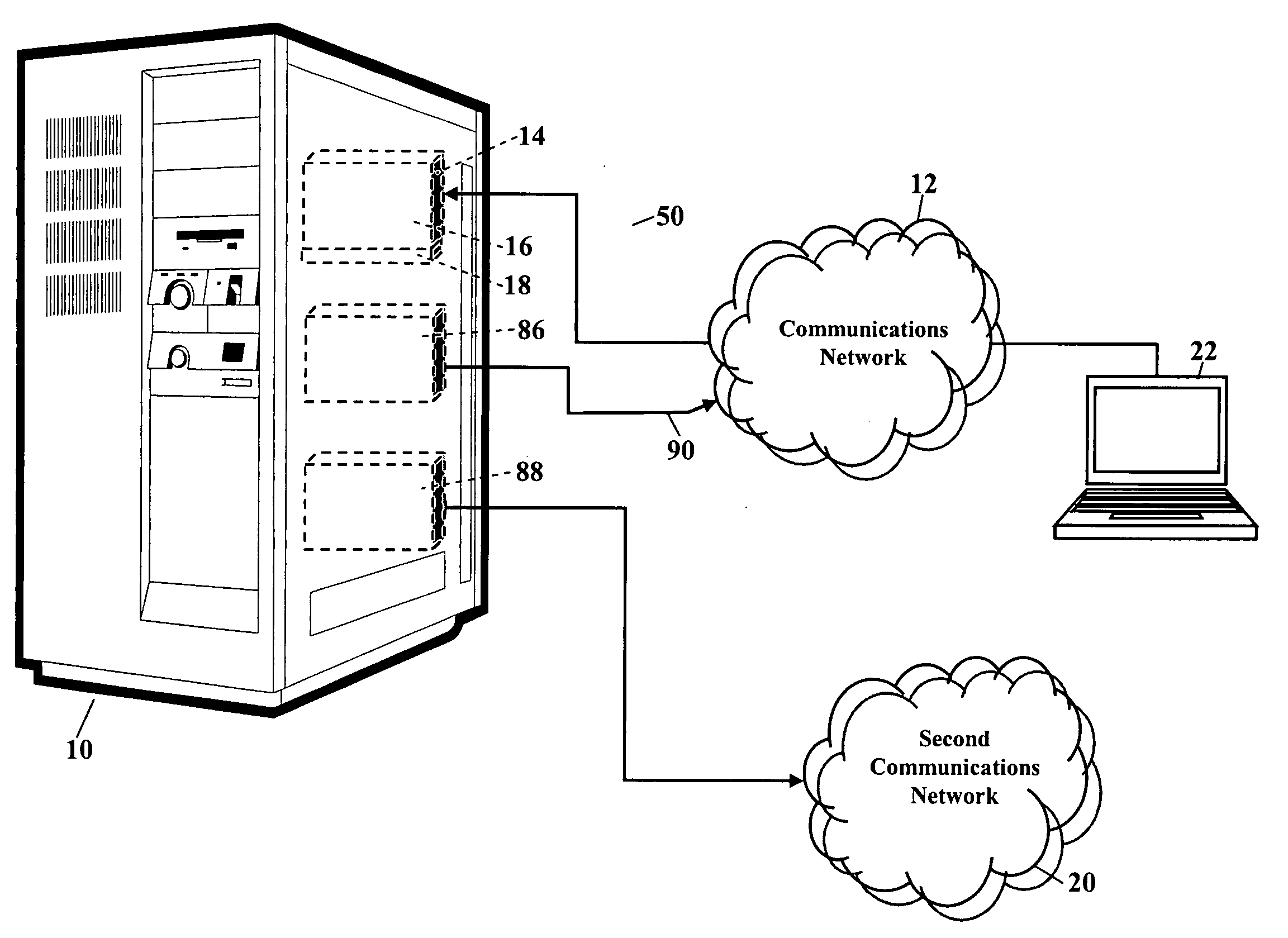
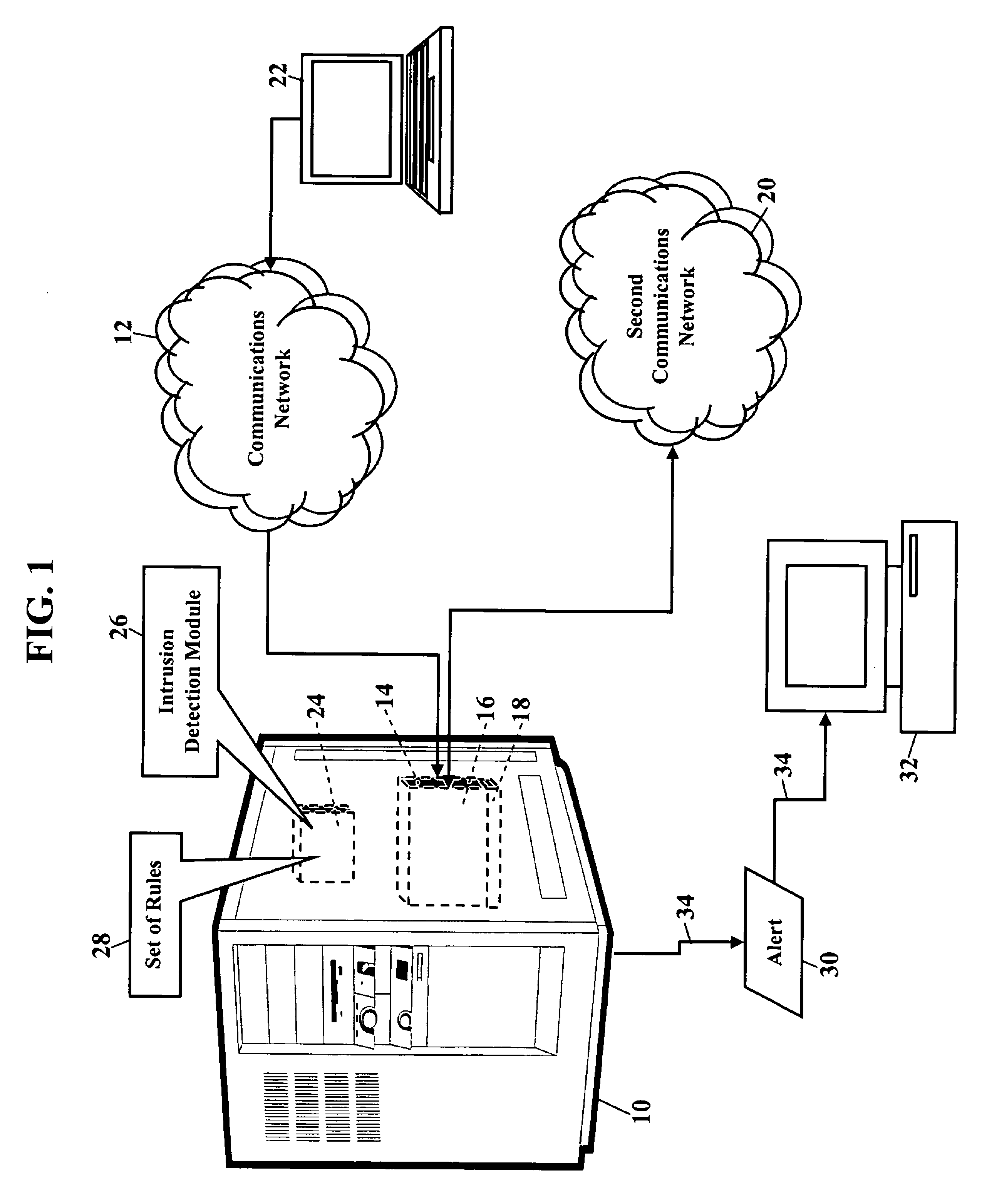
Methods, systems, and products for intrusion detection
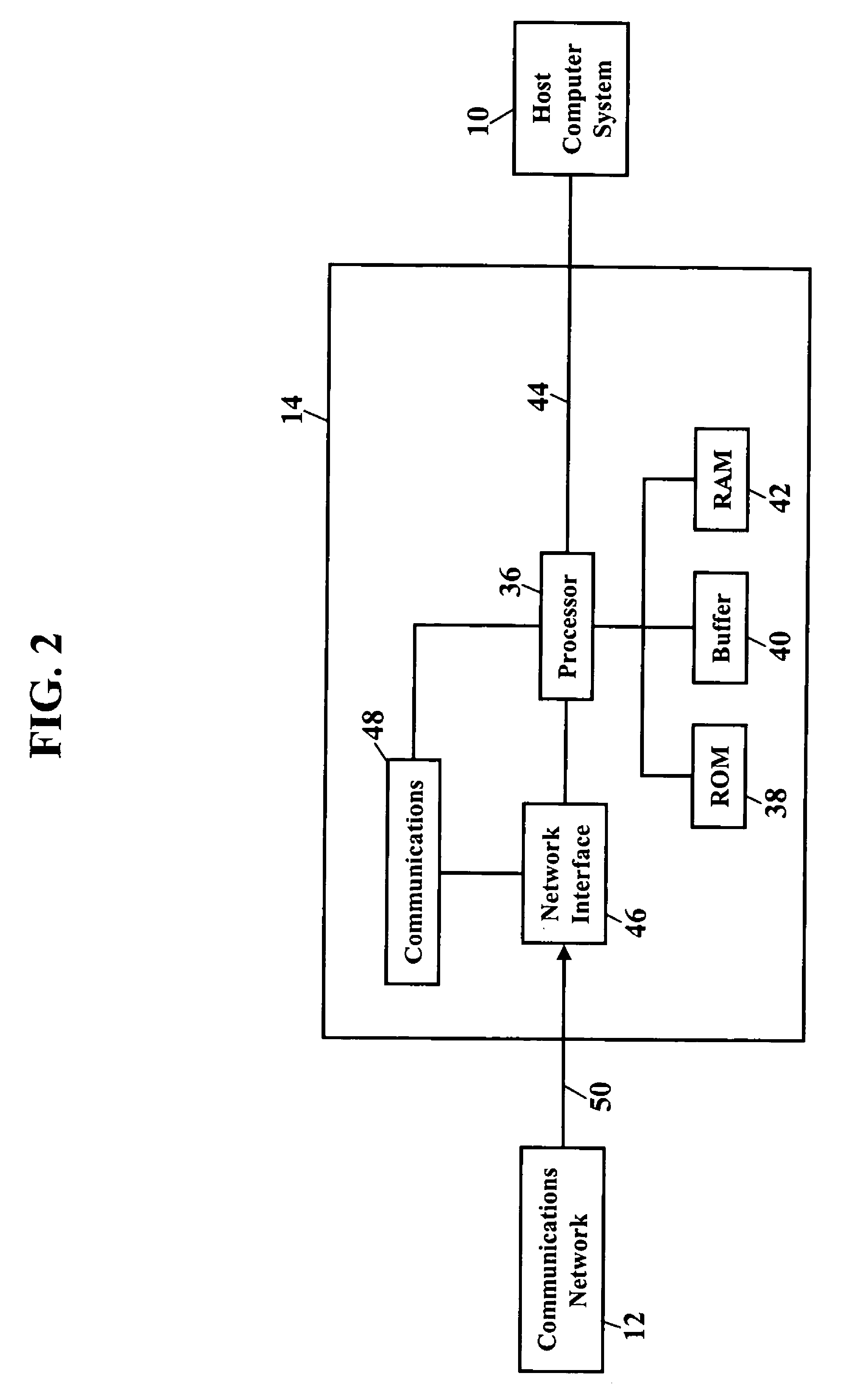
InactiveUS7971053B2Reduce rogue accessReduce intrusionMemory loss protectionError detection/correctionComputer networkComputerized system
Methods, systems, and products are disclosed for detecting an intrusion to a communications network. One embodiment describes a system for detecting intrusions. The system has a peripheral card coupled to a host computer system. The peripheral card has a communications portion and a processor managing the communications portion. The communications portion has only a capability for receiving data packets via a communications network. The communications portion lacks capability of transmitting the data packets via the communications network. The communications portion of the peripheral card reduces intrusion of the communications network.
Owner:BELLSOUTH INTPROP COR
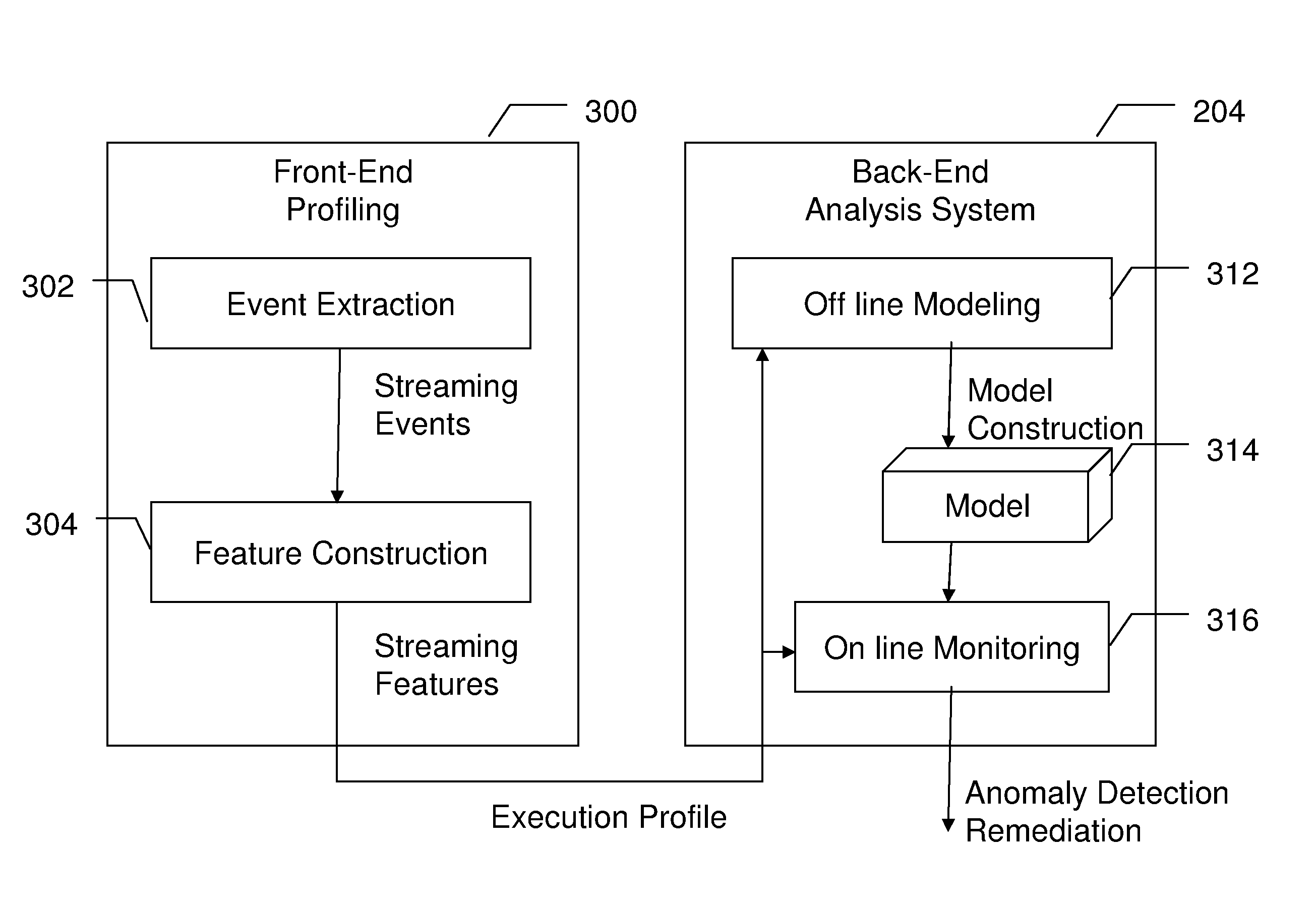
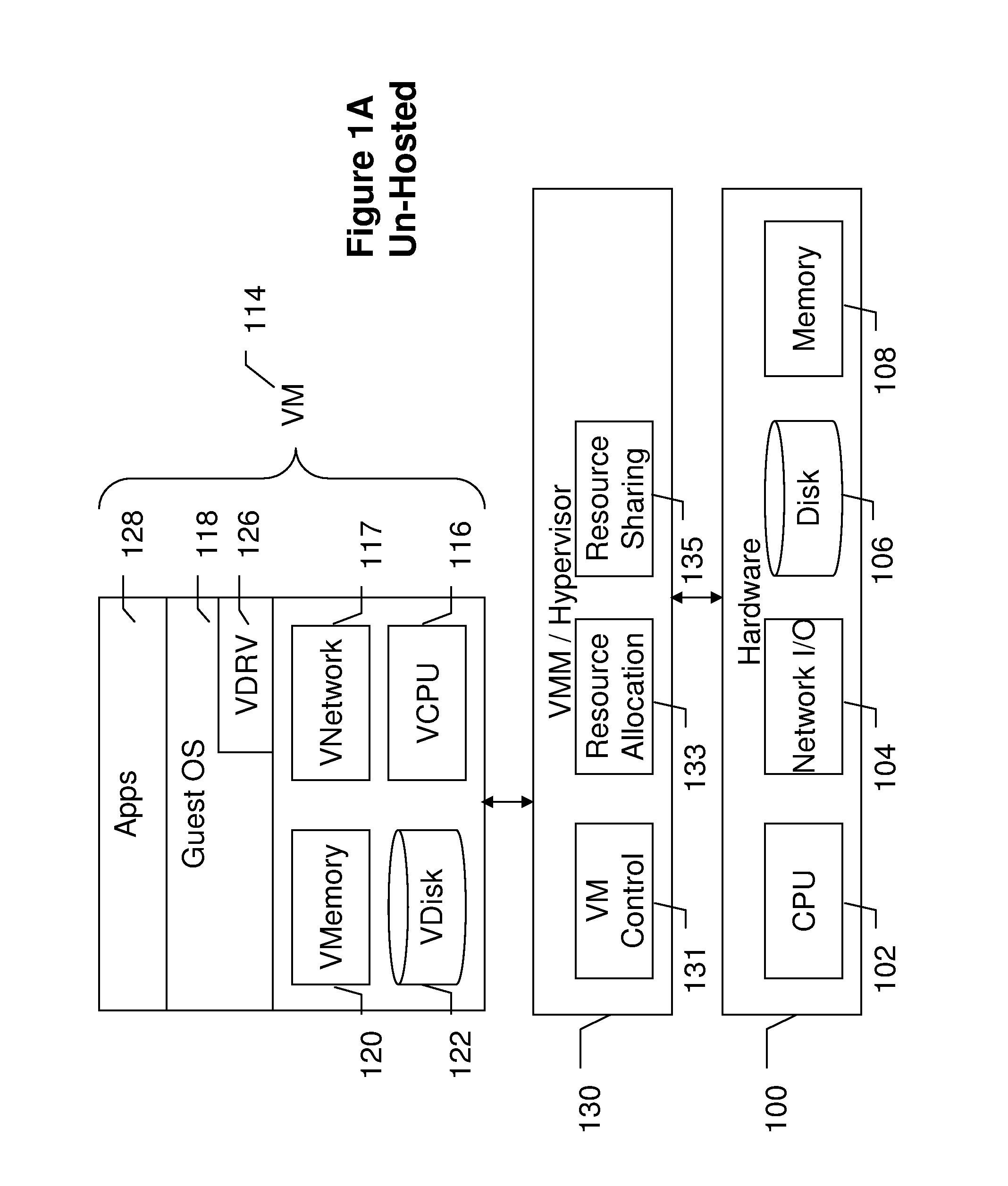
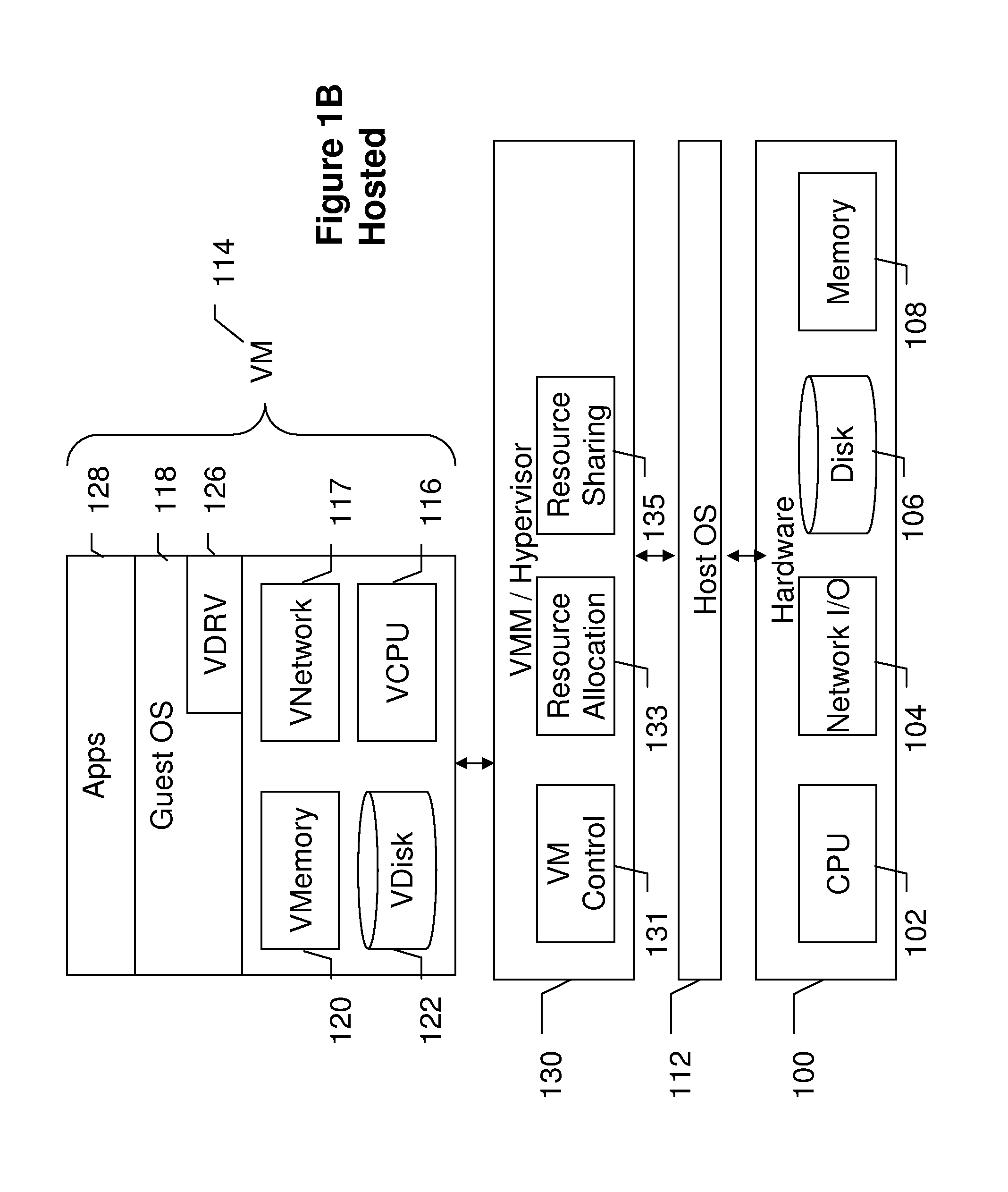
Vmm-based intrusion detection system
InactiveUS20110004935A1Memory loss protectionError detection/correctionPattern recognitionOperational system
An intrusion detection system collects architectural level events from a Virtual Machine Monitor where the collected events represent operation of a corresponding Virtual Machine. The events are consolidated into features that are compared with features from a known normal operating system. If an amount of any differences between the collected features and the normal features exceeds a threshold value, a compromised Virtual Machine may be indicated. The comparison thresholds are determined by training on normal and abnormal systems and analyzing the collected events with machine learning algorithms to arrive at a model of normal operation.
Owner:NORTHEASTERN UNIV
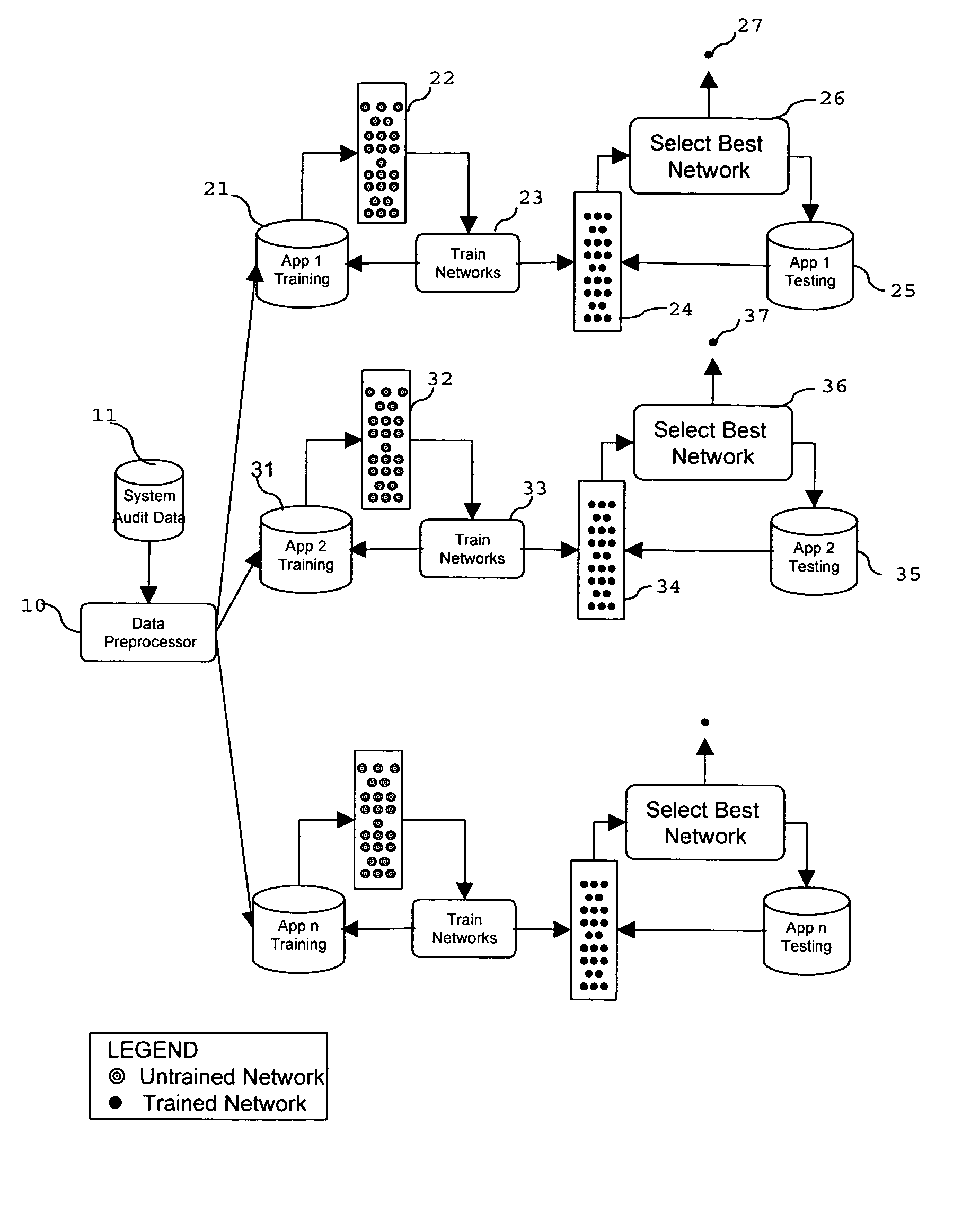
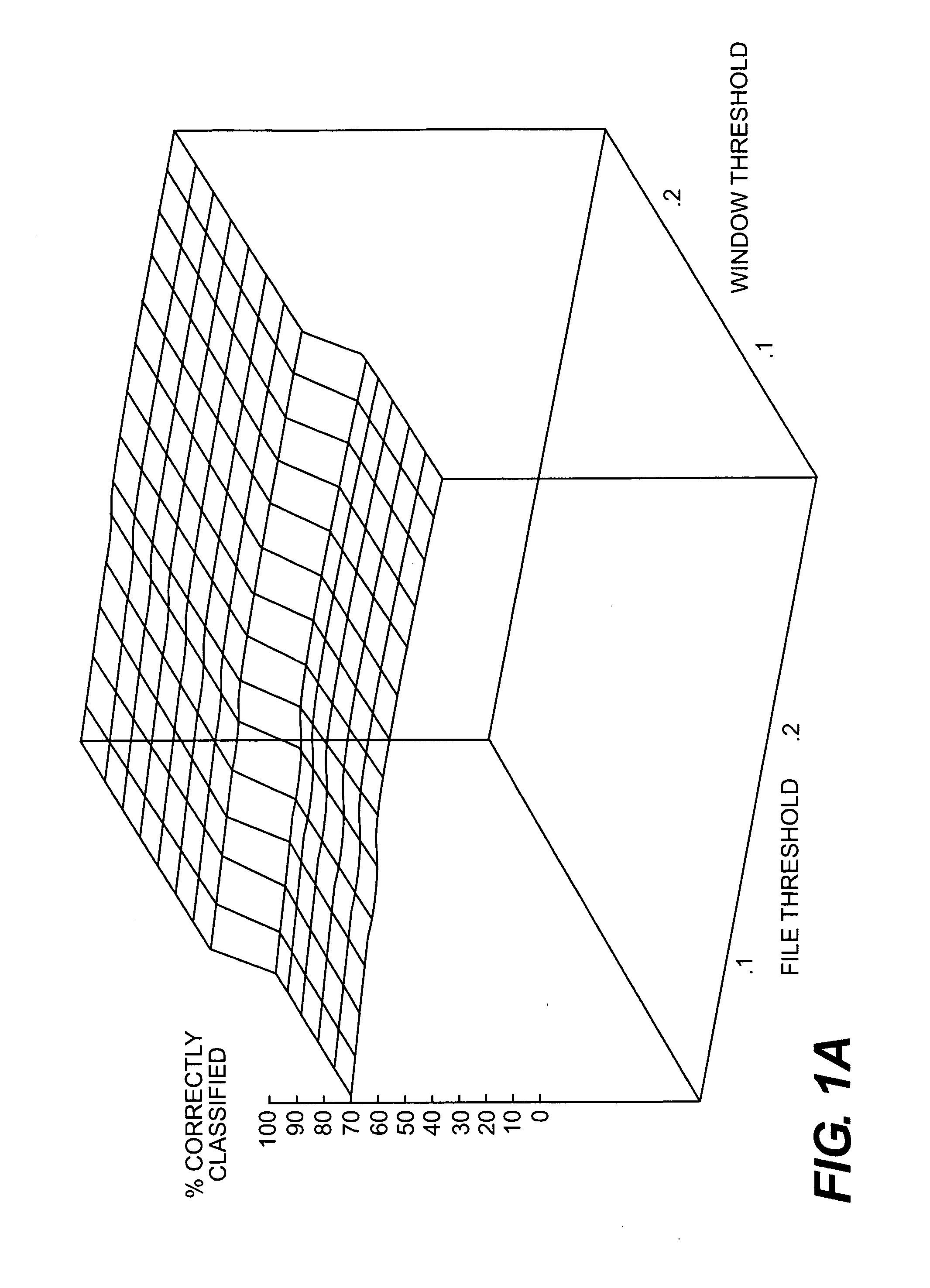
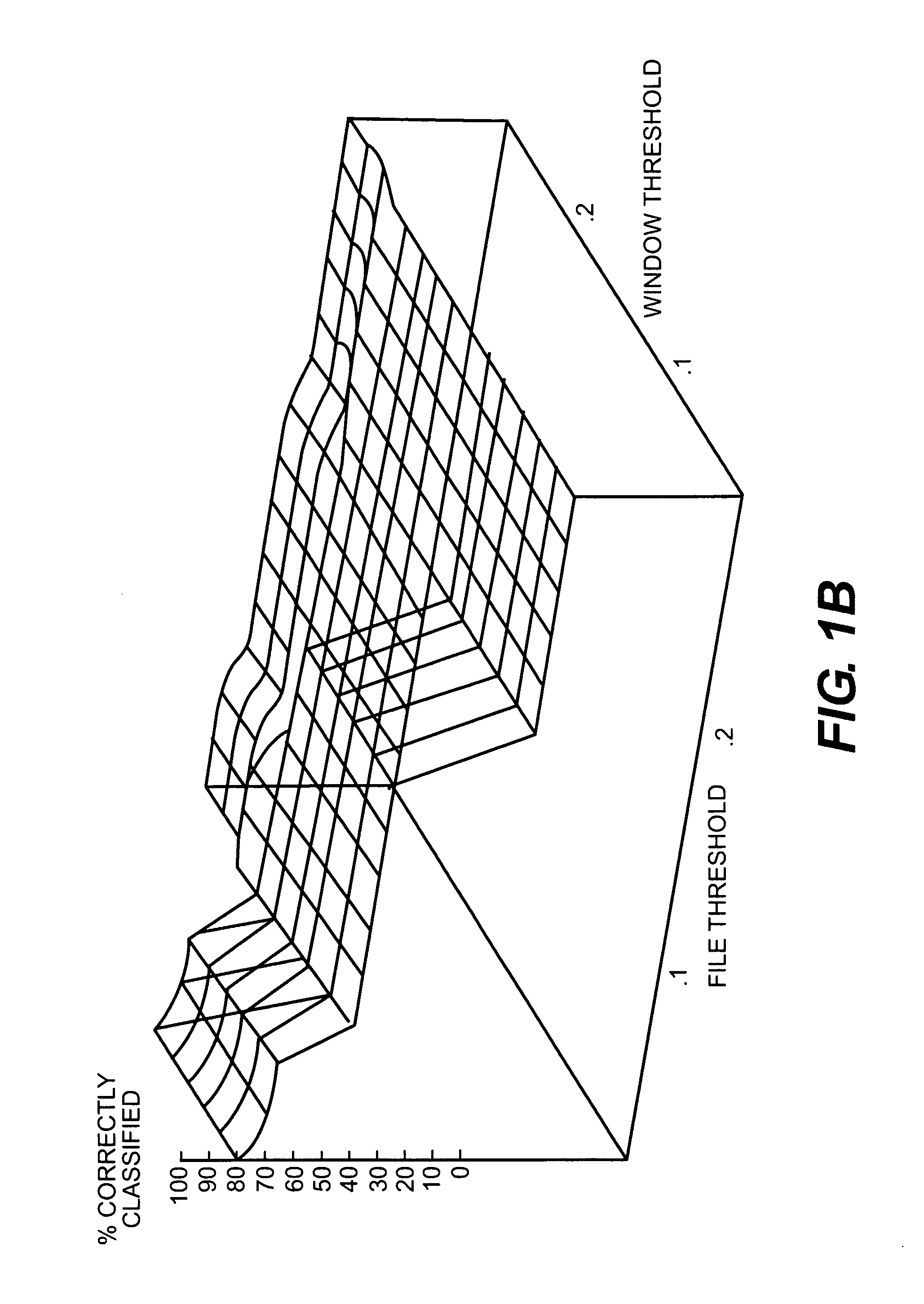
Computer intrusion detection system and method based on application monitoring
InactiveUS7181768B1Reduced false positive falseReduce false negative rateMemory loss protectionError detection/correctionNerve networkPrediction algorithms
An intrusion detection system (IDS) that uses application monitors for detecting application-based attacks against computer systems. The IDS implements application monitors in the form of a software program to learn and monitor the behavior of system programs in order to detect attacks against computer hosts. The application monitors implement machine learning algorithms to provide a mechanism for learning from previously observed behavior in order to recognize future attacks that it has not seen before. The application monitors include temporal locality algorithms to increased the accuracy of the IDS. The IDS of the present invention may comprise a string-matching program, a neural network, or a time series prediction algorithm for learning normal application behavior and for detecting anomalies.
Owner:SYNOPSYS INC
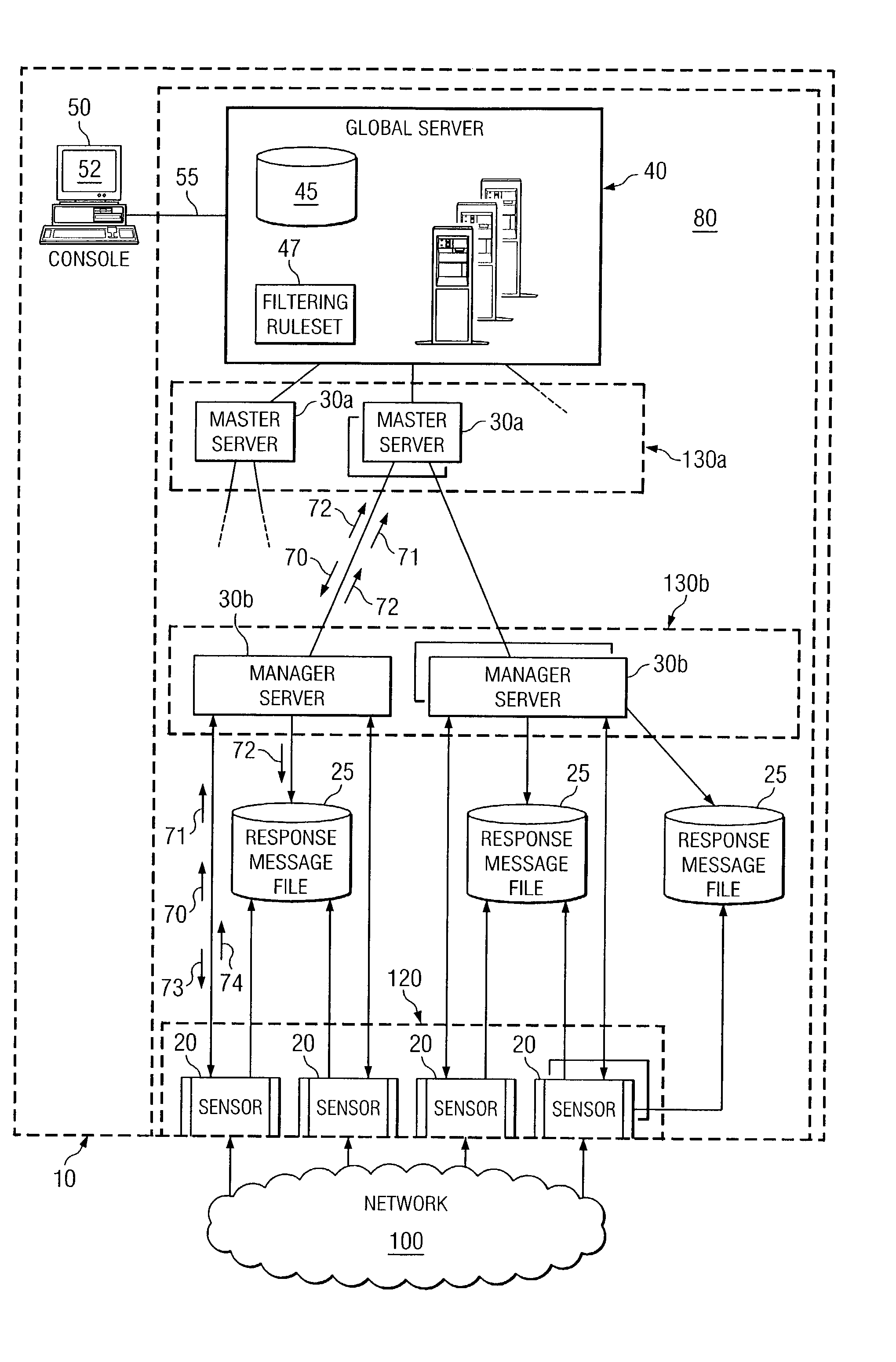
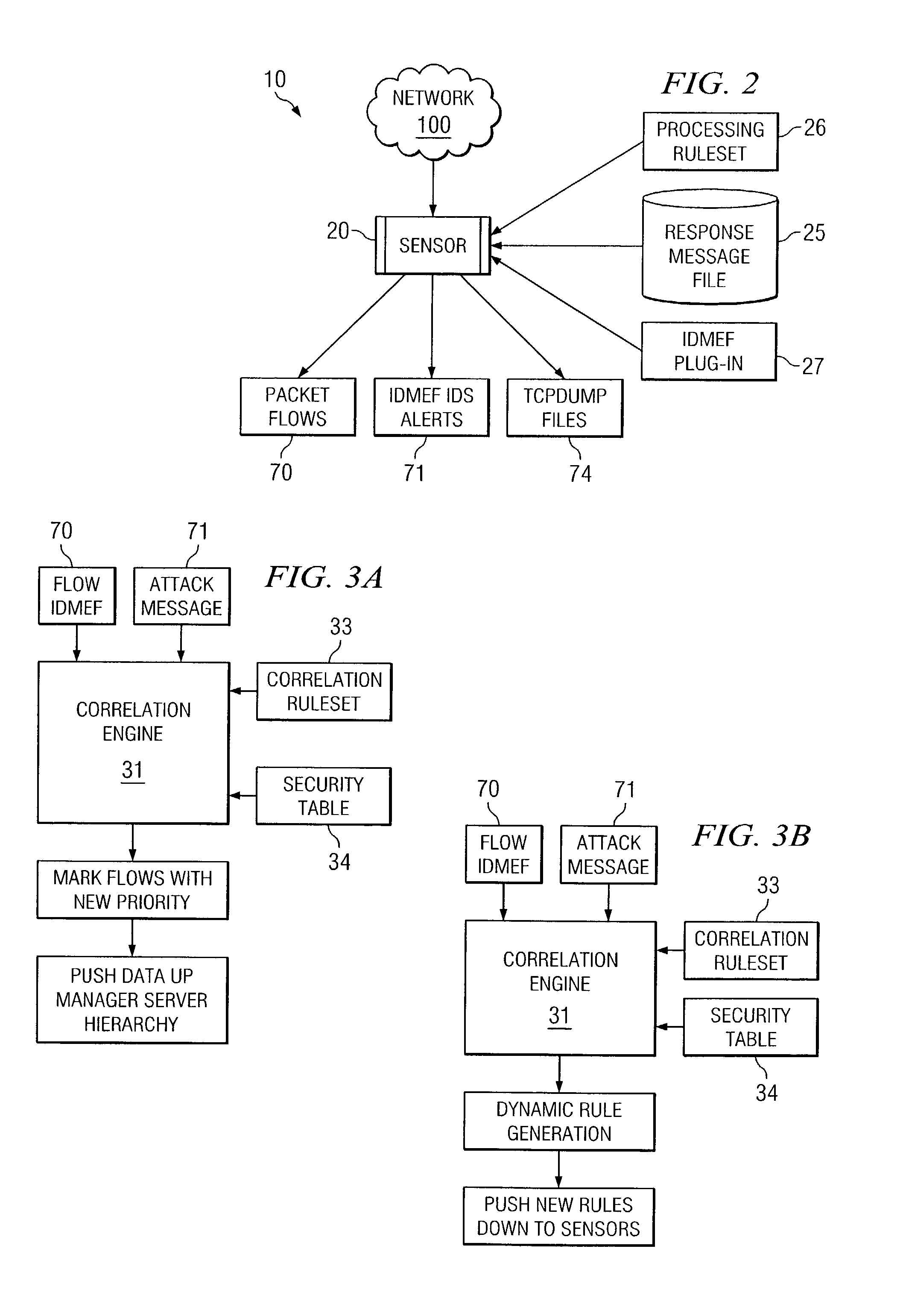
Dynamic rule generation for an enterprise intrusion detection system
ActiveUS7895649B1Lower the volumeReadily apparentMemory loss protectionDigital data processing detailsPacket lossEnterprise system
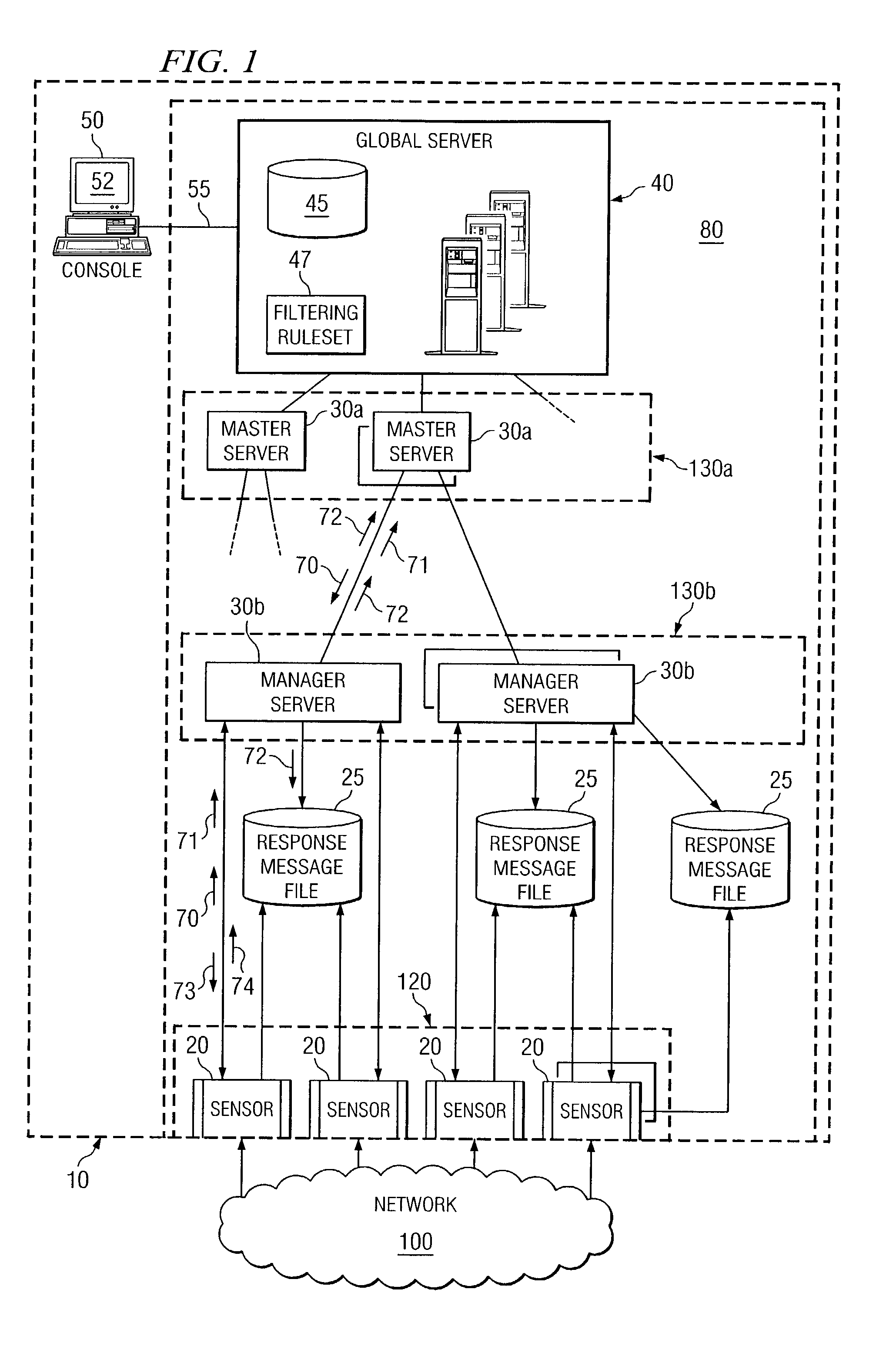
A method for dynamically generating rules for an enterprise intrusion detection system comprises receiving a packet flow from a sensor. The packet flow is dynamically processed to detect if the packet flow represents an attack on the enterprise system. A response message is automatically generated in response to the attack, the response message comprising a signature to identify the attack. The response message is automatically communicated to a response message file, the response message file comprising at least one response message.
Owner:FORCEPOINT FEDERAL
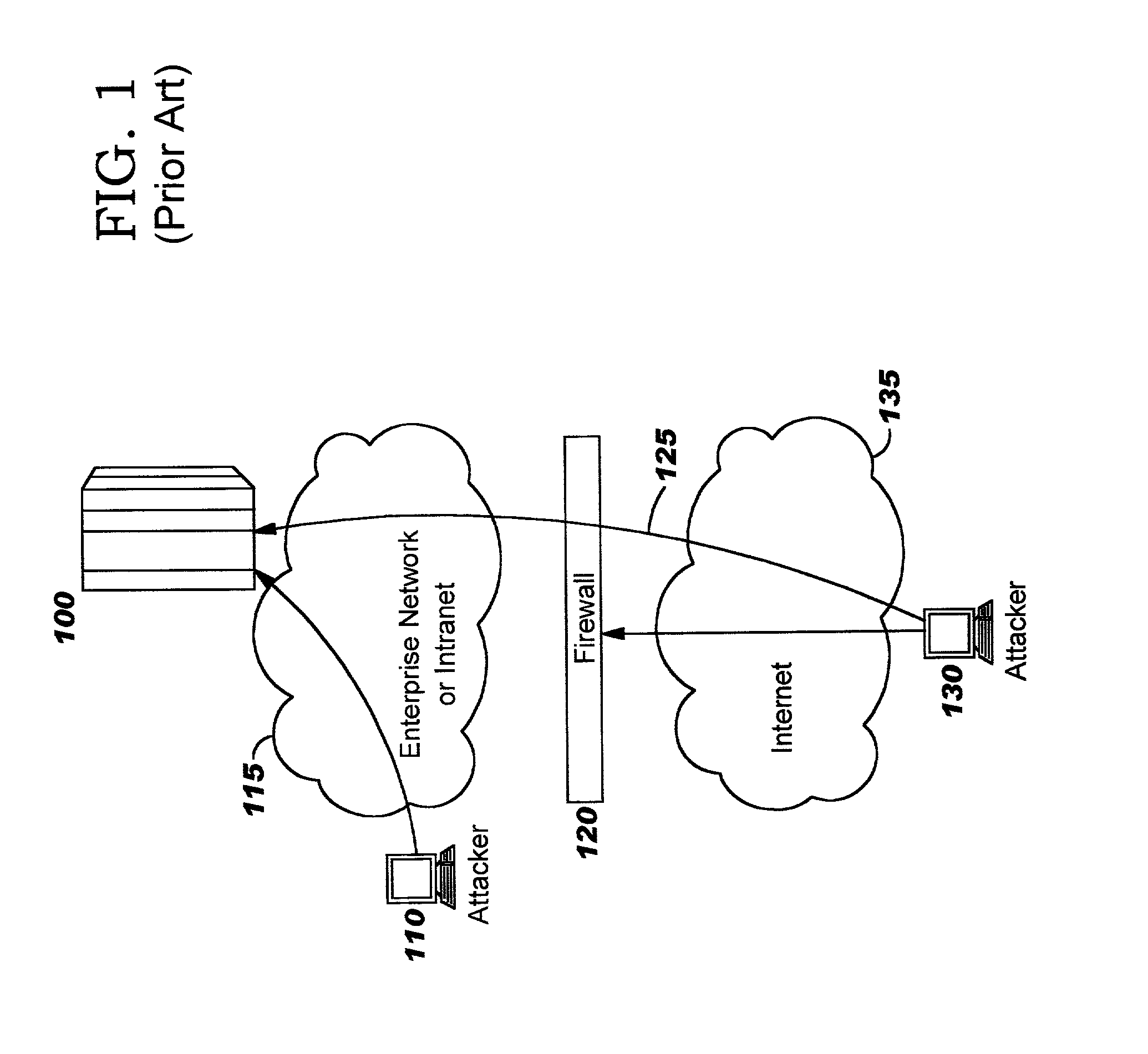
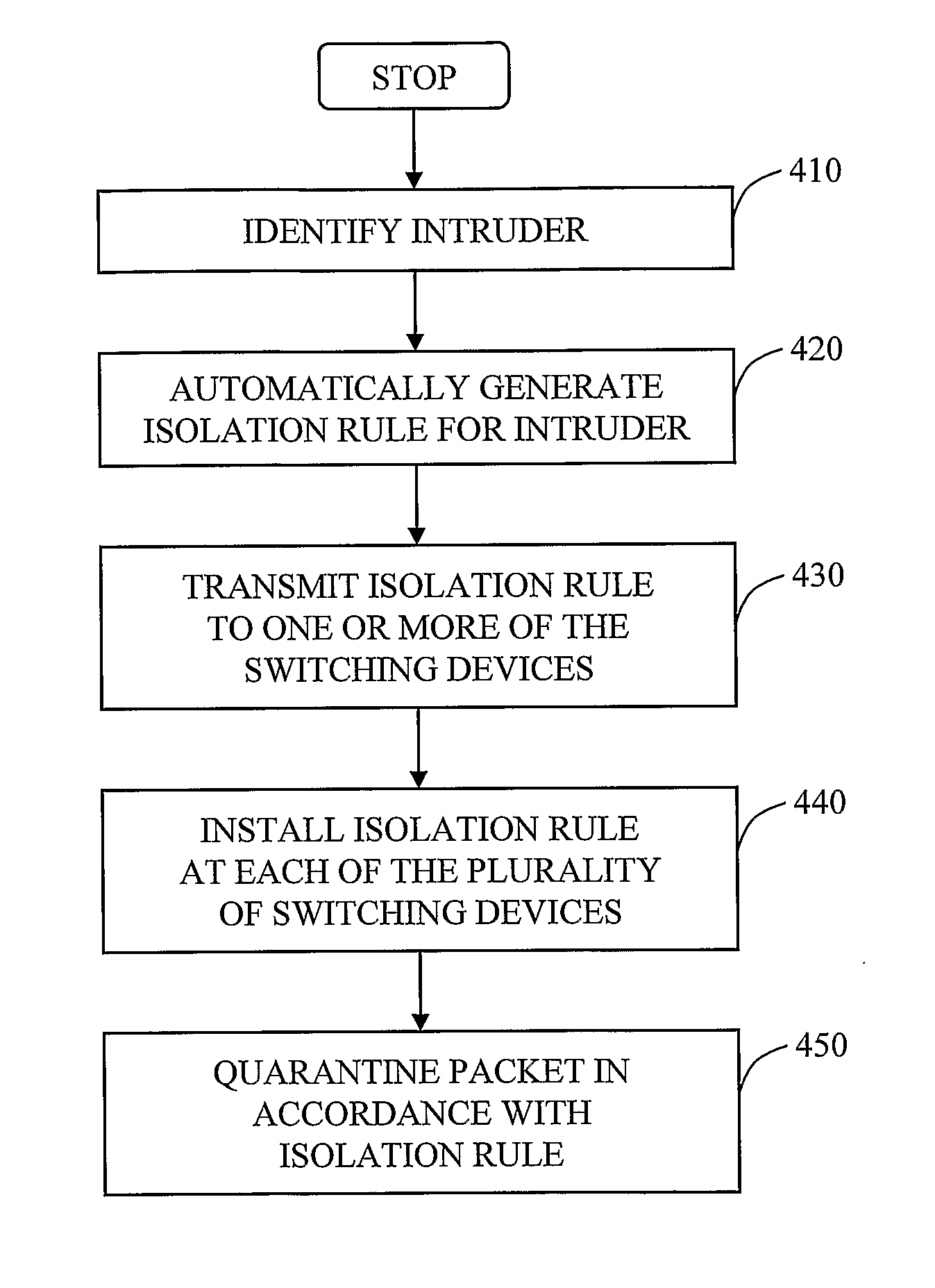
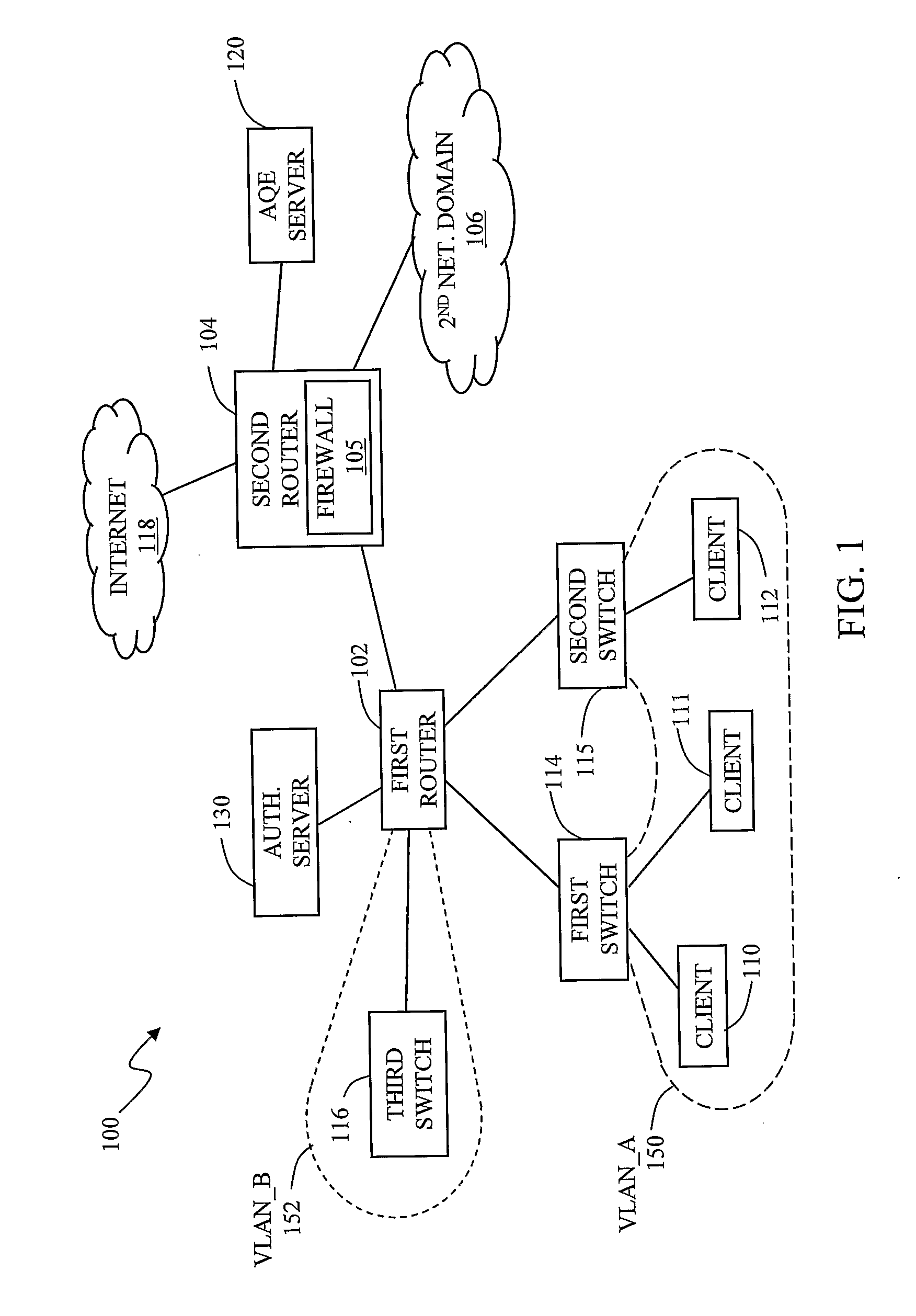
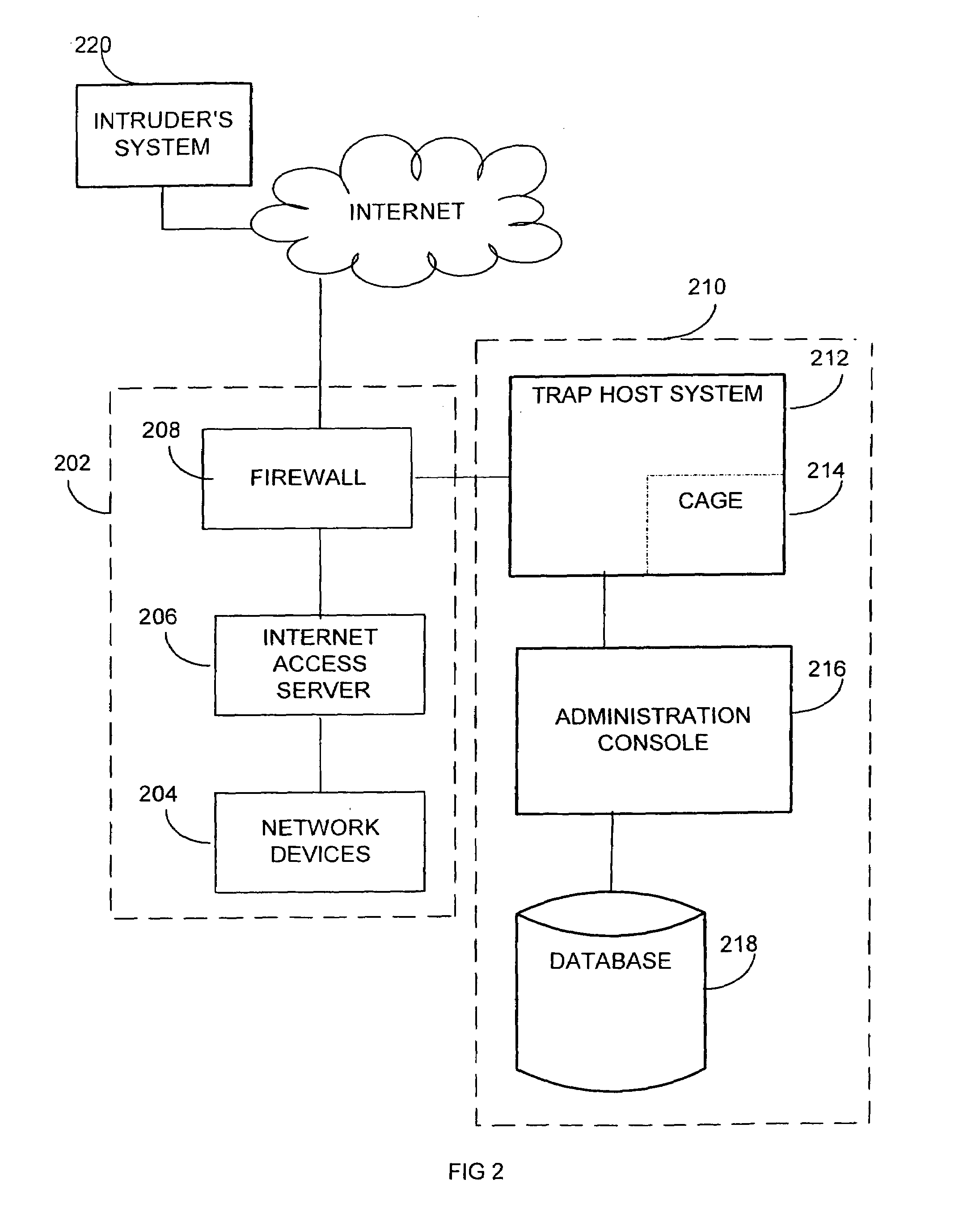
Automated containment of network intruder
InactiveUS20070192862A1Network degradationLow costMemory loss protectionError detection/correctionAutomatic controlVirtual LAN
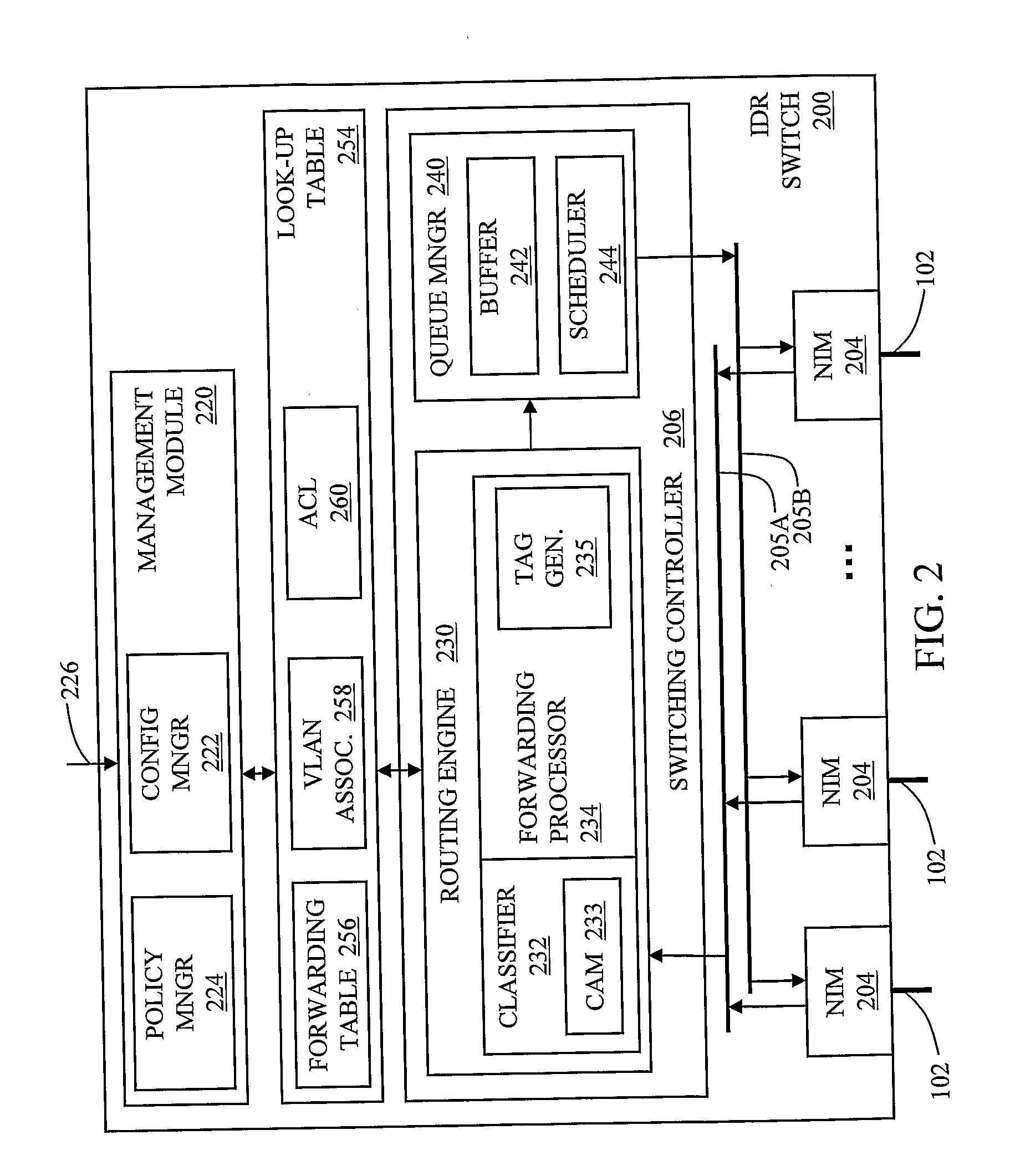
The invention in the preferred embodiment features a system (200) and method for automatically segregating harmful traffic from other traffic at a plurality of network nodes including switches and routers. In the preferred embodiment, the system (200) comprises an intrusion detection system (105) to determine the identity of an intruder and a server (130) adapted to automatically install an isolation rule on the one or more network nodes (114, 115, 116) to quarantine packets from the intruder. The isolation rule in the preferred embodiment is a virtual local area network (VLAN) rule or access control list (ACL) rule that causes the network node to route any packets from the intruder into a quarantine VLAN or otherwise isolate the traffic from other network traffic. In large networks, the isolation rule may be installed on a select plurality of network nodes under the gateway router (104) associated with the node at which the intruder first entered the network (100).
Owner:VERMEULEN VINCENT +1
System and method for host and network based intrusion detection and response
InactiveUS7134141B2Accurate measurementFewer false positivesData processing applicationsMemory loss protectionOperational systemCritical system
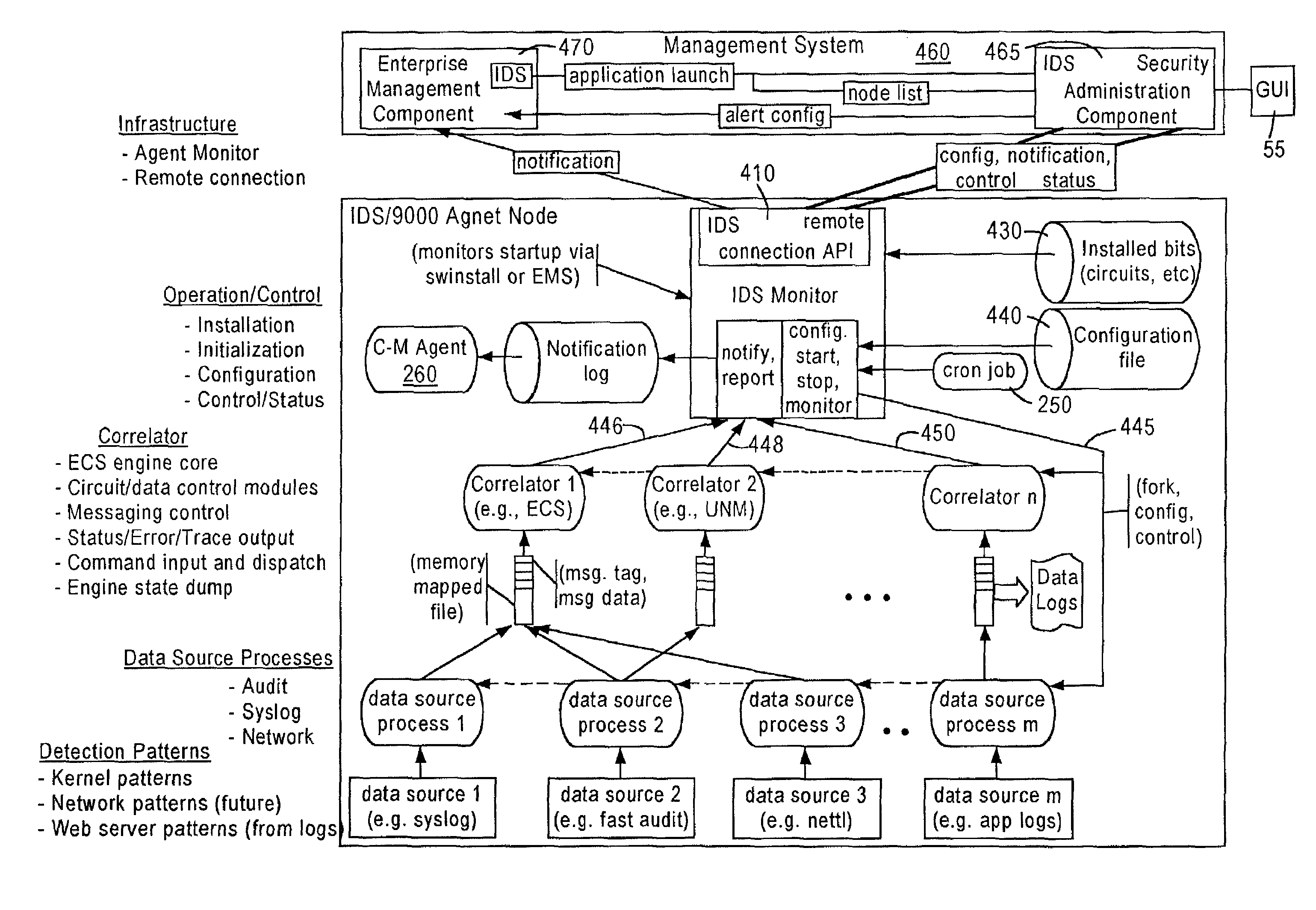
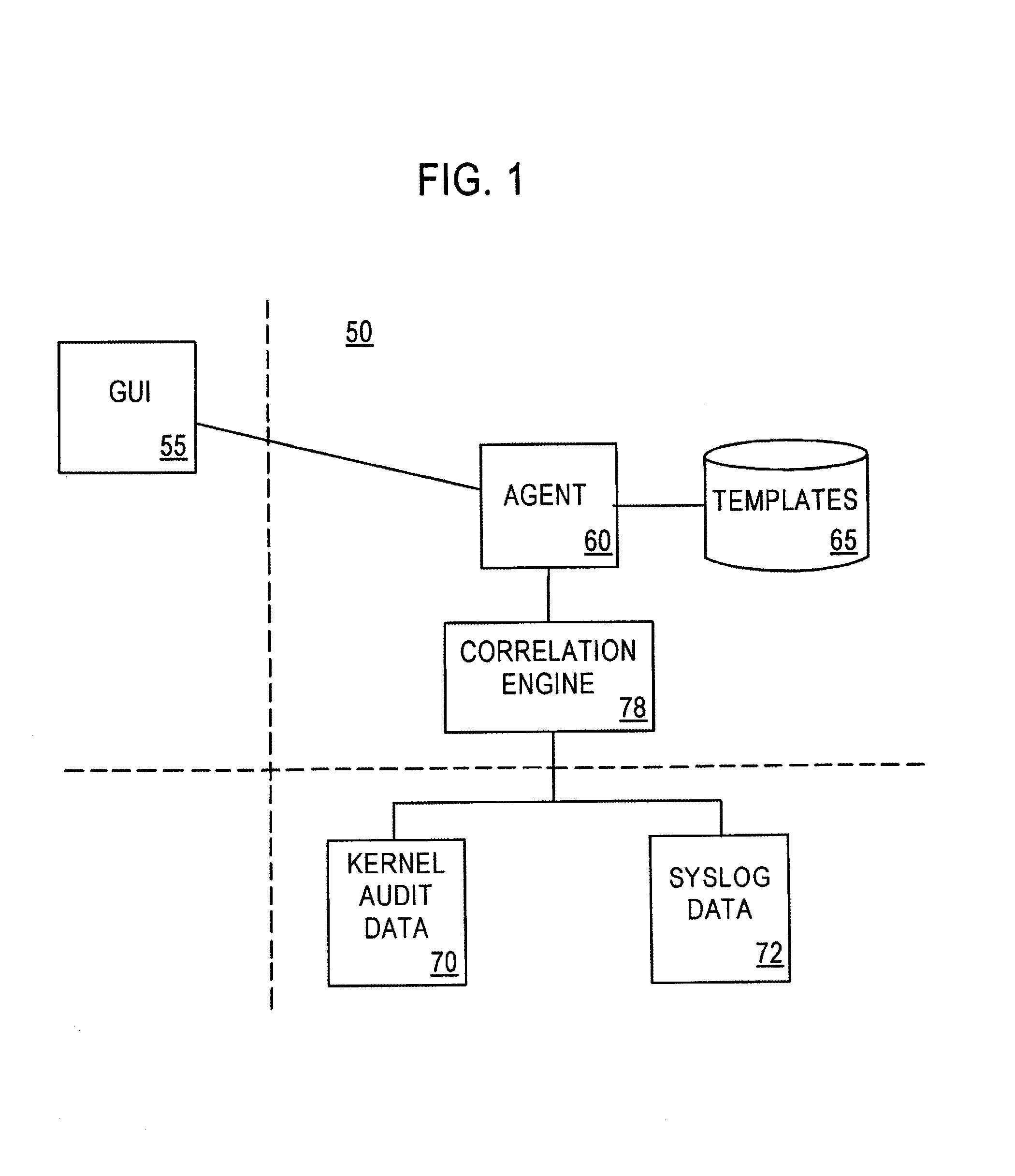
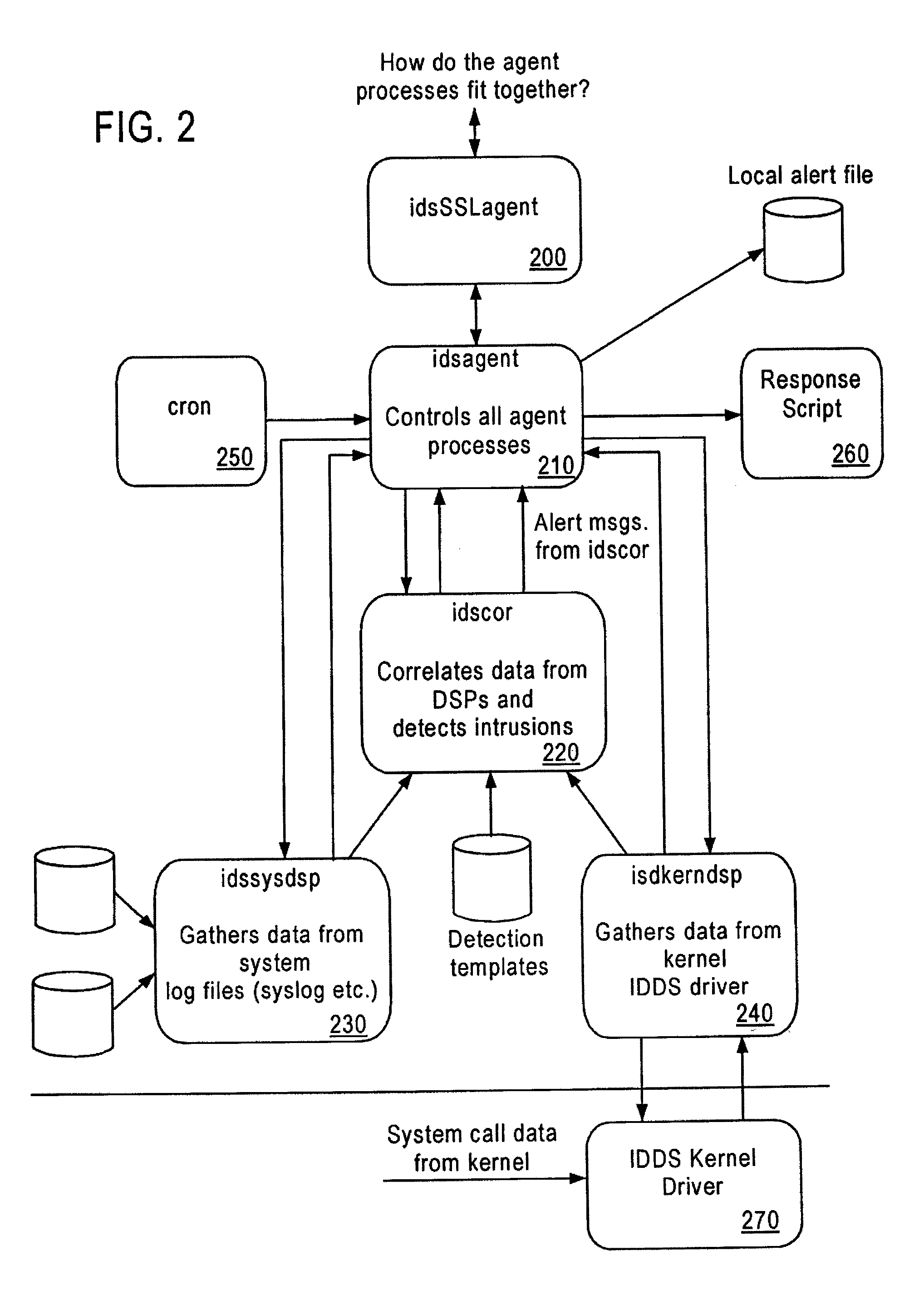
The present application is directed to a host-based IDS on an HP-UX intrusion detection system that enhances local host-level security within the network. It should be understood that the present invention is also usable on, for example, Eglinux, solaris, aix windows 2000 operating systems. It does this by automatically monitoring each configured host system within the network for possible signs of unwanted and potentially damaging intrusions. If successful, such intrusions could lead to the loss of availability of key systems or could compromise system integrity.
Owner:HEWLETT PACKARD DEV CO LP
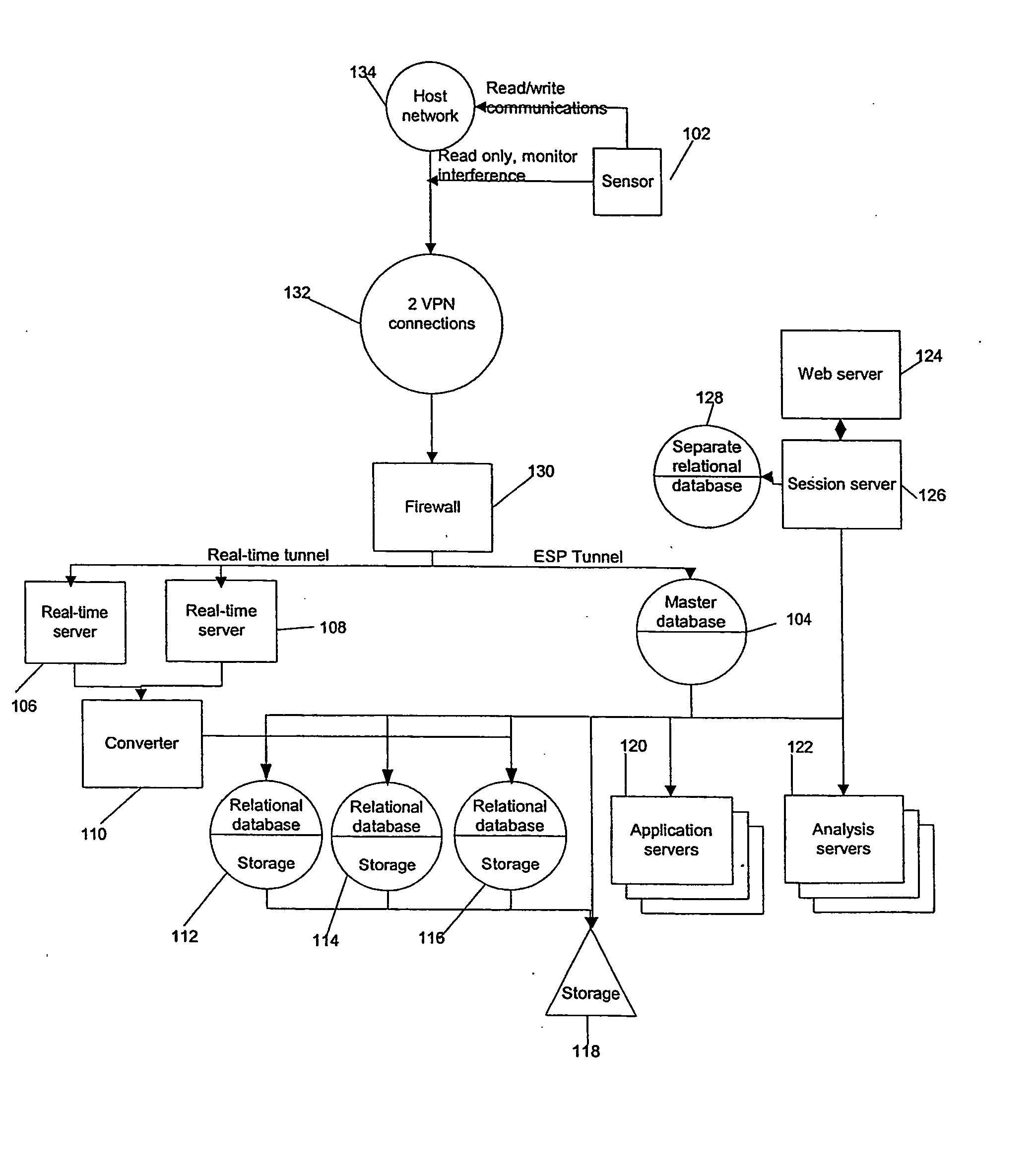
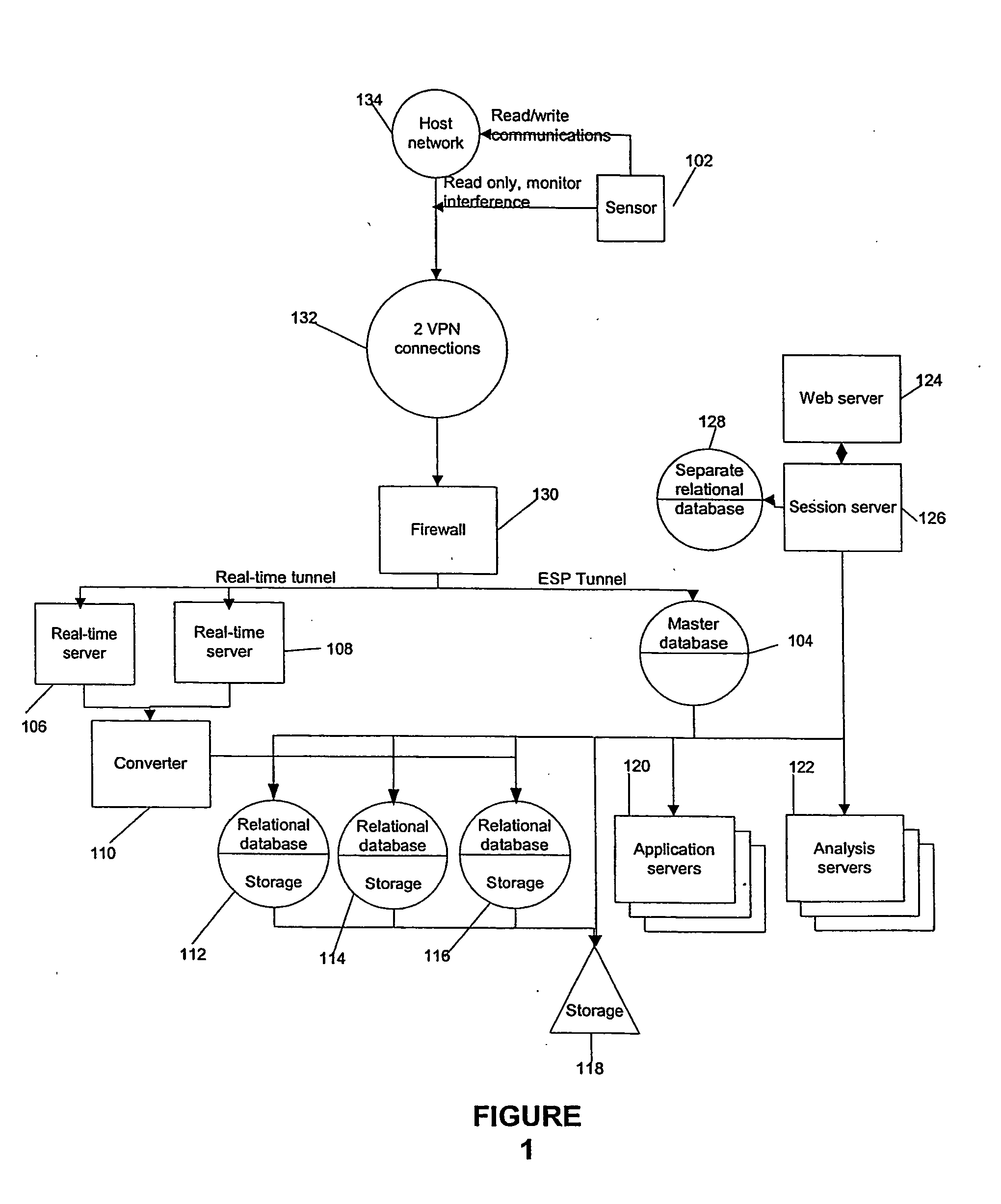
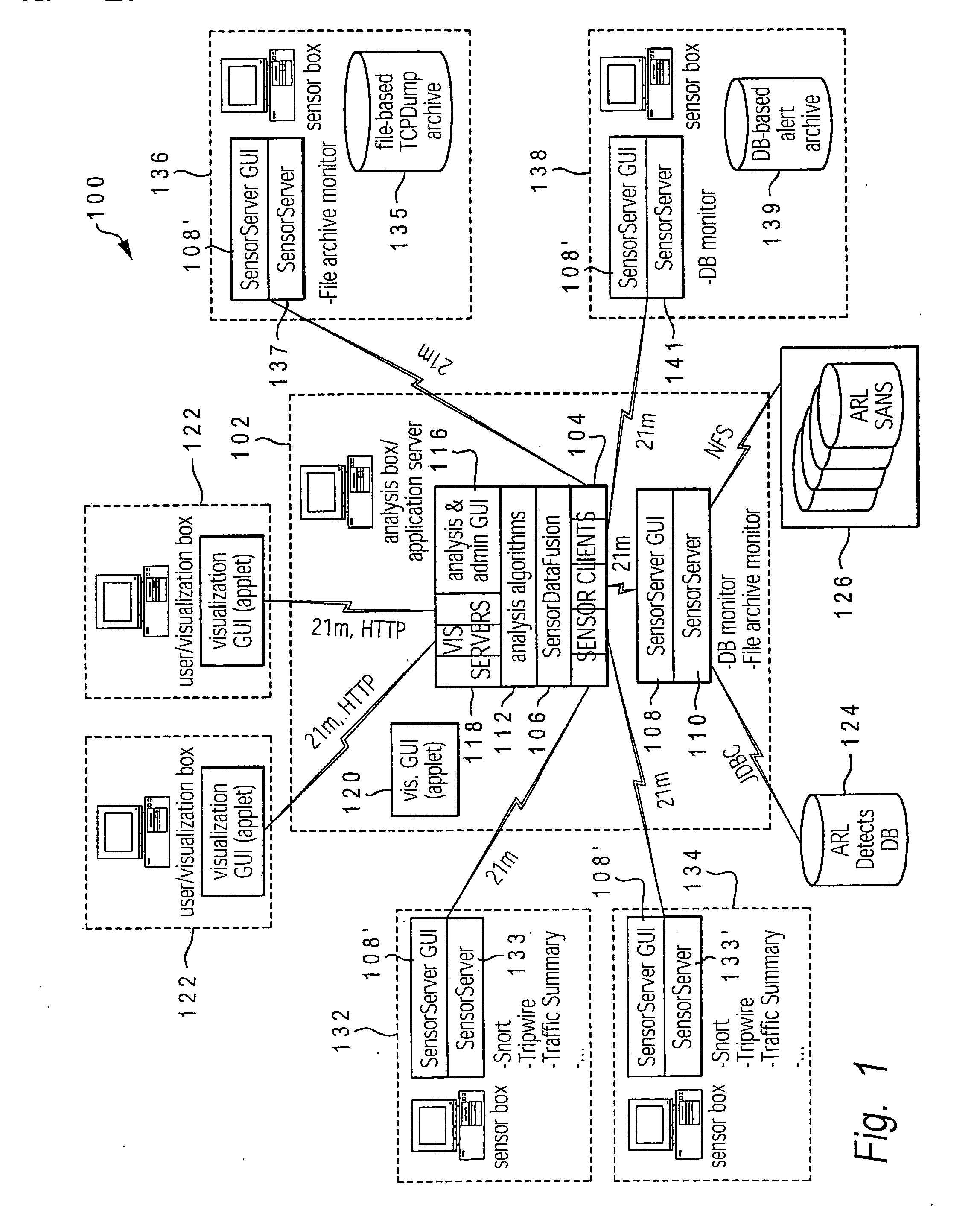
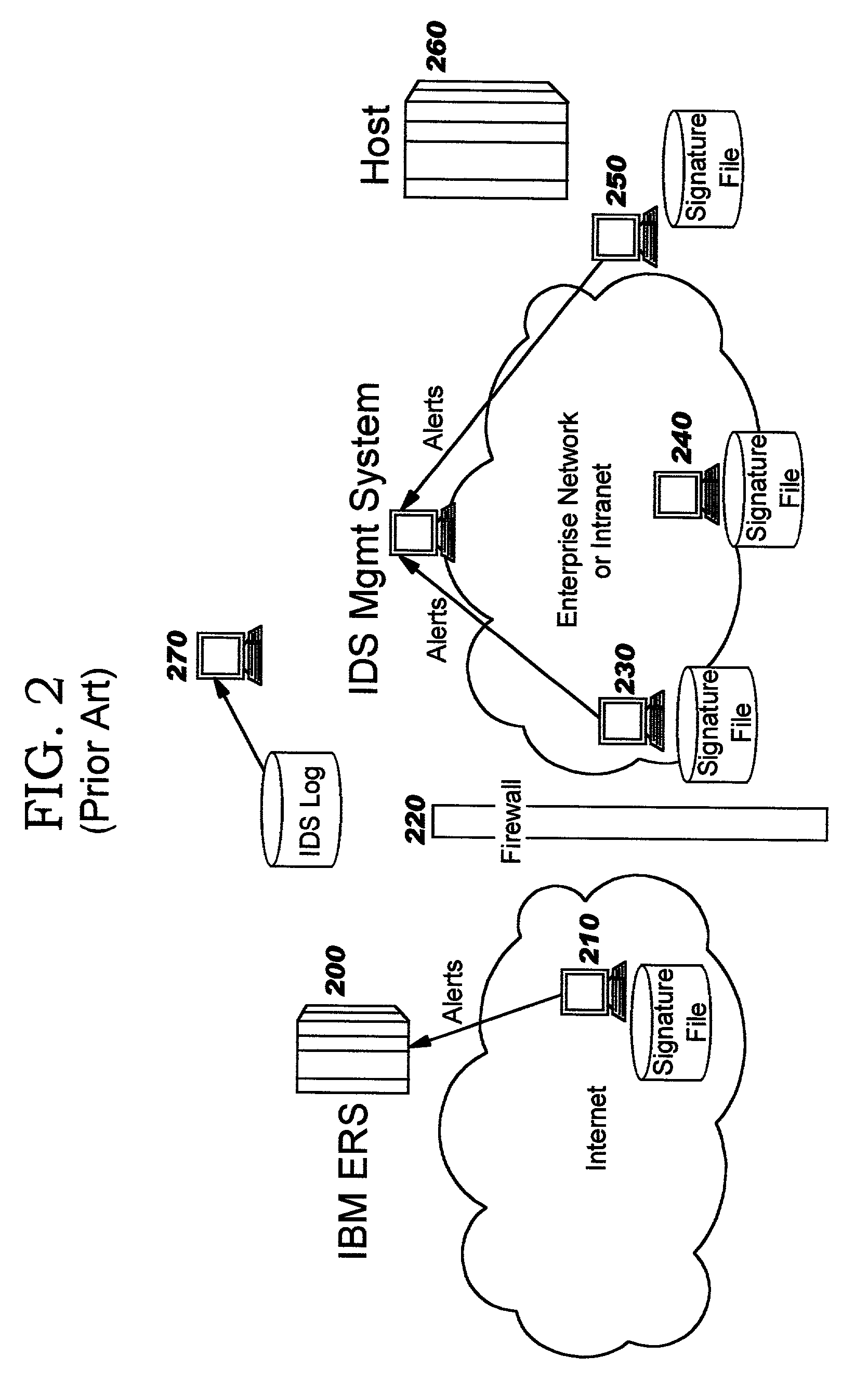
Method and system for managing computer security information
InactiveUS7089428B2Efficient managementMemory loss protectionDigital data processing detailsInternet trafficSafety management systems
A security management system includes a fusion engine which “fuses” or assembles information from multiple data sources and analyzes this information in order to detect relationships between raw events that may indicate malicious behavior and to provide an organized presentation of information to consoles without slowing down the processing performed by the data sources. The multiple data sources can comprise sensors or detectors that monitor network traffic or individual computers or both. The sensors can comprise devices that may be used in intrusion detection systems (IDS). The data sources can also comprise firewalls, audit systems, and other like security or IDS devices that monitor data traffic in real-time. The present invention can identify relationships between one or more real-time, raw computer events as they are received in real-time. The fusion engine can also assess and rank the risk of real-time raw events as well as mature correlation events.
Owner:INT BUSINESS MASCH CORP
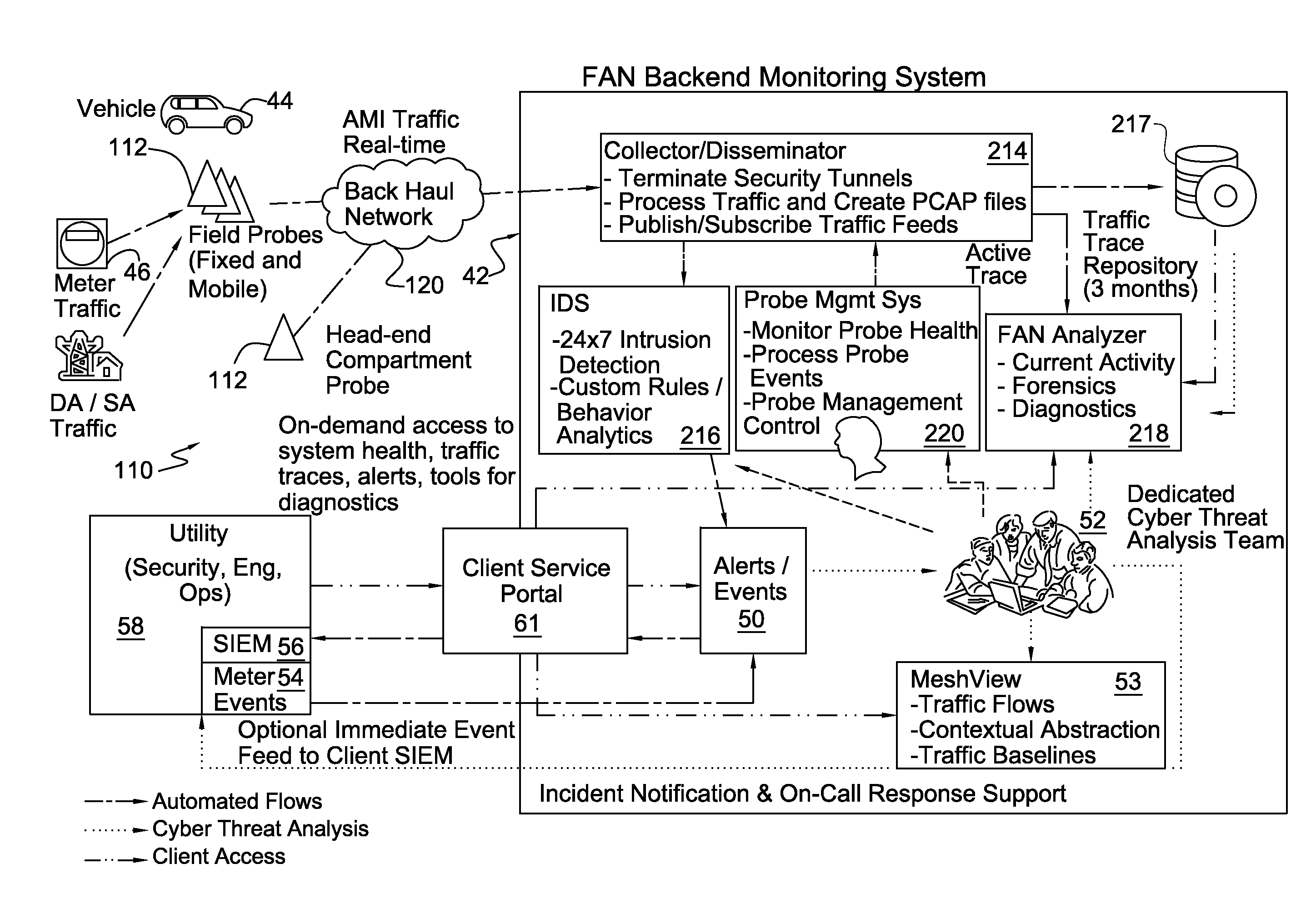
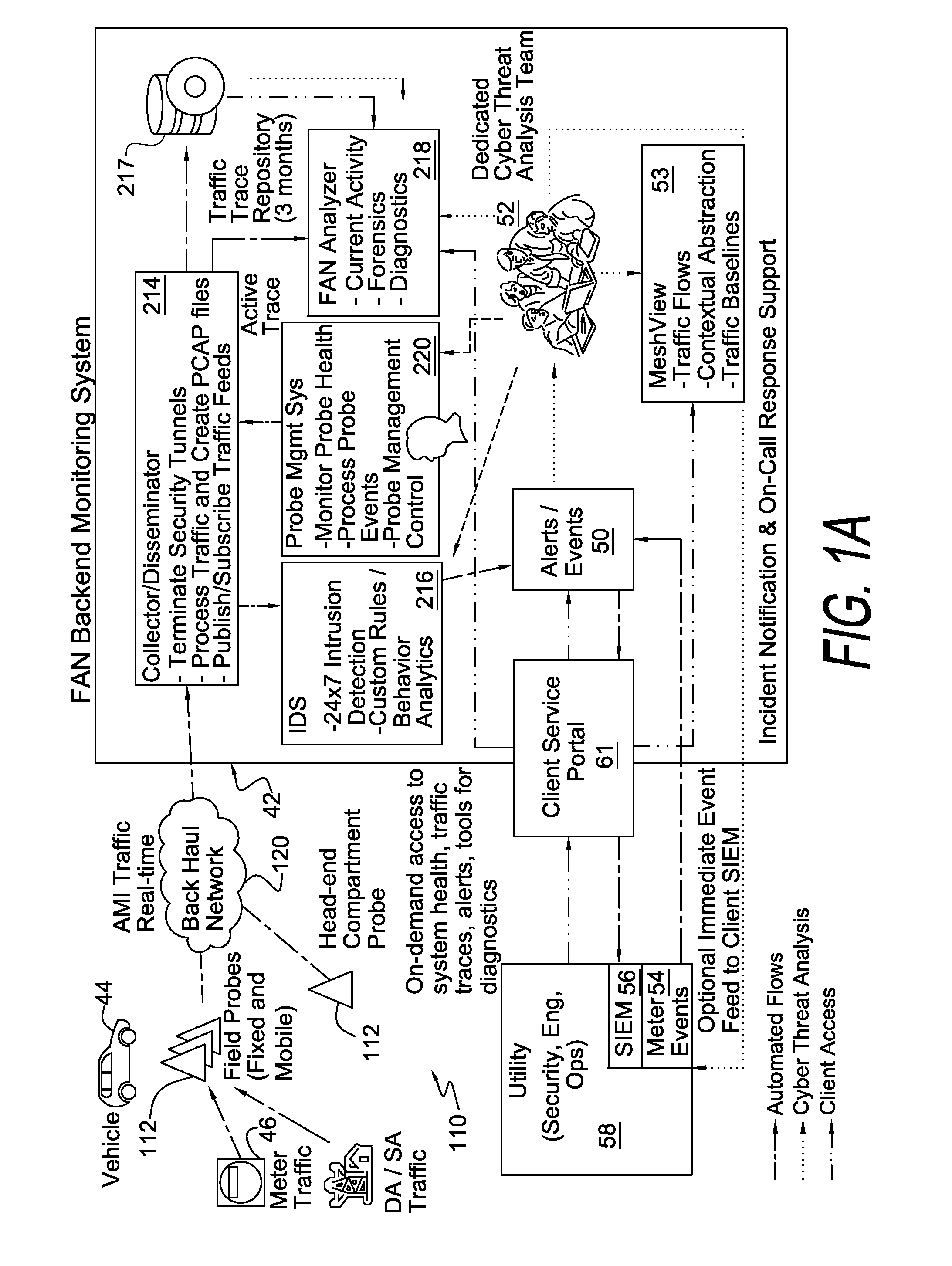
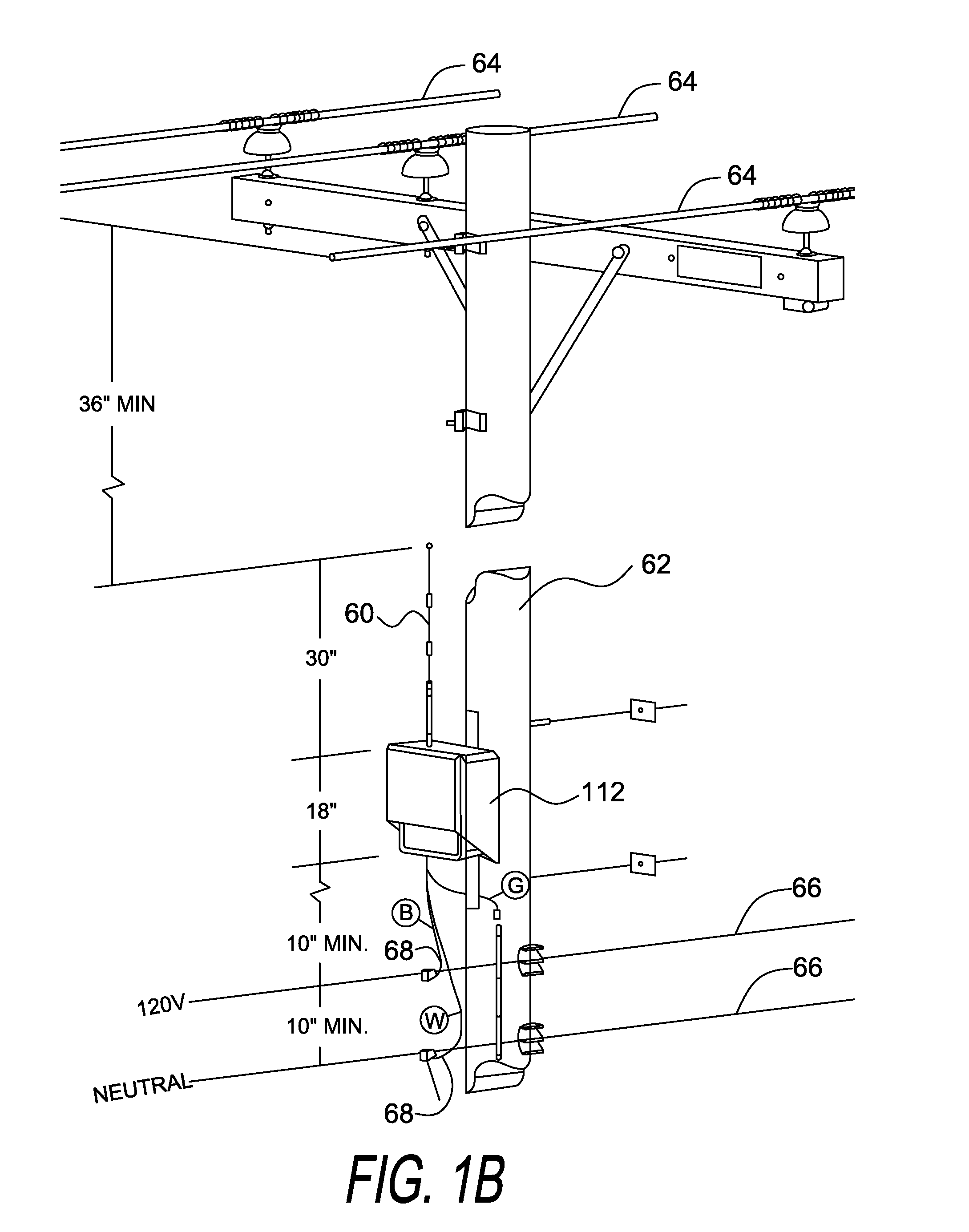
Method and system for packet acquisition, analysis and intrusion detection in field area networks
ActiveUS20130227689A1Memory loss protectionError detection/correctionIntrusion detection systemTraffic volume
A system for intrusion detection in a field area network where data is transmitted via packets, includes a processor for analyzing the packets to ascertain whether the packets conform to a sets of rules indicating an intrusion, and a database for storing an alert indicating an intrusion if the packets conform to at least one rule in the sets. The sets of rules are for field network layer data, internet protocol traffic data and field area application traffic data. A method for detecting intrusion in a field area network where data is transmitted via packets, including analyzing the packets to ascertain whether the packets conform to the sets of rules, and storing an alert indicating an intrusion if the packets conform to at least one rule in the sets of rules.
Owner:PERSPECTA LABS INC
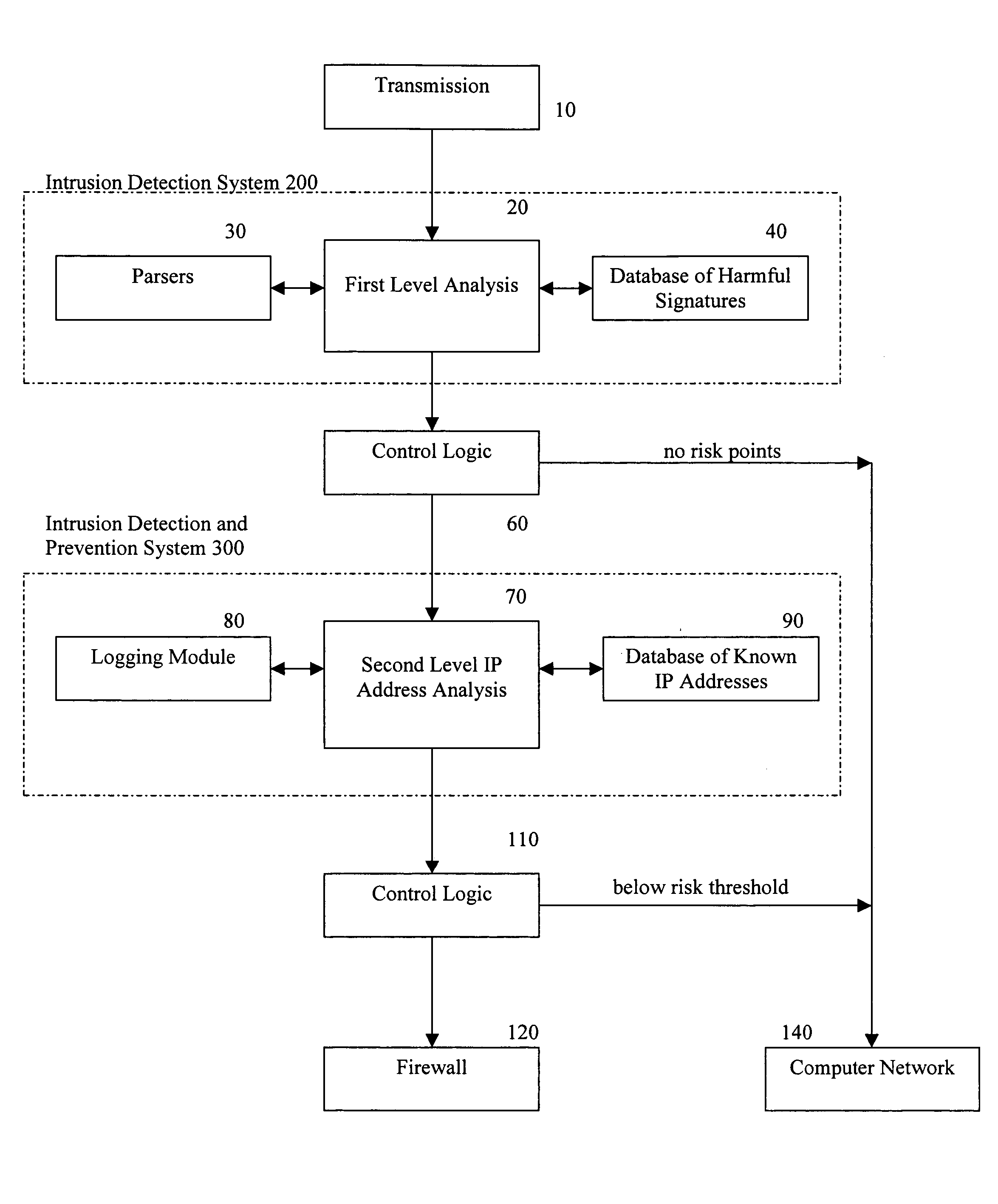
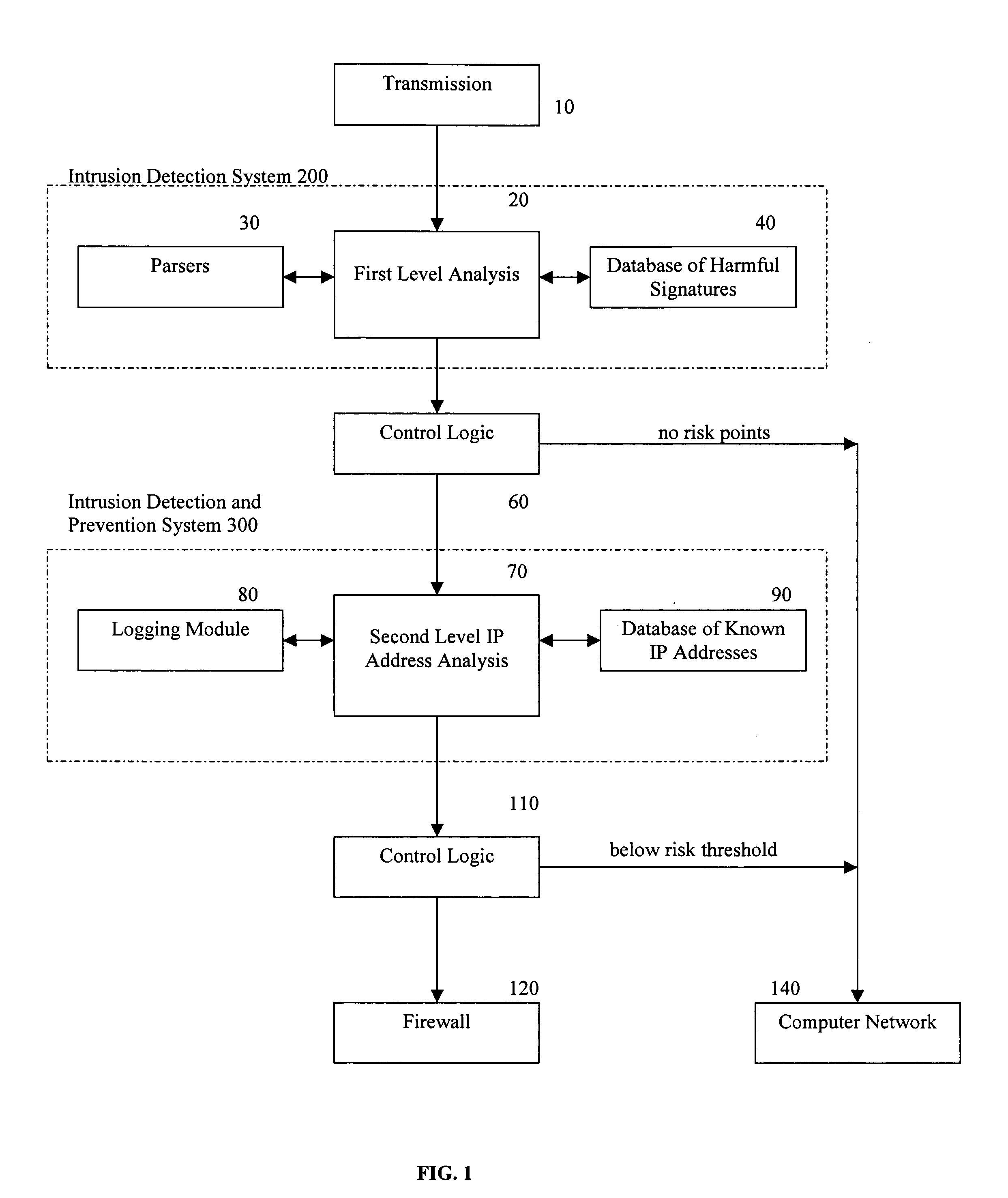
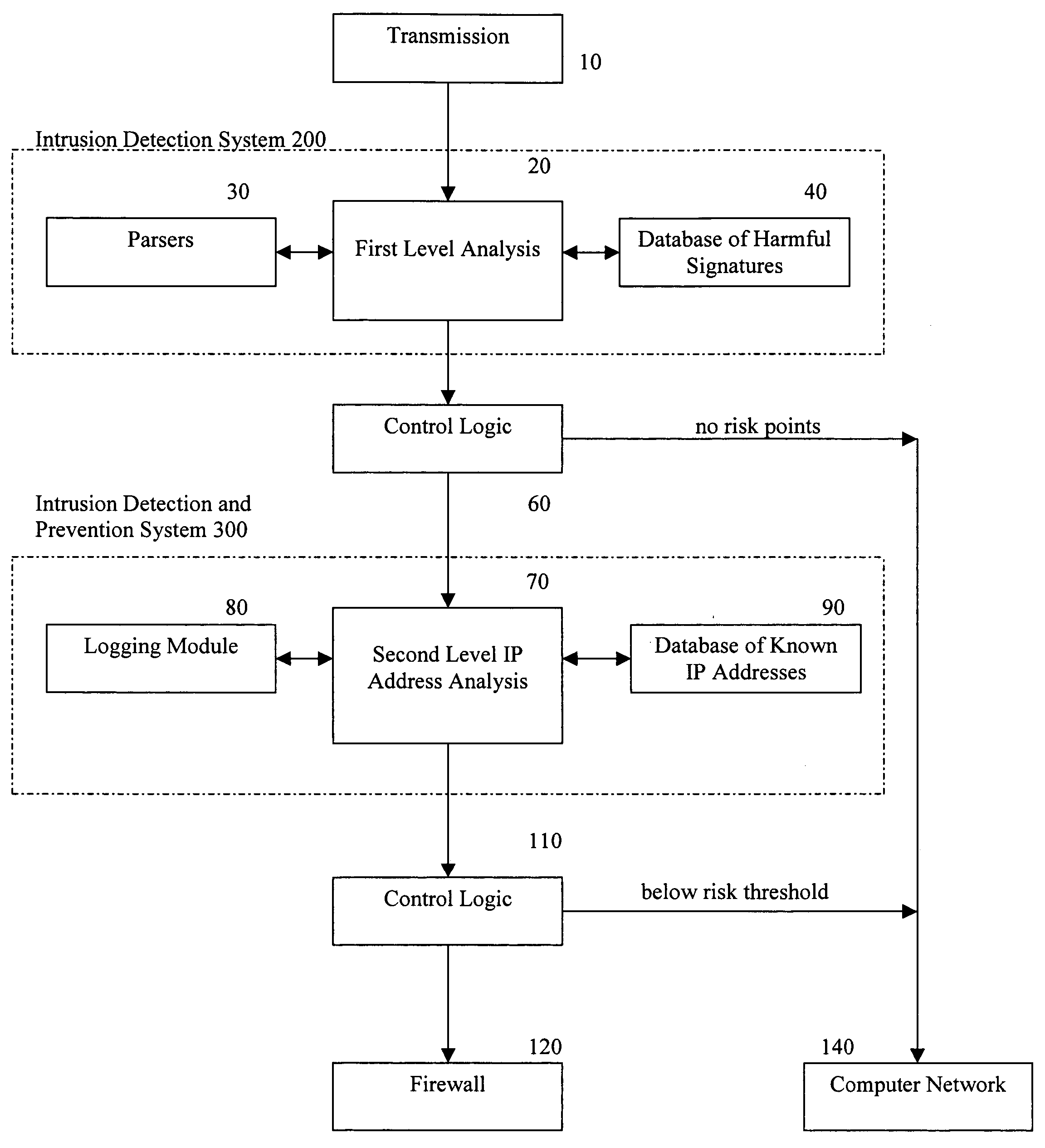
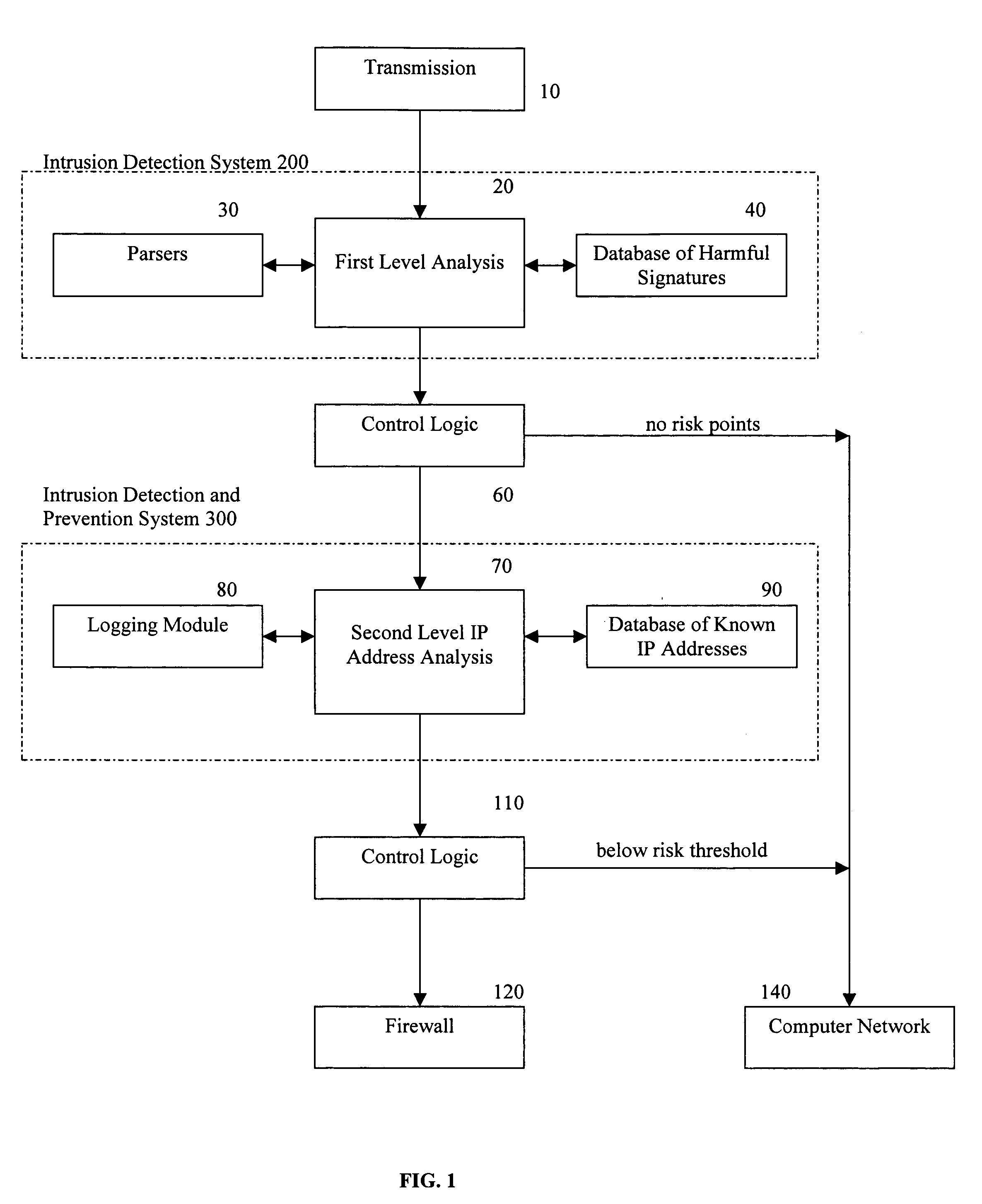
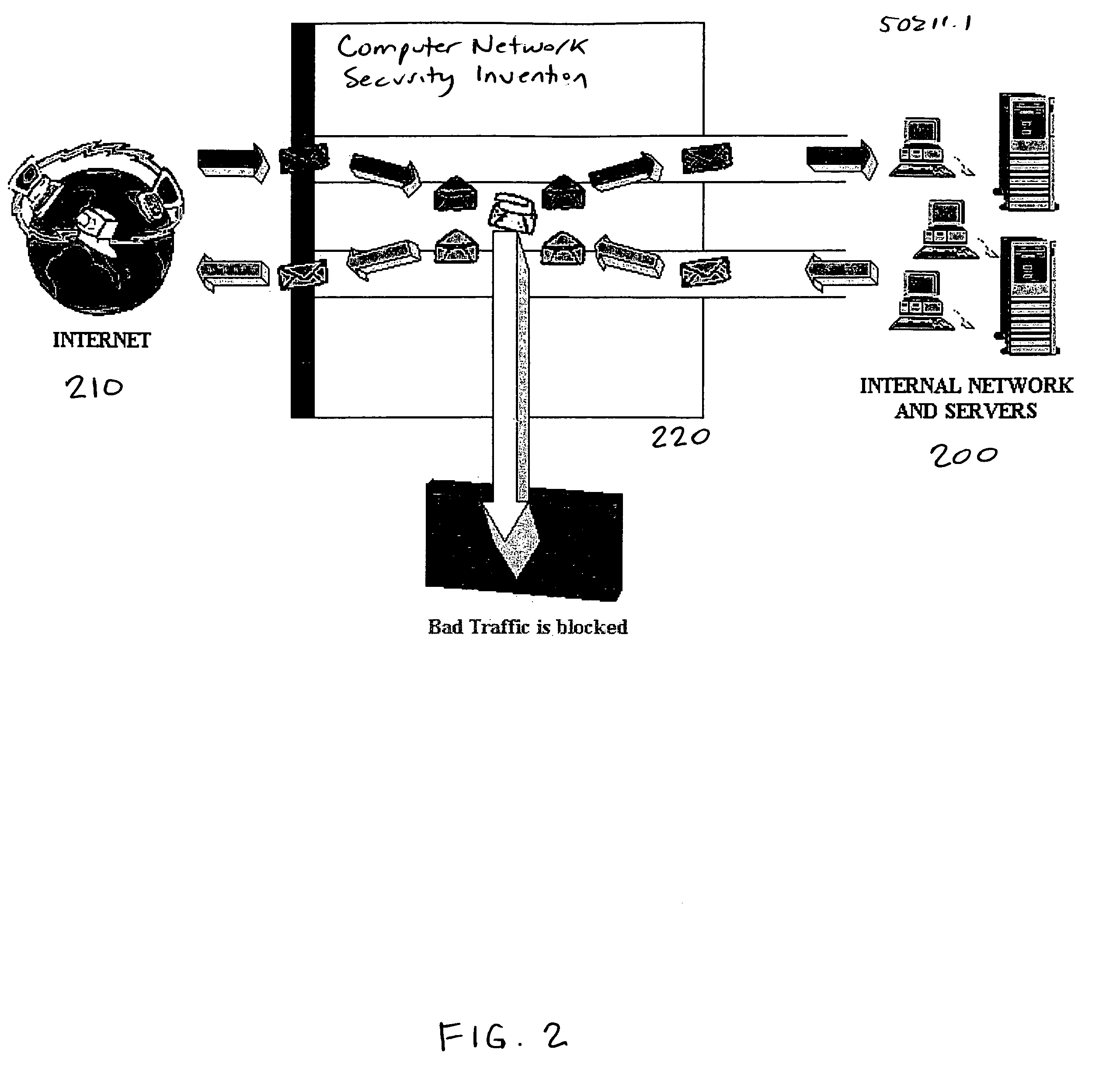
Methods and apparatus for computer network security using intrusion detection and prevention
InactiveUS20050262556A1Overcome disadvantagesMemory loss protectionDigital data processing detailsIp addressIntrusion detection and prevention
A method for providing security to a computer network by selectively blocking network transmissions from selected IP addresses comprising the steps of: establishing a risk threshold whereby transmissions from IP addresses exceeding said risk threshold are selectively blocked; receiving a network transmission having an originating IP address and payload; analyzing the payload of said transmission and assigning a current risk rating to said IP address on the basis of said analysis; comparing the originating IP address of said transmission to a database of known IP addresses, each of said said previous cumulative assigned risk rating being based on at least one previous transmission from a known IP address; known IP addresses having a previous cumulative assigned risk rating, assigning a new cumulative risk rating to said originating IP address, said new cumulative risk rating being the sum of said current risk rating and said previous cumulative assigned risk rating for said originating IP address, with the proviso that where said originating IP address is not contained in said database of known IP addresses, the new cumulative risk rating will equal the current risk rating; logging the new cumulative risk rating for said originating IP address in said database of known IP addresses, with the proviso that where the originating IP address of said transmission is not contained in said database of known IP addresses, a new record is created for the originating IP address and said new cumulative risk rating in said database of known IP addresses; comparing said new cumulative risk rating to said risk threshold; and automatically blocking said transmission if said new cumulative risk rating exceeds said risk threshold.
Owner:DIGITAL SECURITY NETWORK
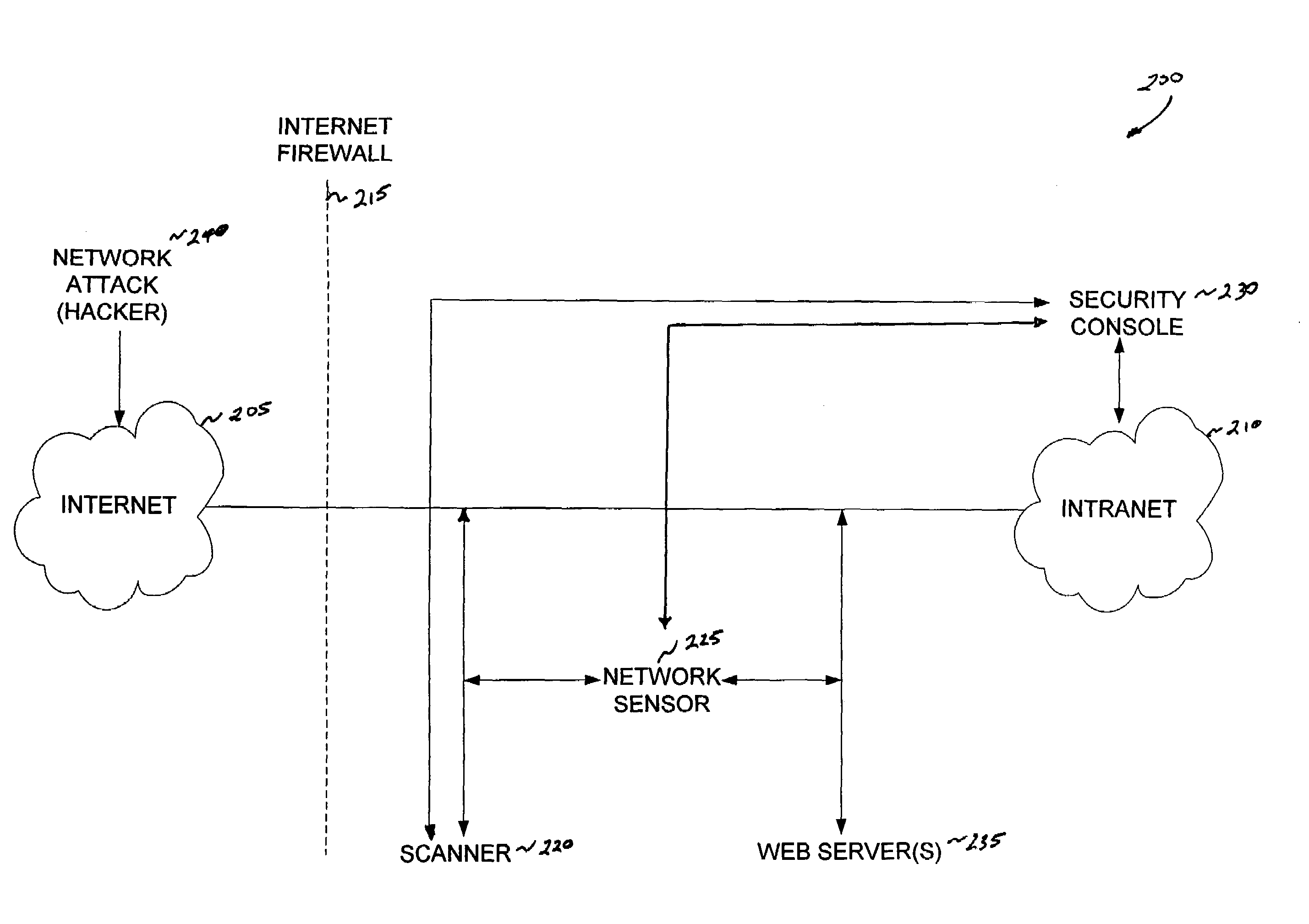
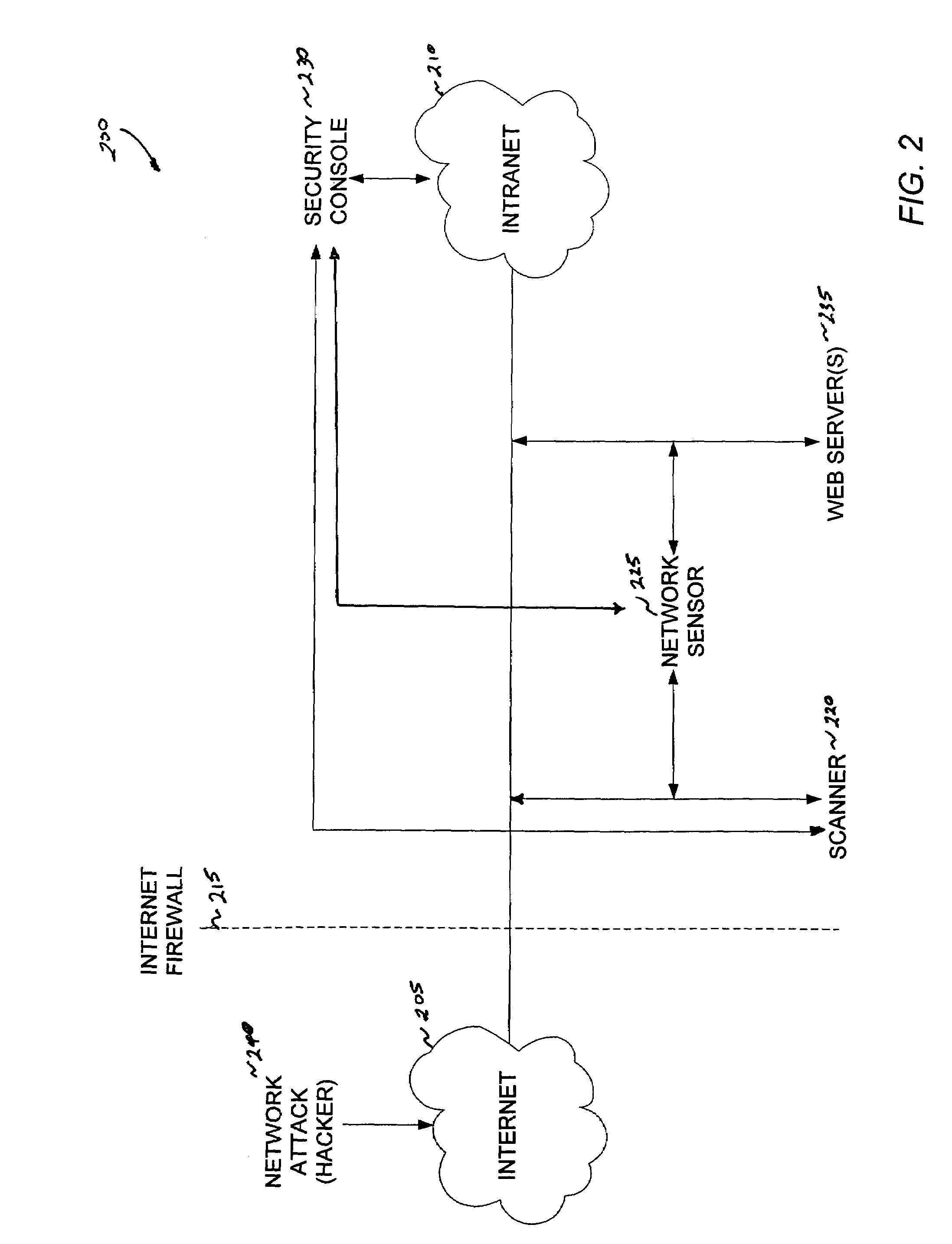
Method and system for intrusion detection in a computer network
InactiveUS7574740B1Memory loss protectionError detection/correctionDatabase intrusion detectionVulnerability
An intrusion detection system for detecting intrusion events in a computer network and assessing the vulnerability of the network components to the detected events. The intrusion detection system comprises a scanner, one or more sensors and a security console for operation within a networked computing environment. A sensor of the inventive intrusion detection system can monitor the networked computing environment for possible intrusion events representing an unauthorized access or use of the network resources. In response to detecting an intrusion event, the sensor can generate a scan request for handling by a scanner. This request initiates a scan of the target computer by the scanner to determine the vulnerability of the target to the attack. Based on this vulnerability analysis, the inventive intrusion detection system can evaluate the severity of the detected intrusion event and issue an alert having a priority corresponding to the severity of the intrusion.
Owner:IBM CORP
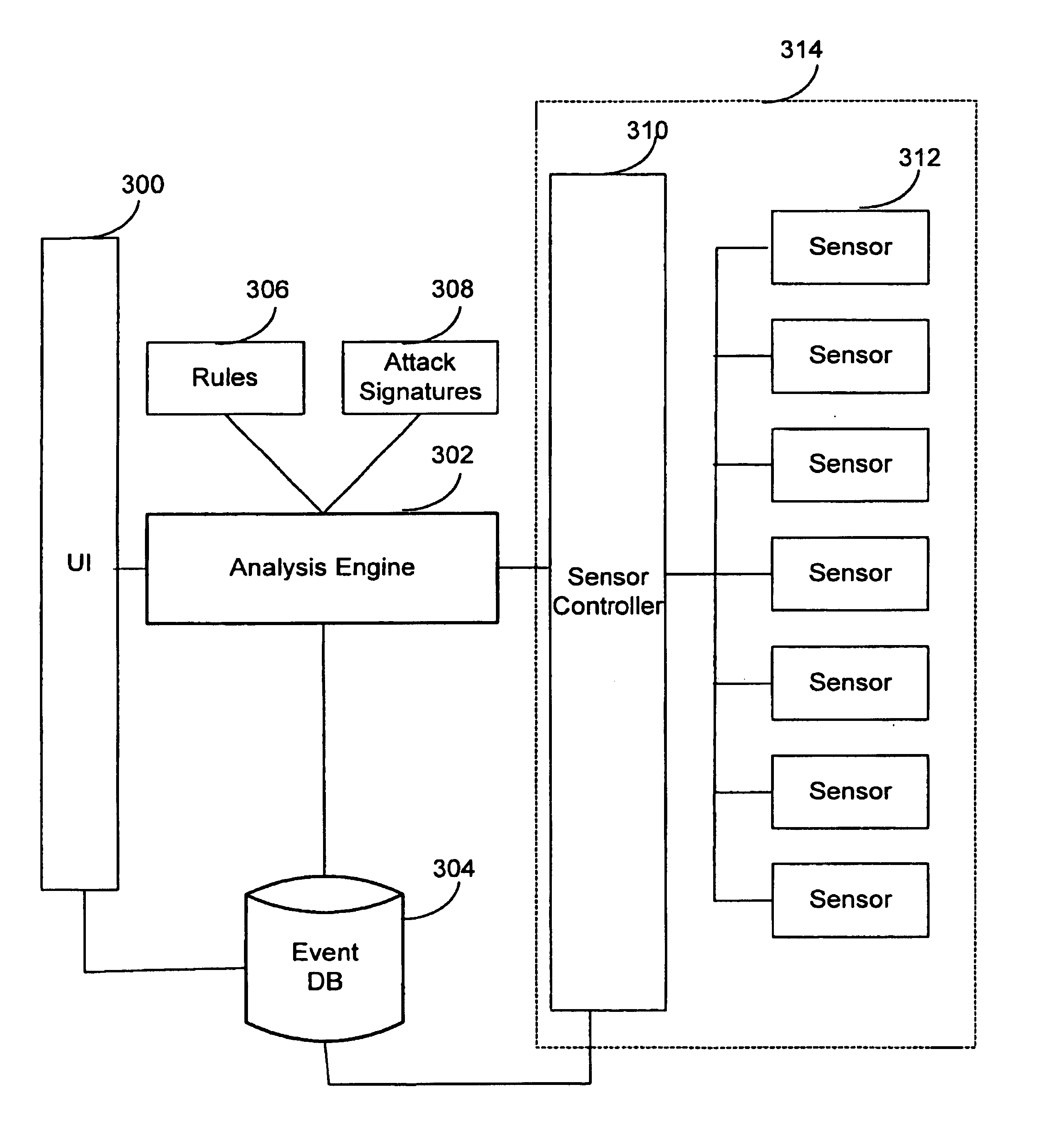
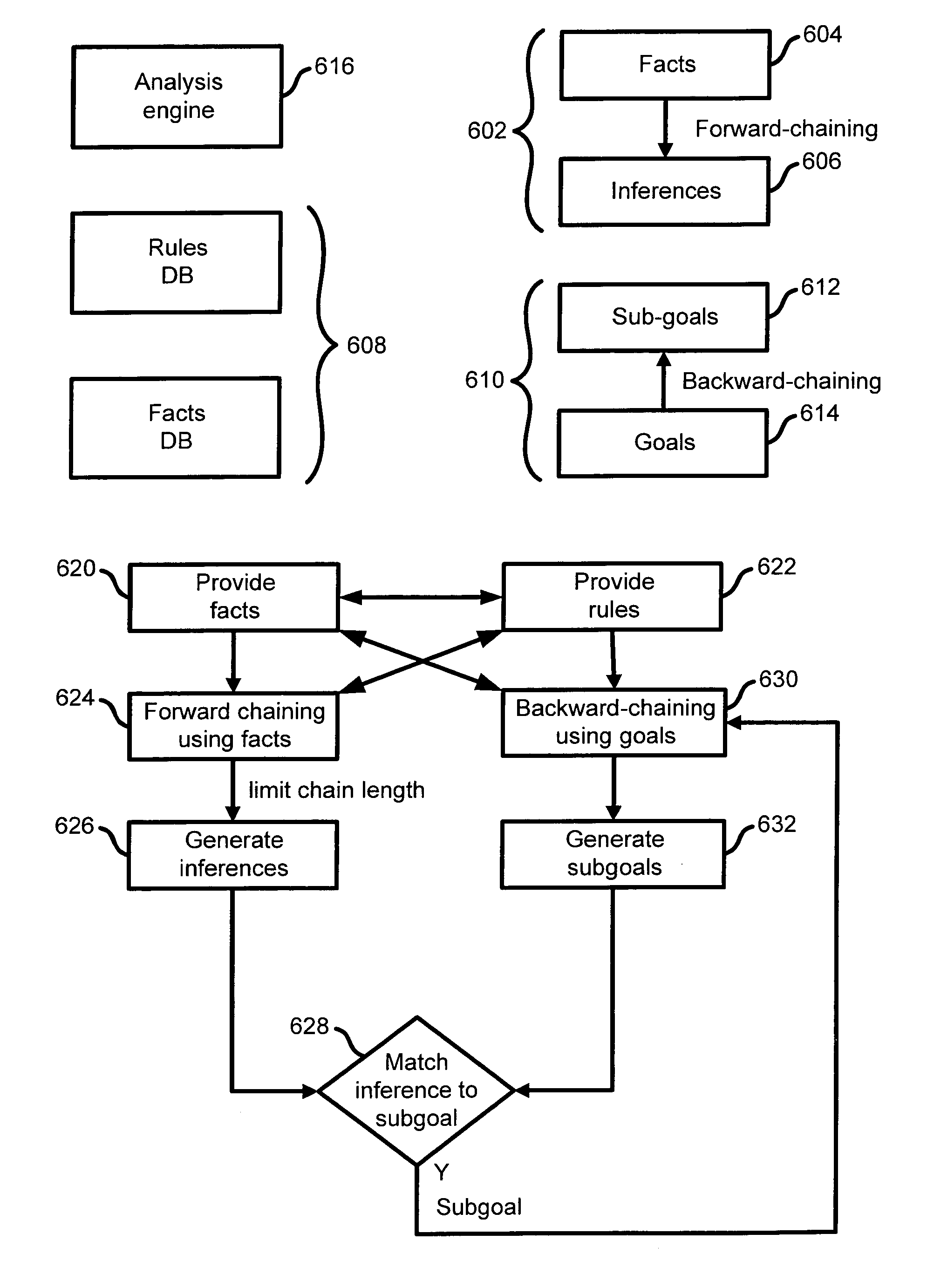
Extensible intrusion detection system
InactiveUS7065657B1Overcome problemsEnabling detectionDigital data processing detailsHardware monitoringTimestampAccess time
A system and method are disclosed for detecting intrusions in a host system on a network. The intrusion detection system comprises an analysis engine configured to use continuations and apply forward- and backward-chaining using rules. Also provided are sensors, which communicate with the analysis engine using a meta-protocol in which the data packet comprises a 4-tuple. A configuration discovery mechanism locates host system files and communicates the locations to the analysis engine. A file processing mechanism matches contents of a deleted file to a directory or filename, and a directory processing mechanism extracts deallocated directory entries from a directory, creating a partial ordering of the entries. A signature checking mechanism computes the signature of a file and compares it to previously computed signatures. A buffer overflow attack detector compares access times of commands and their associated files. The intrusion detection system further includes a mechanism for checking timestamps to identify and analyze forward and backward time steps in a log file.
Owner:SYMANTEC CORP
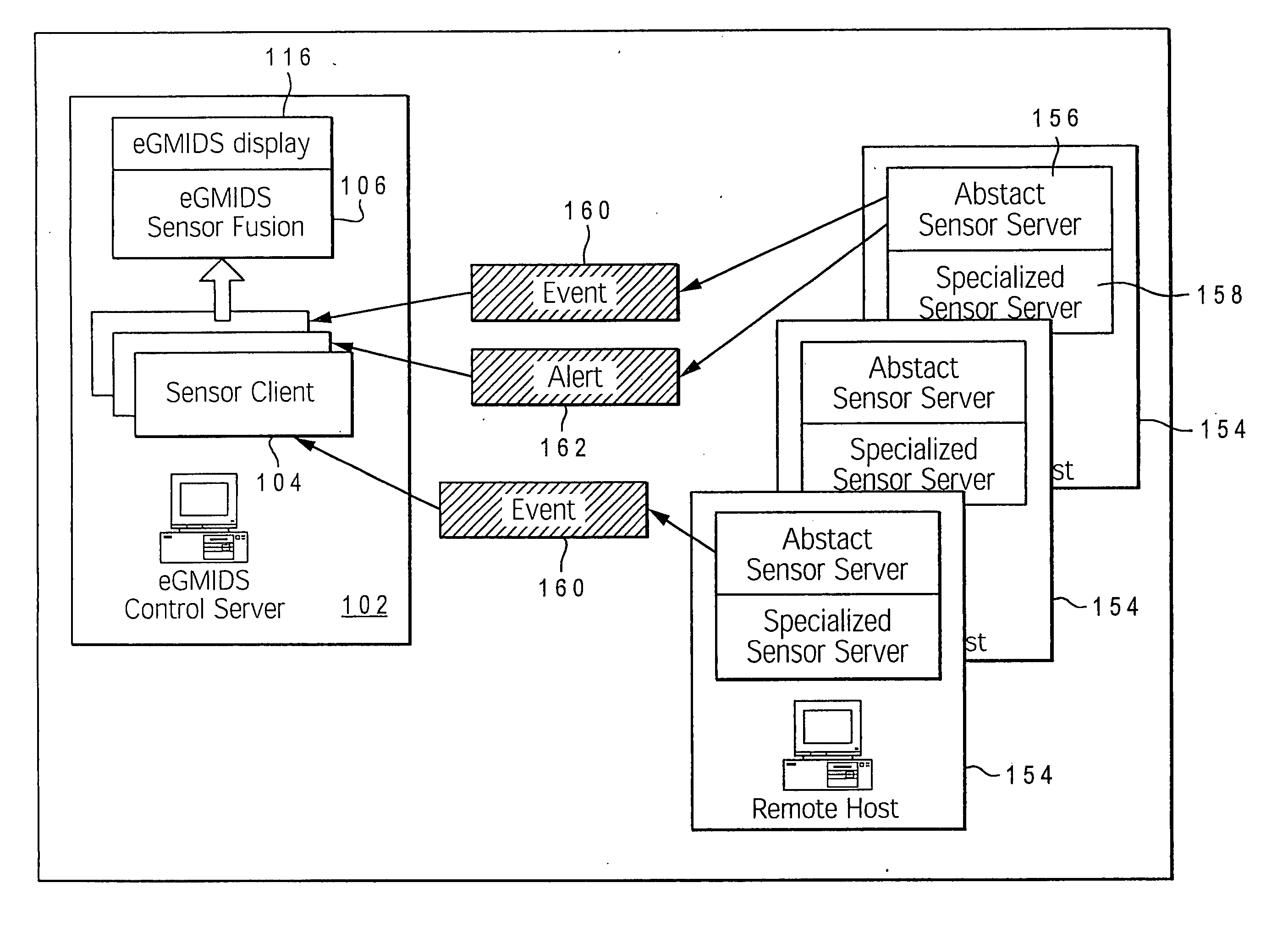
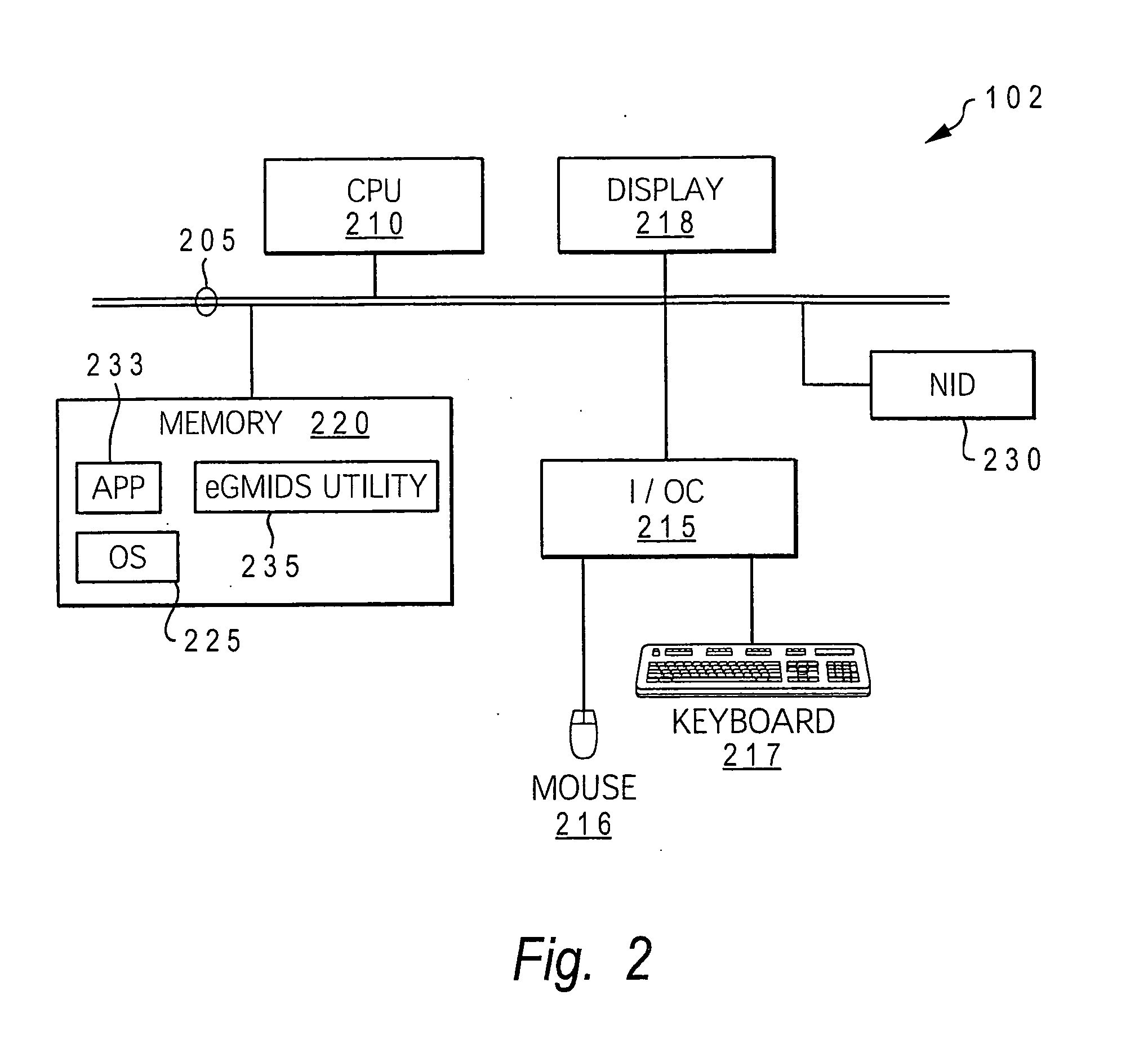
Intelligent intrusion detection system utilizing enhanced graph-matching of network activity with context data
ActiveUS20070209074A1Reduce in quantitySmall sizeMemory loss protectionError detection/correctionNetwork activityGraphics
A method, system, and computer program product for utilizing a mapping of activity occurring at and between devices on a computer network to detect and prevent network intrusions. An enhanced graph matching intrusion detection system (eGMIDS) is provided that provides data collection functions, data fusion techniques, graph matching algorithms, and secondary and other search mechanisms. Threats are modeled as a set of entities and interrelations between the entities and sample threat patterns are stored within a database. The eGMIDS utility initiates a graph matching algorithm by which the threat patterns are compared within the generated activity graph via subgraph isomorphism. A multi-layered approach including a targeted secondary layer search following a match during a primary layer search is provided. Searches are tempered by attributes and constraints and the eGMIDS reduces the number of threat patterns searched by utilizing ontological generalization.
Owner:NORTHROP GRUMMAN SYST CORP
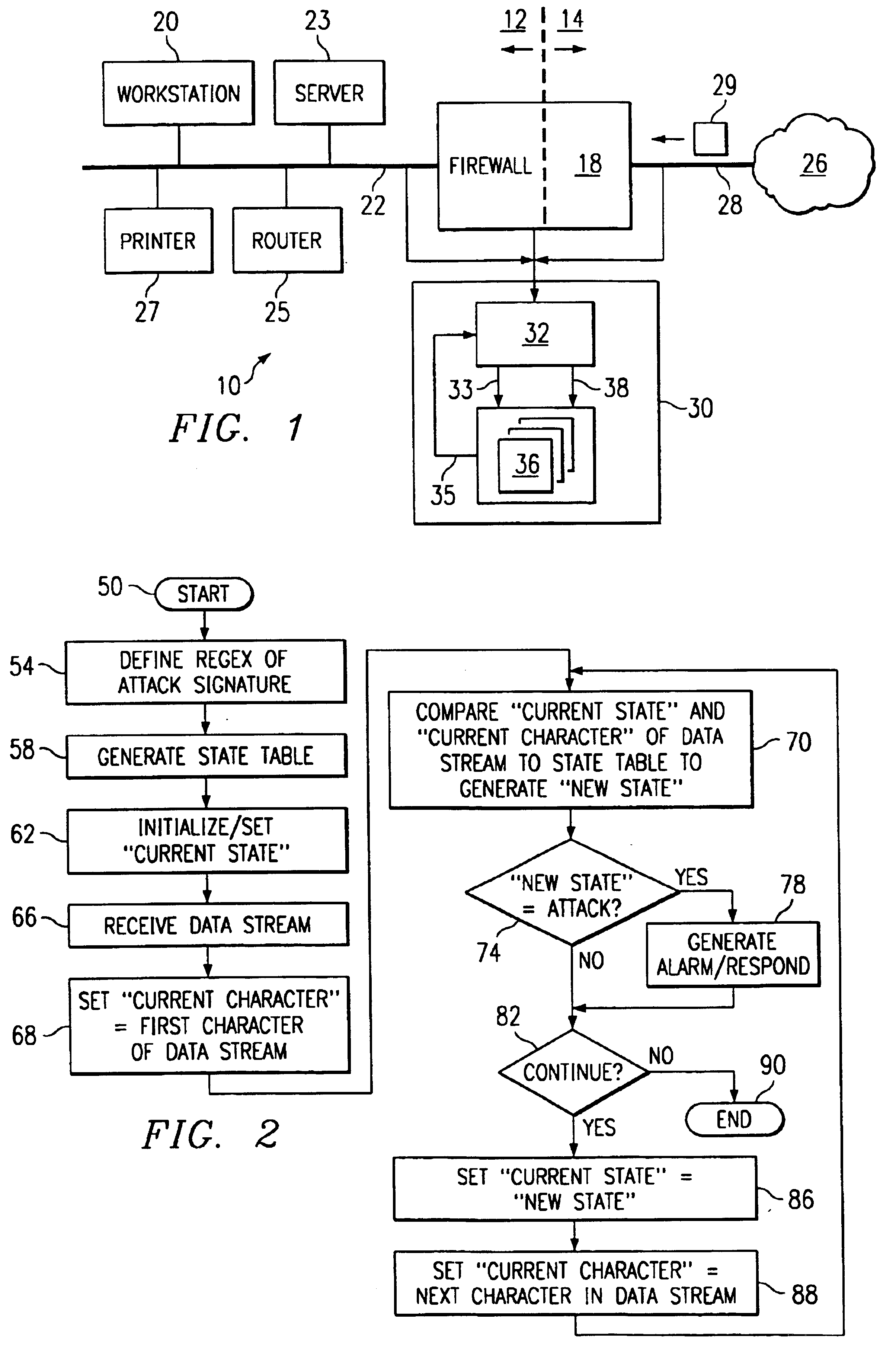
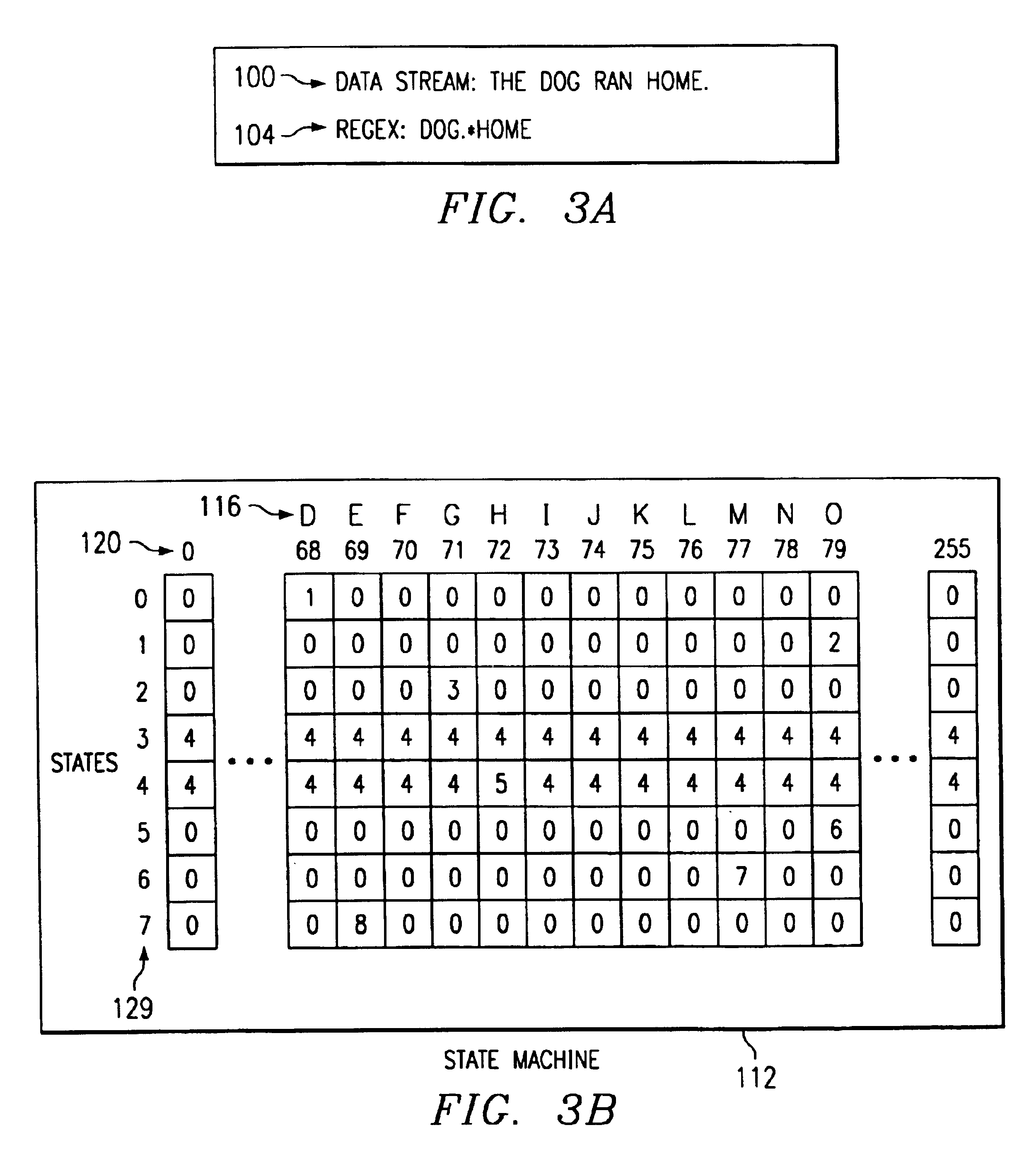
Binary state machine system and method for REGEX processing of a data stream in an intrusion detection system
InactiveUS6880087B1Reduce needPreserve memory resourceMemory loss protectionCode conversionData streamTheoretical computer science
A binary state machine system and method for REGEX processing of a data stream in an intrusion detection system are disclosed. The method comprises maintaining a state table. The state table is indexed such that inputs comprising a current state and a current character yield an output of a new state. The new state is related to an indication of an attack on a computer network. The method further includes maintaining the current state. An input stream comprising a plurality of characters is received. A first character of the input stream is selected as the current character. The current character and the current state are compared to the state table to generate a new state.
Owner:CISCO TECH INC
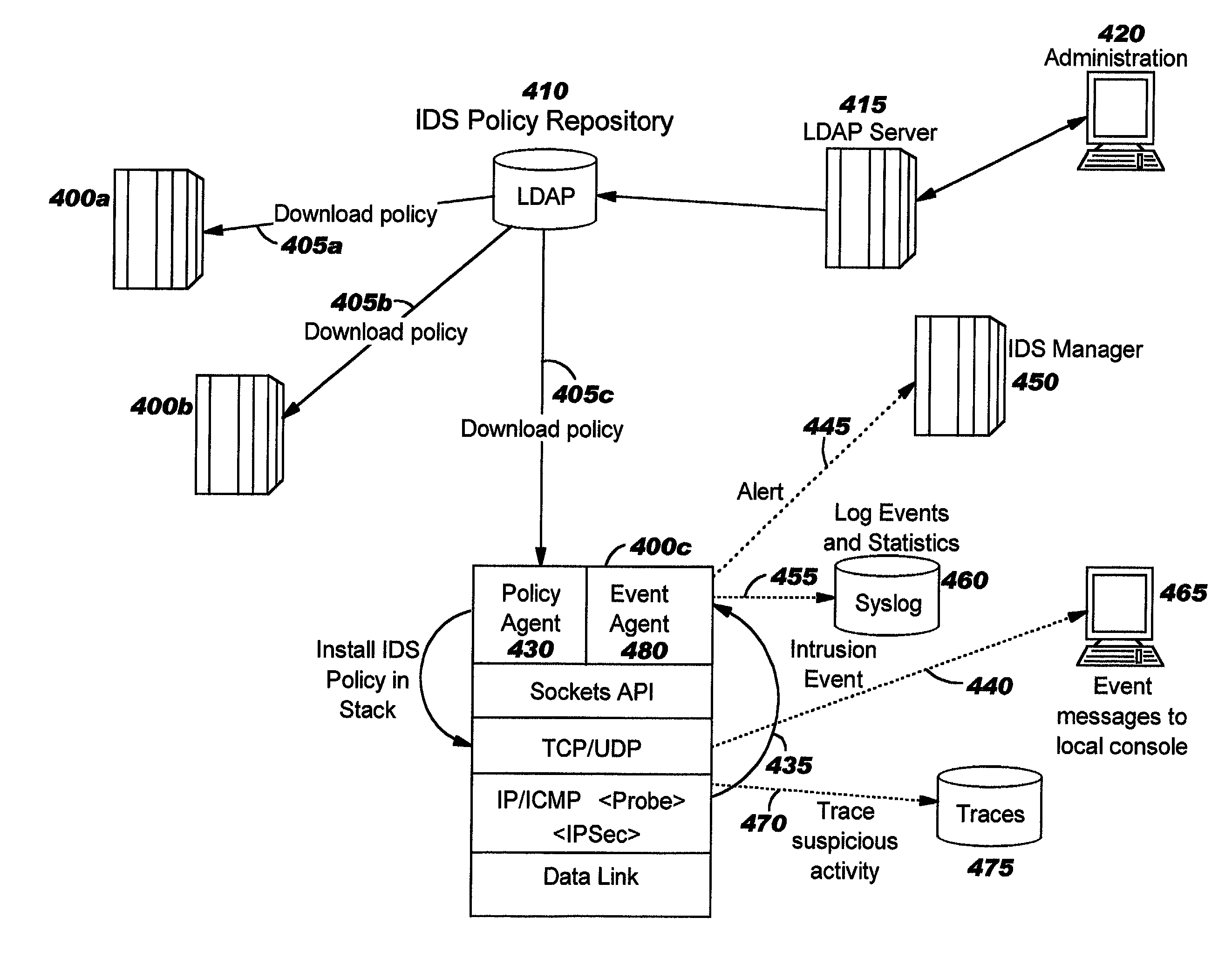
Integrated intrusion detection services
ActiveUS7076803B2Improve securityEasy to detectMemory loss protectionError detection/correctionTraffic capacityPlaintext
Improvements in intrusion detection are disclosed by providing integrated intrusion detection services. Preferably, these services are integrated into a system or server that is the potential target of attack. Stack-based security processing is leveraged for access to cleartext data within the layers of the protocol stack. Layer-specific attacks may therefore be processed efficiently. Evaluation of incoming traffic for an intrusion is preferably performed only after an error condition of some type has been detected. This approach reduces the overhead of intrusion detection by reducing the number of packets to be inspected, and at the same time allows more efficient packet inspection through use of context-specific information that may be used to direct the inspection to particular candidate attacks. Generic attack class capability is also disclosed. Intrusion detection policy information may be used to direct the actions to be taken upon detecting an attack.
Owner:TREND MICRO INC
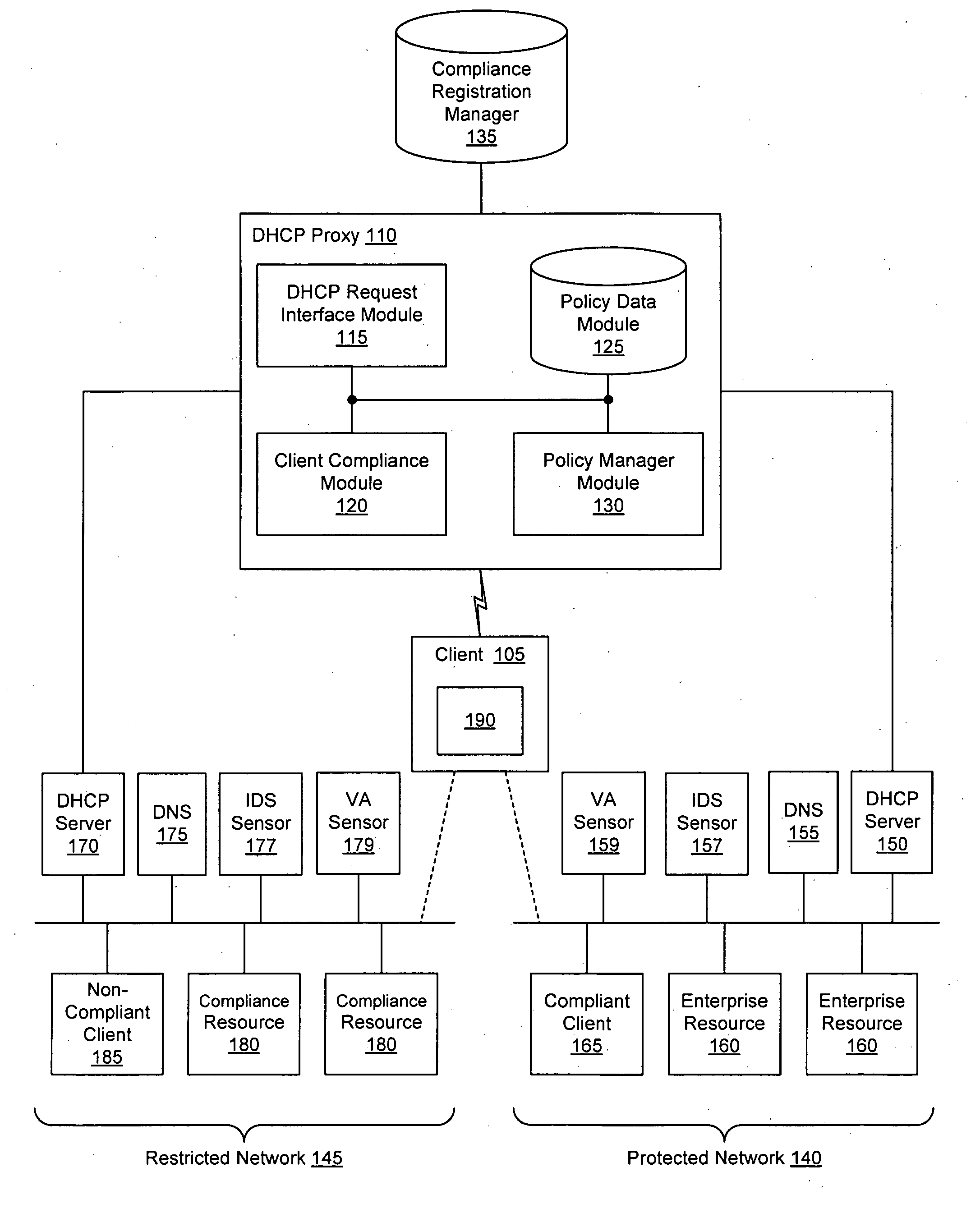
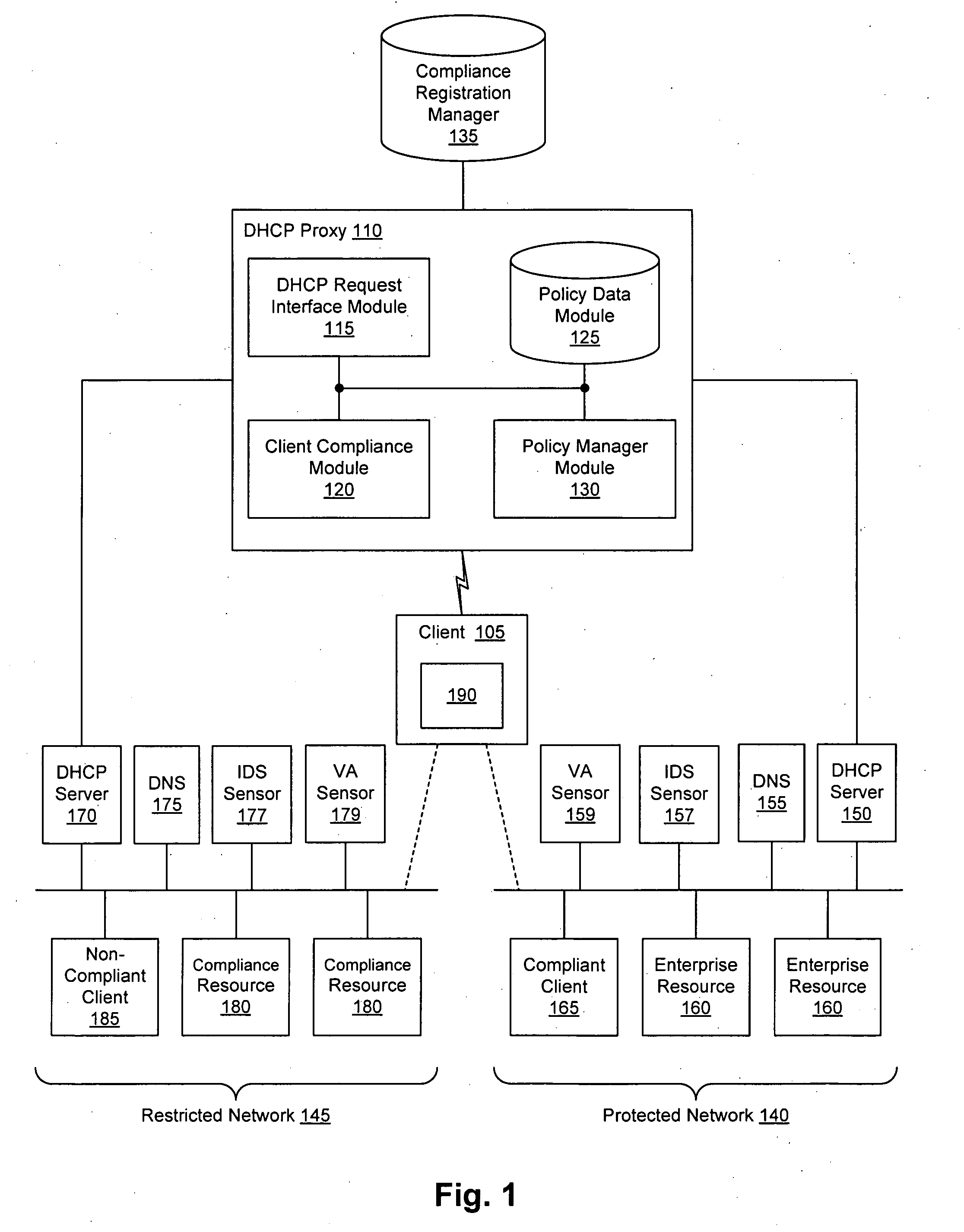
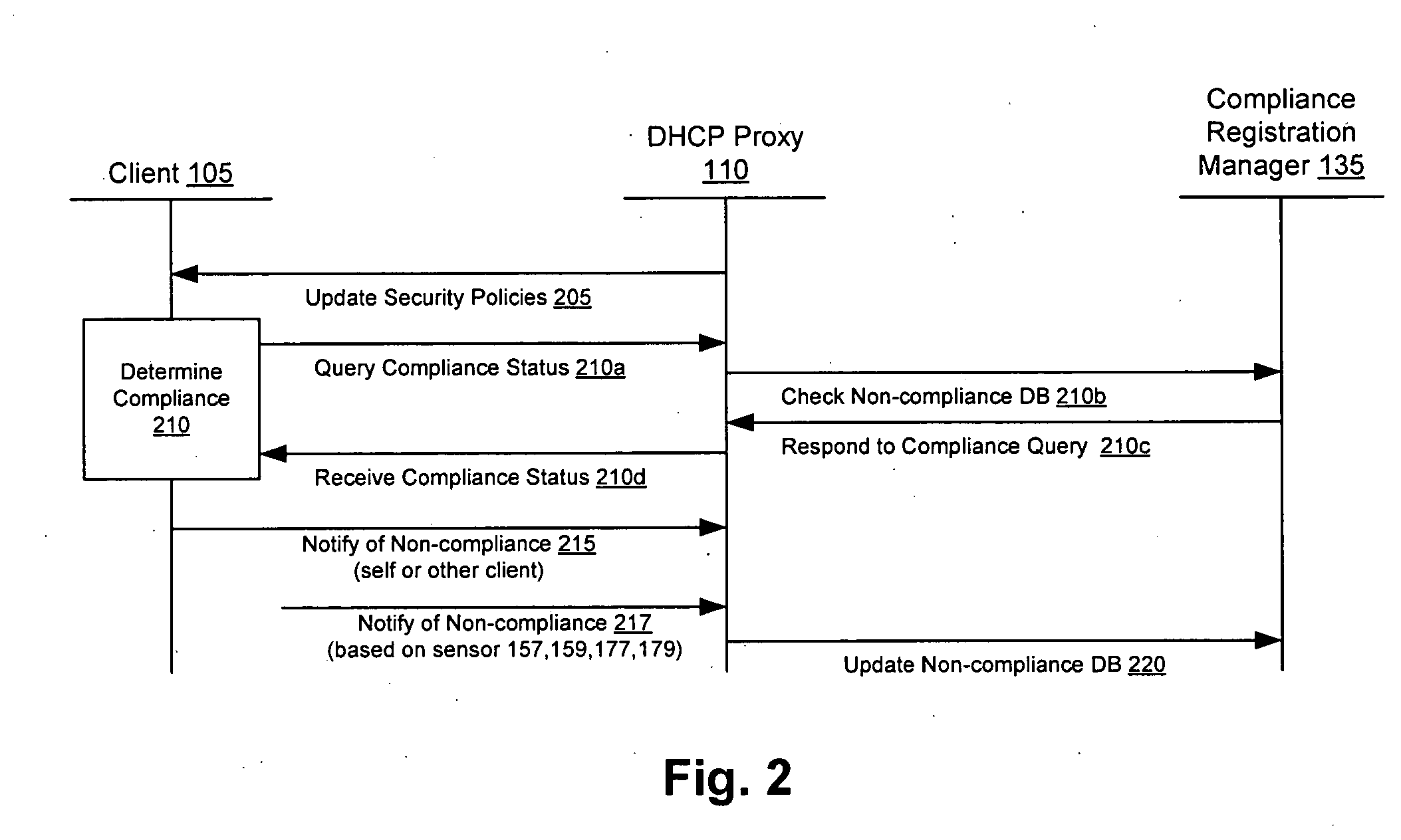
Client compliancy with self-policing clients
InactiveUS20060130139A1Memory loss protectionDigital data processing detailsNon complianceClient compliance
Security sensor data from intrusion detection system (IDS) sensors, vulnerability assessment (VA) sensors, and / or other security sensors is used to enhance the compliancy determination in a client compliancy system. A database is used to store the security sensor data. In one particular embodiment, a list of device compliance statuses indexed by corresponding identifiers (e.g., IP / MAC addresses) combined from IDS, VA, and / or other security sensing technologies is made available as a non-compliance database for query, so that clients and other compliancy authentication elements can tell that a particular client appears to be out of compliance. A client-side self-policing compliance system is enabled, and can be used in conjunction with automated endpoint compliance policy configuration to reduce system administrator burden.
Owner:CA TECH INC
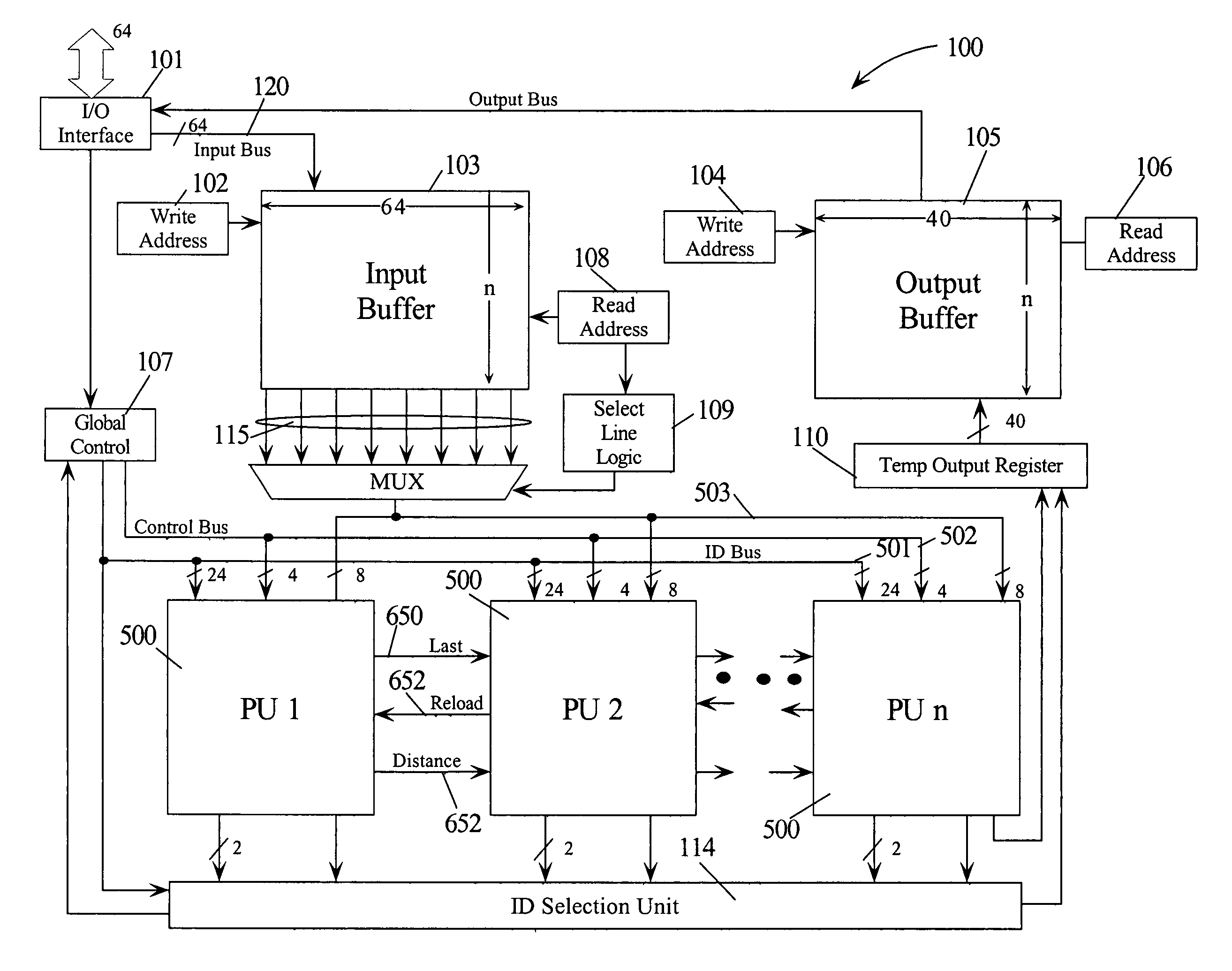
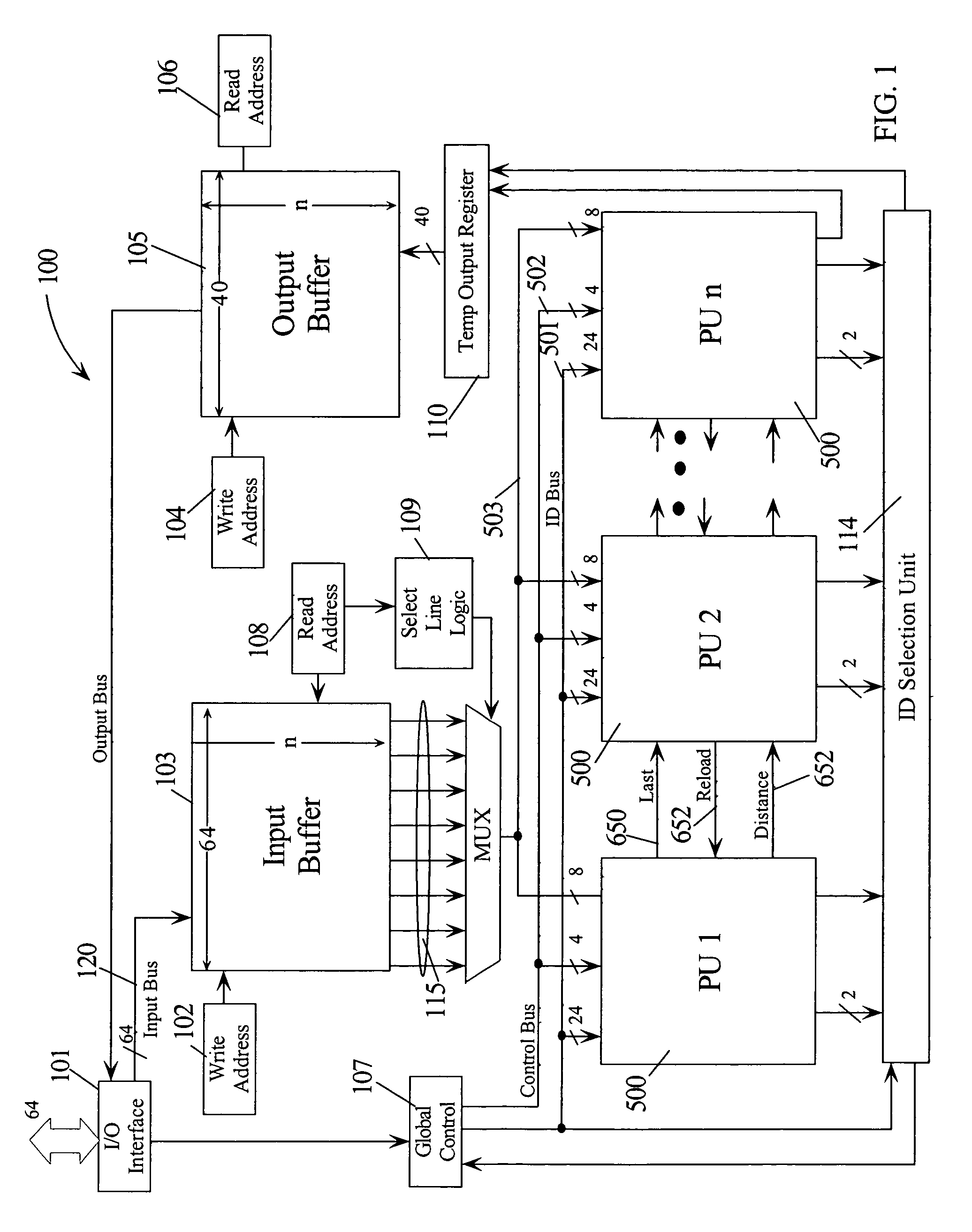
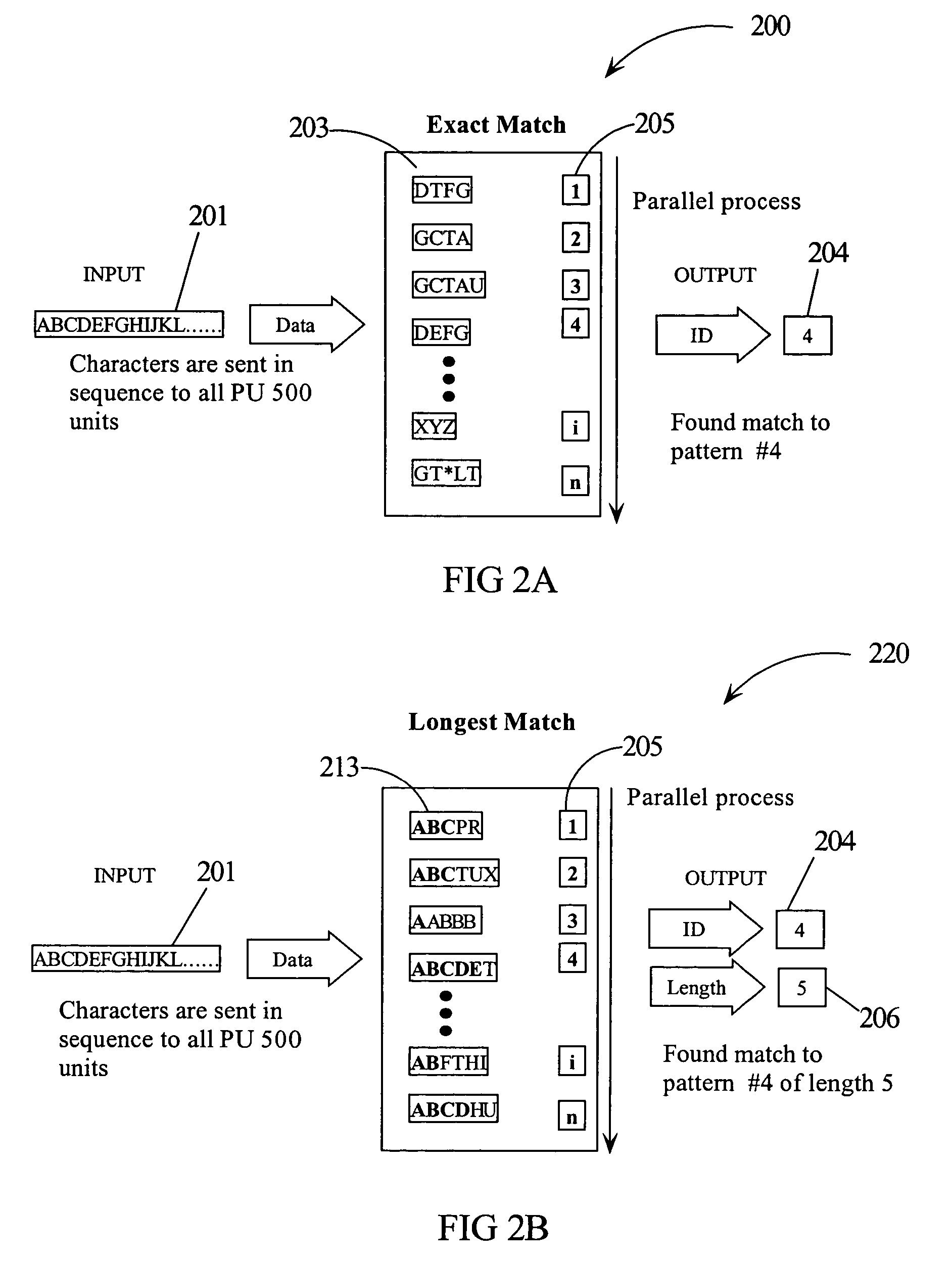
Intrusion detection using a network processor and a parallel pattern detection engine
InactiveUS7487542B2Improve scalabilityMemory loss protectionDigital data processing detailsData streamPattern matching
An intrusion detection system (IDS) comprises a network processor (NP) coupled to a memory unit for storing programs and data. The NP is also coupled to one or more parallel pattern detection engines (PPDE) which provide high speed parallel detection of patterns in an input data stream. Each PPDE comprises many processing units (PUs) each designed to store intrusion signatures as a sequence of data with selected operation codes. The PUs have configuration registers for selecting modes of pattern recognition. Each PU compares a byte at each clock cycle. If a sequence of bytes from the input pattern match a stored pattern, the identification of the PU detecting the pattern is outputted with any applicable comparison data. By storing intrusion signatures in many parallel PUs, the IDS can process network data at the NP processing speed. PUs may be cascaded to increase intrusion coverage or to detect long intrusion signatures.
Owner:TREND MICRO INC
User interface for network security console
ActiveUS7607169B1Memory loss protectionUnauthorized memory use protectionDisplay deviceChronological time
A user interface for a network security console associated with multiple network security devices is disclosed. A graphical user interface (GUI) for use with an intrusion detection system, comprises a radar display that is configured to simulate a stream of time-based events chronologically. In addition, one or more playback controls are configured to control the stream during simulation. In further embodiments, the radar display includes a slider configured to allow a user to jump to events that occurred at a user-defined time.
Owner:MICRO FOCUS LLC
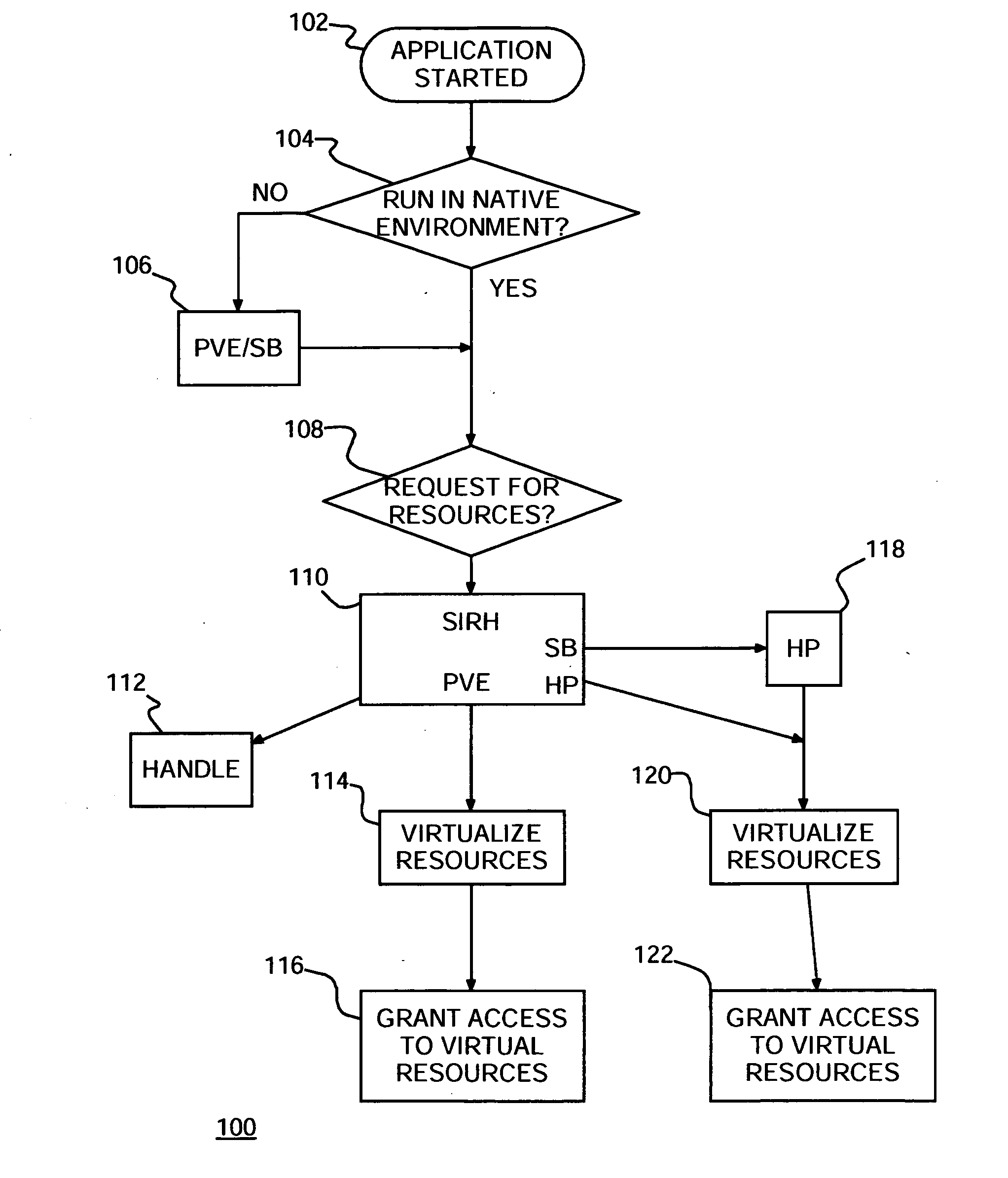
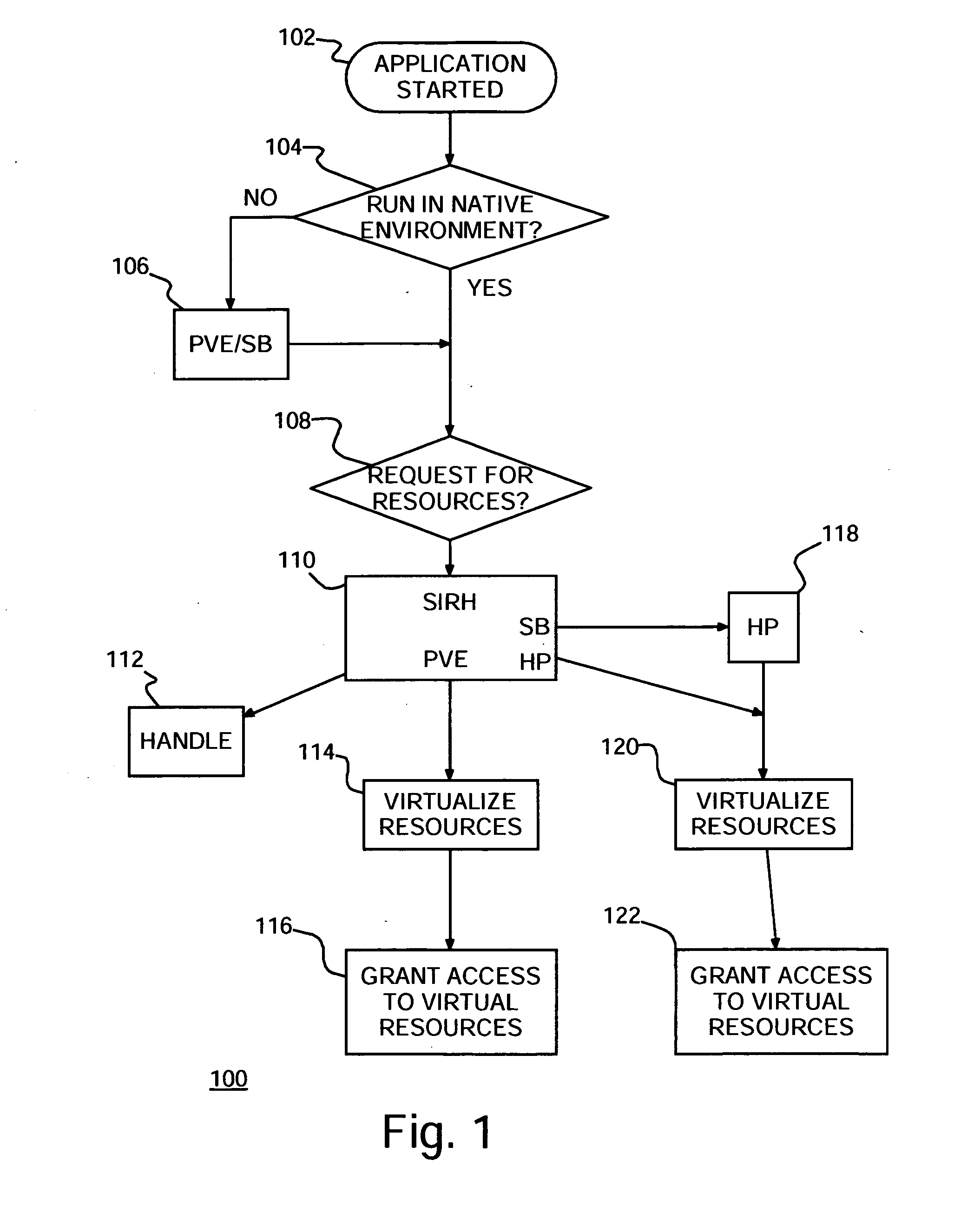
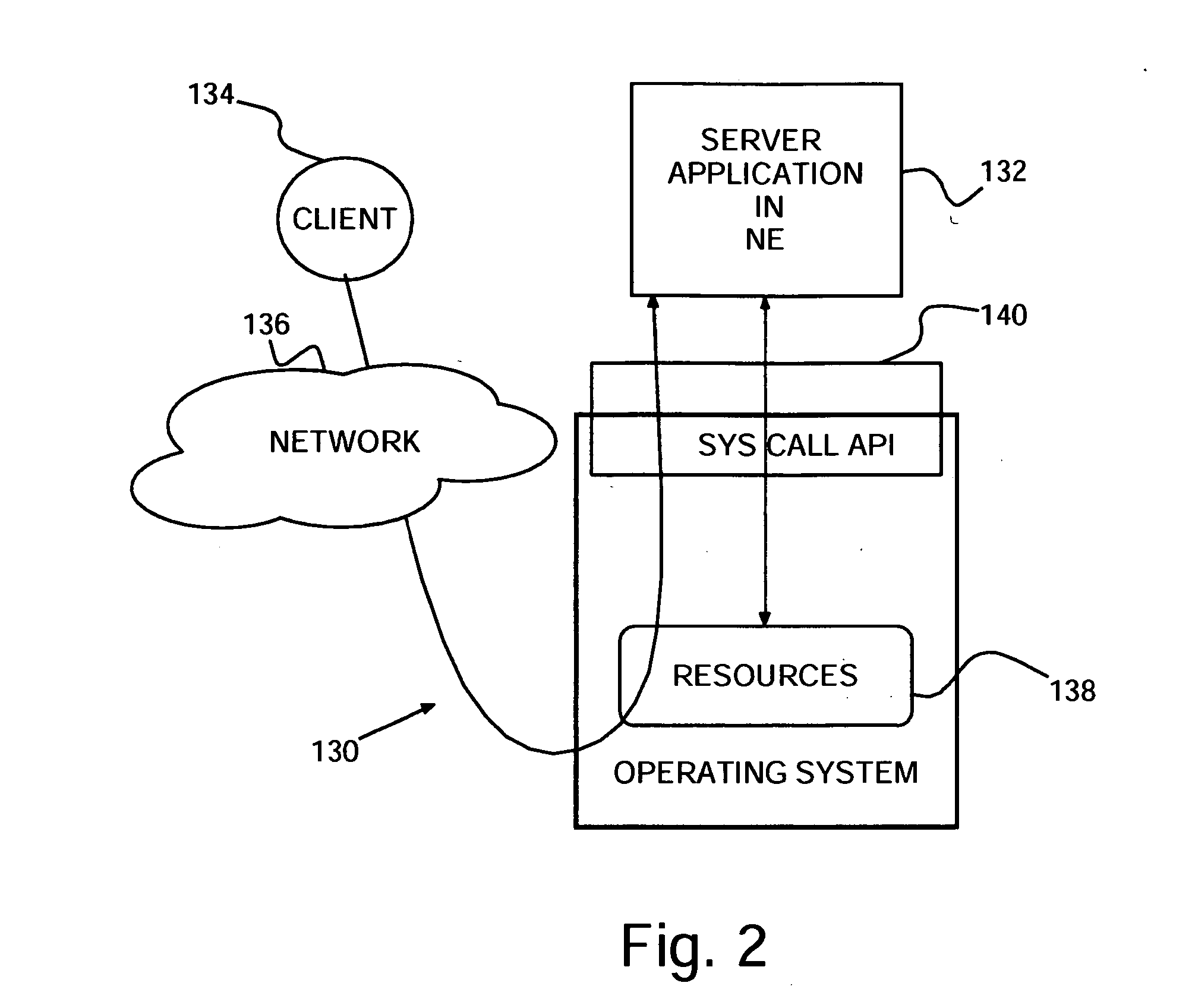
Intrusion detection system
InactiveUS20060161982A1Minimize wasted resourceMemory loss protectionError detection/correctionVirtualizationPersonalization
An intrusion detection system (IDS), method of protecting computers against intrusions and program product therefor. The IDS determines which applications are to run in native environment (NE) and places the remaining applications in a sandbox. Some of the applications in sandboxes may be placed in a personalized virtual environment (PVE) in the sandbox. Upon detecting an attempted attack, a dynamic honeypot may be started for an application in a sandbox and not in a PVE. A virtualized copy of system resources may be created for each application in a sandbox and provided to the corresponding application in the respective sandbox.
Owner:IBM CORP
Methods and apparatus for computer network security using intrusion detection and prevention
InactiveUS7225468B2Memory loss protectionDigital data processing detailsIp addressIntrusion detection and prevention
A method provides security to a computer network by selectively blocking network transmissions from selected IP addresses. The method includes the steps of: establishing a risk threshold whereby transmissions from IP addresses exceeding said risk threshold are selectively blocked; receiving a network transmission having an originating IP address and payload; analyzing the payload of said transmission and assigning a current risk rating to said IP address on the basis of said analysis; comparing the originating IP address of said transmission to a database of known IP addresses, each of said known IP addresses having a previous cumulative assigned risk rating, said previous cumulative assigned risk rating being based on at least one previous transmission from a known IP address; assigning a new cumulative risk rating to said originating IP address; logging the new cumulative risk rating for said originating IP address in said database of known IP addresses. The new cumulative risk rating is compared to said risk threshold and the transmission is blocked if said new cumulative risk rating exceeds said risk threshold.
Owner:DIGITAL SECURITY NETWORK
System and method for detecting computer intrusions
InactiveUS6996843B1Overcome problemsEnabling detectionMemory loss protectionDigital computer detailsTimestampAccess time
A system and method are disclosed for detecting intrusions in a host system on a network. The intrusion detection system comprises an analysis engine configured to use continuations and apply forward- and backward-chaining using rules. Also provided are sensors, which communicate with the analysis engine using a meta-protocol in which the data packet comprises a 4-tuple. A configuration discovery mechanism locates host system files and communicates the locations to the analysis engine. A file processing mechanism matches contents of a deleted file to a directory or filename, and a directory processing mechanism extracts deallocated directory entries from a directory, creating a partial ordering of the entries. A signature checking mechanism computes the signature of a file and compares it to previously computed signatures. A buffer overflow attack detector compares access times of commands and their associated files. The intrusion detection system further includes a mechanism for checking timestamps to identify and analyze forward and backward time steps in a log file.
Owner:SYMANTEC CORP