Method for distributing and encrypting streaming media
A streaming media and key technology, applied in the field of computer information, can solve problems such as server crashes, download speed drops, and inability to continue, and achieve the effect of solving copyright protection problems and improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] A method for streaming media distribution and encryption of the present invention is explained in detail below.
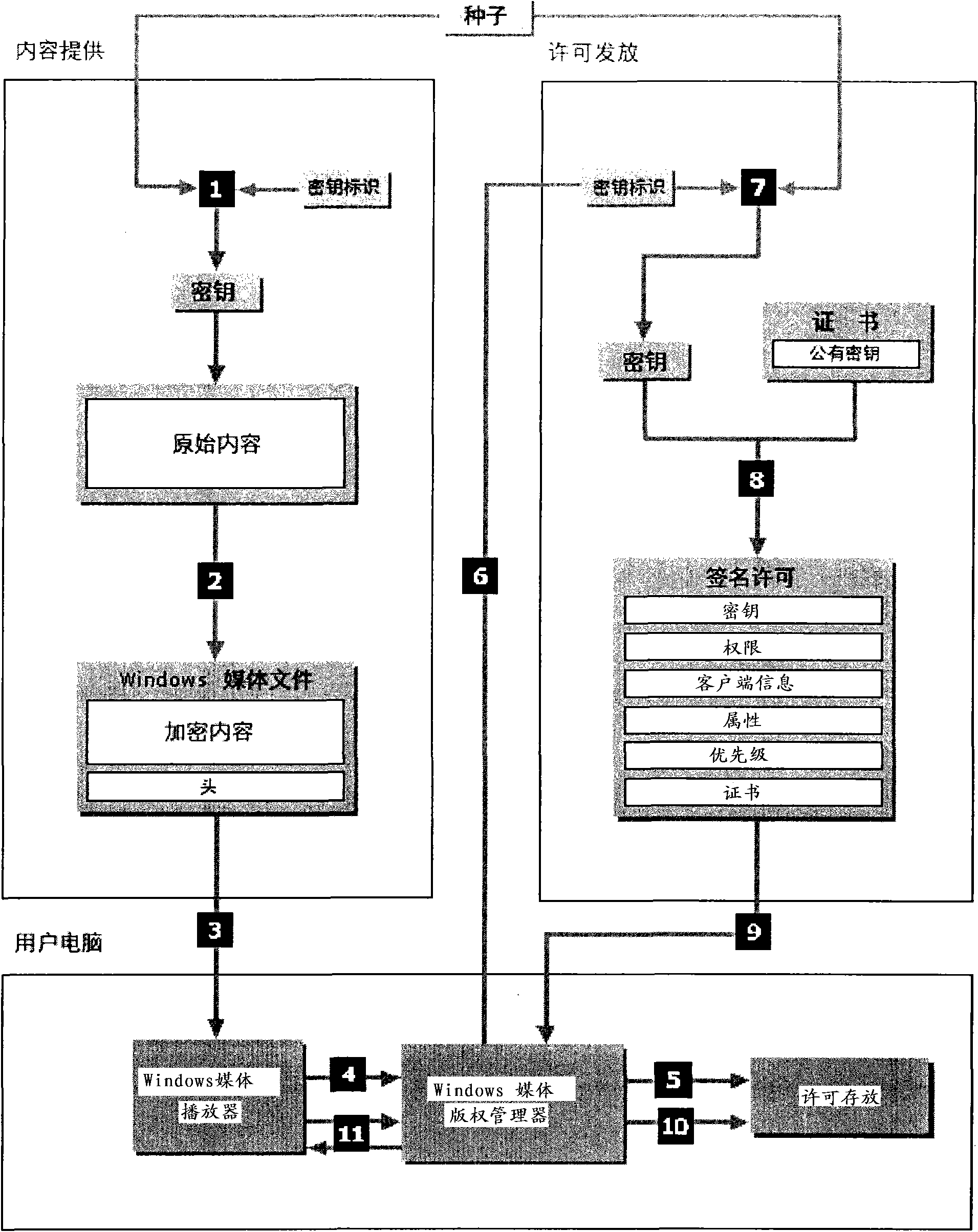
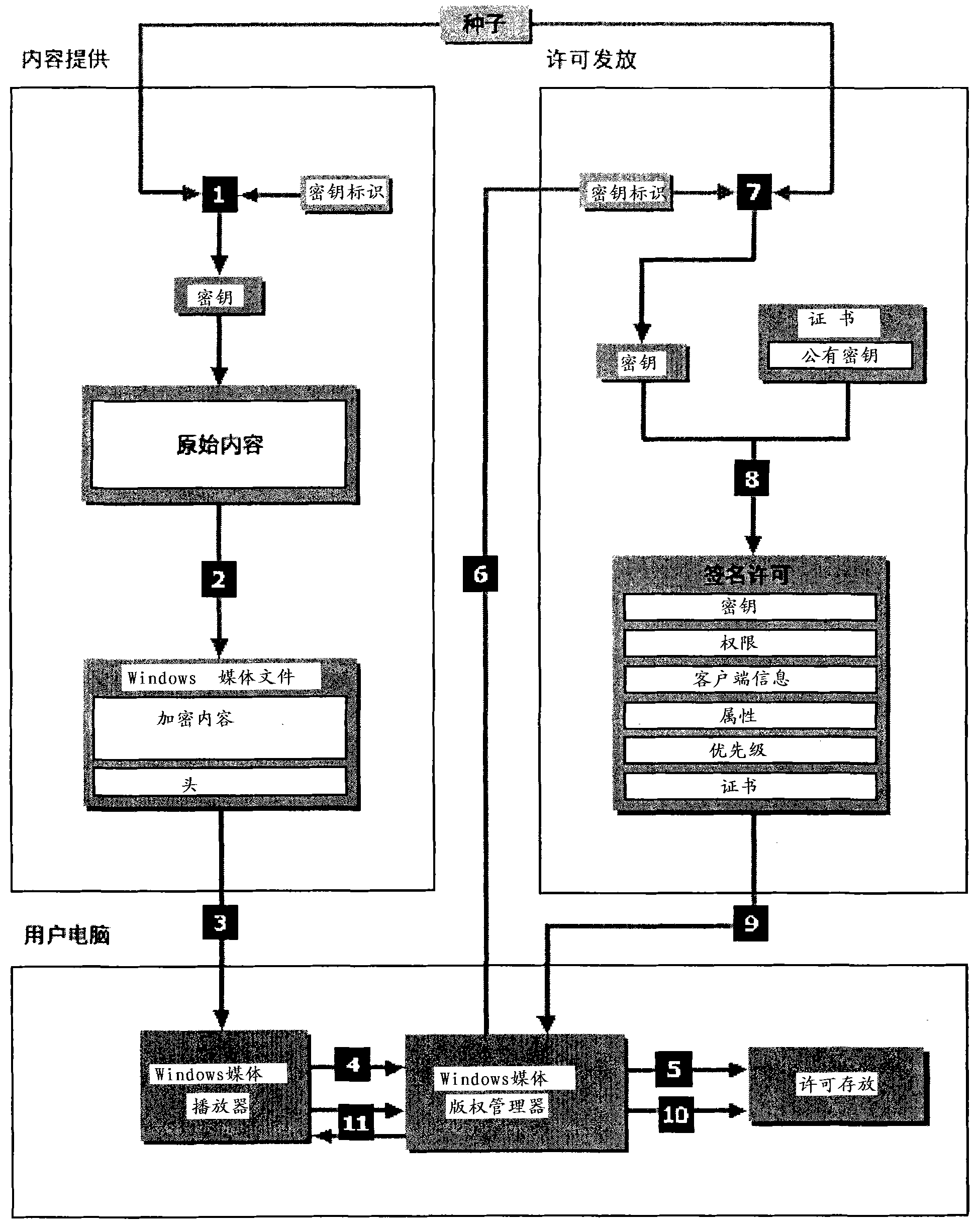
[0024] There are generally two keys used for encryption protection using key technology, one is a public key and the other is a private key; the public key is used for encryption of program content, and the private key is used for encryption. The private key is used to decrypt the program content. In addition, the private key can also be used to judge when the header information of the digital program is tampered with or destroyed, thereby preventing the digital program from being illegally used.
[0025] Another more secure encryption method is to use three keys, that is, divide the private key into two: one is stored on the user's PC, and the other is stored at the verification station (access ticket). Use these two private keys to unlock the digital program, the principle is as attached figure 1 shown.
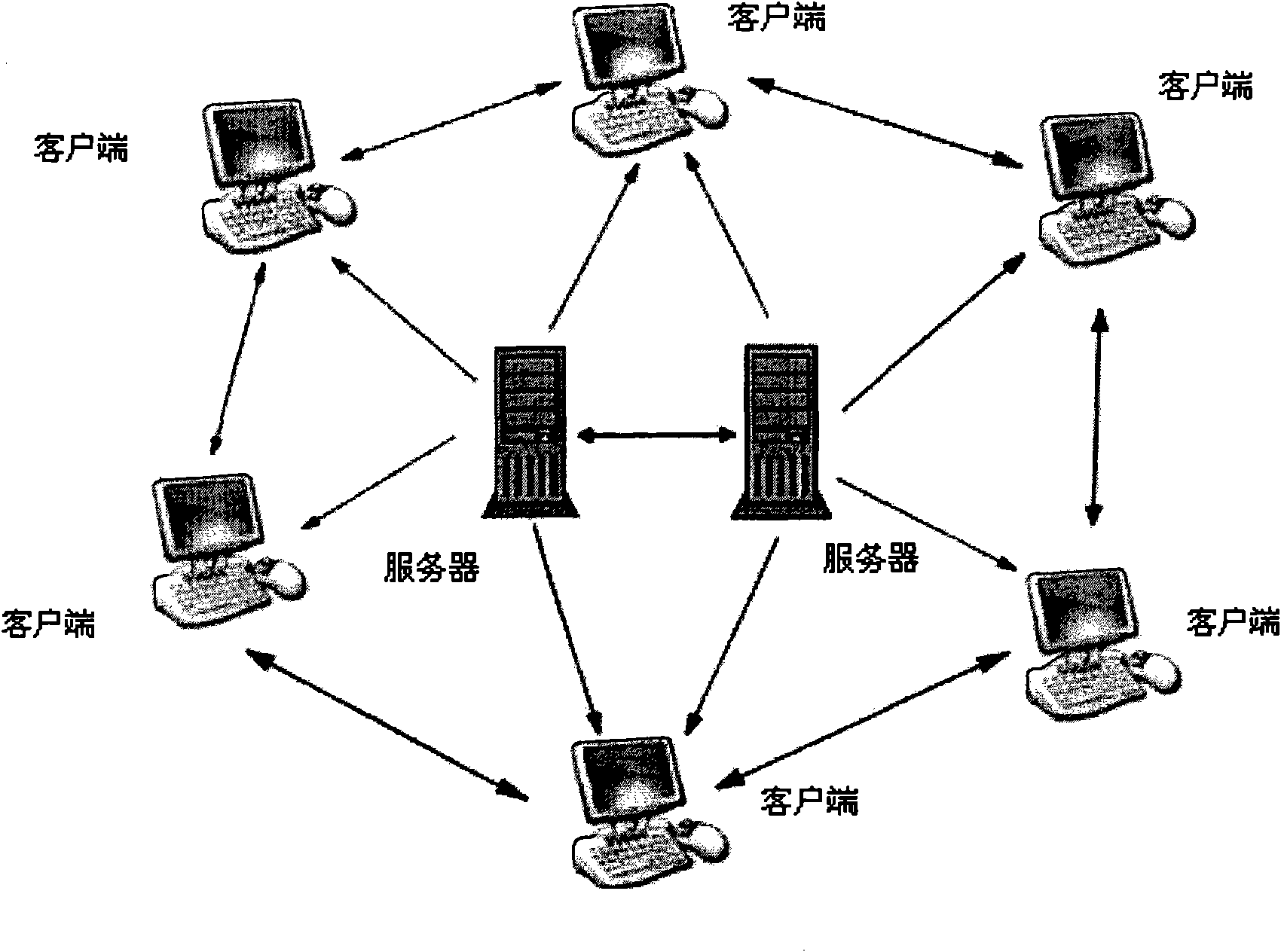
[0026] P2SP is a combination of BT and HTTP (or F...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More