Pass-pattern authentication for computer-based security
A technology of direction mode and verification mechanism, applied in the direction of digital data authentication, etc., can solve problems such as violating the original intention of passwords, difficulty in remembering passwords for users, and increased vulnerability to attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
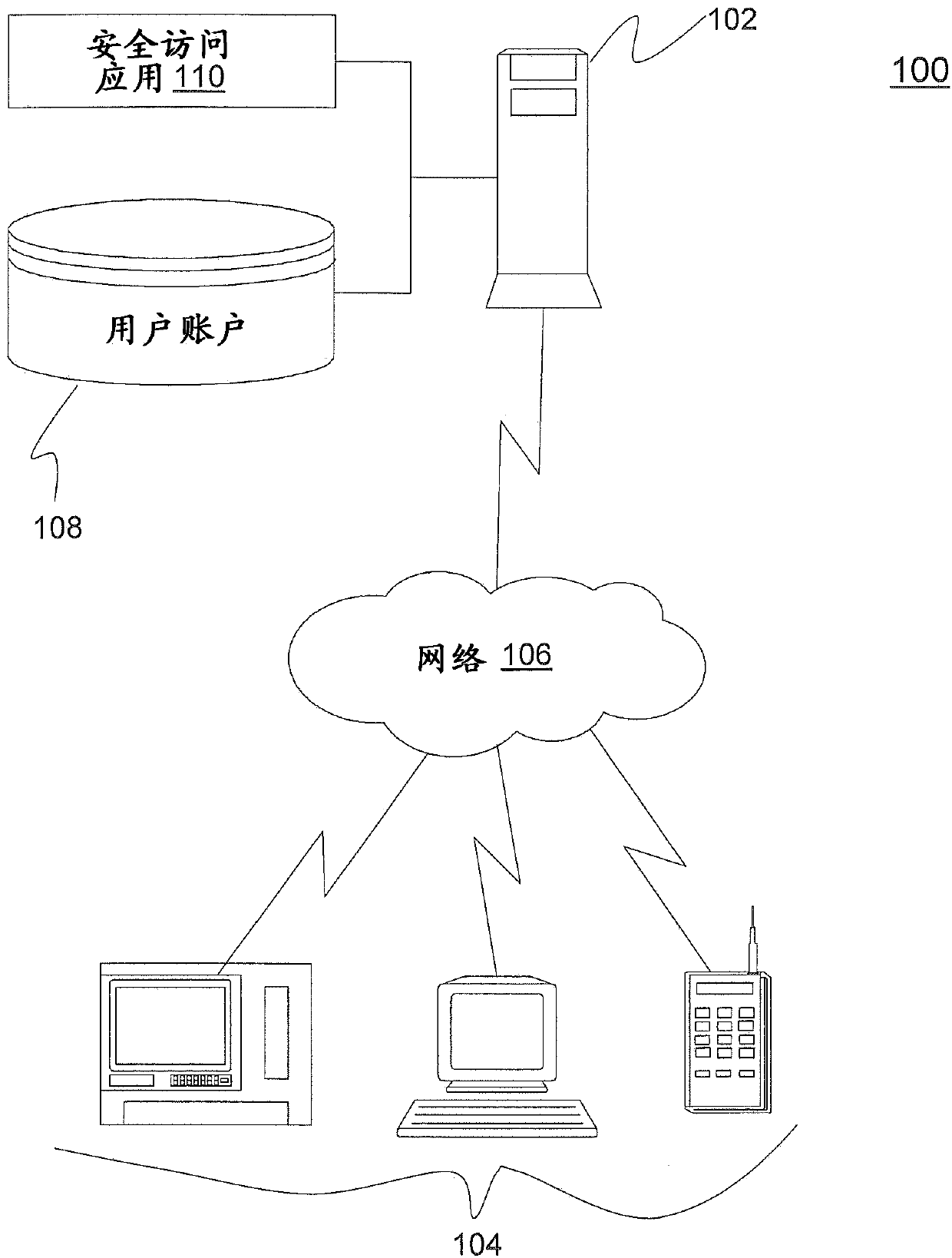
[0015] According to one exemplary embodiment, there is provided a pass-mode verification for a computer-based secure access (also referred to herein as "secure access") process. The secure access process provides a secure authentication technique using a unique sequence of directional patterns selected by the user or assigned to the user's input. A direction pattern sequence contains a series of directional instructions that are followed based on the starting position on the input device and are completely independent of the underlying specified input device characters (i.e., validation is not dependent on or limited to devices such as the keyboard, keypad any specific character letter, symbol or value on an input device such as a , touch screen, etc.). Authentication of the user is based entirely on a sequence of directional patterns entered by the user starting from a random starting point on the input device.
[0016] The starting point on the interface of the input device...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More