Mobile terminal antitheft method and client
A technology of mobile terminals and anti-theft methods, applied in the field of Internet applications, can solve the problems of inability to effectively curb theft crimes, loss, and inability to protect mobile terminals, and achieve the effect of reducing the probability of theft crimes
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
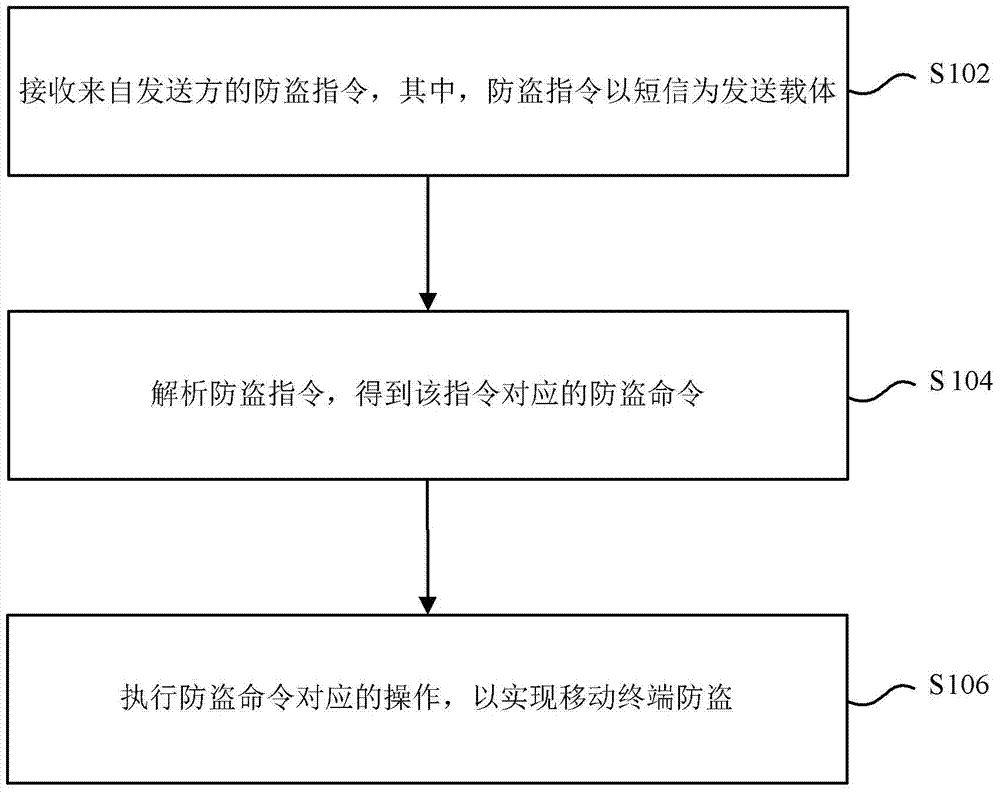
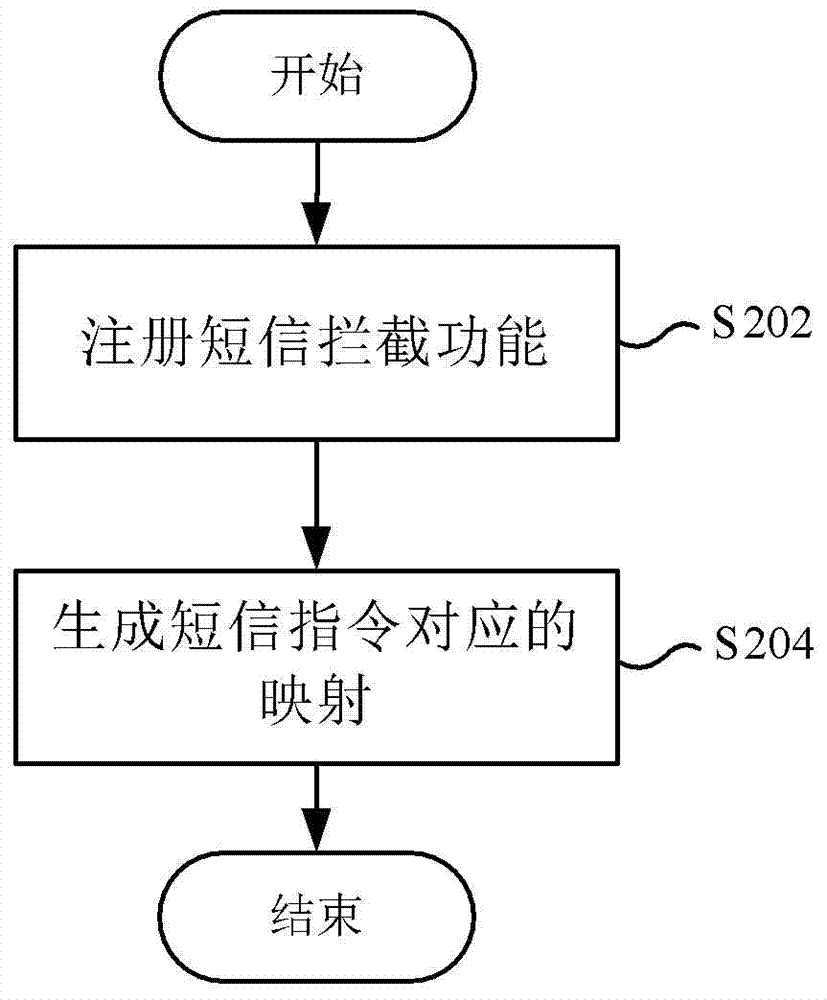
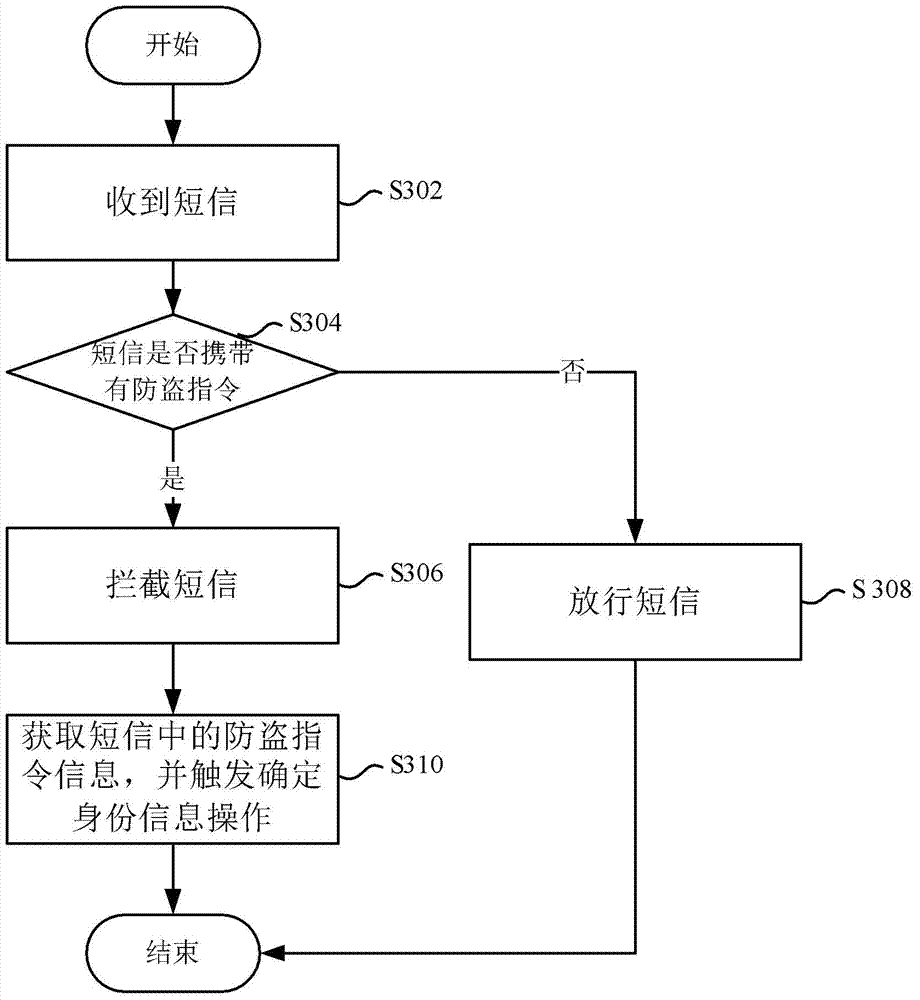
[0073] Figure 7 to Figure 9 It shows a processing flow chart of the mobile terminal anti-theft method according to a preferred embodiment of the present invention, which is used to support any of the above-mentioned mobile terminal anti-theft methods, and makes the above-mentioned mobile terminal anti-theft method clearer and easier to understand. It should be noted that, in order to explain this preferred embodiment more clearly and simply, in this preferred embodiment, the sender is set on the mobile phone of relatives and friends, and the mobile terminal is set on the stolen mobile phone.
[0074] Figure 7 A processing flow chart of a method for preventing theft of a mobile terminal according to a preferred embodiment of the present invention is shown. Such as Figure 7 As shown, after the mobile phone is stolen, the preferred embodiment executes step S702 to send anti-theft text messages to the stolen mobile phone through the mobile phones of relatives and friends. Wh...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More