Locking and unlocking application method, device and system
A designated application and unlocking technology, applied in the field of communication, can solve problems such as user property loss and application software information loss, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
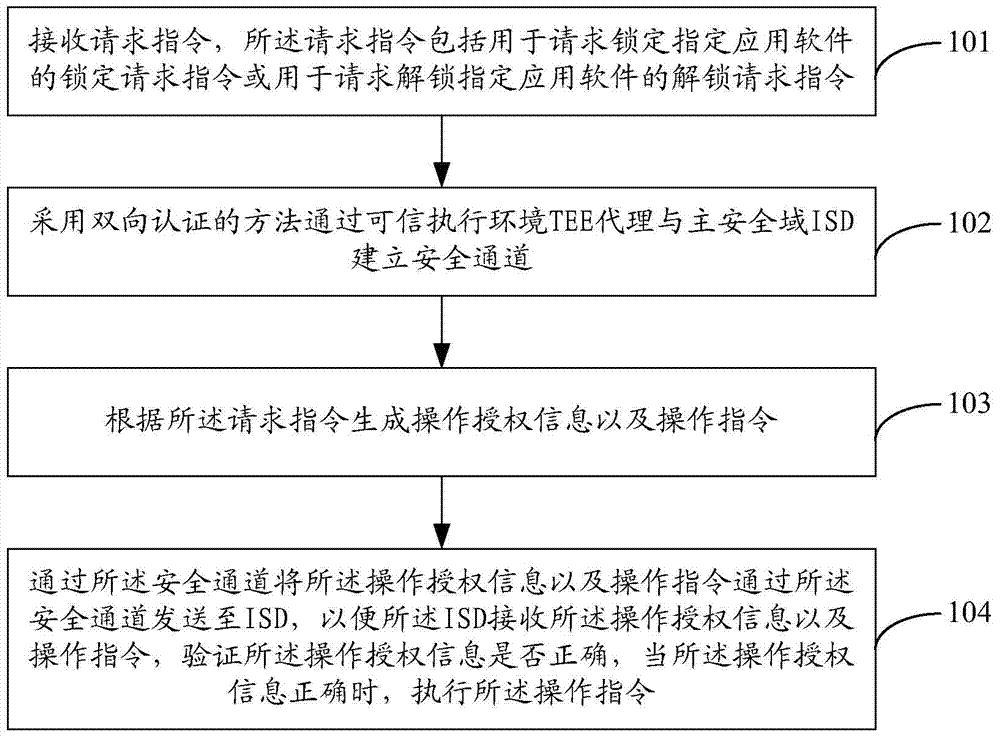
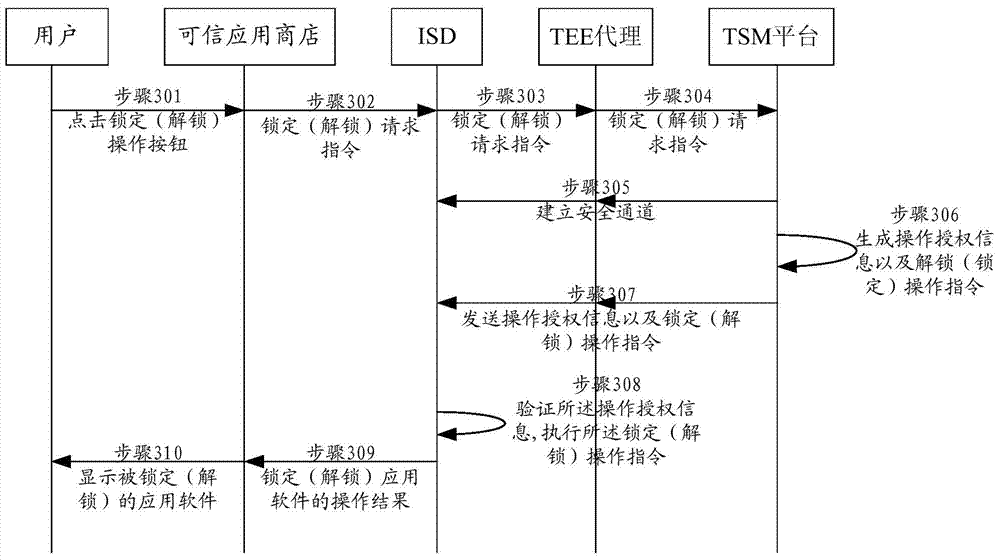
[0072] figure 1 It is a flow chart of Embodiment 1 of a method for locking and unlocking an application of the present invention, which is applied to a trusted service management TSM platform. Embodiment 1 mainly describes the authorization of locking and unlocking, and the method includes:
[0073] Step 101: Receive a request instruction, where the request instruction includes a lock request instruction for requesting to lock a designated application software or an unlock request instruction for requesting to unlock a designated application software.
[0074] The request command received by the TSM platform may be a lock request command for locking one or all application software, or an unlock request command for unlocking one or all application software. For example, when lending the mobile terminal to others, you can only choose to lock several application software with private information, and when the mobile terminal is brought back, unlock the locked application software...
Embodiment approach
[0077] First possible implementation:
[0078] receiving the request instruction sent by the ISD through the TEE proxy, the request instruction is generated by the trusted application store according to the user's operation and sent to the ISD.
[0079] The user can open the trusted application store, and the trusted application store has icons of all application software installed on the mobile terminal, and the user clicks the operation button of locking or unlocking provided on the icon of the application software. After receiving the user's click operation, the trusted application store sends a lock request instruction or an unlock request instruction to the main security domain (Issue Security Domain, ISD). The ISD sends the lock request instruction or the unlock request instruction to the TSM through a Trusted Execution Environment (Trusted Execution Environment, TEE) agent. What needs to be explained here is that all communication information between the ISD and the TS...
Embodiment 2
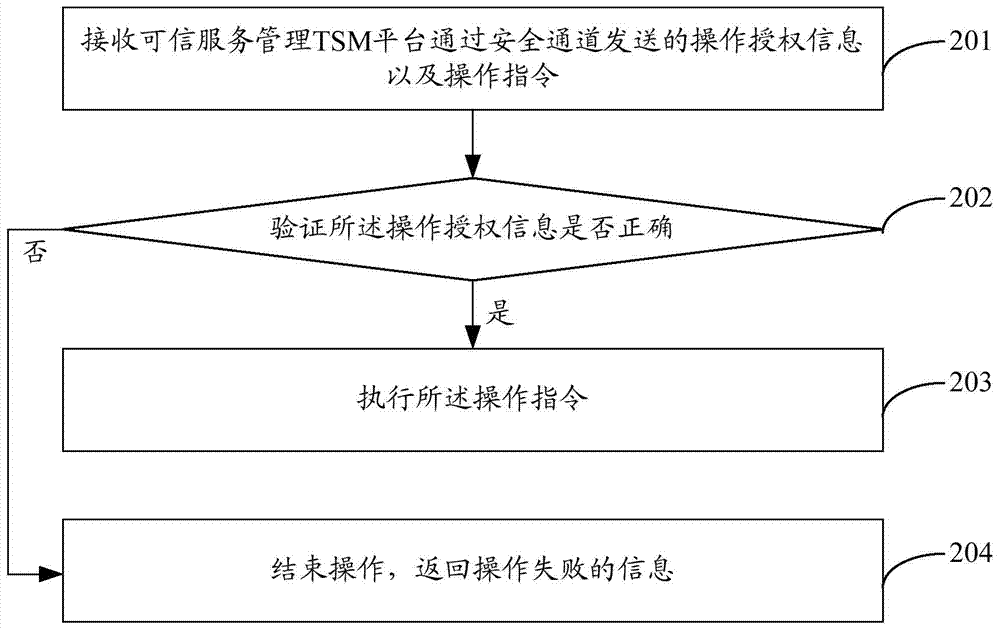
[0115] figure 2 It is a flow chart of Embodiment 2 of a method for locking and unlocking an application of the present invention, which is applied to the main security domain ISD. Embodiment 2 mainly describes the authorization verification of locking and unlocking. The method includes:
[0116] Step 201: Receive the operation authorization information and operation instructions sent by the trusted service management TSM platform through a secure channel.
[0117] The operation authorization information and the operation instruction are generated according to the request instruction received by the TSM platform, the operation instruction corresponds to the request instruction, and when the request instruction is a lock request instruction, the operation instruction is a lock operation instruction, and when the request instruction is an unlock request instruction, the operation instruction is an unlock operation instruction.
[0118] The TSM platform sends the operation autho...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More