A method and system for protecting end user data
A technology for user data and end users, applied in transmission systems, electrical components, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0063] In order to make the purpose, technical solution and advantages of the present invention more clear, the embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
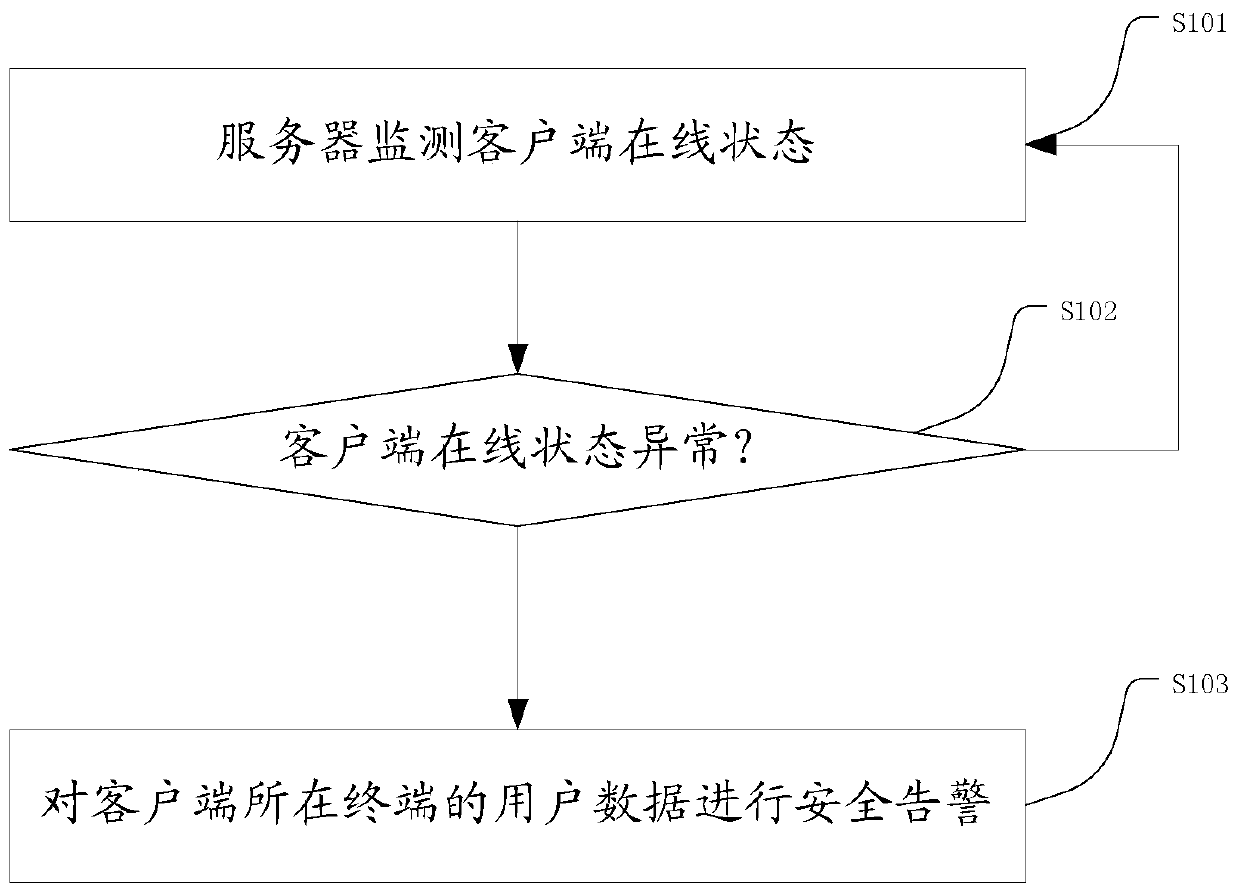
[0064] When there is a network connection between the server and the client, the figure 1 The shown method protects end-user data by the server, as shown in the diagram:
[0065] S101 The server monitors the online status of the client;
[0066] S102 The server judges whether the online status of the client is abnormal, if yes, execute step S103; if not, execute step S101;
[0067] The online status of the client is abnormal, including: the client is not online within the set time, or the client is deleted;
[0068] Preferably, the server monitors that the client is not on...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More