File protection method and system
A technology for protecting systems and files, applied in the field of communication, can solve problems such as inability to guarantee security, and achieve the effects of preventing easy infringement and copying, ensuring security, and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
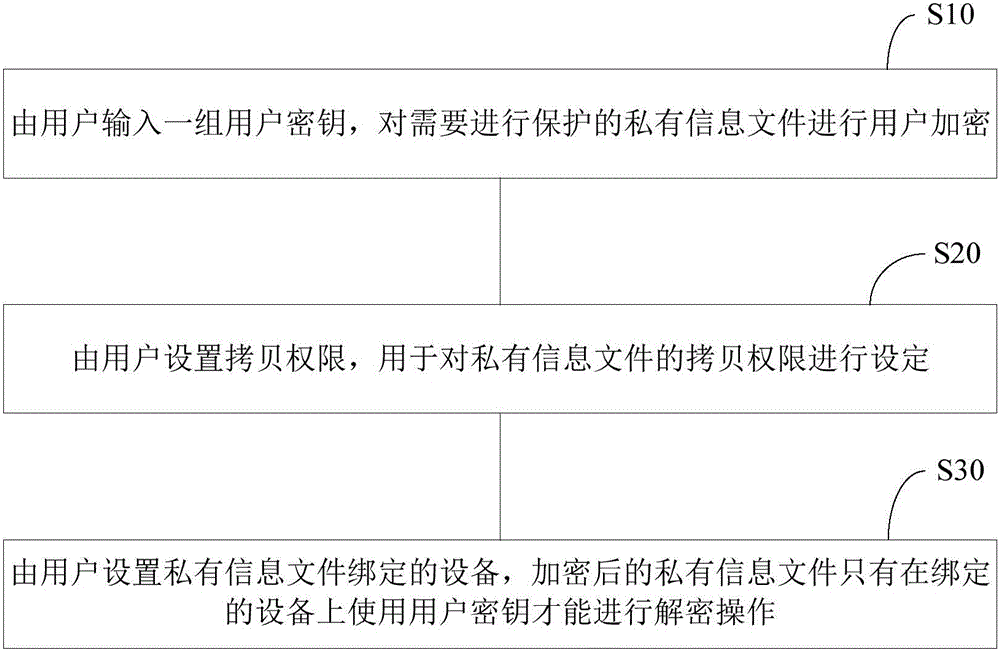
[0024] figure 1 is a flowchart of a file protection method in an embodiment, such as figure 1 As shown, the method includes the following steps:
[0025] S10: The user inputs a group of user keys, and performs user encryption on the private information files that need to be protected.
[0026] In the initial stage, in order to protect the private information files, the user first inputs a set of user keys, and the user password is used to encrypt the private information files, so that the private information files become encrypted files, thereby greatly protecting the private information files. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More