(k,n) threshold based user-friendly visual secret sharing method
A secret sharing and threshold technology, applied in the field of information security, can solve problems such as low security, inconvenient management, and damage to image integrity, and achieve the effects of improving contrast, improving visual effects, and increasing the scope of image application.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] The specific embodiments of the present invention will be described below in conjunction with the accompanying drawings.
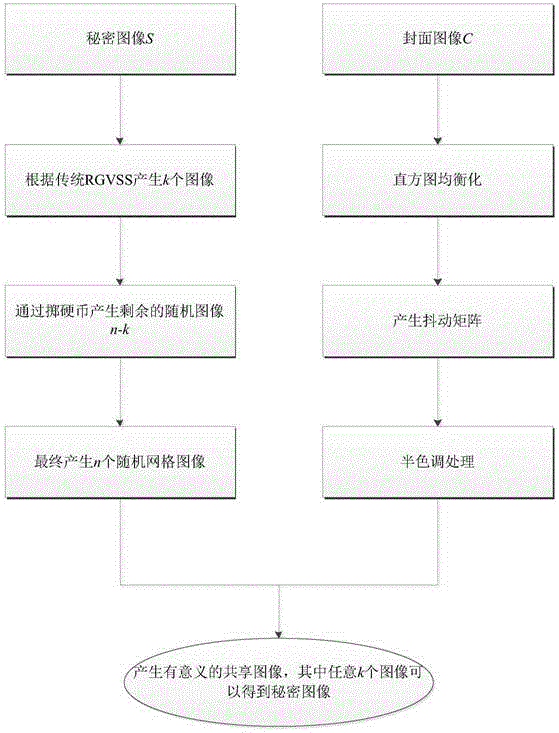
[0037] refer to figure 1 , the implementation steps of the present invention are as follows:
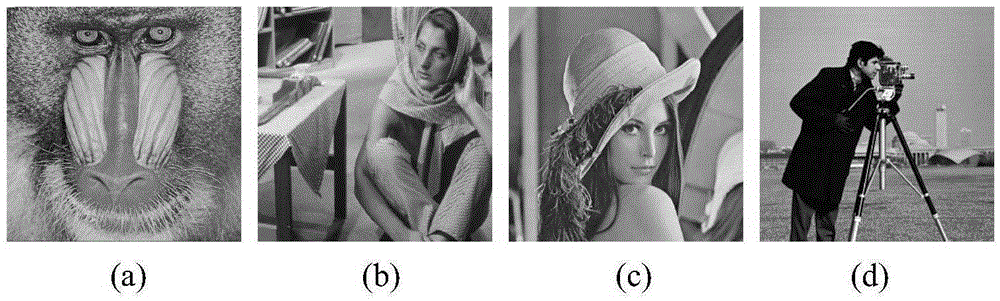
[0038] Step 1, input a secret image S and n cover images C to be protected.
[0039] The secret image S is an image that needs to be protected, and the cover image C is used to hide the secret image S. The size of the cover image and the secret graphic must be equal, here it is set to r×c, r represents the height of the secret image and the cover image, and c represents the secret image and The width of the cover image.
[0040] Step 2, use the traditional random grid-based method to generate a shared image, the secret image S uses a binary image, for the traditional random grid-based visual secret sharing method, firstly, the pixel S of the secret image S i,j For coding, the following first introduces the traditional random grid.
[0041] 2a) Generate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More