Security Location Tracking and Quantitative Evaluation Method for Wireless Sensor Networks
A wireless sensor and network security technology, applied in wireless communication, network topology, electrical components, etc., can solve the problems of non-ranging positioning algorithm wormhole attack, node capture attack, node hardware resource limitation, etc., to reduce the threat level Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
specific Embodiment approach
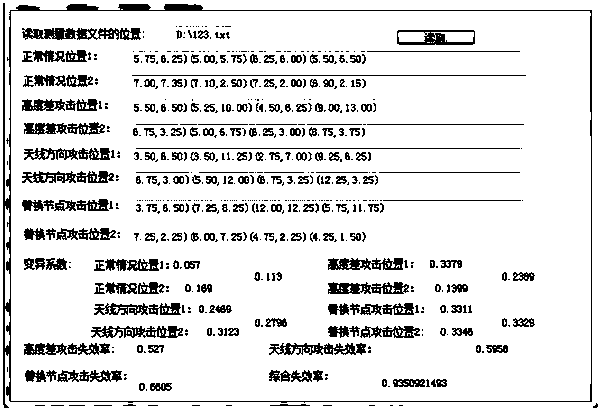
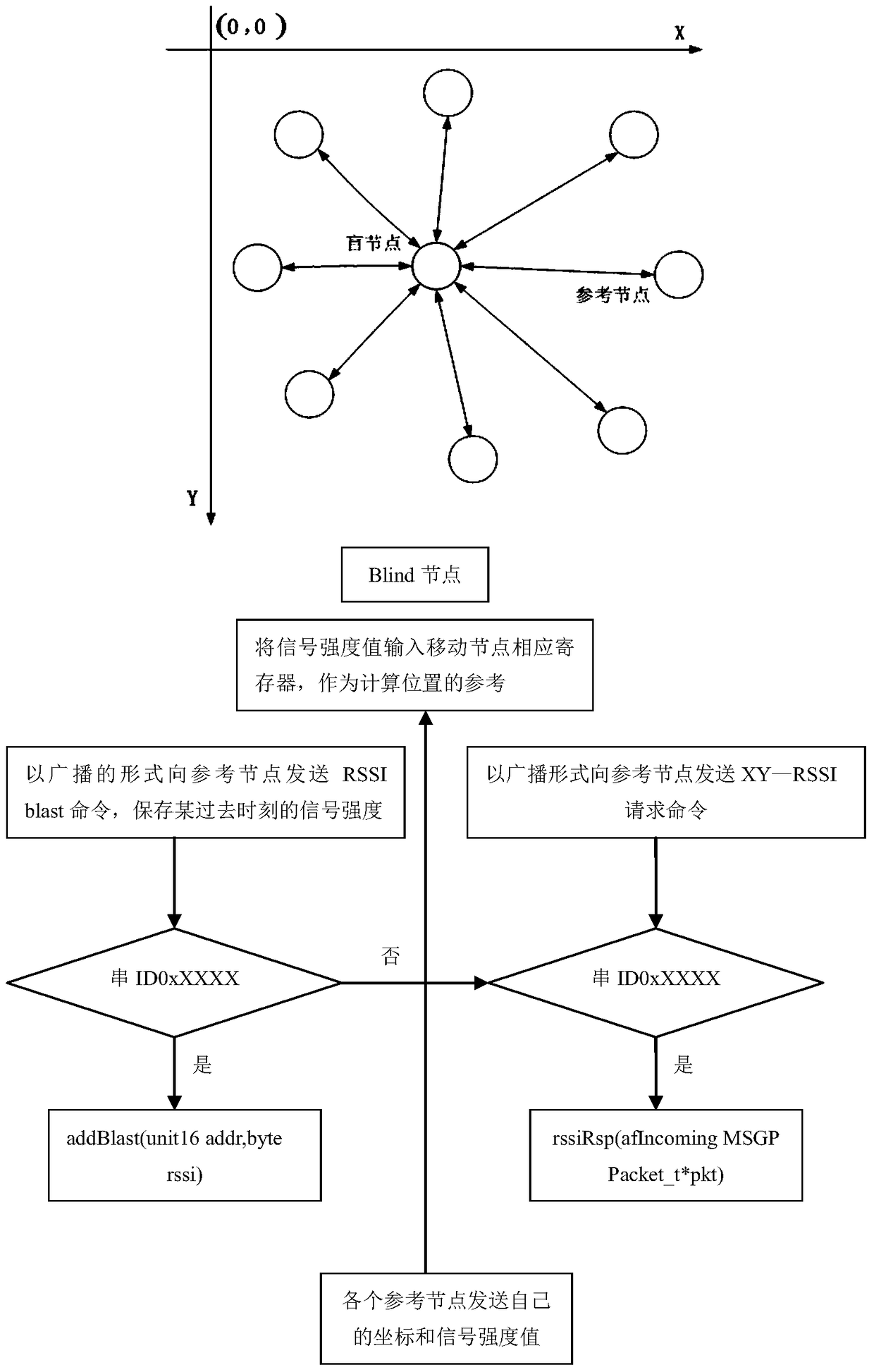
[0035] Step 1: The CC2431 positioning engine is implemented with a function with a simple interface: write the required parameters, wait for the calculation to complete, and then read the calculation result, which is the coordinate of the blind node. The positioning principle is as follows figure 1 .
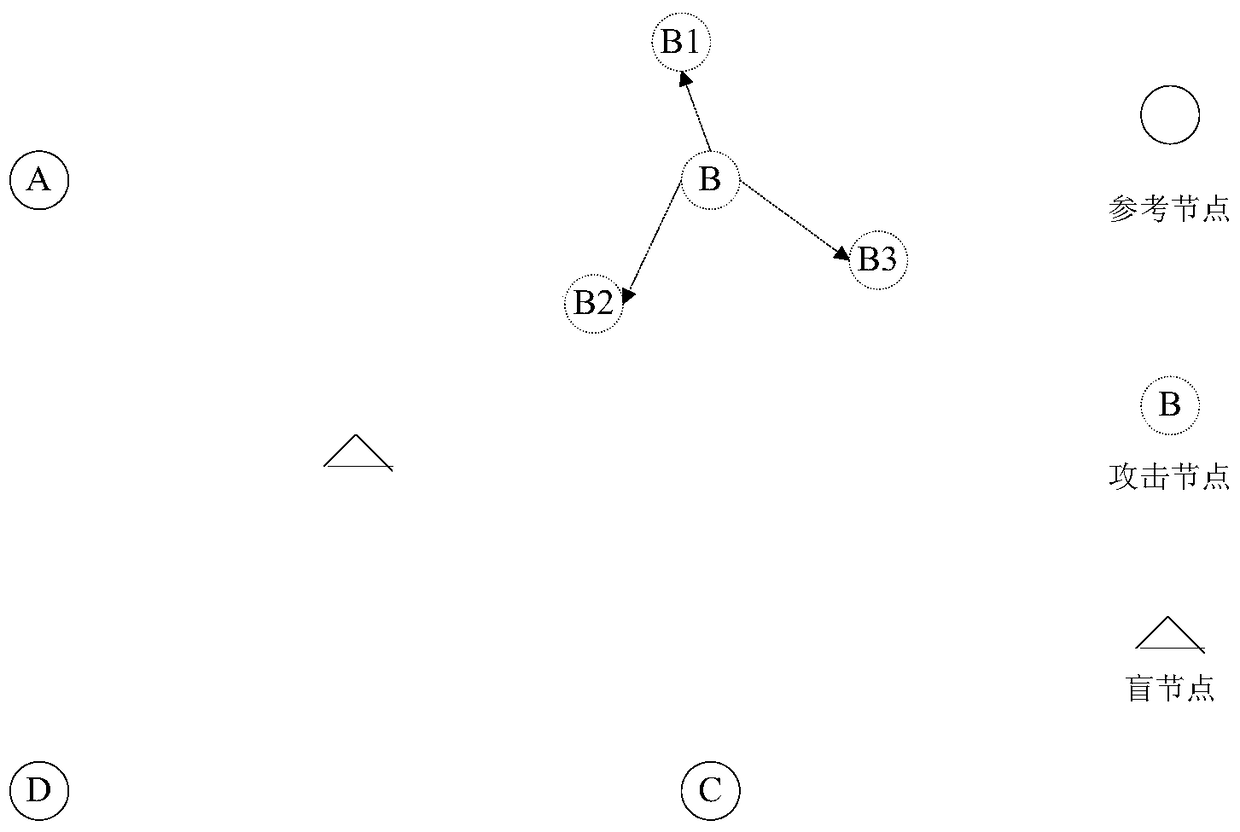
[0036] Step 2: Aiming at the hidden danger of "multiple identity false information" in the wireless sensor network positioning algorithm, establish a sensor network positioning attack technology based on multiple identity false information. The attack model is as follows: figure 2 shown. When the attack node is not added, the positioning coordinates and RSSI value of the reference node are recorded.
[0037] Step 3: Join the attack node, use the attack node to send different position parameters to the blind node at different times, and the XY_RSSI corresponding function in the attack node:
[0038] static void rssiRsp(afIncomingMSGPacket_t*pkt);
[0039] This function compl...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More