Spam interception method and device
A technology of spam information and information database, which is applied in security devices, telephone communication, wireless communication, etc., can solve the problem of inability to intercept, and achieve the effect of reducing burden, large capacity and improving processing efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
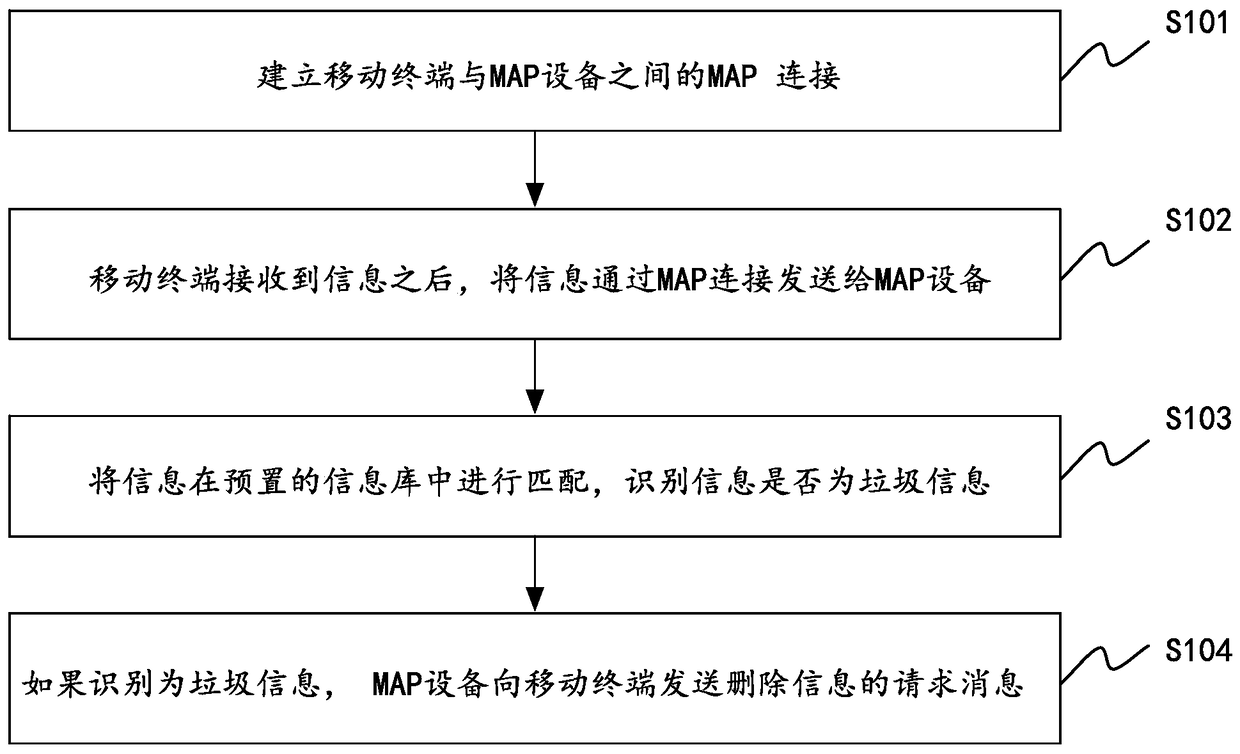
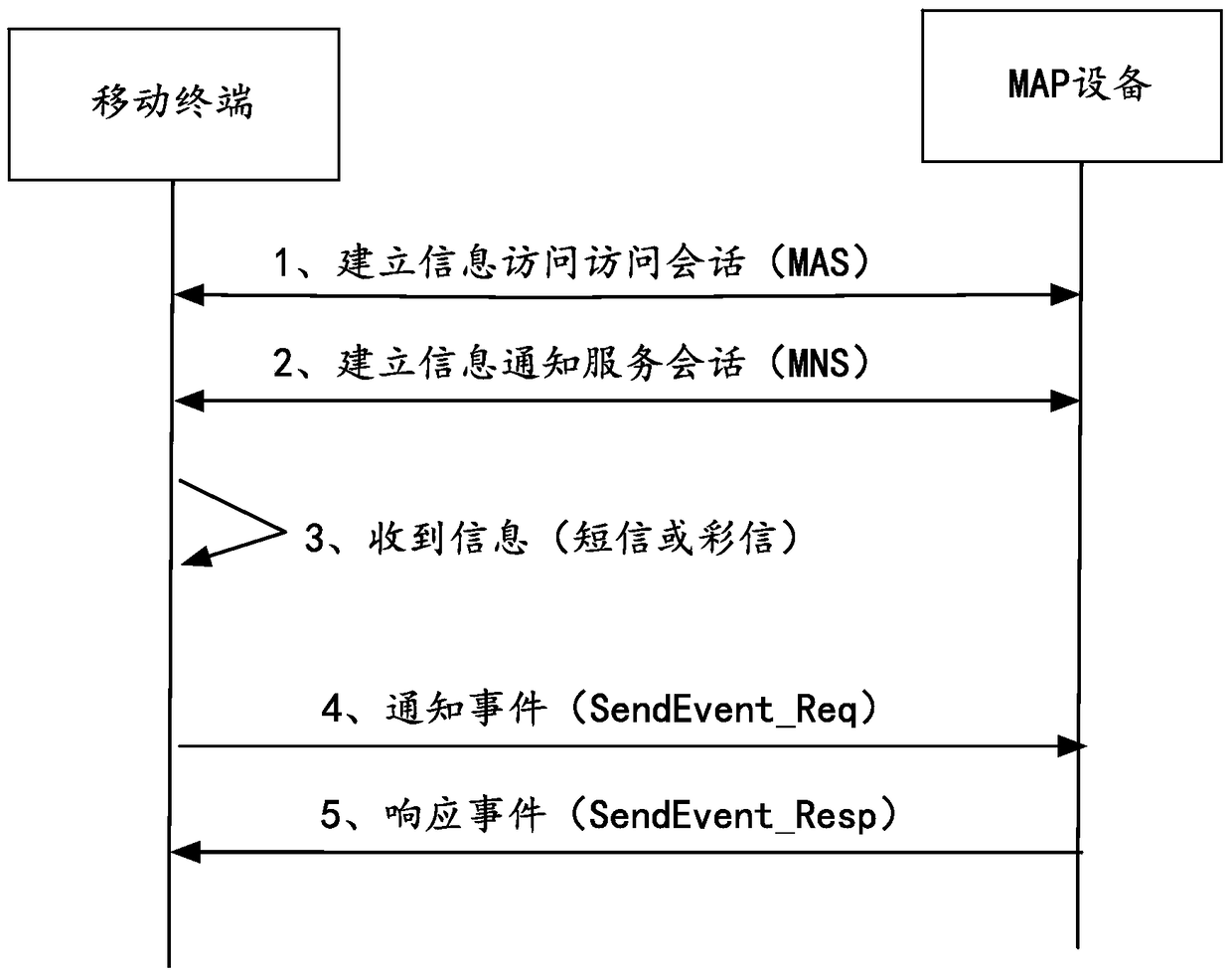
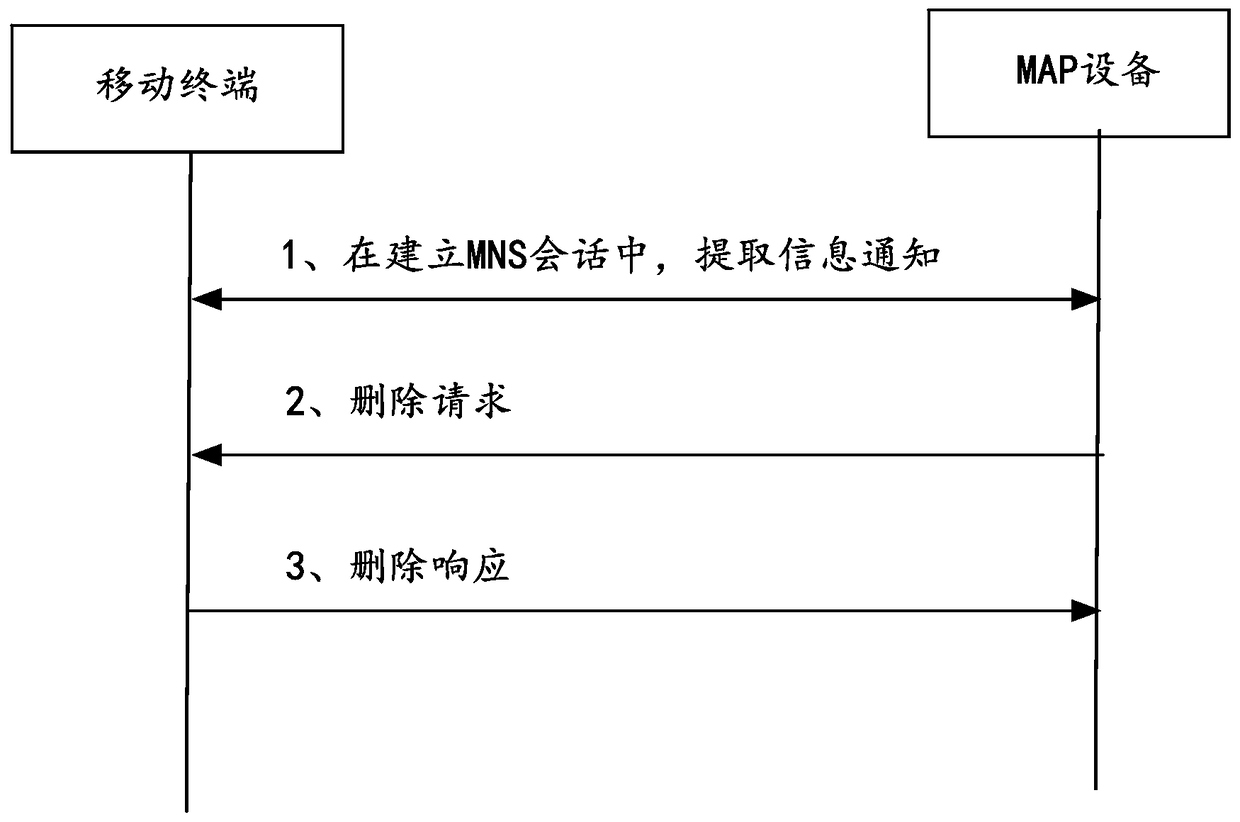
Method used
Image
Examples
Embodiment Construction
[0068] Hereinafter, exemplary embodiments of the present disclosure will be described in more detail with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure can be implemented in various forms and should not be limited by the embodiments set forth herein. On the contrary, these embodiments are provided to enable a more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
[0069] As mentioned earlier, because the iPhone and other iOS-based terminals are closed source, the application (App) downloaded from the App Store and running on the iPhone cannot access or control the information processing program that comes with the iOS system, so it cannot Like open source mobile phones (such as mobile phones based on the andriod system), the security management App directly intercepts ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More