A Method for Mining Attack Frequent Sequence Patterns from Web Logs
A frequent sequence and sequential pattern mining technology, applied in the field of Web security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
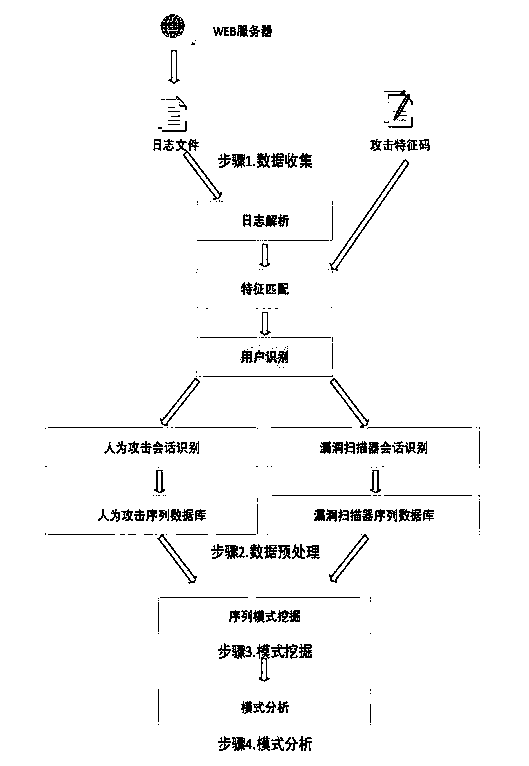
Method used
Image
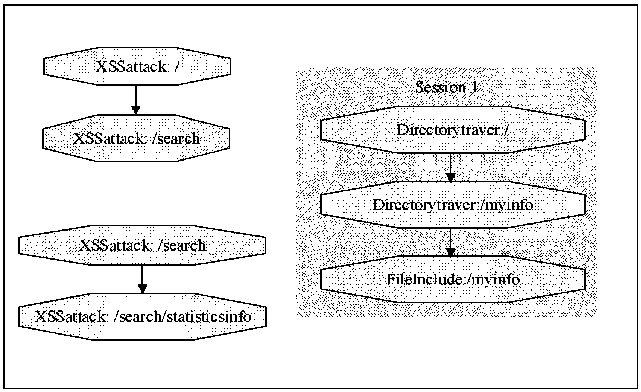
Examples
Embodiment Construction
[0043] The hardware environment of the present invention is mainly a PC host. Among them, the CPU of the PC host is Intel(R) Core(TM) i5-4570, 3.20GHz, the memory is 4GB RAM, and the 64-bit operating system.
[0044] The software implementation of the present invention takes Windows 7 as a platform, and is developed using the Java language under the Eclipse environment. Graphical display with the help of Graphviz tool. The Java version is 1.8.0_40, the Eclipse version is 4.4.2, and the Graphviz version is 2.37.
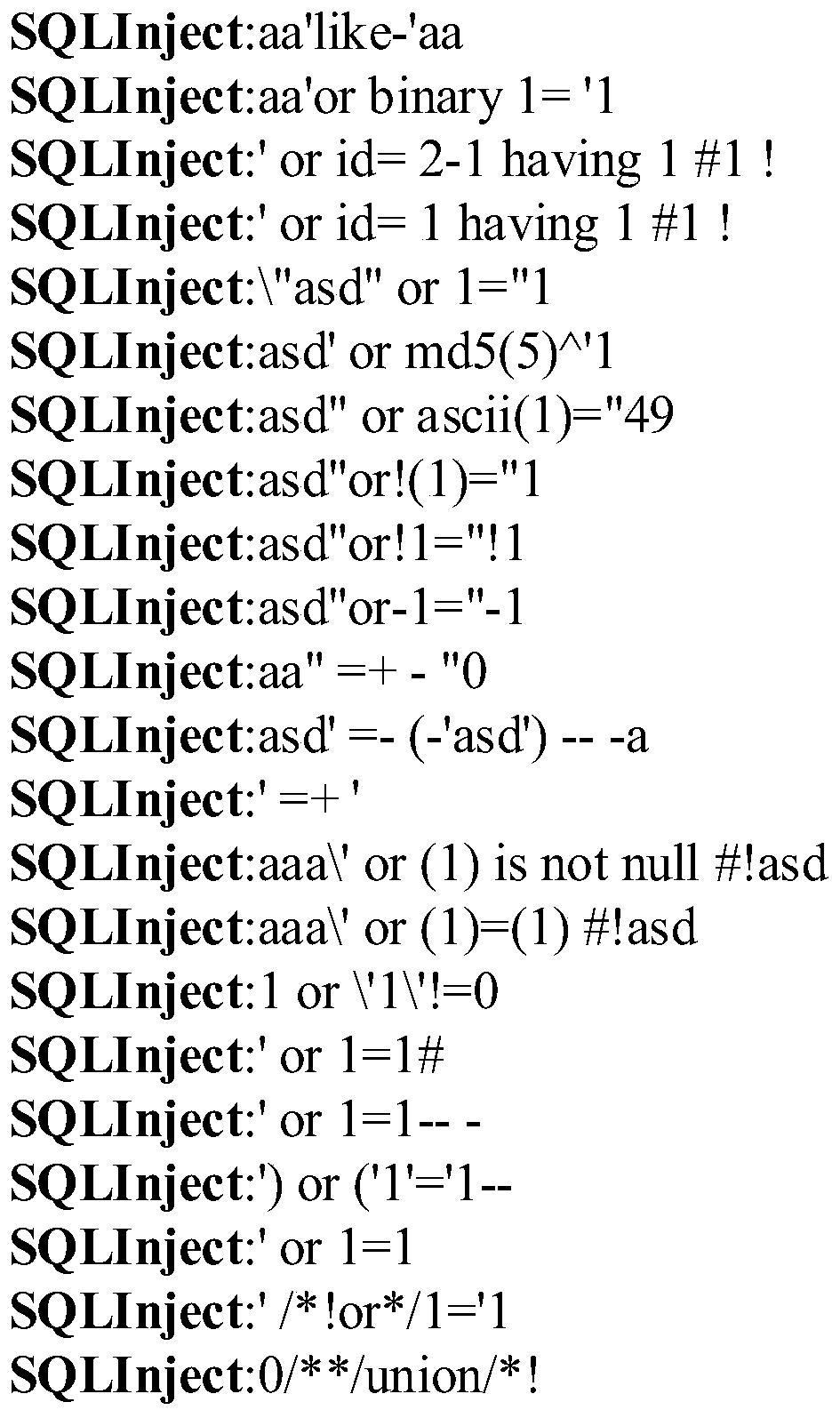
[0045] The experimental data is the Nginx server access log, and its format is visitor IP, authorized user, time, HTTP request, status code, size of transmitted data, upper-level path, and user agent. Specific examples are as follows: Figure 4 shown.
[0046] The operation is mainly divided into two parts, the first part is the log data preprocessing part, and the second part is the data mining and graphical display part.
[0047] 1. Preprocessing part
[0048] ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More