Method and apparatus for malware detection
A malware, call graph technology, used in computer security devices, electrical components, instruments, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
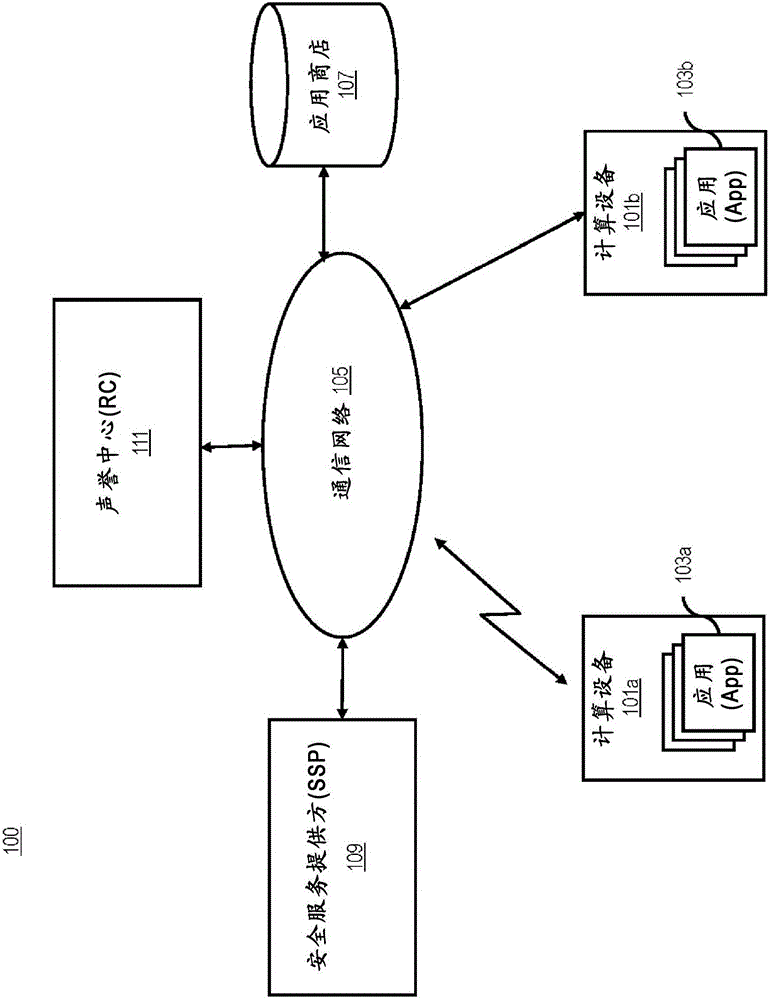
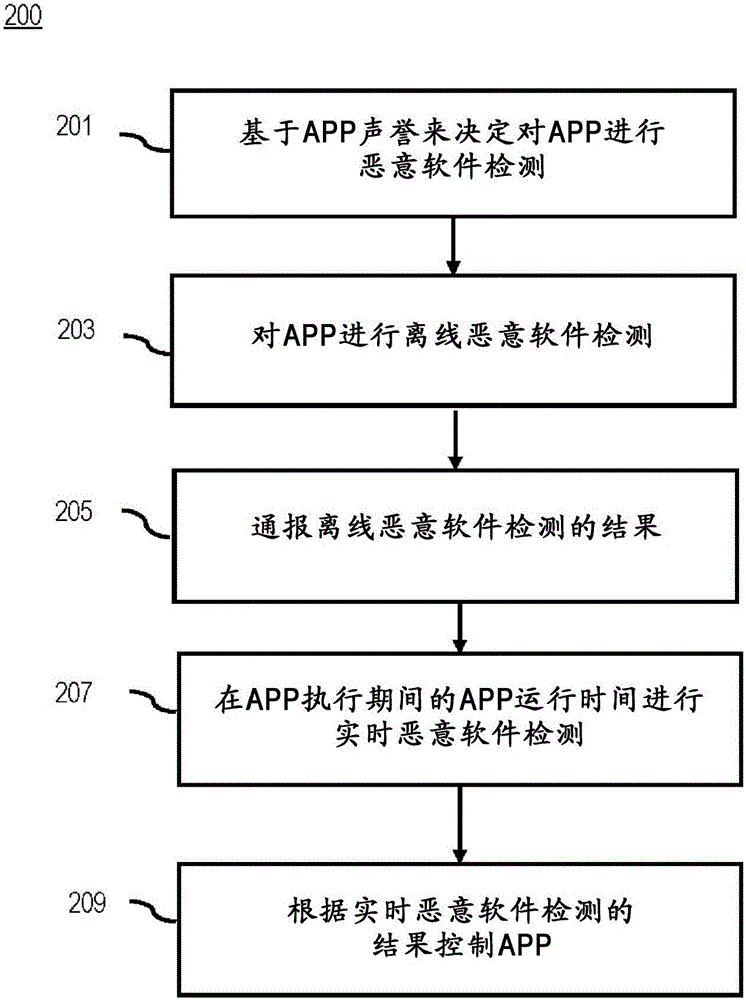
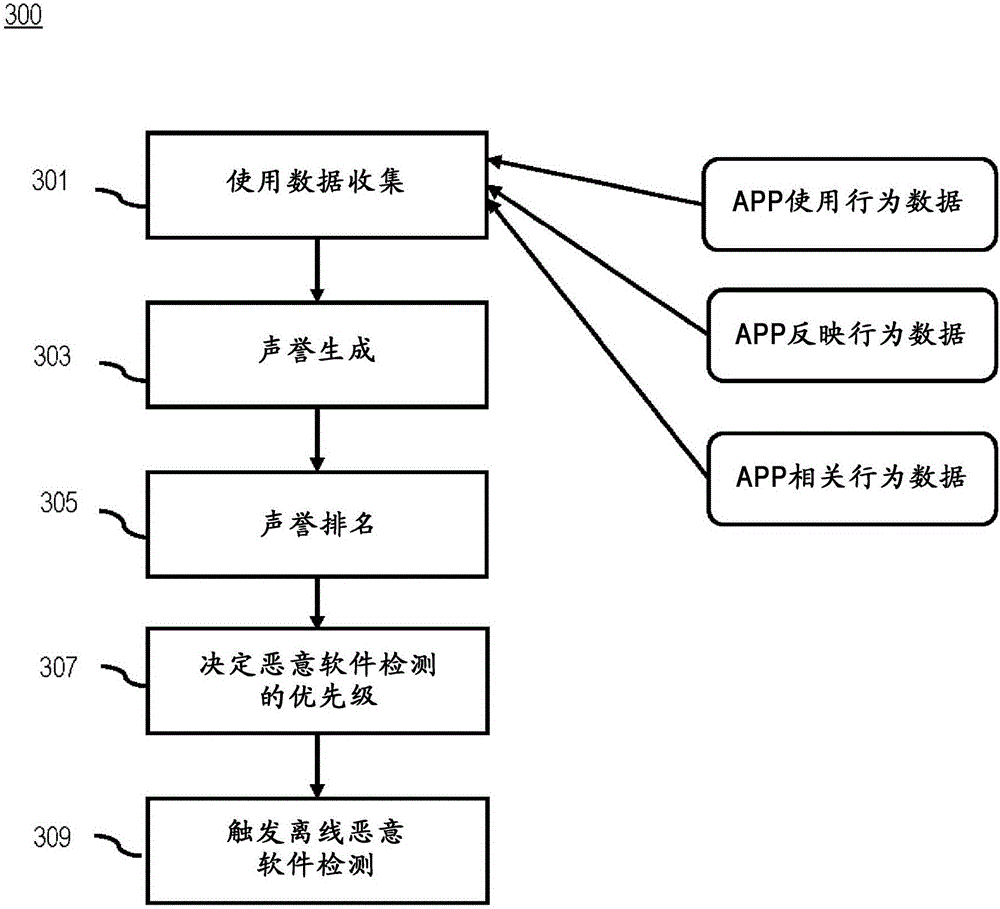
[0025] Examples of methods, apparatus, systems and computer programs for providing malware detection are disclosed. In the following description, for purposes of explanation, numerous specific details are set forth in order to provide a thorough understanding of the embodiments of the invention. It will be apparent, however, to one skilled in the art that the embodiments of the invention may be practiced without these specific details or with an equivalent arrangement. In other instances, well-known structures and devices are shown in block diagram form in order not to unnecessarily obscure the embodiments of the invention. Like reference numerals refer to like elements throughout.
[0026] In the following, a mobile device will be used as an example of a computing device compromised by malware, but other types of computing devices such as laptop computers, desktop computers, home automation and / or control devices are also possible. Also, mobile malware will be used in the d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More