Identify verification system based on recognition technology
A technology of identity verification and identification technology, applied in transmission systems, electrical components, etc., can solve problems such as difficult target feature distinction, difficult target identification and tracking, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
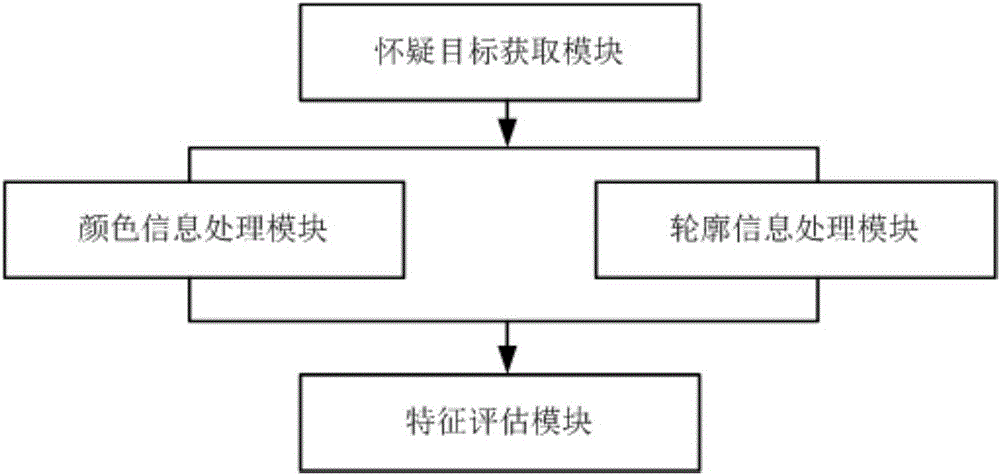
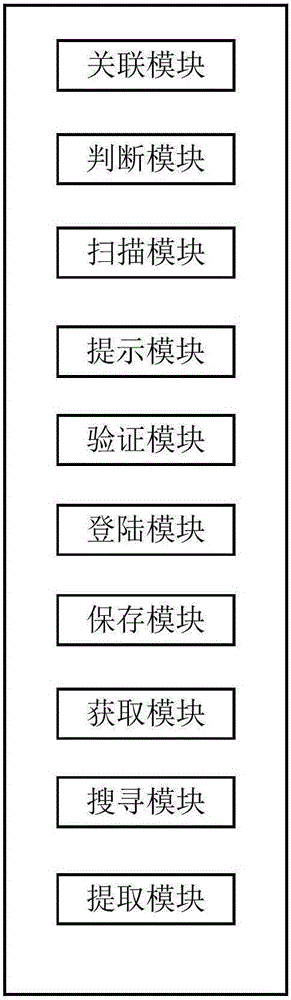
[0049] see figure 1 , figure 2 In this embodiment, an identity verification system based on identification technology includes an identity verification system and a target recognition device connected to the identity verification system, wherein the identity verification system includes:
[0050] An associating module, configured to associate the above-mentioned multiple application systems, so that the accounts and passwords of the multiple application systems become a union;
[0051] A judging module, configured to judge whether at least one of the above-mentioned associated application systems is opened;
[0052]The scanning module is used to scan the cookie file in the client computer when the user opens an application system, so as to determine whether there are cookie files of other application systems associated with the application system in the client computer;
[0053] An acquisition module, configured to acquire the Session identifier stored in the cookie files o...
Embodiment 2
[0086] see figure 1 , figure 2 In this embodiment, an identity verification system based on identification technology includes an identity verification system and a target recognition device connected to the identity verification system, wherein the identity verification system includes:
[0087] An associating module, configured to associate the above-mentioned multiple application systems, so that the accounts and passwords of the multiple application systems become a union;
[0088] A judging module, configured to judge whether at least one of the above-mentioned associated application systems is opened;
[0089] The scanning module is used to scan the cookie file in the client computer when the user opens an application system, so as to determine whether there are cookie files of other application systems associated with the application system in the client computer;
[0090] An acquisition module, configured to acquire the Session identifier stored in the cookie files ...
Embodiment 3
[0123] see figure 1 , figure 2 In this embodiment, an identity verification system based on identification technology includes an identity verification system and a target recognition device connected to the identity verification system, wherein the identity verification system includes:
[0124] An associating module, configured to associate the above-mentioned multiple application systems, so that the accounts and passwords of the multiple application systems become a union;
[0125] A judging module, configured to judge whether at least one of the above-mentioned associated application systems is opened;
[0126] The scanning module is used to scan the cookie file in the client computer when the user opens an application system, so as to determine whether there are cookie files of other application systems associated with the application system in the client computer;
[0127] An acquisition module, configured to acquire the Session identifier stored in the cookie files ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More