A processing method, device and electronic equipment for copying information
A processing method and technology of a processing device are applied in the field of information security and can solve the problems of low operating system security protection efficiency and the like
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
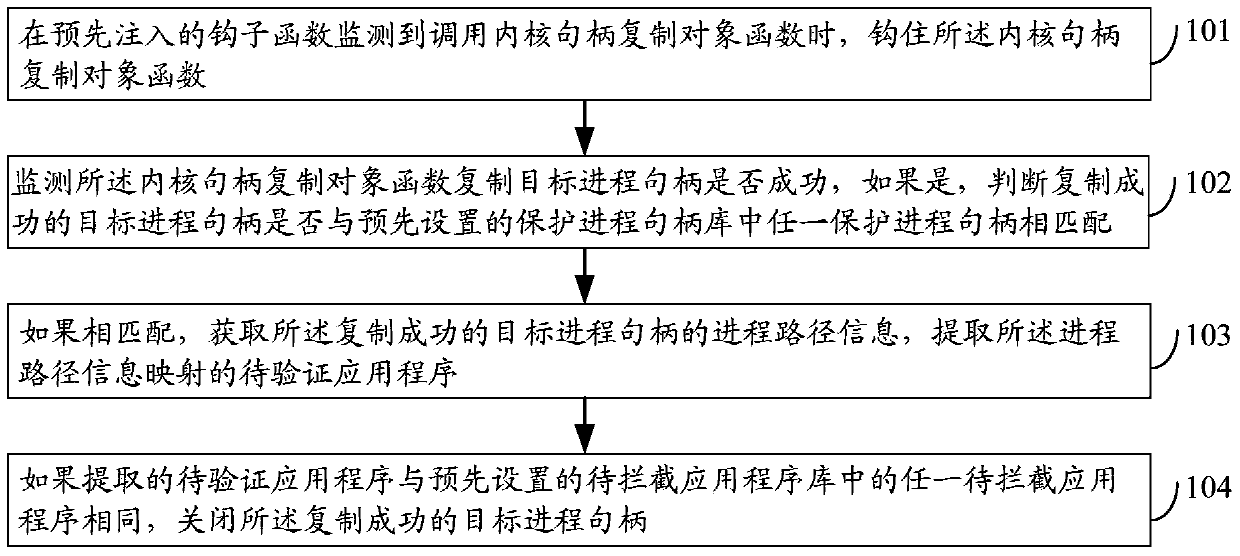
[0055] figure 1 It is a schematic flowchart of a processing method for copying information in Embodiment 1 of the present invention, as shown in figure 1 As shown, the method of this embodiment may include:
[0056] Step 101, when the pre-injected hook function detects that the kernel handle copy object function is called, hook the kernel handle copy object function;
[0057] In this step, as an optional embodiment, the kernel handle duplication object function includes: a kernel NtDuplicateObject function.
[0058] In this embodiment, as an optional embodiment, the hook function is located in the kernel layer of the operating system.
[0059] In the embodiment of the present invention, the injected hook (Hook) function is used to listen to the application layer process, that is, the function call related operation of the application program process located in the application layer, and the related function called by the application layer process and any preset function Whe...
Embodiment 2
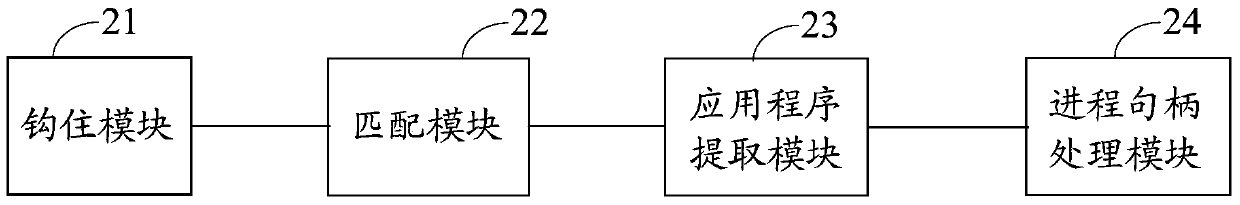
[0097] figure 2 It is a schematic structural diagram of a processing device for copying information in Embodiment 2 of the present invention, as shown in figure 2 As shown, the device of this embodiment may include: a hooking module 21, a matching module 22, an application extraction module 23 and a process handle processing module 24, wherein,
[0098] Hook module 21, for when the pre-injected hook function monitors calling kernel handle copy object function, hook described kernel handle copy object function;
[0099] In this embodiment, as an optional embodiment, the kernel handle copy object function is the kernel NtDuplicateObject function.
[0100] In this embodiment, as an optional embodiment, the hook function is located in the kernel layer of the operating system.
[0101] As an optional embodiment, a hook function may be injected when the security application defense driver application is loaded.
[0102] In the embodiment of the present invention, as an optional...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More