A method and system for shunting reflective ddos traffic
A DDOS and reflective technology, applied in the network field, can solve problems such as transmission congestion, congestion, and high complexity of network construction, and achieve the effect of avoiding transmission congestion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
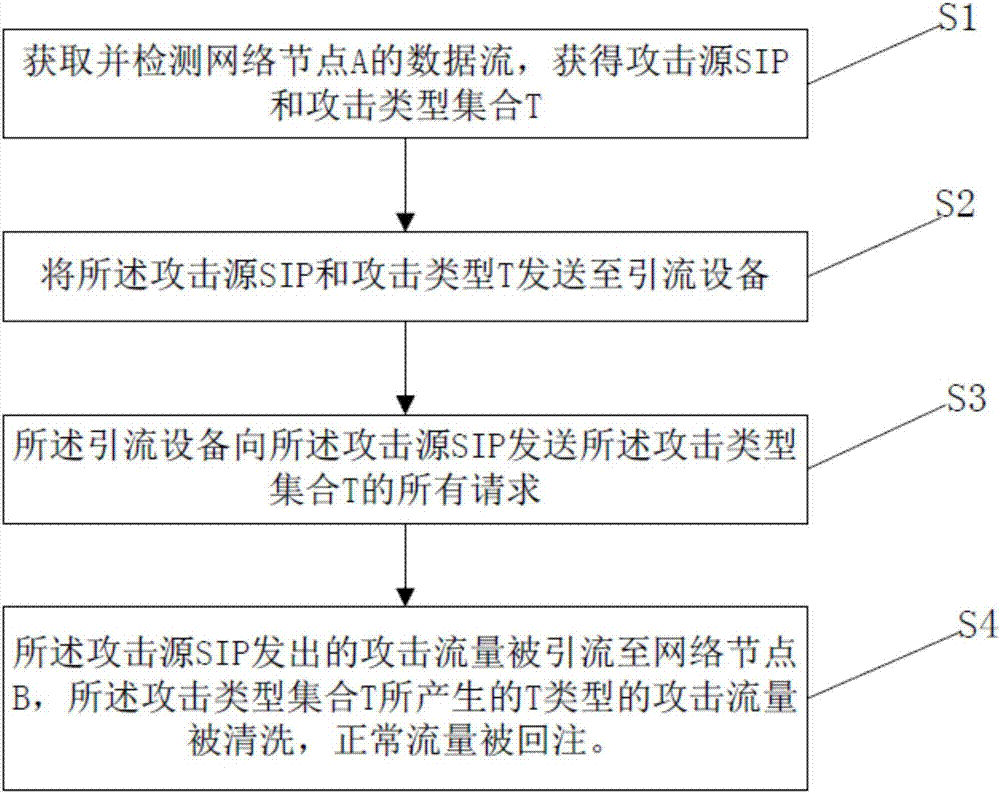
[0027] The technical solutions of the present invention will be further described below in conjunction with the accompanying drawings and through specific implementation methods.
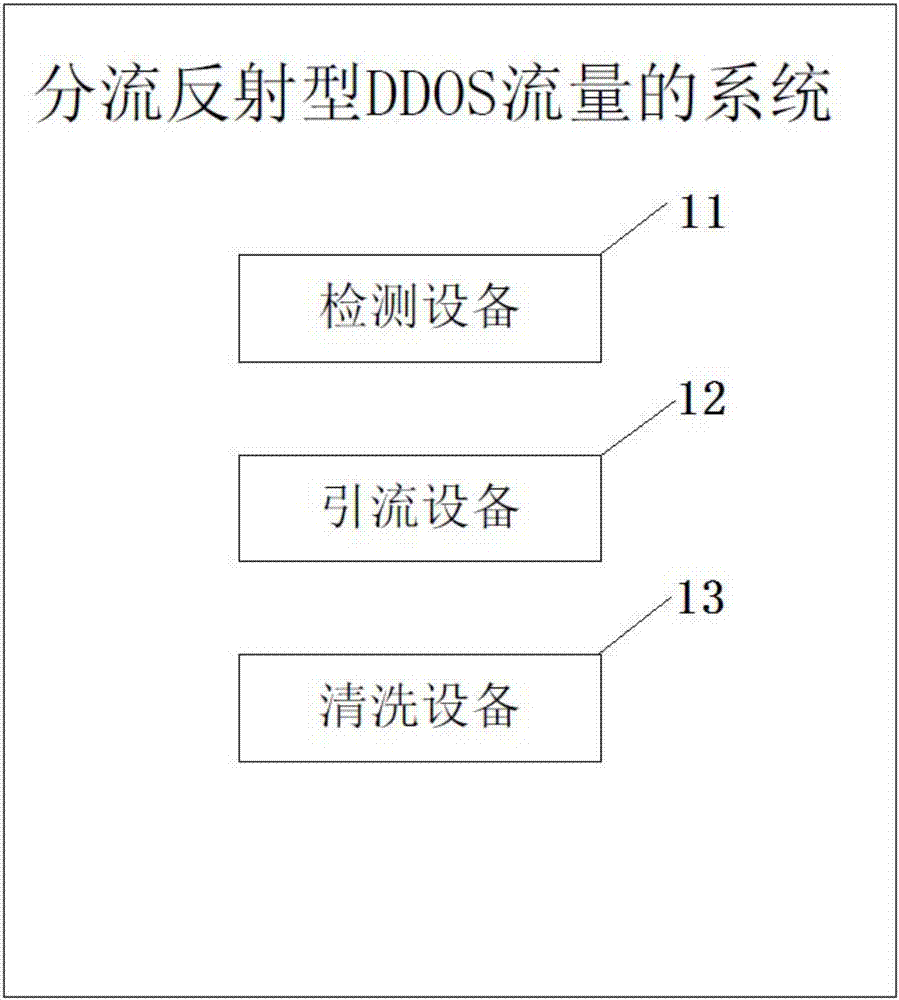
[0028] A method for diverting reflective DDOS traffic includes:
[0029] Step 1 S1: Obtain and detect the data flow of network node A, and obtain the attack source SIP and attack type set T;
[0030] Step 2 S2: Send the attack source SIP and attack type T to the traffic diversion device 12;
[0031] Step 3 S3: the diversion device 12 sends all requests of the attack type set T to the attack source SIP;
[0032] Step 4 S4: The attack traffic sent by the attack source SIP is diverted to the network node B, the T-type attack traffic generated by the attack type set T is cleaned, and the normal traffic is injected back.
[0033] The attack type set T in this embodiment includes ntp, ssdp and dns, which are relatively common attack types. Of course, in other embodiments, the attack type set T can be ot...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More