An implementation method of sm2 white-box digital signature based on remainder system
A residual system and digital signature technology, applied in the field of information security, can solve the problems of high use cost, poor versatility, and inability to deal with white-box attack methods, and achieve the effect of expanding the scope of use, high practicability, and reducing the cost of use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
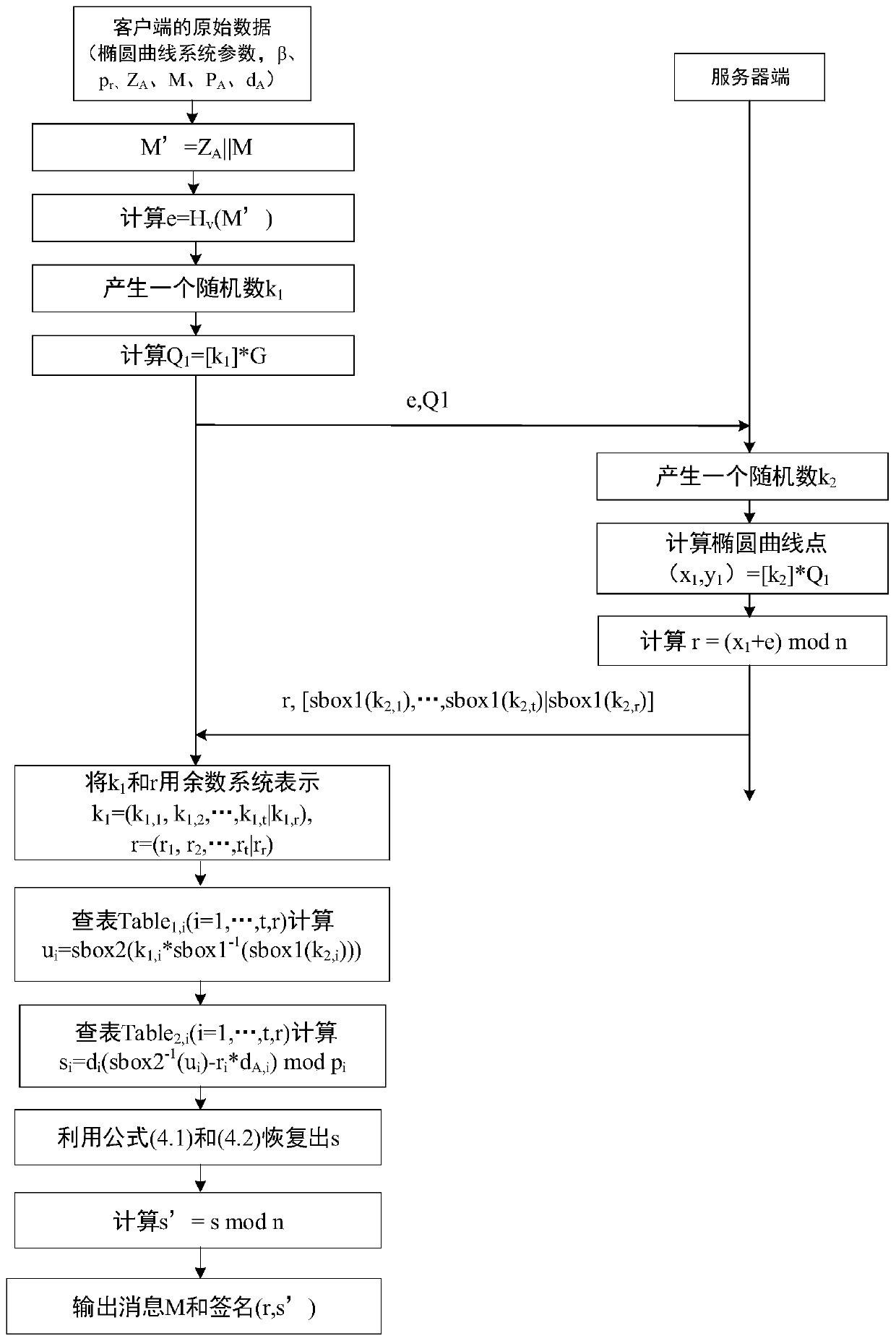
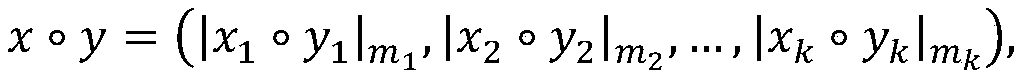
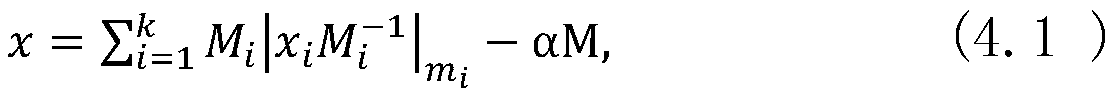
[0033] The design idea of the present invention is to conduct research on the problem that the key operation is not safe in an untrusted environment, and malicious attackers can obtain the system key through white-box attack means, and realize the splitting of large numbers by using the remainder system, thereby reducing The size of the key table; by using scrambling and obfuscation to ensure that the intermediate results are invisible to the attacker; by using the random factor in the cloud to ensure the unknownness of the terminal key calculation relationship, the security of the signature private key during the terminal signature calculation process is realized, and at the same time It can be verified using the standard SM2 signature verification algorithm.
[0034] The present invention is constructed based on the national commercial cryptographic algorithm SM2 digital signature algorithm. Please refer to the management standard issued by the National Commercial Cryptogra...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More