Blockchain encryption retrieval scheme
A block chain and scheme technology, applied in the direction of instruments, electrical digital data processing, digital data protection, etc., can solve the problem of low efficiency of homomorphic encryption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
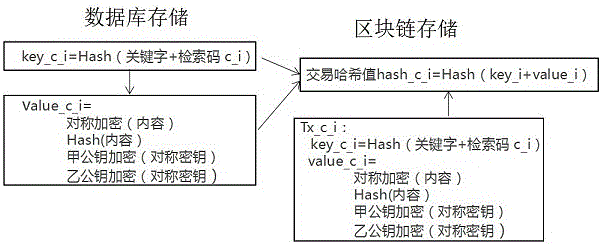
[0018] Example 1, refer to the instructions attached figure 1 , This example illustrates the implementation principle of the encrypted retrieval scheme on the blockchain;
[0019] User A needs to store data on the blockchain, including the searched keywords and content. The user sets a search code c_i for user A to view it by himself or authorize it to be viewed by user B. The steps are as follows;
[0020] Step S1, the keyword to be retrieved and the retrieval code c_i are connected in series, and the hash operation is performed to calculate the hash value hash_c_i. The content value corresponding to the keyword is encrypted with a symmetric key, and the content hash value Hash (content ), encrypt the symmetric key with the public key of A, and encrypt the symmetric key with the public key of B;
[0021] Step S2: Hash all the data obtained in step S1 to obtain the transaction hash value Hash_c_i, which is written into the blockchain together;
[0022] Step S3, data download analysis ...
Embodiment 2
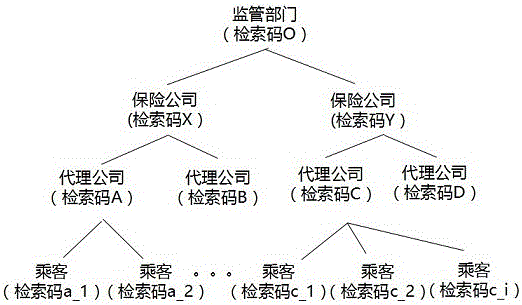
[0027] Example 2, refer to the instructions attached figure 2 , This example illustrates the encryption retrieval scheme of insurance policies on the blockchain;
[0028] Regulatory departments, underwriting companies, agency companies, and passengers are managed with hierarchical authority. The supervisory part can view all the data. The underwriting company can view the information of its subordinate agencies and passengers. The agency can query the information of subordinate passengers, and passengers can only view If you do not know your own information, the agent’s customer service cannot inquire about the passenger’s information;
[0029] Encrypt according to the information query requirements. After the underwriting company or agency company encrypts the information, it is uploaded after being signed by the private key, and an encrypted index is established in the blockchain and database.
[0030] The supervisor, 10 underwriting companies have asymmetric public and private k...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More