Unlocking method and apparatus
A technology for unlocking and unlocking the interface, applied in the fields of instruments, electrical digital data processing, digital data authentication, etc., can solve problems such as poor security, and achieve the effect of solving poor security and enhancing diversity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
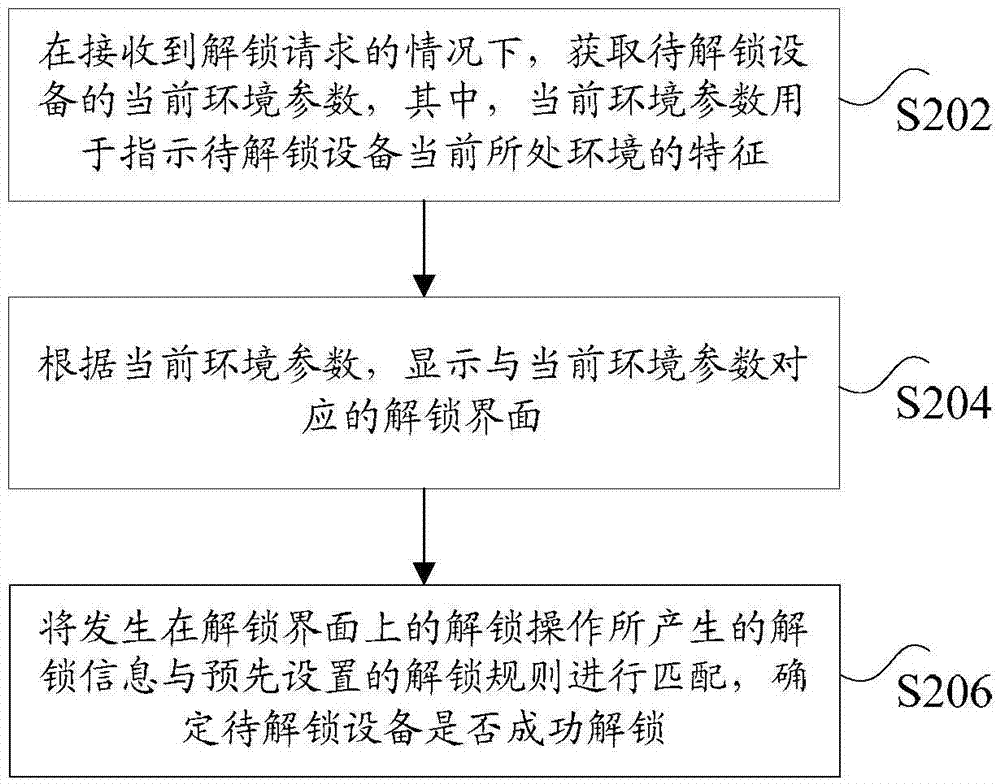
[0033] According to the embodiment of the present application, an embodiment of an unlocking method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions, and, although A logical order is shown in the flowcharts, but in some cases the steps shown or described may be performed in an order different from that shown or described herein.
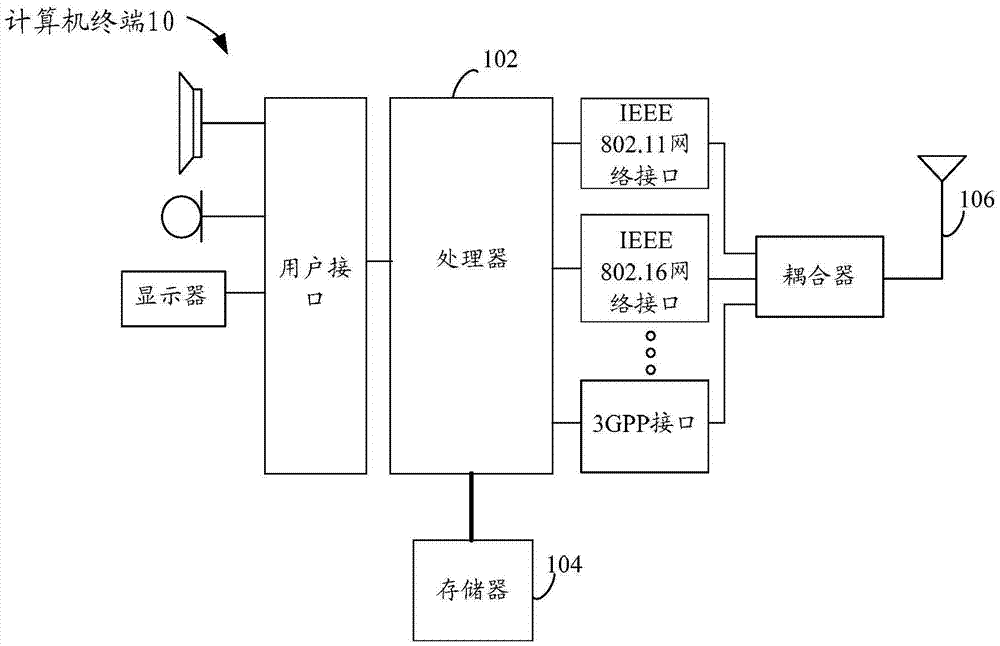
[0034] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. Take running on a computer terminal as an example, figure 1 It is a block diagram of the hardware structure of a computer terminal of an unlocking method according to the embodiment of this application. Such as figure 1 As shown, the computer terminal 10 may include one or more (only one is shown in the figure) processors 102 (the processor...
Embodiment 2
[0093] According to an embodiment of the present application, an unlocking device for implementing the above unlocking method is also provided, such as Figure 8 As shown, the apparatus may include: a first acquiring unit 801 , a first display unit 803 , and a determining unit 805 .
[0094] Wherein, the first acquiring unit 801 is configured to acquire the current environment parameters of the device to be unlocked when an unlock request is received, wherein the current environment parameters are used to indicate the characteristics of the environment in which the device to be unlocked is currently located; the first display unit 803, configured to display an unlocking interface corresponding to the current environmental parameters according to the current environmental parameters; the determining unit 805, configured to match the unlocking information generated by the unlocking operation on the unlocking interface with the preset unlocking rules, and determine the Unlock Whe...
Embodiment 3
[0113] Embodiments of the present application may provide a computer terminal, and the computer terminal may be any computer terminal device in a group of computer terminals. Optionally, in this embodiment, the foregoing computer terminal may also be replaced with a terminal device such as a mobile terminal.
[0114] Optionally, in this embodiment, the foregoing computer terminal may be located in at least one network device among multiple network devices of the computer network.
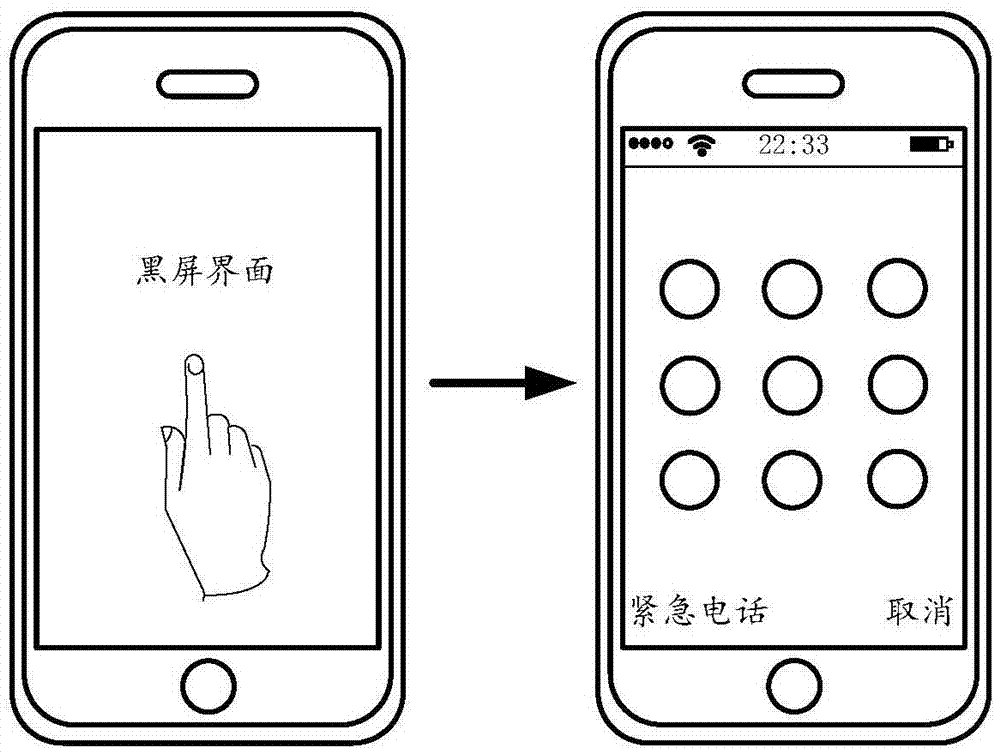
[0115] In this embodiment, the above-mentioned computer terminal can execute the program code of the following steps in the vulnerability detection method of the application program: when an unlock request is received, obtain the current environment parameters of the device to be unlocked, wherein the current environment parameters are used to indicate The characteristics of the environment where the device to be unlocked is currently located; according to the current environment parameters, display...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap