Security authentication method for OpenStack open source cloud user
A security authentication and cloud user technology, applied in the field of identity authentication, can solve the problems of high authentication cost and additional hardware equipment required for authentication, and achieve the effects of improving authentication efficiency, reducing costs, and ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0043] Below in conjunction with accompanying drawing and specific embodiment, the present invention is described in further detail:
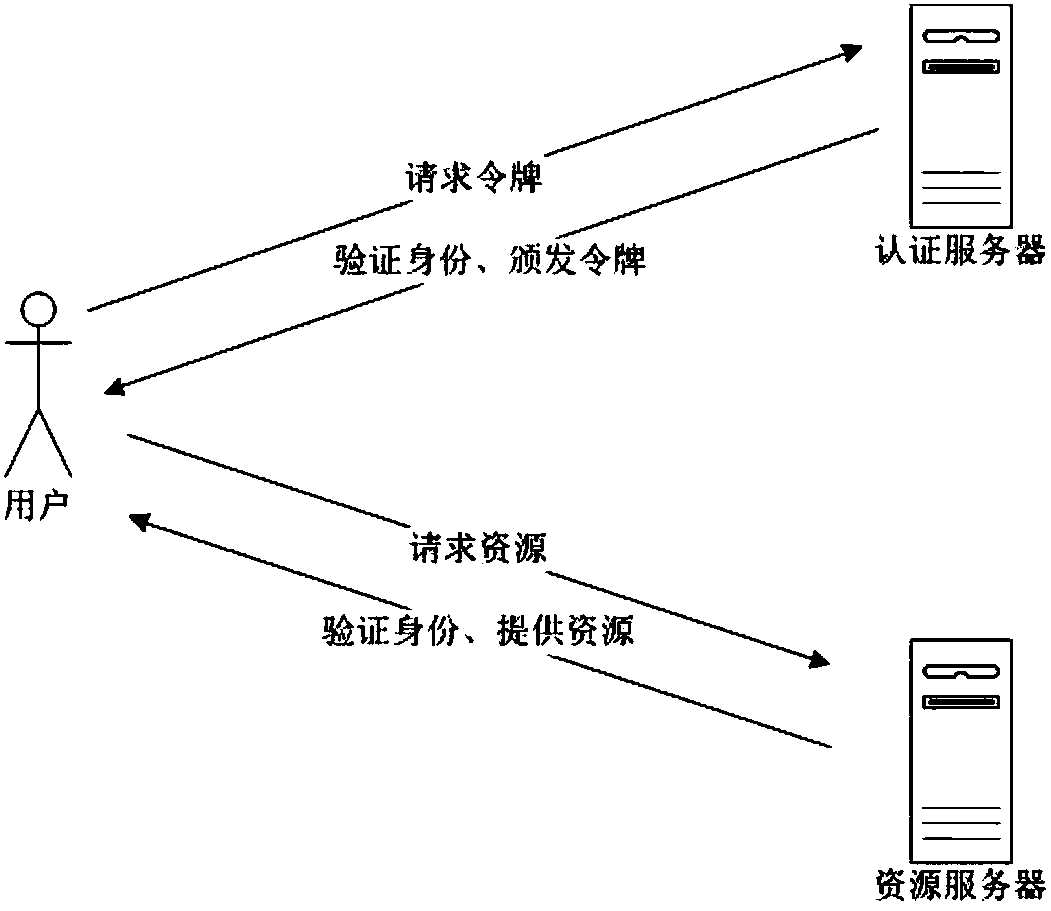
[0044] refer to figure 1 , the security authentication system applicable to the present invention includes an authentication server, a user and a resource server, wherein the user is used to make an authentication request to the authentication server and a resource request to the resource server, and the authentication server is used to verify the identity of the user and issue an order to the user Token, the resource server is used to verify the user token and provide resources.
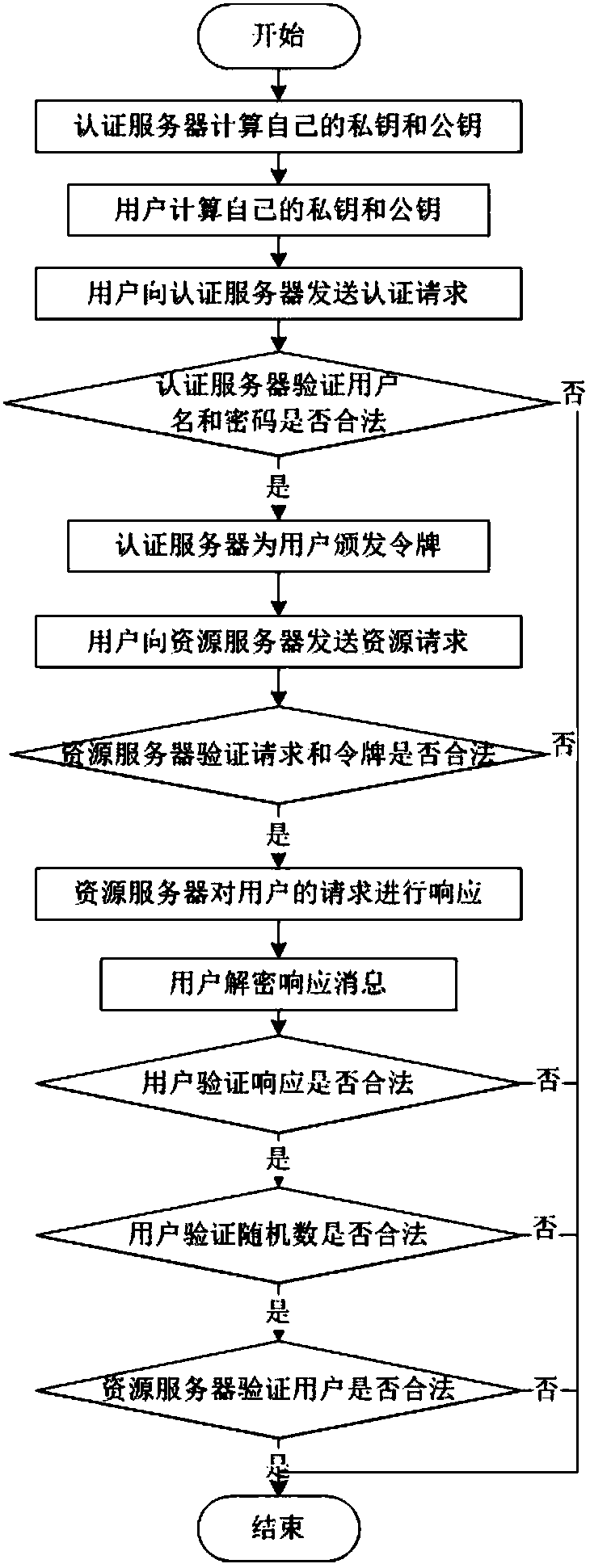
[0045] refer to figure 2 ,
[0046] A security authentication method for an OpenStack open source cloud user, comprising the steps of:
[0047] Step 1) The authentication server calculates its own public key PK s and private key SK s :
[0048] Step 1a) The authentication server determines the finite field GF(2 m ), and in GF(2 m ), select the elliptic curve...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap