Internet of Things equipment, Internet of Things authentication platform, and authentication method and system
An Internet of Things device and Internet of Things authentication technology, which is applied in the field of authentication methods and systems, Internet of Things authentication platforms, and Internet of Things devices, can solve problems such as low communication security and poor authentication effects, and achieve the effect of ensuring uniqueness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
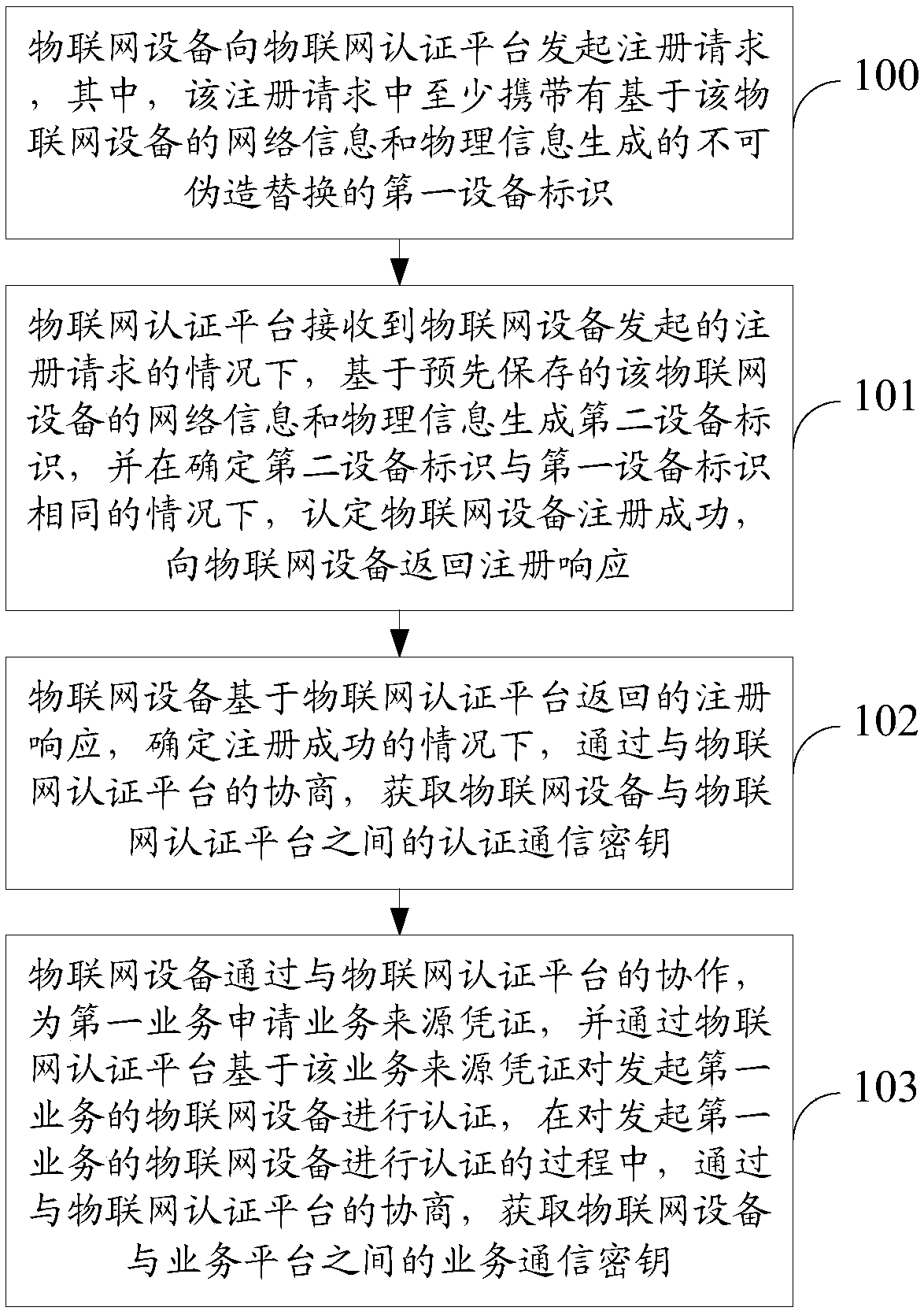
[0053] refer to figure 1 As shown, in Embodiment 1 of the present invention, the flow of the authentication method is as follows:
[0054] Step 100: The Internet of Things device initiates a registration request to the Internet of Things authentication platform, wherein the registration request at least carries an unforgeable and replaceable first device identifier generated based on the network information and physical information of the Internet of Things device.
[0055] Step 101: When the IoT authentication platform receives the registration request initiated by the IoT device, it generates a second device ID based on the pre-saved network information and physical information of the IoT device, and determines the difference between the second device ID and the first If the device identifiers are the same, it is determined that the registration of the IoT device is successful, and a registration response is returned to the IoT device.
[0056] Step 102: Based on the regist...
Embodiment 2
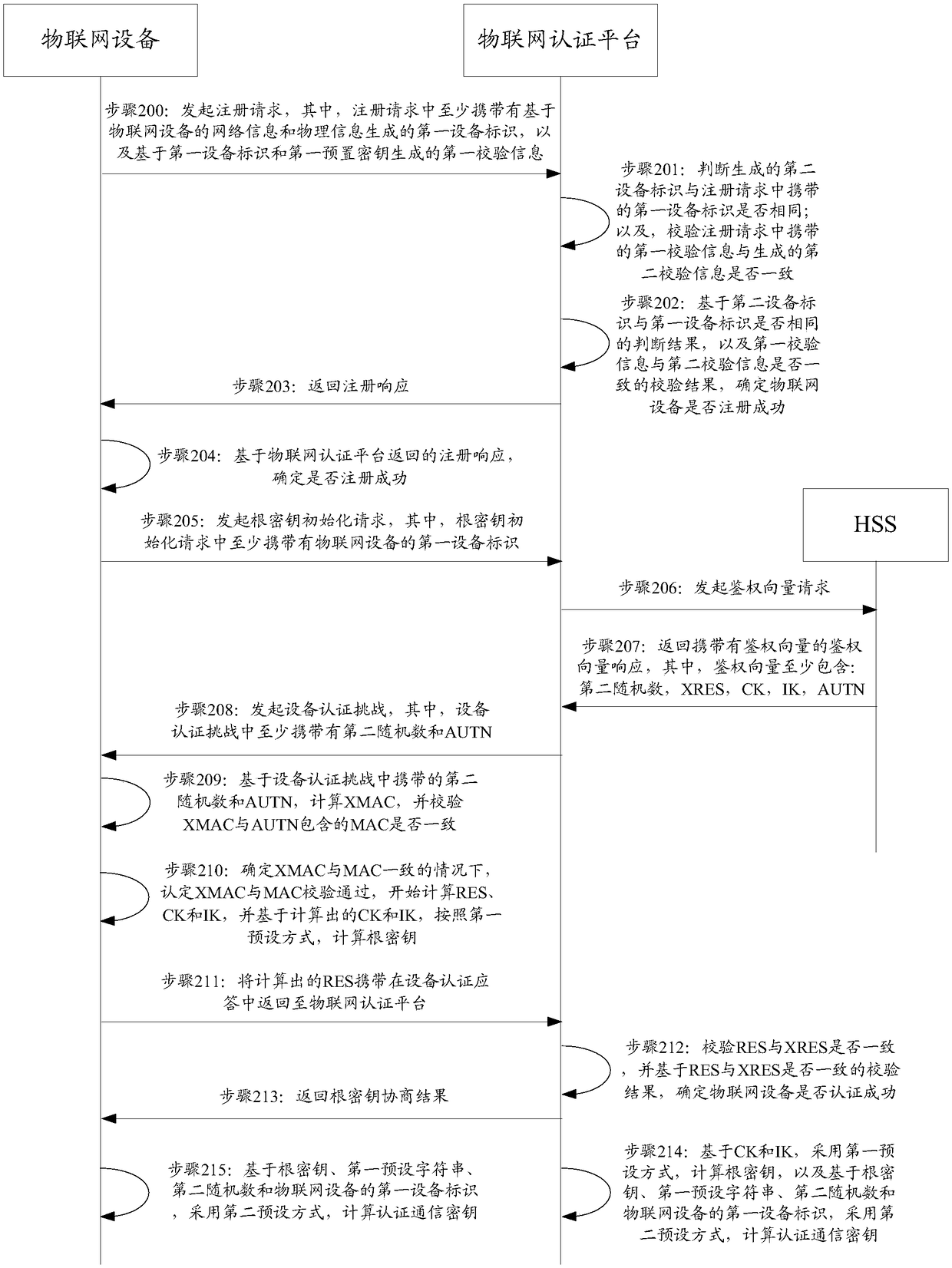
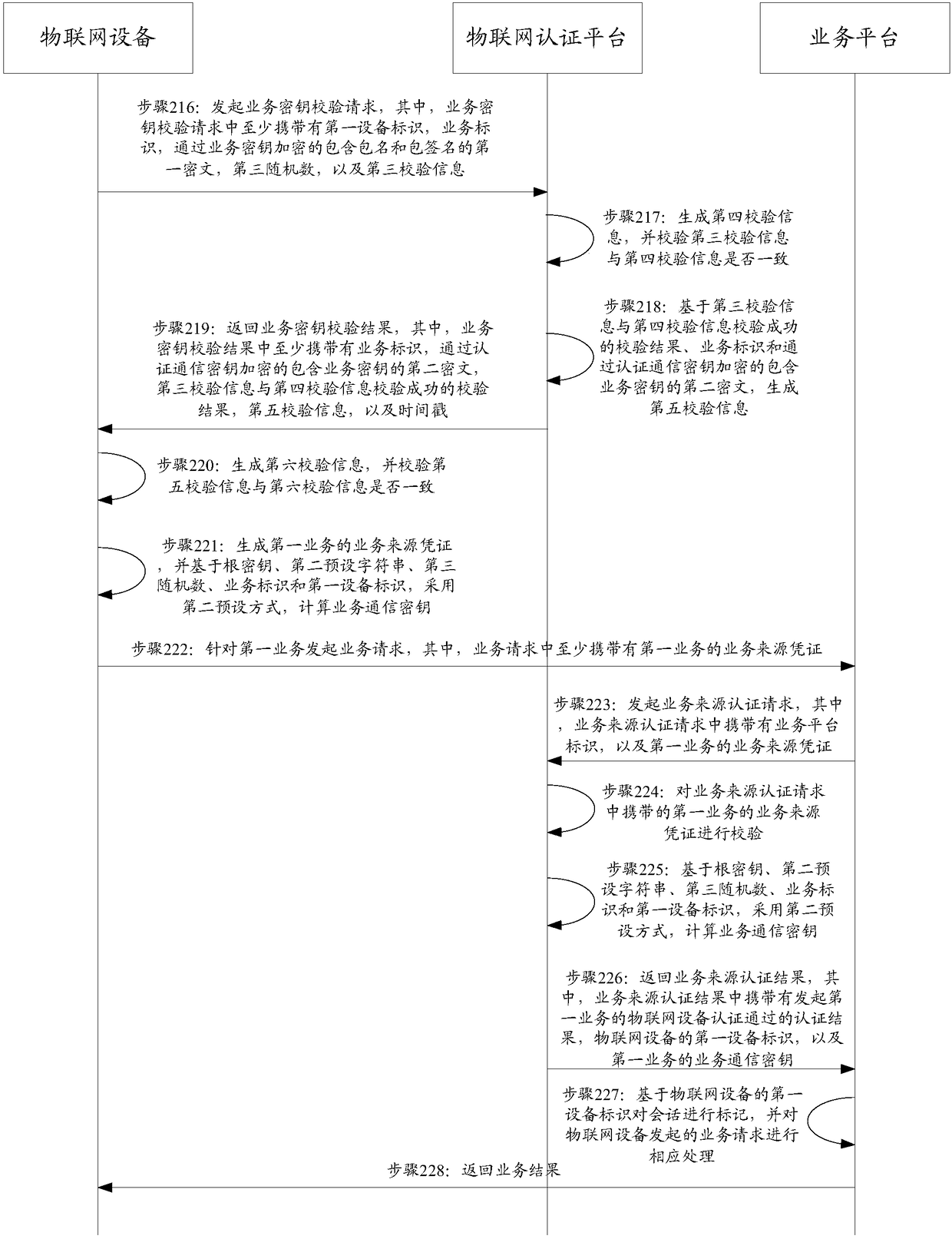
[0060] The authentication method in the above-mentioned embodiment is described in further detail below, refer to Figure 2A and Figure 2B As shown, in Embodiment 2 of the present invention, the specific flow of the authentication method is as follows:
[0061] Step 200: The Internet of Things device initiates a registration request to the Internet of Things authentication platform, wherein the registration request carries at least an unforgeable and replaceable first device identifier generated based on the network information and physical information of the Internet of Things device, and a first device identifier based on the first First verification information generated by the device identifier and the first preset key.
[0062] Preferably, the network information of the IoT device may be, but not limited to, any one or any combination of the following: network access identifier, International Mobile Subscriber Identity (IMSI), Media Access Control (Medium Access Control...
Embodiment 3
[0097] In order to be able to obtain inherent parameter information such as network information and physical information of IoT devices, and to be able to negotiate with the IoT authentication platform for authentication communication keys and business communication keys, a general authentication module can be integrated in IoT devices. The authentication module communicates with the Internet of Things authentication platform to realize the above functions.
[0098] The following uses specific application scenarios to further describe the implementation of the registration phase in detail, see image 3 As shown, in Embodiment 3 of the present invention, the specific process of the registration phase is as follows:
[0099] Step 300: When the general authentication module of the IoT device determines that the preset registration conditions are met, a registration process is triggered. For example, when the general authentication module of the IoT device detects that the baseba...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More