Acquisition method for field value of role property field in form
A technology for acquiring methods and field values, applied in the fields of digital data authentication, electrical digital data processing, special data processing applications, etc., can solve the problems of system user loss, increased authorization, frequent operations, etc., to reduce the probability of authorization errors, The effect of improving efficiency and reliability, and improving the efficiency of rights management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] The technical solution of the present invention will be further described in detail below in conjunction with the accompanying drawings, but the protection scope of the present invention is not limited to the following description.
[0040] [Example 1] If Figure 4 As shown, the method for obtaining the field value of the role property field in the form includes: displaying the candidate field value corresponding to the role property field, and the candidate field value is a role. For example, the form contains the role property field "Contract Signer", and the candidate field values include Salesperson 1, Salesperson 2, and Salesperson 3.
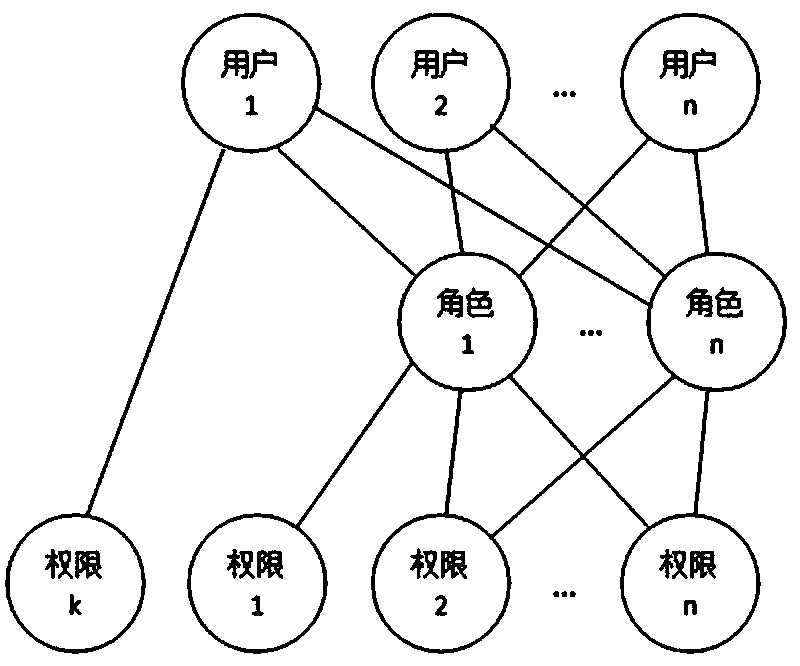
[0041] Such as Figure 5 As shown, the role is an independent individual, not a group / class. A role can only be associated with a unique user at the same time, and a user is associated with one or more roles. The role belongs to the department, and the role is authorized according to the work content of the role, and the name of...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap