Icon safe operation method under voice screen mouse check
A technology for safe operation and icons, applied in the security field, can solve problems such as inability to guarantee timeliness, adverse consequences, and increase labor costs, and achieve the effect of being more practical, reducing errors, and facilitating development.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
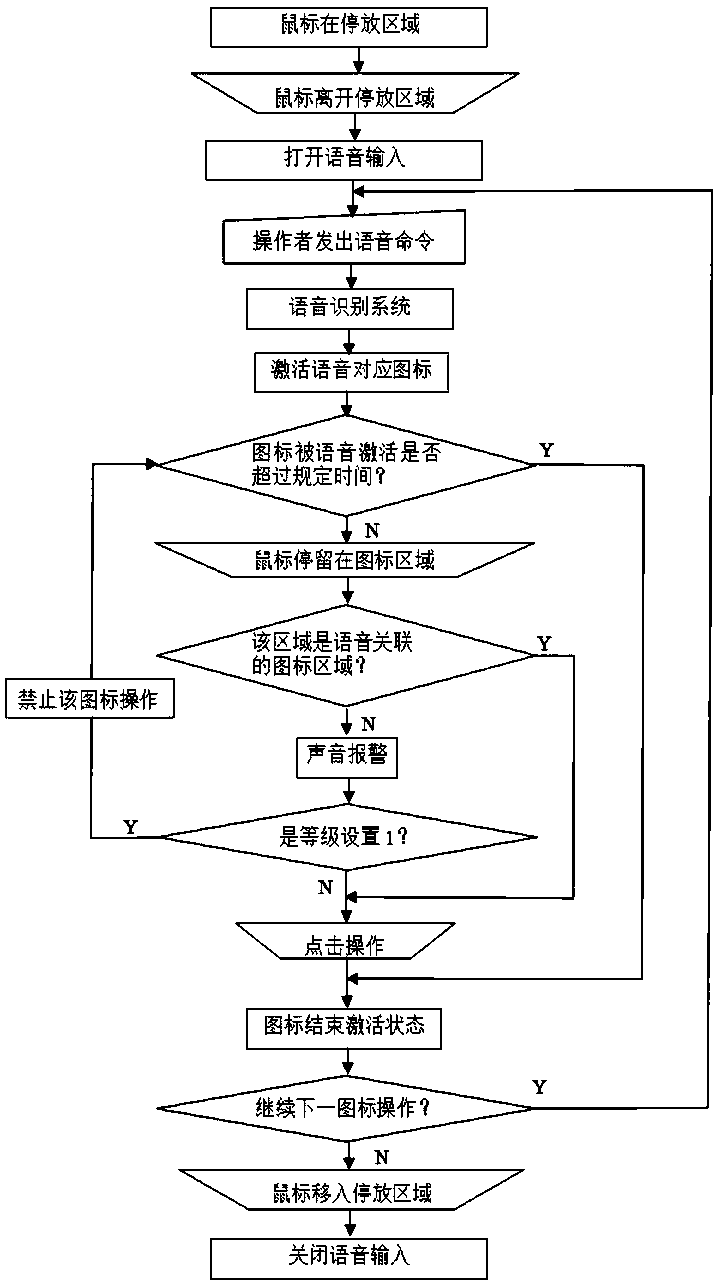
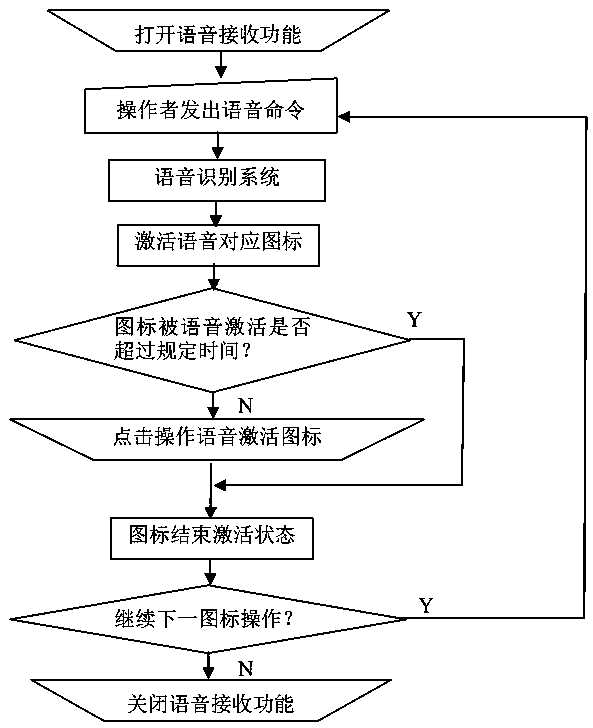
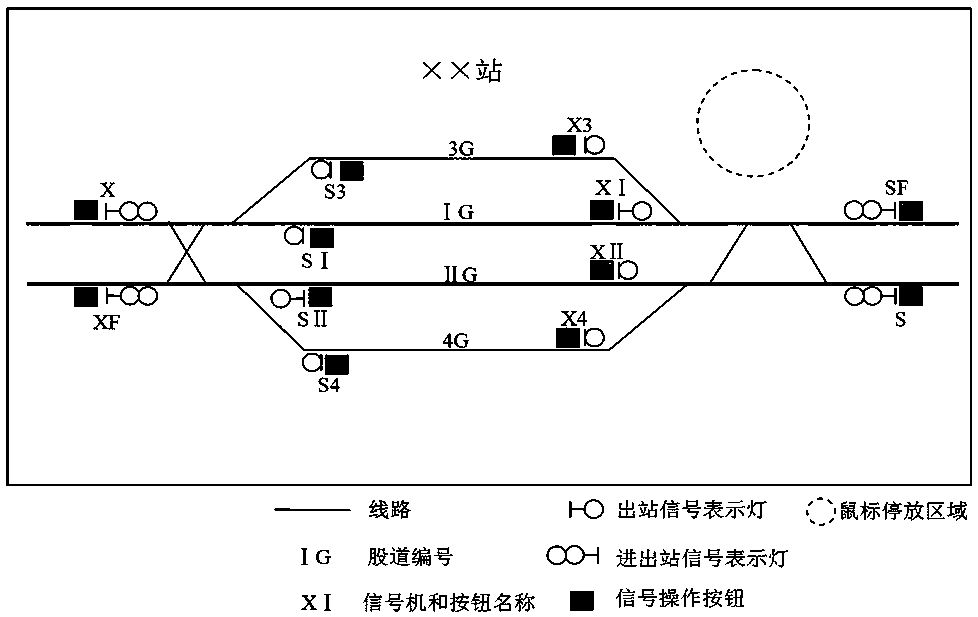
[0030] The present invention is described in further detail now in conjunction with accompanying drawing.
[0031] The technical solutions created and realized by the present invention are divided into two types: a newly developed system and an existing system.
[0032] 1. New development system
[0033] For the new development system, the following work needs to be added when programming:
[0034] 1. Set the association information between voice and screen icon
[0035] The so-called setting the association information between the voice and the screen icon is to set the corresponding relationship between the voice and the screen icon, and construct the voice icon. In principle, there is a one-to-one correspondence between speech and icons, but when the system is more complex, emphasizing the one-to-one correspondence may make the speech too complicated and cause inconvenience to the operation. Therefore, it can be designed as many-to-one and one-to-many according to the ac...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More