Log desensitization method, server and storage medium
A log and desensitization technology, applied in the field of data security, can solve the problem of destroying original log information and achieve the effect of dynamic protection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0026] In the following description, use of suffixes such as 'module', 'part' or 'unit' for denoting elements is only for facilitating description of the present invention and has no specific meaning by itself. Therefore, 'module', 'part' or 'unit' may be used in combination.
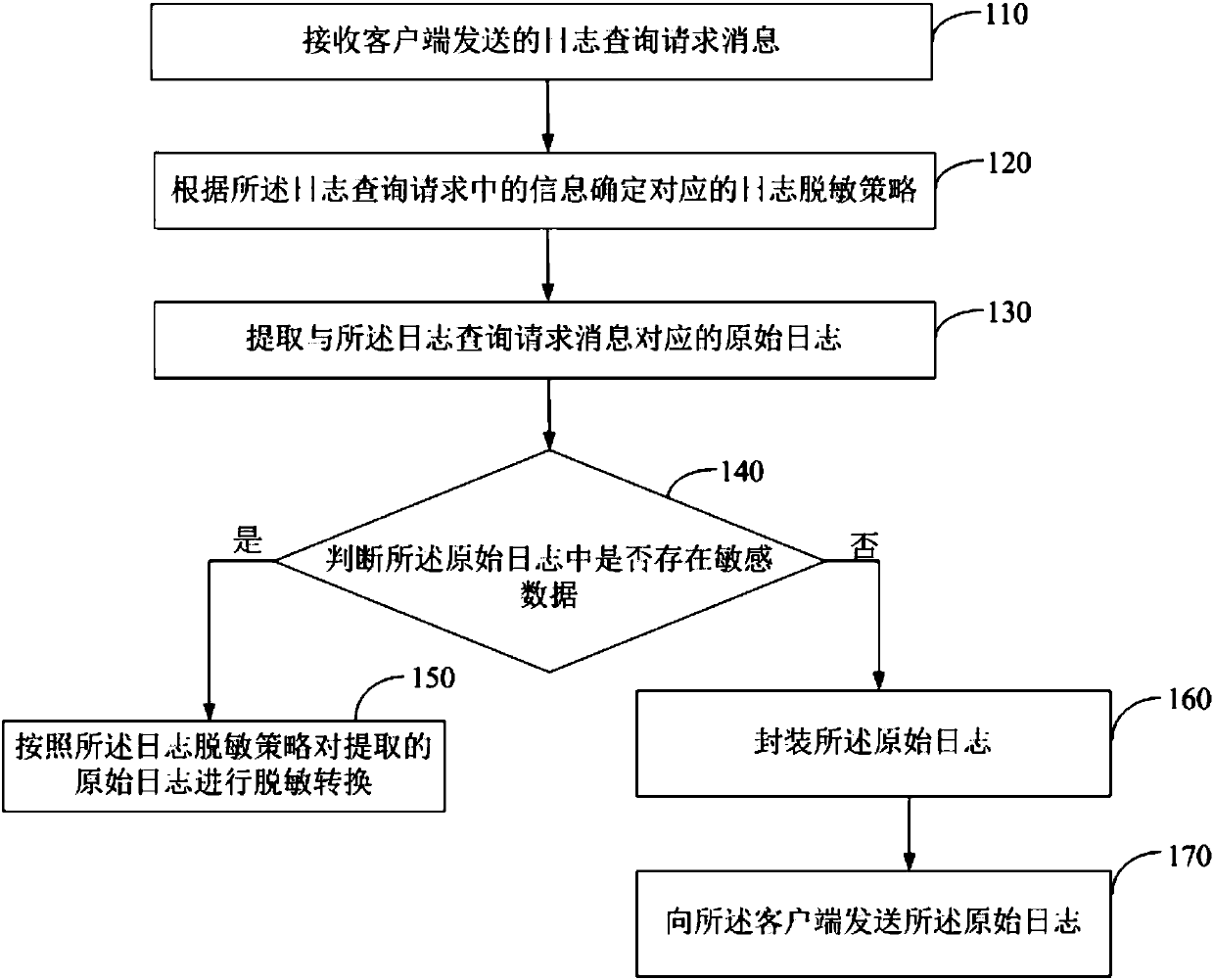
[0027] like figure 1 As shown, it is a schematic flowchart of the log desensitization method provided by the embodiment of the present invention. exist figure 1 Among them, the log desensitization method includes:
[0028] Step 110, receiving a log query request message sent by the client.
[0029] Specifically, when the client is connected to the client through the network, and the client initiates a log query request to the server through the network, the log query request is received. The message format of the log query request carries ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More