A Method of Preventing Injection Attacks for Coprocessors of Public Key Cryptography Algorithms
A technology of coprocessor and cryptographic algorithm, applied in the direction of public key of secure communication, digital transmission system, secure communication device, etc. The effect of injection attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
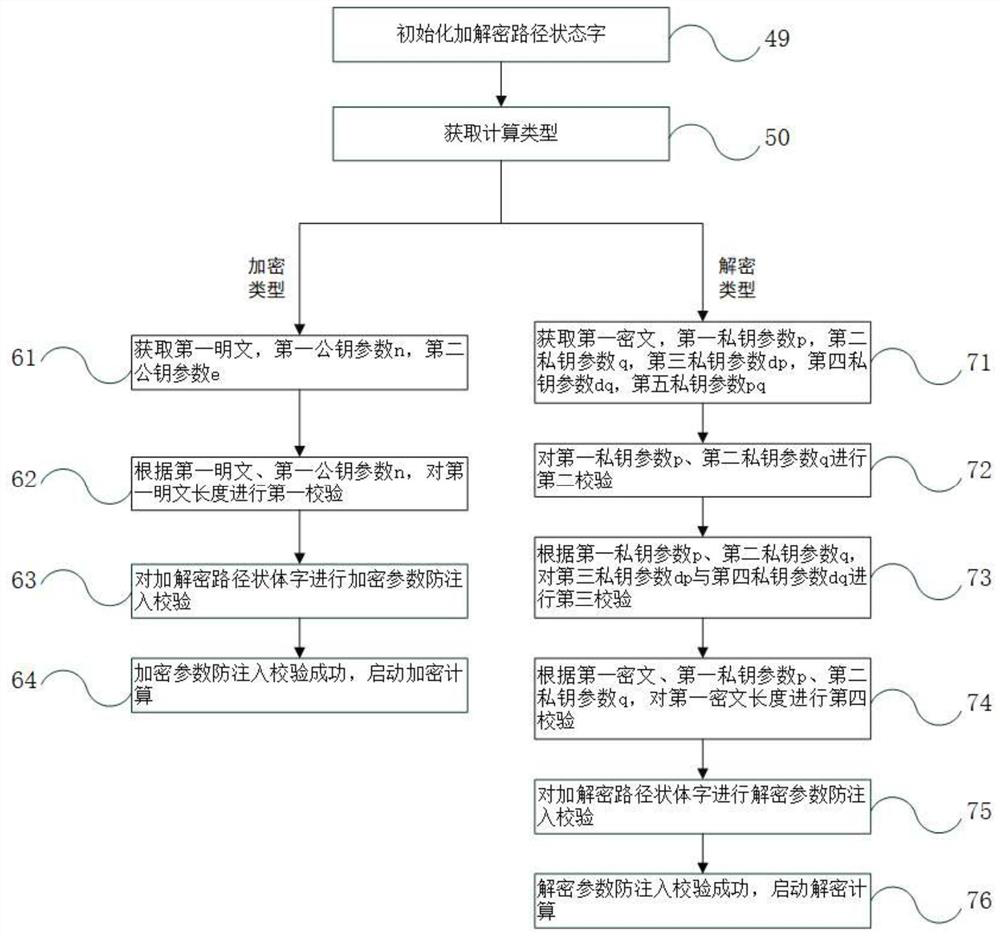
Image
Examples
Embodiment Construction
[0044] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings. Obviously, the described embodiments are only some embodiments of the present invention, rather than all embodiments . Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0045] The public key cryptography algorithm, that is, encryption and decryption do not use the same key: encryption uses public key parameters to operate on plaintext, and decryption uses private key parameters to operate on ciphertext. The key parameters of the public key cryptography algorithm are closely related to large prime numbers, and many times of large prime number calculations are also involved in the calculation process; there ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More