Chaotic encryption method based on Logistic mapping
A chaotic encryption, encryption and decryption technology, applied in the field of video encryption technology, can solve problems such as immature encryption algorithm
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only part of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
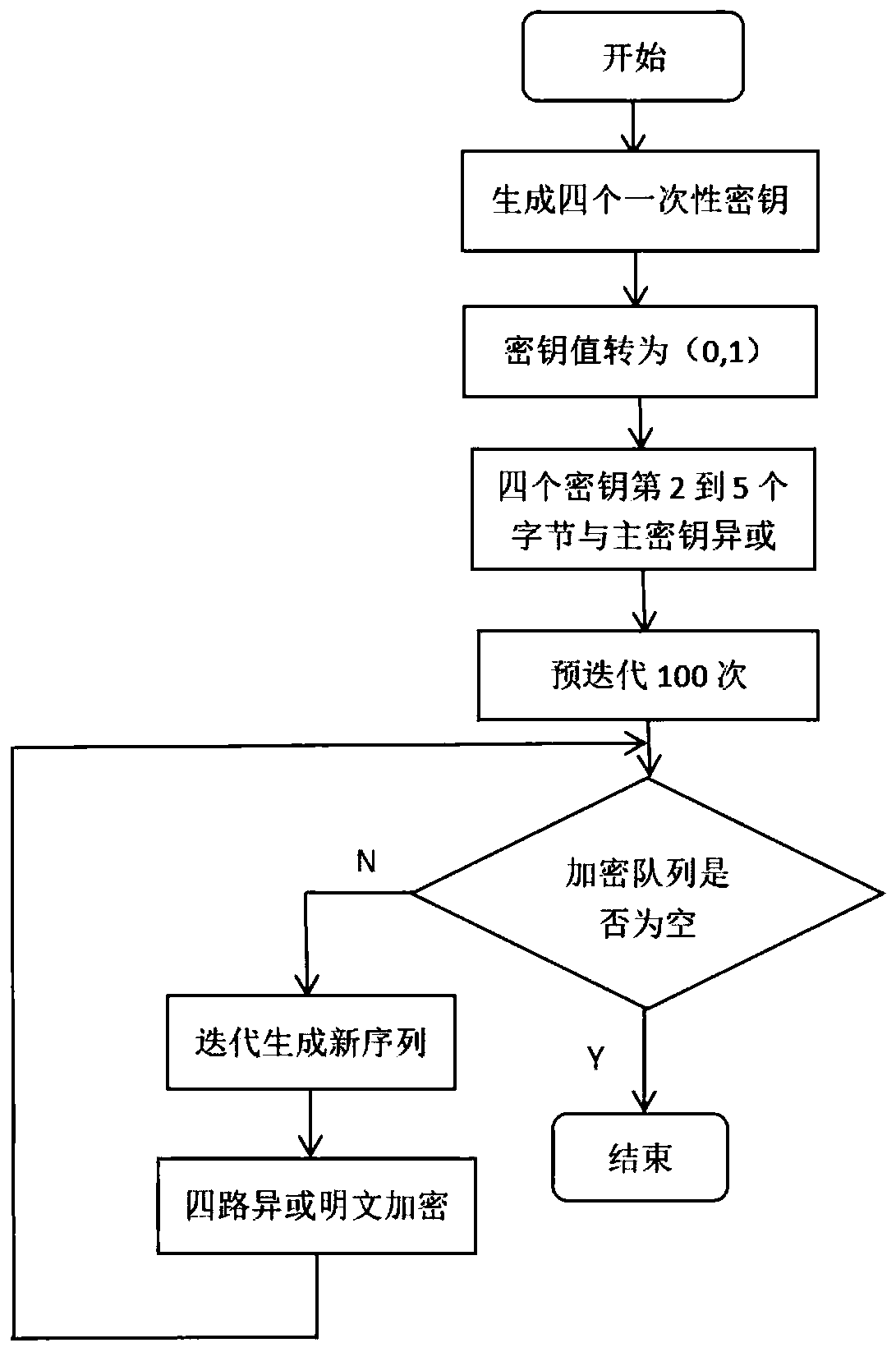
[0039] According to one embodiment of the present invention, propose a kind of lightweight chaotic encryption method, comprise the steps:
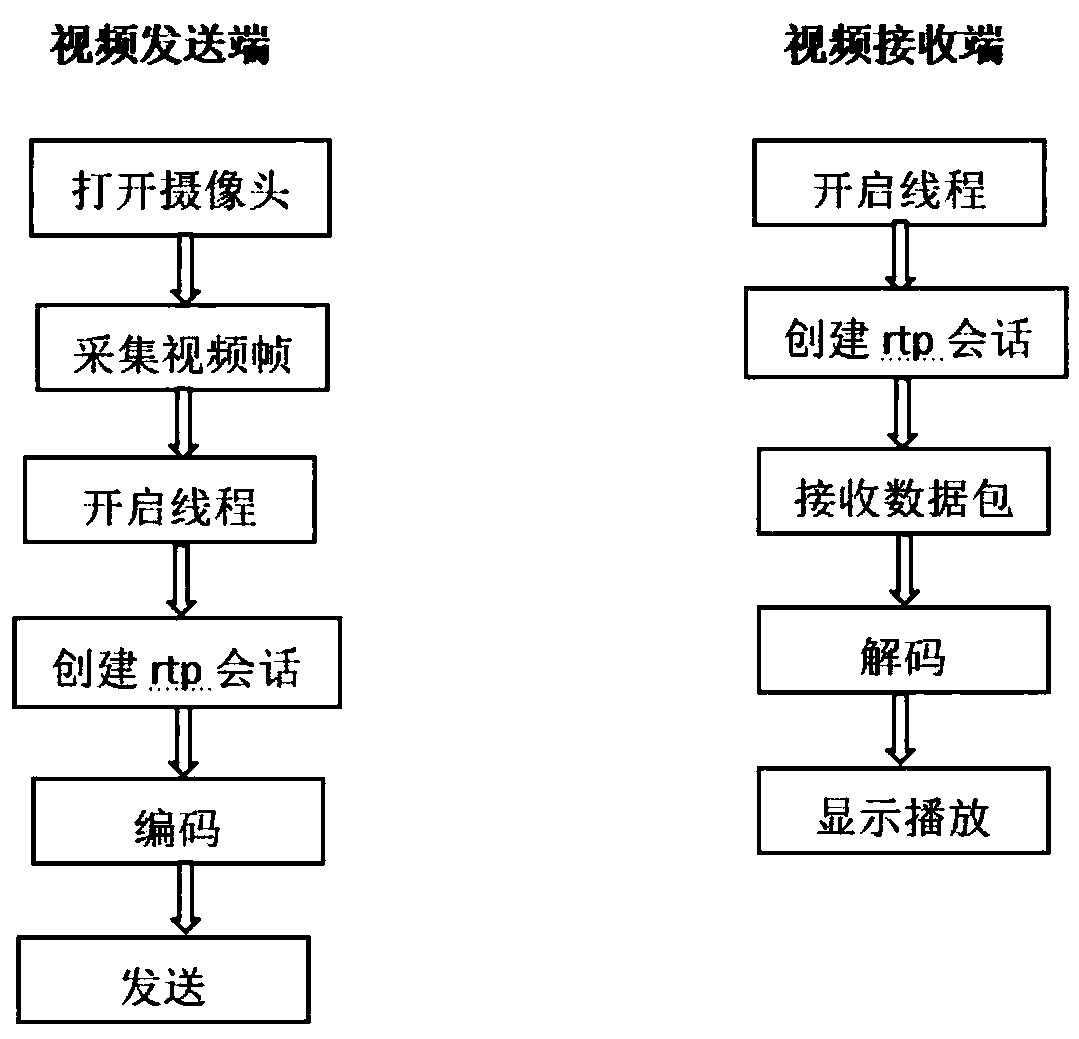
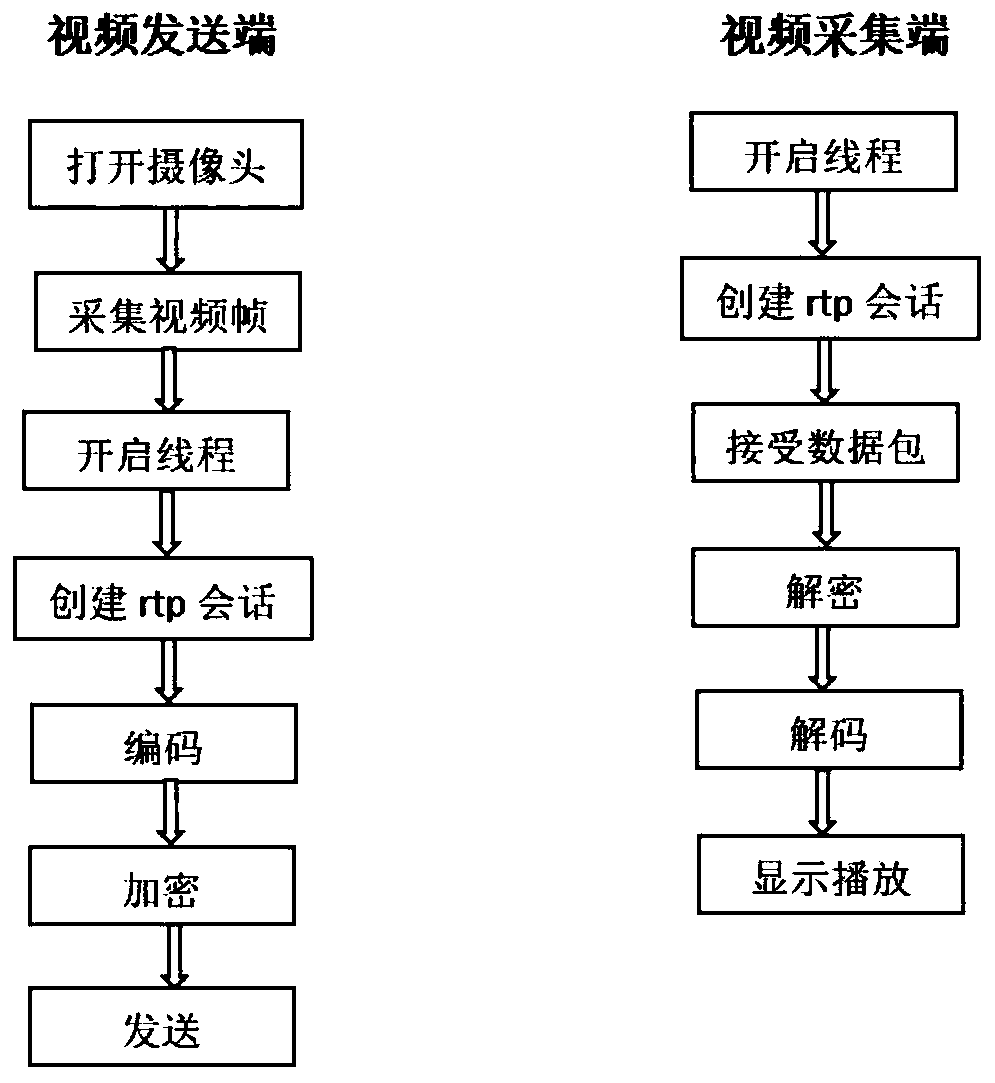
[0040] Involved in the technical solution of video transmission prototype system:
[0041] (1) Design of the scheme:
[0042] (1.1) server end: at first the technical scheme of the present invention will utilize the camera of notebook to gather video, capture video frame then, by data query, this function can ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More