A method and device for detecting tampered applications
A technology that has been tampered with and detected results, applied in the field of mobile Internet, can solve problems such as application integrity cannot be guaranteed, installation failures, smart card security risks, etc., and achieve the effect of avoiding detection of integrity verification.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
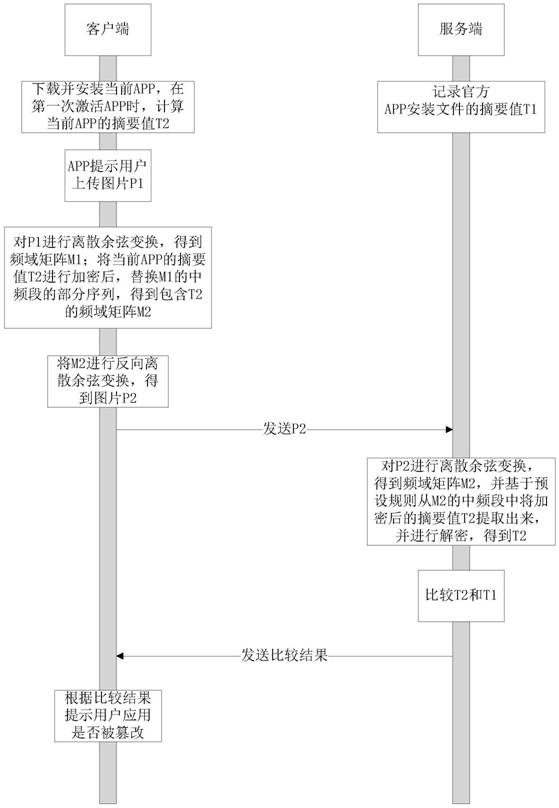
[0062] A method for verifying the integrity of an APP with concealment capabilities on a mobile smart terminal, used in a verification system for the integrity of an application program, including such figure 1 The client and server shown, such as figure 2 shown, including the following steps:
[0063] S1. When the official APP is released, record the summary value T1 of the APP installation file on the server and save it on the server;
[0064] S2. After the user completes the APP installation, when the APP is activated for the first time, the APP starts the daemon process and calculates the summary value T2 of the current APP;
[0065] S3. When the user uses the APP, the APP prompts the user to perform some product process operations that will inevitably upload pictures (such as uploading avatars, setting background pictures, etc.), and the pictures generated during this process are recorded as P1; this picture is the normal use of the user When applying, apply the image ...
Embodiment 2
[0074] Corresponding to the method of the client, this embodiment provides a device for verifying the integrity of the application program, including:
[0075] The installation unit is used to download and install the current application program;
[0076] The verification code calculation unit is configured to activate the current application program and calculate the verification code of the current application program; preferably, the verification code is a summary value generated based on the core file and the resource file of the application program running.
[0077]a first prompting unit, configured to prompt the user to upload the first picture;
[0078] The image transformation unit is configured to acquire the first picture and perform image transformation on it to obtain the first frequency domain matrix; preferably, the image transformation is discrete cosine transformation.
[0079] An encryption and replacement unit, configured to encrypt the check code of the cur...
Embodiment 3
[0085] Corresponding to the method at the server end, this embodiment provides a device for verifying the integrity of an application program, including:
[0086] The recording unit is used to record and save the verification code of the legal application;
[0087] The image transformation unit is used to receive the picture uploaded by the client and perform image transformation; the image transformation is discrete cosine transform.
[0088] The check code extracting unit is used to extract the encrypted check code in the picture; the encrypted check code is obtained by encrypting the abstract value generated based on the core file and the resource file of the current application program.
[0089] The decryption unit is configured to decrypt the encrypted check code to obtain the check code of the current application; the check code is a summary value generated based on the core file and the resource file of the application program.
[0090] The comparison unit is configure...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More