Music embedding attack defense method for voice recognition system
A speech recognition and speech recognition model technology, applied in speech recognition, speech analysis, instruments, etc., can solve problems such as large amount of calculation, achieve good dissemination, great security risks, and protect personal privacy and personal safety.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, and do not limit the protection scope of the present invention.
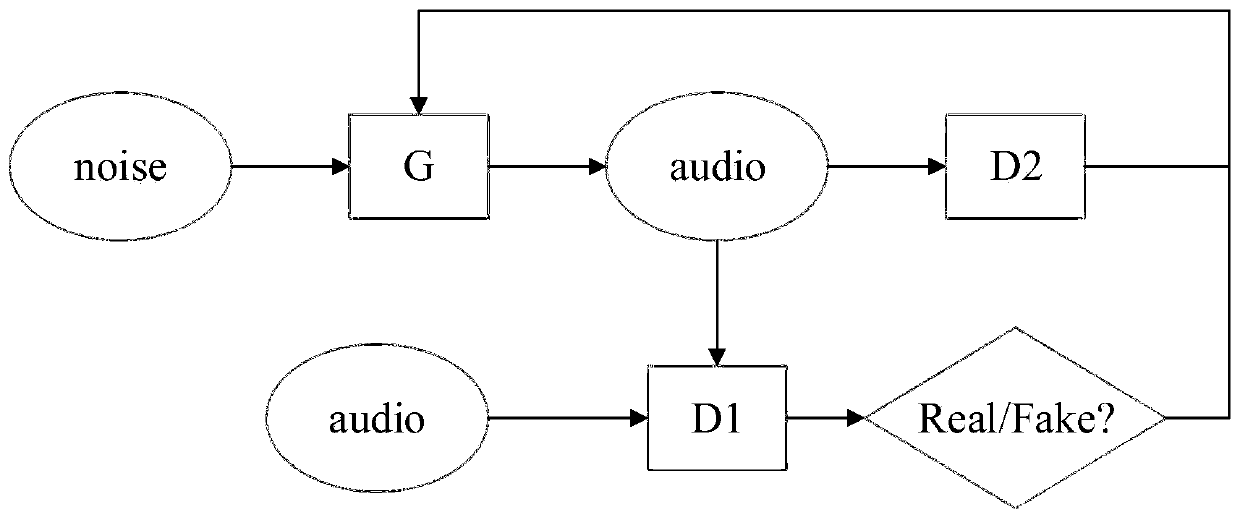
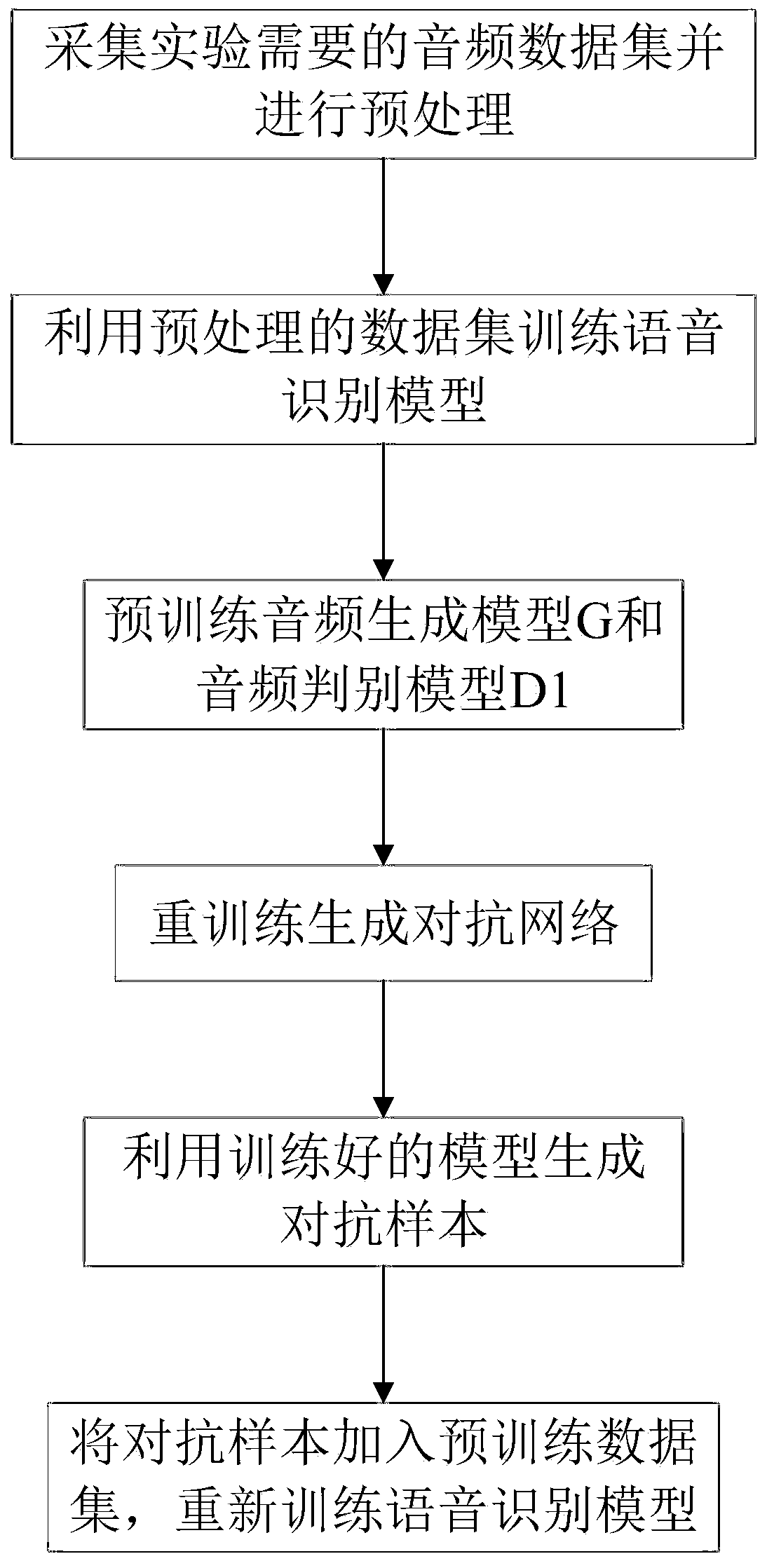
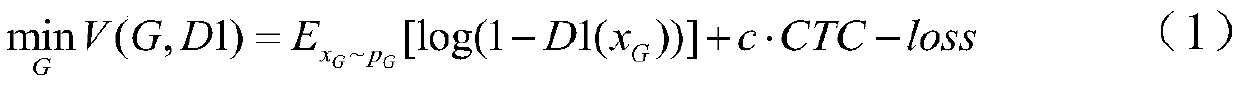
[0030] refer to Figure 1-Figure 2 A method for defending against music embedding attacks for speech recognition systems comprises the following steps:
[0031] (1) Data set preparation and preprocessing: collect the music audio required for the experiment, divide it into a pre-training data set and a disturbance data set for generating adversarial samples, cut the collected music audio and process it into a data stream format;
[0032] (2) Training speech recognition model: use the processed music audio data set to train the speech recognition model, so that the model ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More