A multi-receiver ciphertext searchable identity-based encryption method
An identity encryption, multi-receiver technology, applied in key distribution, can solve the problem of keyword guessing attacks, damage receiver privacy, search information leakage, etc., to resist guessing attacks, improve operating efficiency, and protect search privacy.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
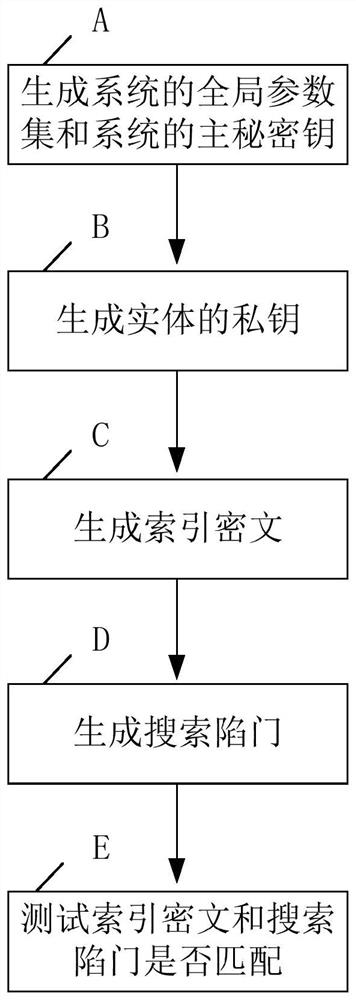
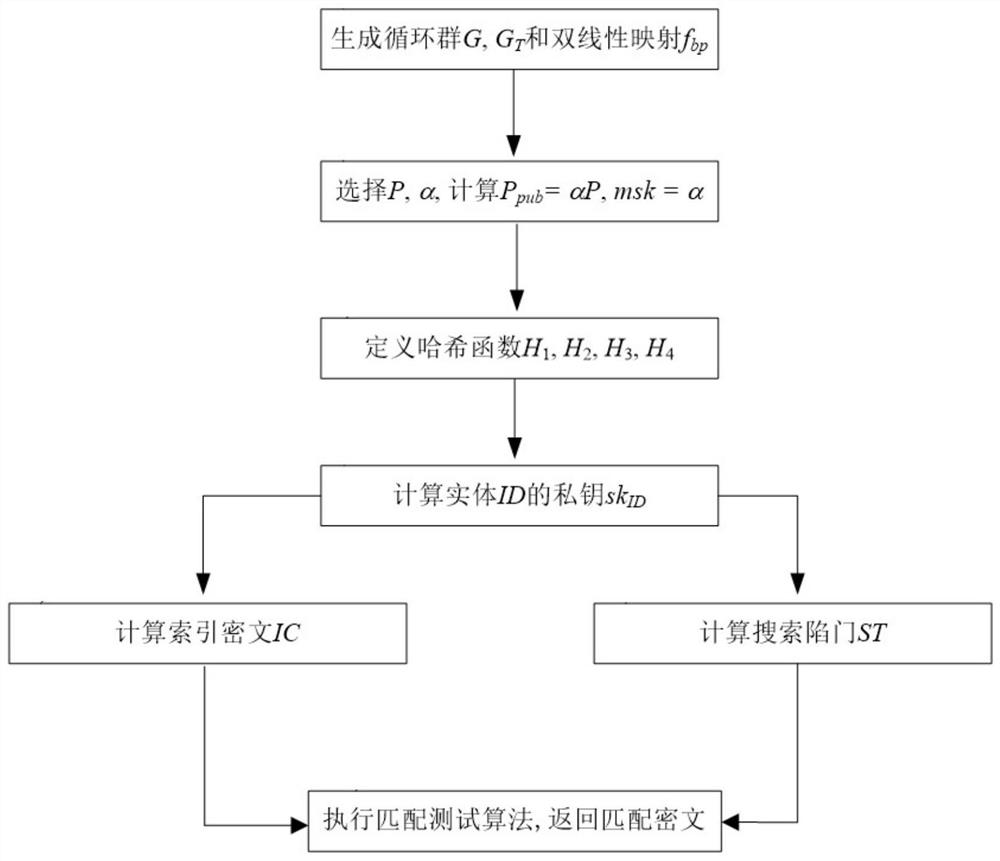
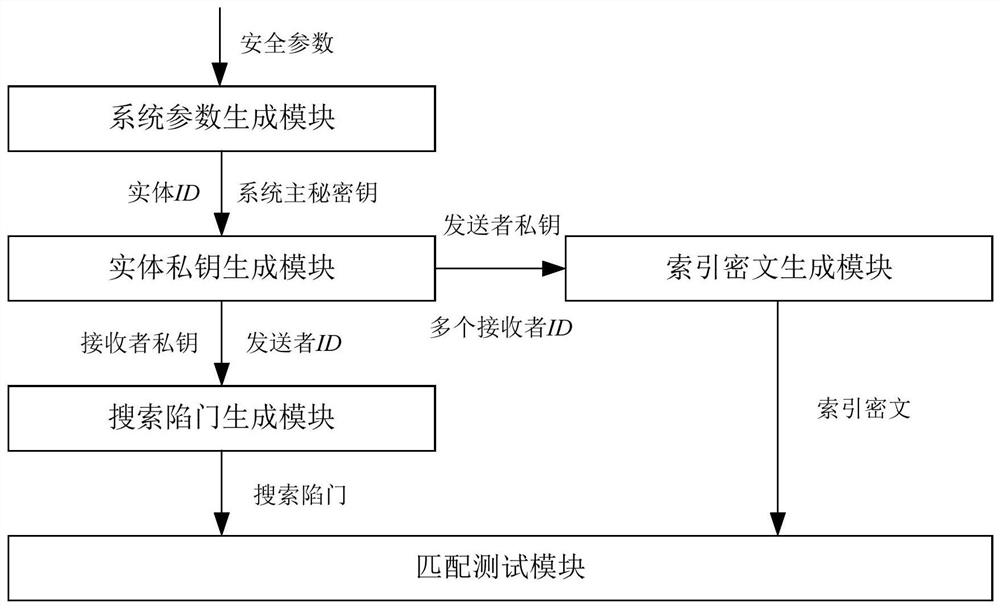
[0040] Below in conjunction with accompanying drawing, technical scheme of the present invention is described in further detail:
[0041] The multi-receiver ciphertext searchable identity-based encryption method of the present invention can be realized by using bilinear mapping. The basic knowledge of bilinear mapping will be briefly introduced below.
[0042] Let q be a prime number, G be an additive cyclic group of order q, G T is the cyclic group of q factorial method, and P is the generator of the additive cyclic group G. If defined in additive cyclic group G and multiplicative cyclic group G T A map f on bp :G×G→G T Satisfying the following three properties, the map is called an effective bilinear map. Among them, f bp :G×G→G T is the Cartesian product of the additive cyclic group G and itself G×G to the multiplicative cyclic group G T The mapping, that is, the bilinear mapping f bp :G×G→G T refers to the function z=f bp (x, y), where x, y∈G are independent vari...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More