An application layer shellcode detection method and device
A detection method and application layer technology, applied in the field of information network security, can solve problems such as inability to achieve attack effects, inability to detect attack behaviors in time, and prediction
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0055]Hereinafter, exemplary embodiments of the present disclosure will be described in more detail with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure can be implemented in various forms and should not be limited by the embodiments set forth herein. On the contrary, these embodiments are provided to enable a more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
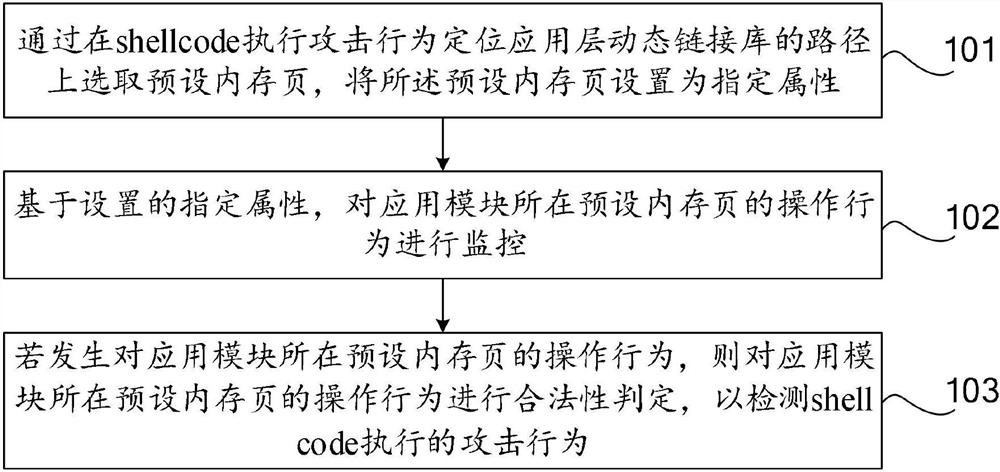
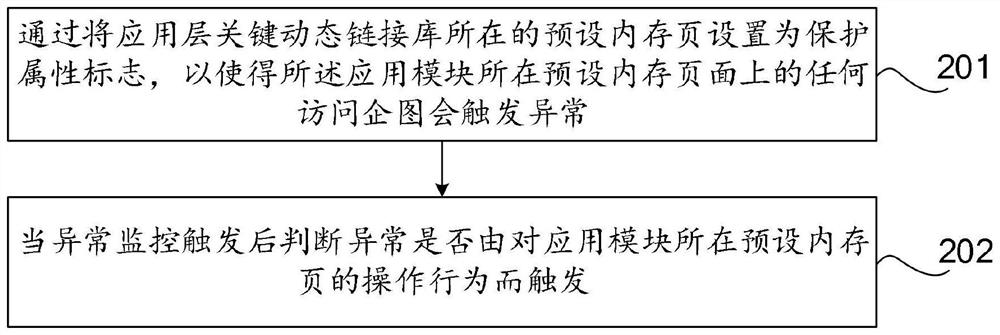
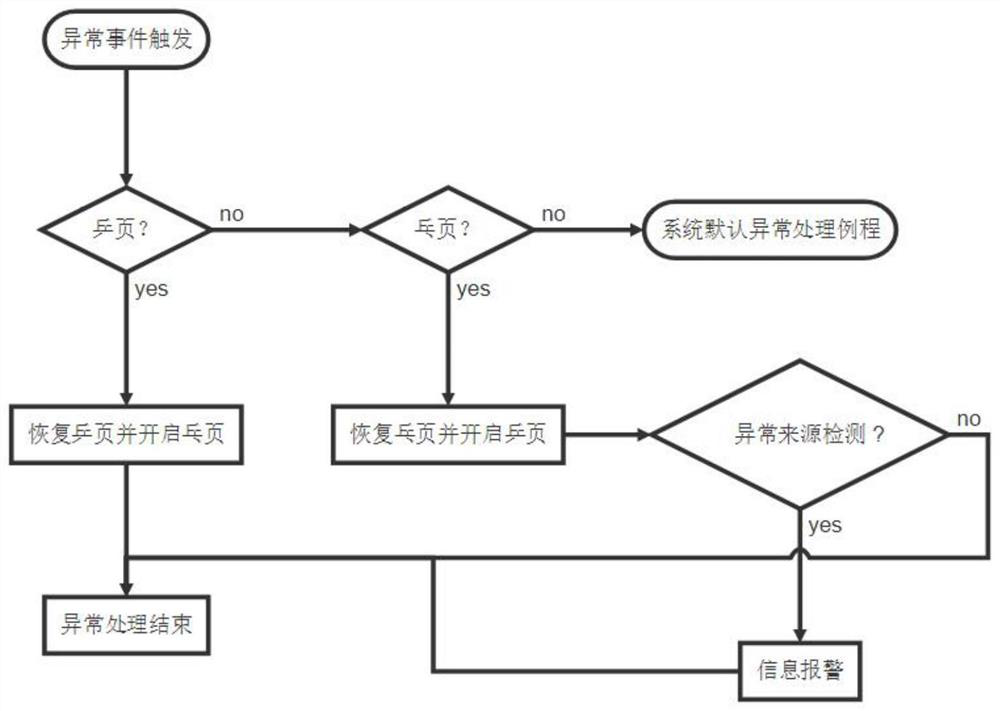
[0056]As mentioned in the background art, in order to bypass the ASLR technology, the shellcode needs to operate on the preset memory page where the application module is located to obtain the system API address. Currently, there is no effective protection technology for bypassing the ASLR mechanism. It is difficult to detect the abnormal behavior of the attacker, and the execution of the application layer shellcode...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More