Threshold decryption method and system based on homomorphic encryption and readable storage medium
A threshold decryption and homomorphic encryption technology, applied in the field of information security, can solve the problem that data is no longer safe
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
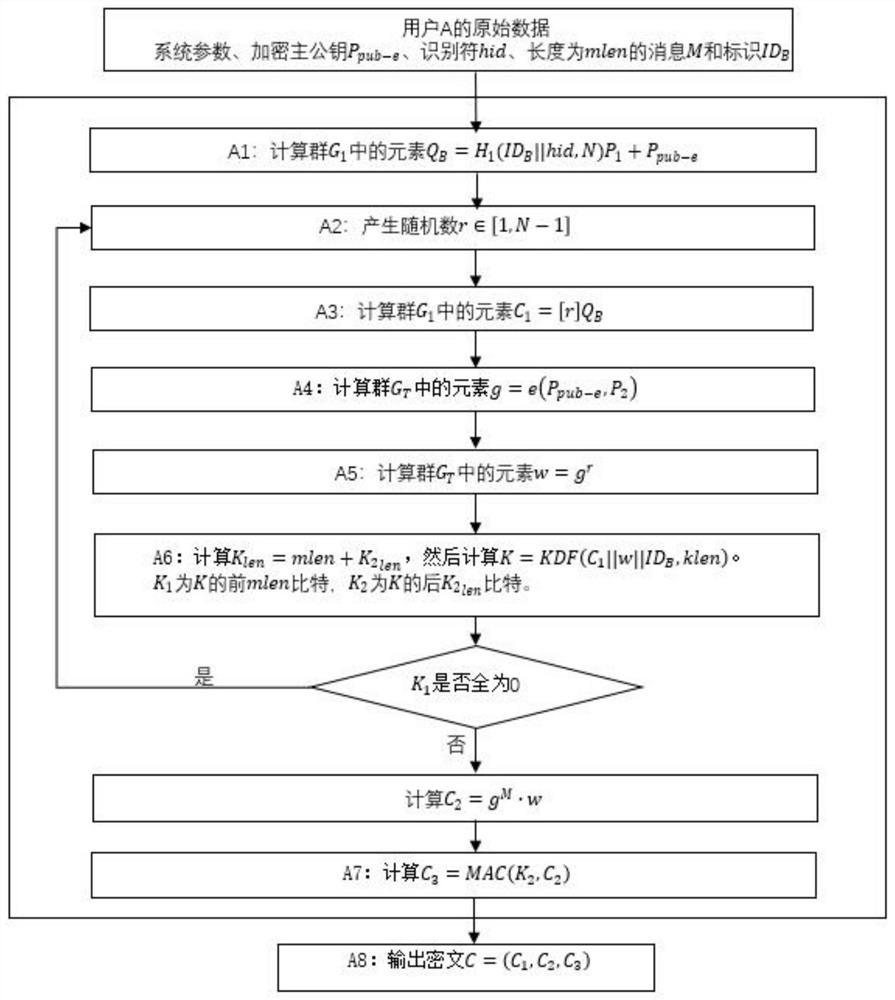
[0048] Terms and symbols:
[0049] A, B: Two users using public key cryptography.
[0050] N: cyclic group G 1 , G 2 and G T The order of is greater than 2 191 prime numbers.
[0051] G 1 : Additive cyclic group of order prime N.
[0052] P 1 : Group G 1 generator of .
[0053] G 2 : Additive cyclic group of order prime N.
[0054] P 2 : Group G 2 generator of .
[0055] G T : The multiplicative cyclic group of prime N order.
[0056] h v (): cryptographic hash function.
[0057] h 1 (): A cryptographic function derived from a cryptographic hash function.
[0058] e: from G 1 ×G 2 to G T bilinear pairing.
[0059] h: The private key generation function identifier identified by one byte, which is selected and made public by KGC.
[0060] ke: encryption master private key.
[0061] P pub-e : Encrypted master public key.
[0062] KDF(): key derivation function.
[0063] MAC(): Message authentication code function.
[0064] ID B : User B's identity, w...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com