APT attack detection method and device, electronic equipment and readable storage medium
An attack detection and grammar technology, applied in the field of malicious attack detection, can solve the problems of high misjudgment rate, easy missed judgment, incomplete security inspection, etc., and achieve the effect of avoiding misjudgment and reducing misjudgment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Example Embodiment
[0080] The purpose of this application is to provide an APT attack detection method, apparatus, electronic device, and readable storage medium, which is animately decreasing the misconduct as much as possible on the basis of unlike.
[0081] In order to make the objects, technical solutions, and advantages of the present application, the technical solutions in the present application embodiment will be clearly described, and the described embodiments will be described in conjunction with the drawings in the present application embodiment. It is an embodiment of the present application, not all of the embodiments. Based on the embodiments in the present application, all other embodiments obtained without making creative labor have not made creative labor premises.
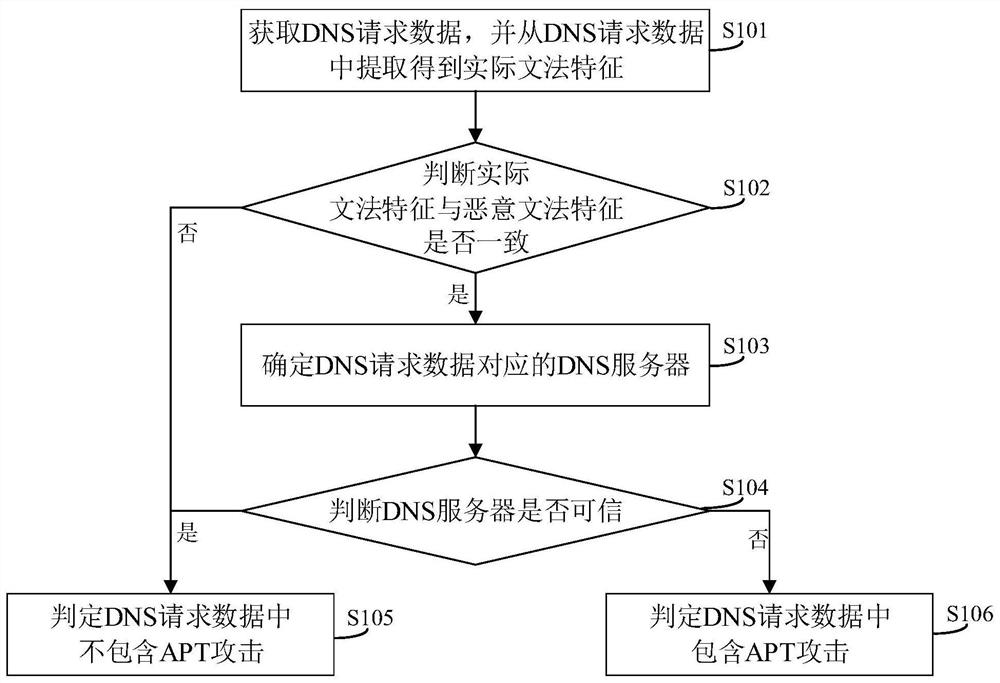
[0082] See figure 1 , figure 1 A flowchart of an APT attack detection method provided herein, including the following steps:
[0083] S101: Get the DNS request data and extract the actual grammatical characteristics fro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More