Block chain based validation of memory commands
A memory and command technology, applied in memory systems, encryption devices with shift registers/memory, instruments, etc., can solve problems such as economic losses, major safety and security issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
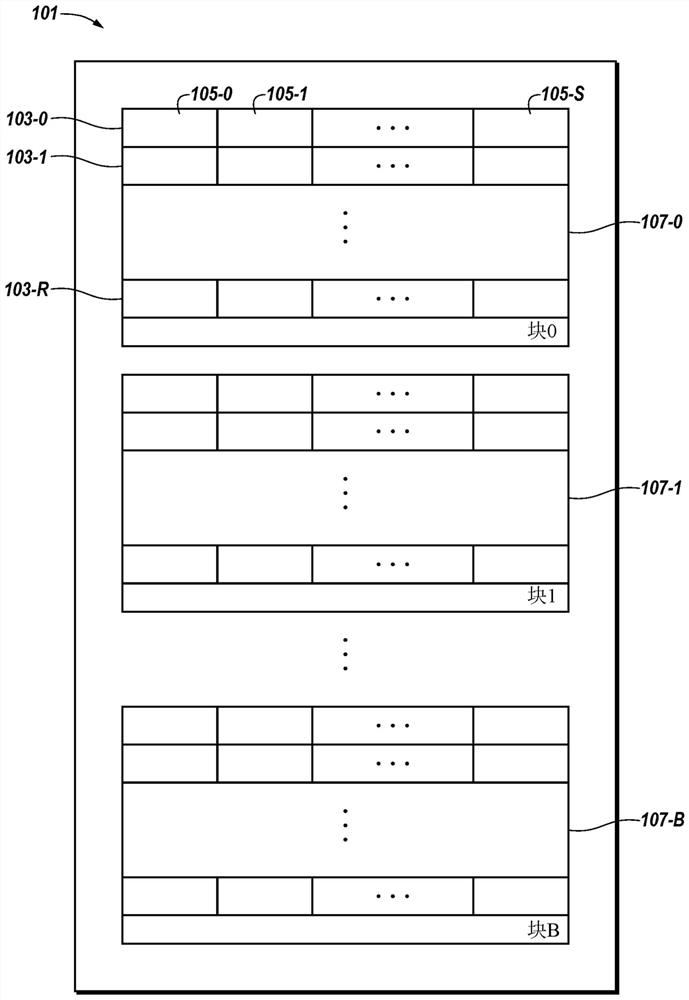
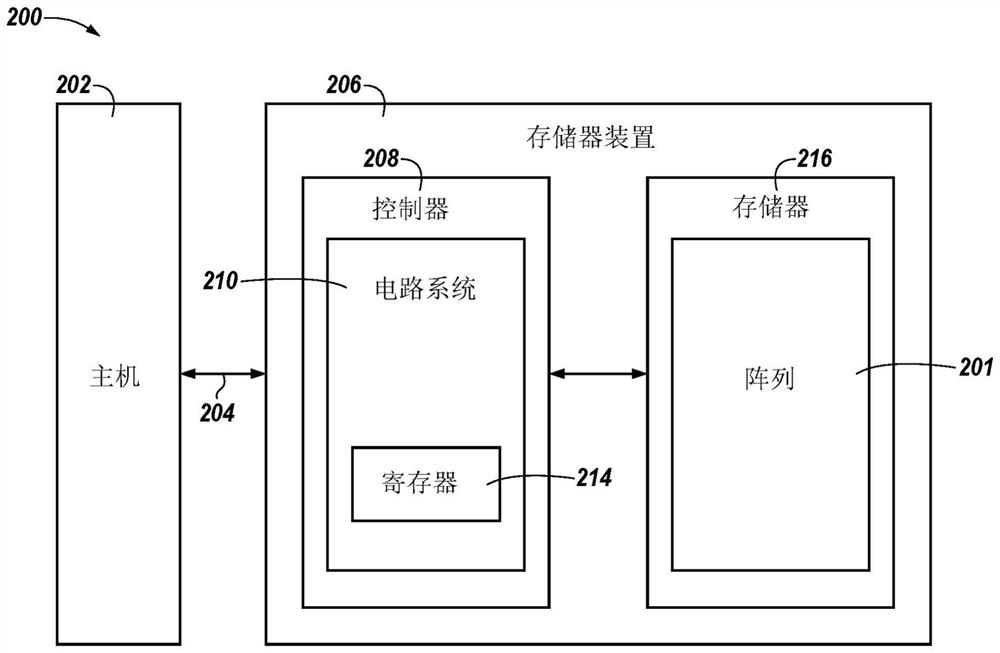
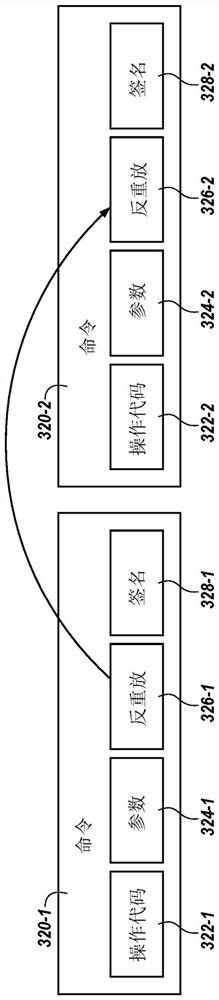
[0016] The present disclosure encompasses devices, methods, and systems for blockchain-based verification of memory commands. Embodiments include: a memory; and circuitry configured to: receive a command included in a block in a chain of blocks for verifying a command to be executed on the memory, wherein the command includes a command based on the anti-replaying a portion of a previous command in a previous block in a chain of blocks; validating the command using the anti-replaying portion of the command; and executing the command on the memory after validating the command.
[0017] Many threats may affect the operation of memory (eg, a memory device) and / or data stored therein (eg, data stored in memory cells of a memory device). For example, a hacker or other malicious user may attempt to perform an activity (eg, an attack), such as a man-in-the-middle (MITM) attack, to make unauthorized changes to the operation of the memory and / or to data stored therein for malicious purp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More