Group user migration method and device, equipment and storage medium
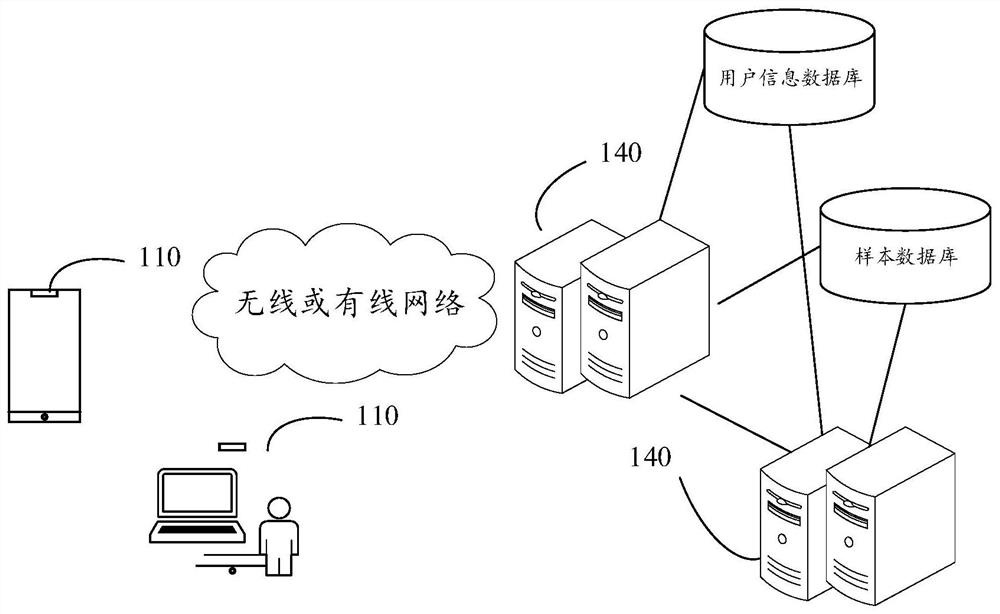
A group and user technology, applied in the computer field, can solve the problem of low efficiency of group user migration and achieve high security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
example 1
[0088] Example 1. There are application A and application B, and both of application A and application B have the function of instant messaging. In the early stage of development, the enterprise used application A to communicate with customers. With the development of the enterprise and the Internet, application A may not be able to meet the needs of the enterprise to communicate with customers. For example, the number of friends allowed in application A is small. In this case, the business may want to use App B, which allows a larger number of friends to be added, to communicate with customers. For the enterprise, directly abandoning application A and adopting application B will lead to the loss of users, and it will take more time to introduce original customers to application B one by one through application A. In addition, in the process of introducing customers from application A to application B, the enterprise also needs to use both application A and application B to ma...
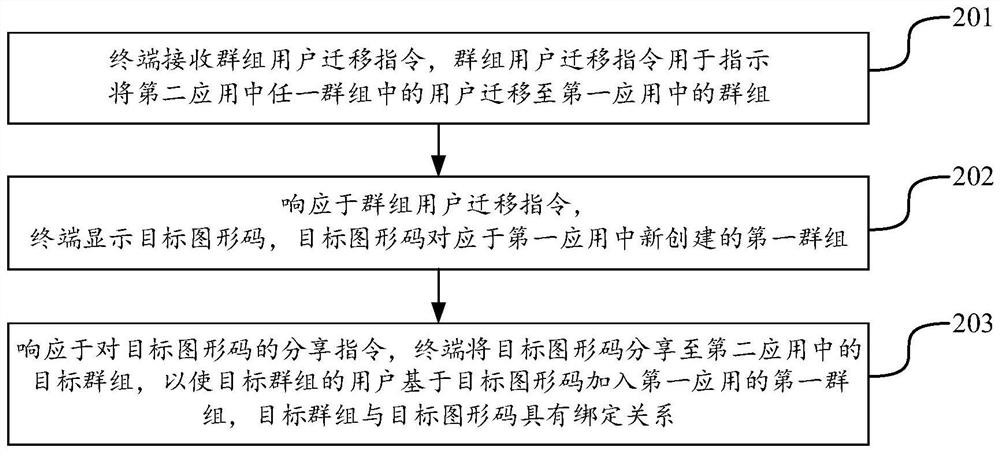
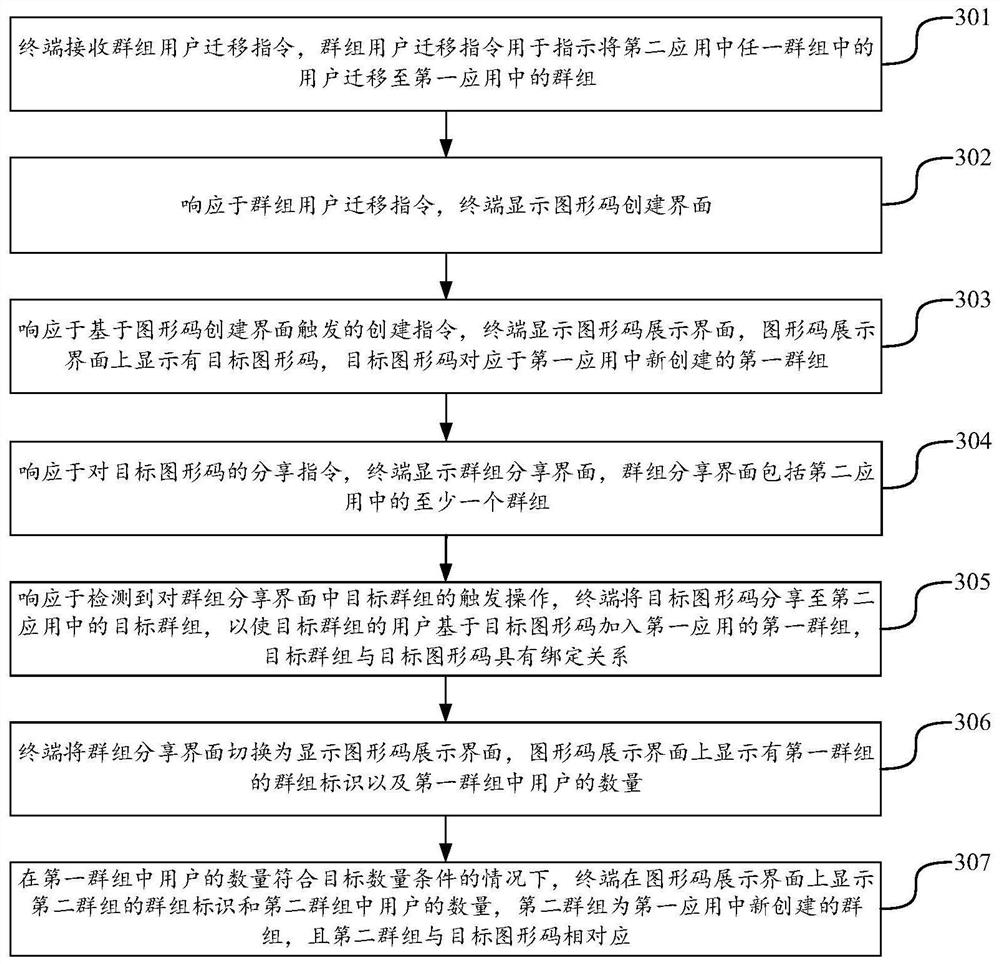
Embodiment approach
[0171] In this implementation mode, only users in the target group can join the first group, and users who are not in the target group cannot join the first group, which realizes "one code for one group" and improves the accuracy of the target graphic code. safety.
[0172] The above implementation manner will be described below through two examples.
[0173] Example 1. In response to the user's second group joining request based on the target graphic code, the first application server obtains the group ID of the user's joining group in the second application. In response to the fact that the group identifiers of the groups that the user joins do not include the group identifier of the target group, the first application server rejects the user's request to join the first group, and the user cannot join the first group.
example 2
[0174] Example 2: The request to join the first group carries the group ID of the group to which the user belongs in the second application, and the first application server can obtain the user's group ID from the request to join the first group. 2. The group ID of the group to which the application belongs. In response to the fact that the group ID of the group to which the user belongs in the second application is different from the group ID of the target group, the first application server rejects the user's request to join the first group, and the user cannot join the first group. group.
[0175] 1505. In response to the number of users in the first group meeting the target number condition, the first application server creates a second group in the first application, where the second group corresponds to the target graphic code.
[0176] 1506. In response to the first group joining request of other users in the target group based on the target graphic code, the first app...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap